We at Crack4sure are committed to giving students who are preparing for the Checkpoint 156-315.80 Exam the most current and reliable questions . To help people study, we've made some of our Check Point Certified Security Expert (CCSE) R80 exam materials available for free to everyone. You can take the Free 156-315.80 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
CPM process stores objects, policies, users, administrators, licenses and management data in a database. The database is:
Fill in the blank: A new license should be generated and installed in all of the following situations EXCEPT when ________ .
To fully enable Dynamic Dispatcher with Firewall Priority Queues on a Security Gateway, run the following command in Expert mode then reboot:
What is the mechanism behind Threat Extraction?
SSL Network Extender (SNX) is a thin SSL VPN on-demand client that is installed on the remote user’s machine via the web browser. What are the two modes of SNX?
What is correct statement about Security Gateway and Security Management Server failover in Check Point R80.X in terms of Check Point Redundancy driven solution?
Which Mobile Access Application allows a secure container on Mobile devices to give users access to internal website, file share and emails?
What is the recommended configuration when the customer requires SmartLog indexing for 14 days and SmartEvent to keep events for 180 days?
What level of CPU load on a Secure Network Distributor would indicate that another may be necessary?
There are two R77.30 Security Gateways in the Firewall Cluster. They are named FW_A and FW_B. The cluster is configured to work as HA (High availability) with default cluster configuration. FW_A is configured to have higher priority than FW_B. FW_A was active and processing the traffic in the morning. FW_B was standby. Around 1100 am, its interfaces went down and this caused a failover. FW_B became active. After an hour, FW_A’s interface issues were resolved and it became operational.
When it re-joins the cluster, will it become active automatically?
Which command can you use to enable or disable multi-queue per interface?
Which of the following authentication methods ARE NOT used for Mobile Access?
You have successfully backed up Check Point configurations without the OS information. What command would you use to restore this backup?
Which statement is true regarding redundancy?
With MTA (Mail Transfer Agent) enabled the gateways manages SMTP traffic and holds external email with potentially malicious attachments. What is required in order to enable MTA (Mail Transfer Agent) functionality in the Security Gateway?
What is true about the IPS-Blade?
What is the base level encryption key used by Capsule Docs?
When doing a Stand-Alone Installation, you would install the Security Management Server with which other Check Point architecture component?
If you needed the Multicast MAC address of a cluster, what command would you run?
After the initial installation on Check Point appliance, you notice that the Management-interface and default gateway are incorrect.
Which commands could you use to set the IP to 192.168.80.200/24 and default gateway to 192.168.80.1.
Which blades and or features are not supported in R80?
In R80 spoofing is defined as a method of:
When a packet arrives at the gateway, the gateway checks it against the rules in the hop Policy Layer, sequentially from top to bottom, and enforces the first rule that matches a packet. Which of the following statements about the order of rule enforcement is true?
The fwd process on the Security Gateway sends logs to the fwd process on the Management Server via which 2 processes?
How can SmartView application accessed?
During the Check Point Stateful Inspection Process, for packets that do not pass Firewall Kernel Inspection and are rejected by the rule definition, packets are:
N NO: 211
The essential means by which state synchronization works to provide failover in the event an active member goes down, ____________ is used specifically for clustered environments to allow gateways to report their own state and learn about the states of other members in the cluster.
How many layers make up the TCP/IP model?
Which packet info is ignored with Session Rate Acceleration?
Pamela is Cyber Security Engineer working for Global Instance Firm with large scale deployment of Check Point Enterprise Appliances using GAiA/R80.10. Company’s Developer Team is having random access issue to newly deployed Application Server in DMZ’s Application Server Farm Tier and blames DMZ Security Gateway as root cause. The ticket has been created and issue is at Pamela’s desk for an investigation. Pamela decides to use Check Point’s Packet Analyzer Tool-fw monitor to iron out the issue during approved Maintenance window.
What do you recommend as the best suggestion for Pamela to make sure she successfully captures entire traffic in context of Firewall and problematic traffic?
Which VPN routing option uses VPN routing for every connection a satellite gateway handles?
Which is the correct order of a log flow processed by SmartEvent components?
