We at Crack4sure are committed to giving students who are preparing for the Checkpoint 156-315.77 Exam the most current and reliable questions . To help people study, we've made some of our Check Point Certified Security Expert exam materials available for free to everyone. You can take the Free 156-315.77 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
If using AD Query for seamless identity data reception from Microsoft Active Directory (AD), which of the following methods is NOT Check Point recommended?
Which two processes are responsible on handling Identity Awareness?
Check Point recommends that you back up systems running Check Point products. Run your back ups during maintenance windows to limit disruptions to services, improve CPU usage, and simplify time allotment. Which back up method does Check Point recommend anytime outside a maintenance window?
Which command would you use to save the interface information before upgrading a GAiA Gateway?
SmartProvisioning can provision the Operating System and network settings on which of the following?
When upgrading to NGX R65, which Check Point products do not require a license upgrade to be current?
SSL termination takes place:
Fill in the blank.
Type the command and syntax you would use to verify that your Check Point cluster is functioning correctly.
Which command will only show the number of entries in the connection table?
Which of the following functions CANNOT be performed in Client Info on computer information collected?
Which of the following components contains the Events Data Base?
For proper system operation, the Administrator has to configure the DLP Portal and define its DNS name for which of the following conditions?
True or false? After creating a snapshot of a Windows 2003 SP2 Security Management Server, you can restore it on a Secure Platform R76 Security Management Server, except you must load interface information manually.
You must set up SIP with a proxy for your network. IP phones are in the 172.16.100.0 network.
The Registrar and proxy are installed on host 172.16.100.100.
To allow handover enforcement for outbound calls from SIP-net to network Net_B on the Internet, you have defined the following objects:
Network object: SIP-net: 172.16.100.0/24
SIP-gateway: 172.16.100.100
VoIP Domain object: VolP_domain_A
1.Endpoint domain: SIP-net
2.VoIP gateway installed at: SIP-gateway host object
How would you configure the rule?
While using the SmartProvisioning Wizard to create a new profile, you cannot continue because there are no devices to select. What is a possible reason for this?
i) All devices already have a profile assigned to them
ii) Provisioning Blade is not enabled on the devices
iii) No UTM- 1/Power- 1/Secure Platform devices are defined in Smart Dashboard
iv) SIC is not established on the devices.
What is the consequence of clearing the "Log VoIP Connection" box in Global Properties?
What firewall kernel table stores information about port allocations for Hide NAT connections?
Organizations are sometimes faced with the need to locate cluster members in different geographic locations that are distant from each other. A typical example is replicated data centers whose location is widely separated for disaster recovery purposes. What are the restrictions of this solution?
If the number of kernel instances for CoreXL shown is 6, how many cores are in the physical machine?
The set of rules that governs the types of objects in the directory and their associated attributes is called the:
The SmartEvent Client:
Which of the following does NOT happen when using Pivot Mode in ClusterXL?
Fill in the blank. The command that typically generates the firewall application, operating system, and hardware specific drivers is _____.
What can you do to see the current number of kernel instances in a system with CoreXL enabled?
How are cached usernames and passwords cleared from the memory of a Security Gateway?
When a failed cluster member recovers, which of the following actions is NOT taken by the recovering member?
What is the SmartEvent Analyzer's function?
Anytime a client initiates a connection to a server, the firewall kernel signals the FWD process using a trap. FWD spawns the _____ child service, which runs the security server.
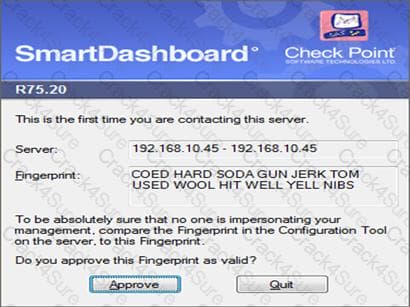
How could you compare the Fingerprint shown to the Fingerprint on the server? Run cpconfig and select:
Exhibit:
Fill in the blank.
MultiCorp is located in Atlanta. It has a branch office in Europe, Asia, and Africa. Each location has its own AD controller for local user login. How many ADqueries have to be configured?
