We at Crack4sure are committed to giving students who are preparing for the Checkpoint 156-915.80 Exam the most current and reliable questions . To help people study, we've made some of our Check Point Certified Security Expert Update - R80.10 exam materials available for free to everyone. You can take the Free 156-915.80 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Your organization maintains several IKE VPN’s. Executives in your organization want to know which mechanism Security Gateway R80 uses to guarantee the authenticity and integrity of messages. Which technology should you explain to the executives?
You are trying to configureDirectional VPN Rule Match in the Rule Base. But the Match column does not have the option to see the Directional Match. You see the following window.
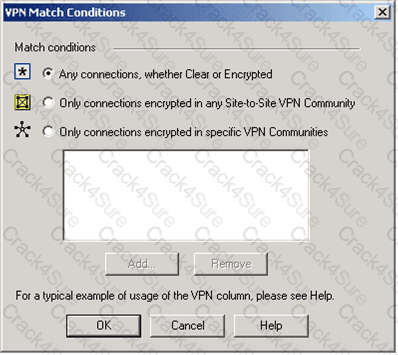
What must you enable to see the Directional Match?
You find that Gateway fw2 can NOT be added to the cluster object. What are possible reasons for that?
Exhibit:
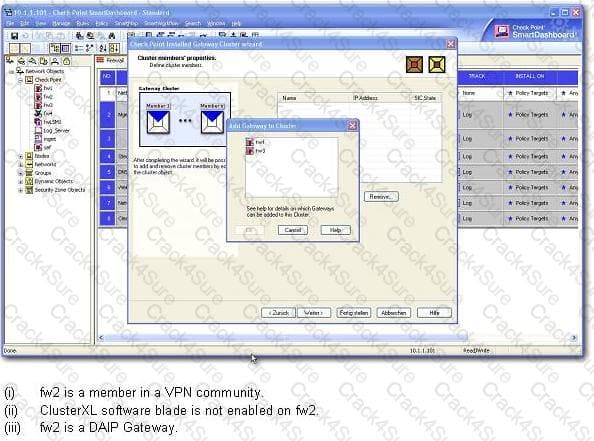
1) fw2 is a member in a VPN community.
2) ClusterXL software blade is not enabled on fw2.
3) fw2 is a DAIP Gateway.
Fill in the blanks. To view the number of concurrent connections going through your firewall, you would use the command and syntax __ ___ __ __________ __ .
If Jack was concerned about the number of log entries he would receive in the SmartReporter system, which policy would he need to modify?
Which CLI tool helps on verifying proper ClusterXL sync?
Where is it necessary to configure historical records in SmartView Monitor to generate Express reports in SmartReporter?
Can you implement a complete IPv6 deployment without IPv4 addresses?
Fill in the blank.
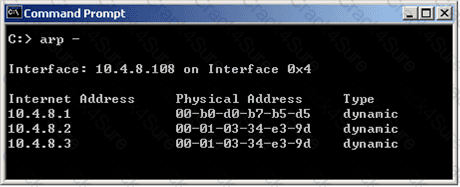
InNew Mode HA, the internal cluster IP VIP address is 10.4.8.3. The internal interfaces on two members are 10.4.8.1 and 10.4.8.2 Internal host 10.4.8.108 pings 10.4.8.3, and receives replies. Review the ARP table from the internal Windows host 10.4.8.108. According to the output, which member is the standby machine?
To provide full connectivity upgrade status, use command
What command withappropriate switches would you use to test Identity Awareness connectivity?
Type the full fw command and syntax that will show full synchronization status.
Fill in the blank with a numeric value. The default port number for Secure Sockets Layer (SSL) connections with the LDAP Serveris
If your firewall is performing a lot of IPS inspection and the CPUs assigned tofw_worker_thread are at or near 100%, which of the following could you do to improve performance?
A ClusterXL configuration is limited to ___ members.
Fill in the blank. To save your OSPF configuration in GAiA, enter the command ___________ .
Which statements about Management HA are correct?
1) Primary SmartCenter describes first installed SmartCenter
2) Active SmartCenter is always used to administrate with SmartConsole
3) Active SmartCenter describes first installed SmartCenter
4) Primary SmartCenter is always used to administrate with SmartConsole
Which three of the following are ClusterXL member requirements?
1) same operating systems
2) same Check Point version
3) same appliance model
4) same policy
How many pre-defined exclusions are included by default in SmartEvent R80 as part of the product installation?
