We at Crack4sure are committed to giving students who are preparing for the Checkpoint 156-215.77 Exam the most current and reliable questions . To help people study, we've made some of our Check Point Certified Security Administrator exam materials available for free to everyone. You can take the Free 156-215.77 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Where is the easiest and BEST place to find information about connections between two machines?
Your Security Management Server fails and does not reboot. One of your remote Security Gateways managed by the Security Management Server reboots.
What occurs with the remote Gateway after reboot?
A digital signature:
What must a Security Administrator do to comply with a management requirement to log all traffic accepted through the perimeter Security Gateway?
You are MegaCorp’s Security Administrator. There are various network objects which must be NATed. Some of them use the Automatic Hide NAT method, while others use the Automatic Static NAT method. What is the rule order if both methods are used together? Give the BEST answer.
You are responsible for the configuration of MegaCorp’s Check Point Firewall. You need to allow two NAT rules to match a connection. Is it possible? Give the BEST answer.
How can you configure an application to automatically launch on the Security Management Server when traffic is dropped or accepted by a rule in the Security Policy?
You have a diskless appliance platform. How do you keep swap file wear to a minimum?
Which command would provide the most comprehensive diagnostic information to Check Point Technical Support?
What command syntax would you use to see accounts the gateway suspects are service accounts?
Access Role objects define users, machines, and network locations as:
What physical machine must have access to the User Center public IP address when checking for new packages with SmartUpdate?
Which of the following authentication methods can be configured in the Identity Awareness setup wizard?
A snapshot delivers a complete GAiA backup. The resulting file can be stored on servers or as a local file in /var/CPsnapshot/snapshots. How do you restore a local snapshot named MySnapshot.tgz?
What is the primary benefit of using the command upgrade_export over either backup or snapshot?
Over the weekend, an Administrator without access to SmartDashboard installed a new R77 Security Gateway using GAiA. You want to confirm communication between the Gateway and the Management Server by installing the Security Policy. What might prevent you from installing the Policy?
During which step in the installation process is it necessary to note the fingerprint for first-time verification?
You are running the license_upgrade tool on your GAiA Gateway. Which of the following can you NOT do with the upgrade tool?
What are you required to do before running the command upgrade_export?
What CANNOT be configured for existing connections during a policy install?
Captive Portal is a __________ that allows the gateway to request login information from the user.
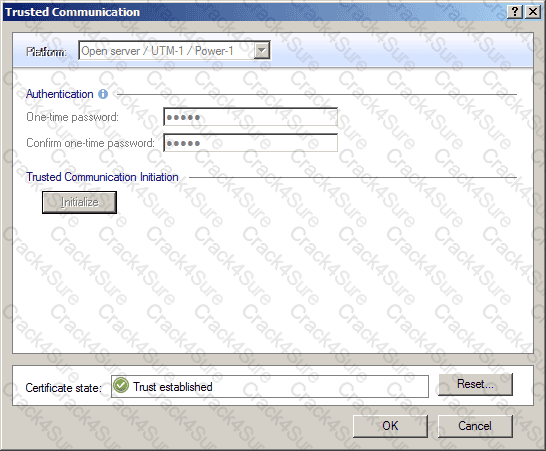
What happens when you open the Gateway object window Trusted Communication and press and confirm Reset?
Exhibit:
Complete this statement from the options provided. Using Captive Portal, unidentified users may be either; blocked, allowed to enter required credentials, or required to download the _____________.
If you were NOT using IKE aggressive mode for your IPsec tunnel, how many packets would you see for normal Phase 1 exchange?
The Identity Agent is a lightweight endpoint agent that authenticates securely with Single Sign-On (SSO). What is not a recommended usage of this method?
Which of these attributes would be critical for a site-to-site VPN?
Certificates for Security Gateways are created during a simple initialization from _____________.
Which authentication type permits five different sign-on methods in the authentication properties window?
Which Client Authentication sign-on method requires the user to first authenticate via the User Authentication mechanism, when logging in to a remote server with Telnet?