When troubleshooting user authentication, you may see the following entries in a debug of the user authentication process. In which order are these messages likely to appear?
The process _____ is responsible for the authentication for Remote Access clients.
The process that performs the authentication for SSL VPN Users is:
Security server configuration settings are stored in _____.
The process that performs the authentication for legacy session authentication is:
Which of the following is a valid Active Directory designation for user Jane Doe in the MIS department of AcmeCorp.com?
When using a template to define a user in SmartDirectory, the user’s password should be defined in the _____ object.
How is SmartWorkflow enabled?
How is change approved for implementation in SmartWorkflow?
What could the following regular expression be used for in a DLP rule?
\$([0-9]*,[0-9] [0-9] [0-9]. [0-9] [0-9]
Select the best answer.
In ClusterXL, _______ is defined by default as a critical device.
How can you verify that SecureXL is running?
What is not available for Express Reports compared to Standard Reports?
A Smart ProvisioningGateway could be a member of which VPN communities?
(i) Center In Star Topology
(ii) Satellite in Star Topology
(iii) Carter in Remote Access Community
(iv) Meshed Community
Typically, when you upgrade the Security Management Server, you install and configure a fresh R76 installation on a new computer and then migrate the database from the original machine.
Which of the following statements are TRUE?
What is the command to enter the router shell?
You want to verify that your Check Point cluster is working correctly.
Which command line tool can you use?
How would you set the debug buffer size to 1024?
Fred is troubleshooting a NAT issue and wants to check to see if the inbound connection from this internal network is being translated across the interface in the firewall correctly. He decides to use the fw monitor to capture the traffic from the source 192.168.3.5 or the destination of 10.1.1.25 on his Security Gateway. Green that has an IP of 192.168.4.5. What command captures this traffic in a file that he can download and review with WireShark?
Fill in the blank.
Type the command and syntax to view critical devices on a cluster member in a ClusterXL environment.
Check Point support has asked Tony for a firewall capture of accepted packets. What would be the correct syntax to create a capture file to a filename called monitor.out?
Jon is explaining how the inspection module works to a colleague. If a new connection passes through the inspection module and the packet matches the rule, what is the next step in the process?
Steve is troubleshooting a connection problem with an internal application. If he knows the source IP address is 192.168.4.125, how could he filter this traffic?
_____ is the called process that starts when opening SmartView Tracker application.
Which Check Point tool allows you to open a debug file and see the VPN packet exchange details.
Regarding QoS guarantees and limits, which of the following statements is FALSE?
VPN access control would fall under which VPN component?
Even after configuring central logging on Connecter, Connecterlogs are not displaying in Smart View Tracker. What could be the cause of this problem?
With is the SmartEvent Correlation Unit's function?
You need to completely reboot the Operating System after making which of the following changes on the Security Gateway? (i.e. the command cprestart is not sufficient.)
1. Adding a hot-swappable NIC to the Operating System for the first time.
2. Uninstalling the R75 Power/UTM package.
3. Installing the R75 Power/UTM package.
4. Re-establishing SIC to the Security Management Server.
5. Doubling the maximum number of connections accepted by the Security Gateway.
When deploying a dedicated DLP Gateway behind a perimeter firewall on an interface leading to the internal network (there is only one internal network):
Which command would you use to save the interface information before upgrading a Windows Gateway?
Before upgrading SecurePlatform, you should create a backup.
To save time, many administrators use the command backup.
This creates a backup of the Check Point configuration as well as the system configuration.
An administrator has installed the latest HFA on the system for fixing traffic problems after creating a backup file. There is a mistake in the very complex static routing configuration.
The Check Point configuration has not been changed.
Can the administrator use a restore to fix the errors in static routing?
The Security Gateway is installed on SecurePlatform R77. The default port for the Web User Interface is ____________.
What Shell is required in Gaia to use WinSCP?
When, during policy installation, does the atomic load task run?