What givesadministrators more flexibility when configuring Captive Portal instead of LDAP query for Identity Awareness authentication?
The third-shift Administrator was updating Security Management Server access settings in Global Properties. He managed to lock all administrators out of their accounts. How should you unlock these accounts?
Select the correct statement about Secure Internal Communications (SIC) Certificates. SIC Certificates:
What type of traffic can be re-directed to the Captive Portal?
John Adams is an HR partner in the ACME organization. ACME IT wants to limit access to HR servers to designated IP addresses to minimizemalware infection and unauthorized access risks. Thus, the gateway policy permits access only from John's desktop which is assigned a static IP address 10.0.0.19.
John received a laptop and wants to access the HR Web Server from anywhere in the organization. The IT department gave the laptop a static IP address, but that limits him to operating it only from his desk. The current Rule Base contains a rule that lets John Adams access the HR Web Server from his laptop with a static IP (10.0.0.19). He wants tomove around the organization and continue to have access to the HR Web Server.
To make this scenario work, the IT administrator:
1) Enables Identity Awareness on a gateway, selects AD Query as one of the Identity Sources installs the policy.
2) Adds an access role object to the Firewall Rule Base that lets John Adams PC access the HR Web Server from any machine and from any location.
What should John do when he cannot access the web server from a different personal computer?
Several Security Policies can be used for different installation targets. The Firewall protecting Human Resources’ servers should have its own Policy Package. These rules must be installed on this machine and not onthe Internet Firewall. How can this be accomplished?
Your company is running Security Management Server R80 on GAiA, which has been migrated through each version starting from CheckPoint 4.1. How do you add a new administrator account?
Where can you find the Check Point’s SNMP MIB file?
Which of the following statements accurately describes the command upgrade_export?
Suppose the Security Gateway hard drive fails and you are forced to rebuild it. You have a snapshot file stored to a TFTP server andbackups of your Security Management Server. What is the correct procedure for rebuilding the Gateway quickly?
You find that Users are not prompted for authentication when they access their Web servers, even though you havecreated an HTTP rule via User Authentication. Choose the BEST reason why.
Your internal network is configured to be 10.1.1.0/24. This network is behind your perimeter R80 Gateway, which connects to your ISP provider. How do you configure the Gateway to allow this network to go out to the Internet?
Your organization’s disaster recovery plan needs an update to the backup and restore section to reap the new distributed R80 installation benefits. Your plan must meet the following required and desired objectives:
Required Objective: The Security Policy repository must be backed up no less frequently than every 24 hours.
Desired Objective: The R80 components that enforce the Security Policies should be backed up at least once a week.
Desired Objective: Back up R80 logs at least once a week.
Your disasterrecovery plan is as follows:
- Use the cron utility to run the command upgrade_export each night on the Security Management Servers.
- Configure the organization's routine back up software to back up the files created by the command upgrade_export.
- Configure the GAiA back up utility to back up the Security Gateways every Saturday night.
- Use the cron utility to run the command upgrade_export each Saturday night on the log servers.
- Configure an automatic, nightly logswitch.
- Configure theorganization's routine back up software to back up the switched logs every night.
Upon evaluation, your plan:
You are a Security Administrator who has installed Security Gateway R80 on your network. You need to allow a specific IP address range for a partner site to access your intranet Web server. To limit the partner’s access for HTTP and FTP only, you did the following:
1)Created manual Static NAT rules for the Web server.
2) Cleared the following settings in the Global Properties > Network Address Translation screen:
- Allow bi-directional NAT
- Translate destination on client side
Do the above settings limit the partner’s access?
You want to implement Static Destination NAT in order to provide external, Internet users access to an internal Web Serverthat has a reserved (RFC 1918) IP address. You have an unused valid IP address on the network between your Security Gateway and ISP router. You control the router that sits between the firewall external interface and the Internet.
What is an alternative configuration if proxy ARP cannot be used on your Security Gateway?
You are running a R80 Security Gateway on GAiA. In case of a hardware failure, you have a server with the exact same hardware and firewall version installed. What back up method could be used to quickly put the secondary firewall into production?
You have three servers located in a DMZ, using private IP addresses. You wantinternal users from 10.10.10.x to access the DMZ servers by public IP addresses. Internal_net 10.10.10.x is configured for Hide NAT behind the Security Gateway’s external interface.