What SmartEvent component creates events?
John is using Management HA. Which Security Management Server should he use for making changes?
One of major features in R80 SmartConsole is concurrent administration.
Which of the following is NOT possible considering that AdminA, AdminB and AdminC are editing the same Security Policy?
SmartEvent has several components that function together to track security threats. What is the function of the Correlation Unit as a component of this architecture?
Which of the following technologies extracts detailed information from packets and stores that information in state tables?
What scenario indicates that SecureXL is enabled?
Which of the following is NOT a type of Endpoint Identity Agent?
What is the valid range for Virtual Router Identifier (VRID) value in a Virtual Routing Redundancy Protocol (VRRP) configuration?
Besides fw monitor, what is another command that can be used to capture packets?
a. ping
B. arp
C. tcpdump
D. traceroute
Which of the following is NOT a valid type of SecureXL template?
What is the most recommended way to install patches and hotfixes?
What state is the Management HA in when both members have different policies/databases?
Which of these statements describes the Check Point ThreatCloud?
What is the command to see cluster status in cli expert mode?
Fill in the blank: Authentication rules are defined for ________ .
What statement best describes the Proxy ARP feature for Manual NAT in R80.10?
What two ordered layers make up the Access Control Policy Layer?
In a Client to Server scenario, which inspection point is the first point immediately following the tables and rule base check of a packet coming from outside of the network?
When simulating a problem on ClusterXL cluster with cphaprob –d STOP -s problem -t 0 register, to initiate a failover on an active cluster member, what command allows you remove the problematic state?
Which TCP-port does CPM process listen to?
D18912E1457D5D1DDCBD40AB3BF70D5D
The system administrator of a company is trying to find out why acceleration is not working for the traffic. The traffic is allowed according to the rule based and checked for viruses. But it is not accelerated. What is the most likely reason that the traffic is not accelerated?
The Firewall kernel is replicated multiple times, therefore:
When Identity Awareness is enabled, which identity source(s) is(are) used for Application Control?
DLP and Geo Policy are examples of what type of Policy?
Which is NOT an example of a Check Point API?
What CLI utility runs connectivity tests from a Security Gateway to an AD domain controller?
In which formats can Threat Emulation forensics reports be viewed in?
What component of R80 Management is used for indexing?
What key is used to save the current CPView page in a filename format cpview_”cpview process ID”.cap”number of captures”?
SmartEvent provides a convenient way to run common command line executables that can assist in investigating events. Right-clicking the IP address, source or destination, in an event provides a list of default and customized commands. They appear only on cells that refer to IP addresses because the IP address of the active cell is used as the destination of the command when run. The default commands are:
What is the correct order of the default “fw monitor” inspection points?
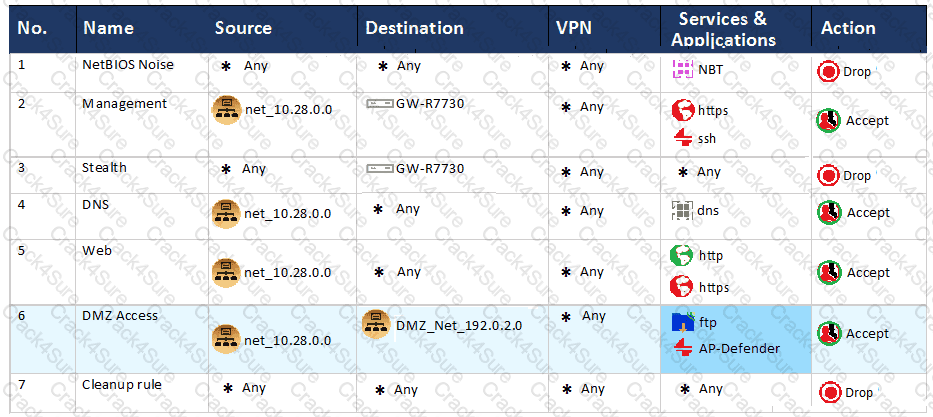
You are the administrator for ABC Corp. You have logged into your R80 Management server. You are making some changes in the Rule Base and notice that rule No.6 has a pencil icon next to it.
What does this mean?