You run cpconfig to reset SIC on the Security Gateway. After the SIC reset operation is complete, the policy that will be installed is the:
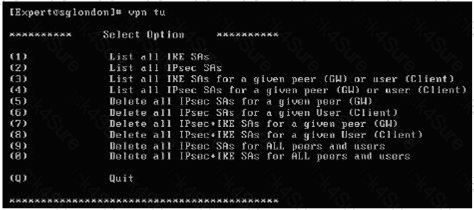
When using vpn tu, which option must you choose if you want to rebuild your VPN for a specific IP (gateway)?
Exhibit:
You want to establish a VPN, using certificates. Your VPN will exchange certificates with an external partner. Which of the following activities should you do first?
Which of the following describes the default behavior of an R77 Security Gateway?
John Adams is an HR partner in the ACME organization. ACME IT wants to limit access to HR servers to designated IP addresses to minimize malware infection and unauthorized access risks. Thus, the gateway policy permits access only from John's desktop which is assigned an IP address 10.0.0.19 via DHCP.
John received a laptop and wants to access the HR Web Server from anywhere in the organization. The IT department gave the laptop a static IP address, but that limits him to operating it only from his desk. The current Rule Base contains a rule that lets John Adams access the HR Web Server from his laptop. He wants to move around the organization and continue to have access to the HR Web Server.
To make this scenario work, the IT administrator:
1) Enables Identity Awareness on a gateway, selects AD Query as one of the Identity Sources installs the policy.
2) Adds an access role object to the Firewall Rule Base that lets John Adams PC access the HR Web Server from any machine and from any location.
John plugged in his laptop to the network on a different network segment and he is not able to connect. How does he solve this problem?
A marketing firm’s networking team is trying to troubleshoot user complaints regarding access to audio-streaming material from the Internet. The networking team asks you to check the object and rule configuration settings for the perimeter Security Gateway.
Which SmartConsole application should you use to check these objects and rules?
Which of the following statements BEST describes Check Point’s Hide Network Address Translation method?
Which of the following can be found in cpinfo from an enforcement point?
The third-shift Administrator was updating Security Management Server access settings in Global Properties. He managed to lock all administrators out of their accounts.
How should you unlock these accounts?
After filtering a fw monitor trace by port and IP, a packet is displayed three times; in the i, I, and o inspection points, but not in the O inspection point.
Which is the likely source of the issue?
While in SmartView Tracker, Brady has noticed some very odd network traffic that he thinks could be an intrusion. He decides to block the traffic for 60 minutes, but cannot remember all the steps. What is the correct order of steps needed to set up the block?
1) Select Active Mode tab in SmartView Tracker.
2) Select Tools > Block Intruder.
3) Select Log Viewing tab in SmartView Tracker.
4) Set Blocking Timeout value to 60 minutes.
5) Highlight connection that should be blocked.
Jack has locked himself out of the Kirk Security Gateway with an incorrect policy and can no longer connect from the McCoy Management Server.
Jack still has access to an out of band console connection on the Kirk Security Gateway. He is logged into the Gaia CLI, what does he need to enter in order to be able to fix his mistake and push policy?
What is also referred to as Dynamic NAT?
Which NAT option is available for Manual NAT as well as Automatic NAT?
What is the appropriate default Gaia Portal address?
Which set of objects have an Authentication tab?
Your company enforces a strict change control policy. Which of the following would be MOST effective for quickly dropping an attacker’s specific active connection?
Lilly needs to review VPN History counters for the last week.
Where would she do this?
Katie has been asked to do a backup on the Blue Security Gateway. Which command would accomplish this in the Gaia CLI?
The R77 fw monitor utility is used to troubleshoot which of the following problems?
How can you activate the SNMP daemon on a Check Point Security Management Server?
You are trying to save a custom log query in R77 SmartView Tracker, but getting the following error:
Could not save
Which of the following is a likely explanation for this?
What statement is true regarding Visitor Mode?
Assume you are a Security Administrator for ABCTech. You have allowed authenticated access to users from Mkting_net to Finance_net. But in the user’s properties, connections are only permitted within Mkting_net. What is the BEST way to resolve this conflict?