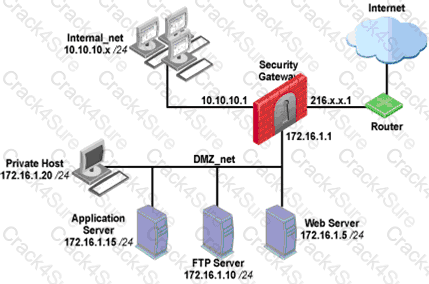
What is the best configuration for 10.10.10.x users to access the DMZservers, using the DMZ servers’ public IP addresses?
Your R80 primary Security Management Server is installed on GAiA. You plan to schedule the Security Management Server to run fw logswitch automatically every 48 hours. How do you create this schedule?
You have created a Rule Base for firewall, websydney. Now you are going to create a new policy package with security and address translation rules for a secondGateway.
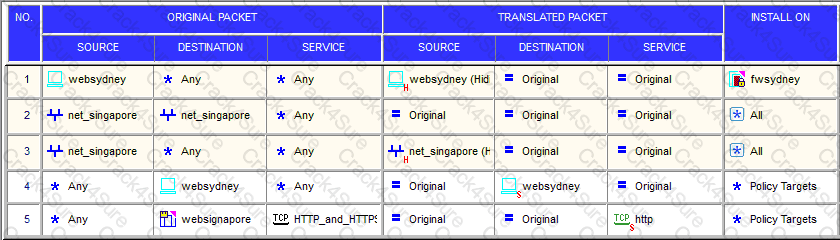
What is TRUE about the new package’s NAT rules?
Which command would provide the most comprehensive diagnostic information to Check Point Technical Support?
In SmartDashboard, Translate destination on client side is checked in Global Properties. When Network Address Translation is used:
Which of the following allows administrators to allow or deny traffic to or from a specific network based on the user’s credentials?
Peter is your new Security Administrator. On his first working day, he is very nervous and enters the wrong password three times. His account is locked. What can bedone to unlock Peter’s account? Give the BEST answer.
Which of the following tools is used to generate a Security Gateway R80 configuration report?
An internal host initiates a session to the Google.com website and is set for Hide NAT behind the Security Gateway. The initiating traffic is an example of __________.
You need to back up the routing, interface, and DNSconfiguration information from your R80 GAiA Security Gateway. Which backup-and-restore solution do you use?
You need to change the number of firewall instances used by CoreXL. How can you achieve this goal?
What’s true about Troubleshooting option in the IPS profile properties?
Which of the following is NOT a type of Check Point APIavailable in R80.10?
What command can you use to have cpinfo display all installed hotfixes?
What processes does CPM control?
R80.10 management server can manage gateways with which versions installed?
When installing a dedicated R80 SmartEvent server, what is the recommended size of the root partition?
When configuring SmartEvent Initial settings, you must specify a basic topology for SmartEvent to help it calculate traffic direction for events. What is this setting called, and what are you defining?
What is not a component of Check Point SandBlast?
What is considered Hybrid Emulation Mode?
The Regulatory Compliance pane shows compliance statistics for selected regulatory standards, based on the Security Best Practice scan. Which of the following does NOT show in this pane?
What is the proper CLISH syntax to configure a default route via 192.168.255.1 in Gaia?
During inspection of your Threat Prevention logs you find four different computers having one event each with a Critical Severity. Which ofthose hosts should you try to remediate first?
What is the purpose of Priority Delta in VRRP?
Which one ofthe following processes below would not start if there was a licensing issue.
You find one of your cluster gateways showing “Down” when you run the “cphaprob stat” command. You then run the “clusterXL_admin up” on the down member but unfortunately the member continues to show down. What command do you run to determine the case?
Which deployment methods can an administrator choose when deploying the Sandblast agent?
What is the command to see cluster status in cli expert mode?
The Firewall Administrator is required to create 100 new host objects withdifferent IP addresses. What API command can he use in the script to achieve the requirement?
How long may verification of one file take for Sandblast Threat Emulation?
The Event List within the Events tab contains:
You noticed that CPU cores on the Security Gateway are usually 100% utilized and many packets were dropped. You don’t have a budget to perform a hardware upgrade at this time. To optimize drops you decide to use Priority Queues and fully enable Dynamic Dispatcher. How can you enable them?
Which of these options is an implicit MEP option?
In the Check Point Firewall Kernel Module, each Kernel is associated with a key, which specifies the type of traffic applicable to the chain module. For Stateful Mode configuration, chain modules marked with ___________ will not apply.
Jack hasfinished building his new SMS server, Red, on new hardware. He used SCP to move over the Red-old.tgz export of his old SMS server. What is the command he will use to import this into the new server?