You are preparing computers for a new ClusterXL deployment. For your cluster, you plan to use three machines with the following configurations:
Cluster Member 1: OS - GAiA; NICs - QuadCard; Memory - 1 GB; Security Gateway - version: R71 and primary Security Management Server installed, version: R77
Cluster Member 2: OS - GAiA; NICs - 4 Intel 3Com; Memory - 1 GB; Security Gateway only, version: R77
Cluster Member 3: OS - GAiA; NICs - 4 other manufacturers; Memory - 512 MB; Security Gateway only, version: R77
Are these machines correctly configured for a ClusterXL deployment?
Fill in the blank with a numeric value. The default port number for standard TCP connections with the LDAP server is
During a Security Management Server migrate export, the system:
You are preparing computers for a new ClusterXL deployment. For your cluster, you plan to use four machines with the following configurations:
Cluster Member 1: OS - GAiA; NICs - QuadCard; Memory - 1 GB; Security Gateway only, version: R77
Cluster Member 2: OS - GAiA; NICs - 4 Intel 3Com; Memory - 1 GB; Security Gateway only, version: R77
Cluster Member 3: OS - GAiA; NICs - 4 other manufacturers; Memory: 512 MB; Security Gateway only, version: R77
Security Management Server: MS Windows 2008; NIC - Intel NIC (1); Security Gateway and primary Security Management Server installed, version: R77
Are these machines correctly configured for a ClusterXL deployment?
The process _____ is responsible for GUI Client communication with the SmartCenter.
Which of the following is the preferred method for adding static routes in GAiA?
When using Captive Portal to send unidentified users to a Web portal for authentication, which of the following is NOT a recommended use for this method?
Paul has just joined the MegaCorp security administration team. Natalie, the administrator, creates a new administrator account for Paul in SmartDashboard and installs the policy. When Paul tries to login it fails. How can Natalie verify whether Paul’s IP address is predefined on the security management server?
MultiCorp is running Smartcenter R71 on an IPSO platform and wants to upgrade to a new Appliance with R77. Which migration tool is recommended?
Where do you define NAT properties so that NAT is performed either client side or server side? In SmartDashboard under:
The “MAC Magic” value must be modified under the following condition:
What is the proper CLISH syntax to configure a default route via 192.168.255.1 in GAiA?
You are the MegaCorp Security Administrator. This company uses a firewall cluster, consisting of two cluster members. The cluster generally works well but one day you find that the cluster is behaving strangely. You assume that there is a connectivity problem with the cluster synchronization link (cross-over cable). Which of the following commands is the BEST for testing the connectivity of the crossover cable?
What is used to validate a digital certificate?
What is the most common cause for a Quick mode packet 1 failing with the error “No Proposal Chosen” error?
Fill in the blank.
To remove site-to-site IKE and IPSEC keys you would enter command _____ _____ and select the option to delete all IKE and IPSec SA’s.
Which of the following is TRUE concerning unnumbered VPN Tunnel Interfaces (VTIs)?
Remote clients are using SSL VPN to authenticate via LDAP server to connect to the organization. Which gateway process is responsible for the authentication?
Katie has enabled User Directory and applied the license to Security Management Server, Green. Her supervisor has asked her to configure the Password Strength options of the least one digit, one symbol, 8 characters long and include an uppercase character. How should she accomplish this?
MicroCorp experienced a security appliance failure. (LEDs of all NICs are off.) The age of the unit required that the RMA-unit be a different model. Will a revert to an existing snapshot bring the new unit up and running?
How does Check Point recommend that you secure the sync interface between gateways?
In GAiA, if one is unsure about a possible command, what command lists all possible commands.
You configure a Check Point QoS Rule Base with two rules: an HTTP rule with a weight of 40, and the Default Rule with a weight of 10. If the only traffic passing through your QoS Module is HTTP traffic, what percent of bandwidth will be allocated to the HTTP traffic?
Lilly has generated an IKE debug on her Security Gateway. She has asked Jack to transfer the file to Support. Where is the file located?
How do you verify the Check Point kernel running on a firewall?
CPD is a core Check Point process that does all of the following EXCEPT:
In Gaia, the operating system can be changed to 32-bit or 64-bit, provided the processor supports 64-bit. What command toggles to 64-bit.
Frank is concerned with performance and wants to configure the affinities settings. His gateway does not have the Performance pack running. What would Frank need to perform in order configure those settings?