3 Months Free Update
3 Months Free Update
3 Months Free Update
You are the Check Point administrator for Alpha Corp with an R80 Check Point estate. You have received a call by one of the management users stating that they are unable to browse the Internet with their new tablet connected to the company Wireless. The Wireless system goes through the Check Point Gateway. How do you review the logs to see what the problem may be?
You want to store the GAiA configuration in a file for later reference. What command should you use?
Using ClusterXL, what statement is true about the Sticky Decision Function?
Identity Awareness lets an administrator easily configure network access and auditing based on three items Choose the correct statement.
Fill in the blanks: Default port numbers for an LDAP server is ______ for standard connections and _______ SSL connections.
Of all the Check Point components in your network, which one changes most often and should be backed up most frequently?
Fill in the blanks: The _______ collects logs and sends them to the _______.
After trust has been established between the Check Point components, what is TRUE about name and IP-address changes?
How is communication between different Check Point components secured in R80? As with all questions, select the best answer.
When a Security Gateways sends its logs to an IP address other than its own, which deployment option is installed?
Which option, when applied to a rule, allows traffic to VPN gateways in specific VPN communities?
Which repositories are installed on the Security Management Server by SmartUpdate?
Which configuration element determines which traffic should be encrypted into a VPN tunnel vs. sent in the clear?
Which of the following situations would not require a new license to be generated and installed?
Identity Awareness allows the Security Administrator to configure network access based on which of the following?
In which scenario will an administrator need to manually define Proxy ARP?
One of major features in R80.x SmartConsole is concurrent administration. Which of the following is NOT possible considering that AdminA, AdminB, and AdminC are editing the same Security Policy?
SandBlast offers flexibility in implementation based on their individual business needs. What is an option for deployment of Check Point SandBlast Zero-Day Protection?
Fill in the blank: In Security Gateways R75 and above, SIC uses ______________ for encryption.
If an administrator wants to restrict access to a network resource only allowing certain users to access it, and only when they are on a specific network what is the best way to accomplish this?
While enabling the Identity Awareness blade the Identity Awareness wizard does not automatically detect the windows domain Why does it not detect the windows domain?
Which part of SmartConsole allows administrators to add, edit delete, and clone objects?
Most Check Point deployments use Gaia but which product deployment utilizes special Check Point code (with unification in R81.10)?
Identity Awareness allows easy configuration for network access and auditing based on what three items?
Fill in the blank: With the User Directory Software Blade, you can create user definitions on a(n) ___________ Server.
The Network Operations Center administrator needs access to Check Point Security devices mostly for troubleshooting purposes. You do not want to give her access to the expert mode, but she still should be able to run tcpdump. How can you achieve this requirement?
Which single Security Blade can be turned on to block both malicious files from being downloaded as well as block websites known to host malware?
Fill in the blank: A(n)_____rule is created by an administrator and configured to allow or block traffic based on specified criteria.
Full synchronization between cluster members is handled by Firewall Kernel. Which port is used for this?
Fill in the blanks: A Security Policy is created in_____, stored in the_____ and Distributed to the various
Which is NOT an encryption algorithm that can be used in an IPSEC Security Association (Phase 2)?
Customer’s R80 management server needs to be upgraded to R80.10. What is the best upgrade method when the management server is not connected to the Internet?
If there are two administrators logged in at the same time to the SmartConsole, and there are objects locked for editing, what must be done to make them available to other administrators? Choose the BEST answer
Phase 1 of the two-phase negotiation process conducted by IKE operates in ______ mode.
Fill in the blank: When a policy package is installed, ________ are also distributed to the target installation Security Gateways.
Which type of Check Point license ties the package license to the IP address of the Security Management Server?
Which Check Point software blade prevents malicious files from entering a network using virus signatures and anomaly-based protections from ThreatCloud?
Can multiple administrators connect to a Security Management Server at the same time?
Which of the following is NOT a policy type available for each policy package?
What does it mean if Deyra sees the gateway status:
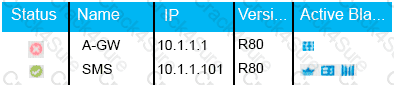
Choose the BEST answer.
Which Threat Prevention Profile is not included by default in R80 Management?
A Check Point Software license consists of two components, the Software Blade and the Software Container. There are ______ types of Software Containers: ________.
In order for changes made to policy to be enforced by a Security Gateway, what action must an administrator perform?
In order to modify Security Policies, the administrator can use which of the following tools? (Choose the best answer.)
Traffic from source 192.168.1.1 is going to www.google.com. The Application Control Blade on the gateway is inspecting the traffic. Assuming acceleration is enable which path is handling the traffic?
The default shell of the Gaia CLI is cli.sh. How do you change from the cli.sh shell to the advanced shell to run Linux commands?
For Automatic Hide NAT rules created by the administrator what is a TRUE statement?
The purpose of the Communication Initialization process is to establish a trust between the Security Management Server and the Check Point gateways. Which statement best describes this Secure Internal
Communication (SIC)?
Which of the following is considered a "Subscription Blade", requiring renewal every 1-3 years?
Name the utility that is used to block activities that appear to be suspicious.
Which tool provides a list of trusted files to the administrator so they can specify to the Threat Prevention blade that these files do not need to be scanned or analyzed?
A network administrator has informed you that they have identified a malicious host on the network, and instructed you to block it. Corporate policy dictates that firewall policy changes cannot be made at this time. What tool can you use to block this traffic?
John is using Management HA. Which Smartcenter should be connected to for making changes?
Which Threat Prevention Software Blade provides comprehensive protection against malicious and unwanted network traffic, focusing on application and server vulnerabilities?
In a Distributed deployment, the Security Gateway and the Security Management software are installed on what platforms?
When a gateway requires user information for authentication, what order does it query servers for user information?
You are going to perform a major upgrade. Which back up solution should you use to ensure your database can be restored on that device?
The “Hit count” feature allows tracking the number of connections that each rule matches. Will the Hit count feature work independently from logging and Track the hits even if the Track option is set to “None”?
In the Check Point Security Management Architecture, which component(s) can store logs?
Which one of the following is the preferred licensing model? Select the BEST answer
Which of the following is an identity acquisition method that allows a Security Gateway to identify Active Directory users and computers?
Why is a Central License the preferred and recommended method of licensing?
Which backup utility captures the most information and tends to create the largest archives?
Fill in the blank: By default, the SIC certificates issued by R80 Management Server are based on the ____________ algorithm.
Please choose correct command syntax to add an “emailserver1” host with IP address 10.50.23.90 using GAiA management CLI?
What are valid authentication methods for mutual authenticating the VPN gateways?
Choose what BEST describes the reason why querying logs now are very fast.
How can the changes made by an administrator before publishing the session be seen by a superuser administrator?
Which of the following is NOT a valid application navigation tab in the R80 SmartConsole?
Which type of Endpoint Identity Agent includes packet tagging and computer authentication?
What is the BEST command to view configuration details of all interfaces in Gaia CLISH?