We at Crack4sure are committed to giving students who are preparing for the Cisco 200-201 Exam the most current and reliable questions . To help people study, we've made some of our Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) exam materials available for free to everyone. You can take the Free 200-201 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
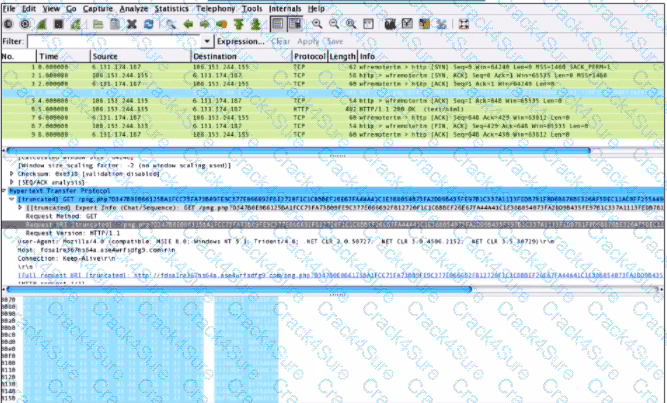
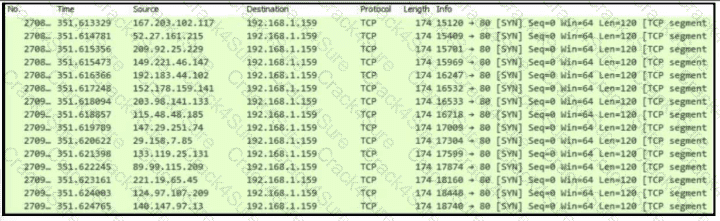
Refer to the exhibit.
What is occurring?
Which security model assumes an attacker within and outside of the network and enforces strict verification before connecting to any system or resource within the organization?
A data privacy officer at a marketing firm has received a request from a former client to delete all personally sensitive information held by the company. The firm operates globally and follows international data protection standards. The only information retained about the client is a unique customer ID, "051473912", which is not directly tied to the name, address, or any other identifiable details. Which action should the data privacy officer take?
What describes the difference when comparing attack surface and vulnerability in practice?
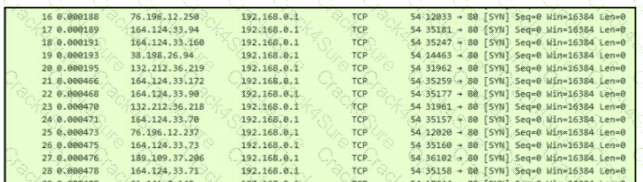
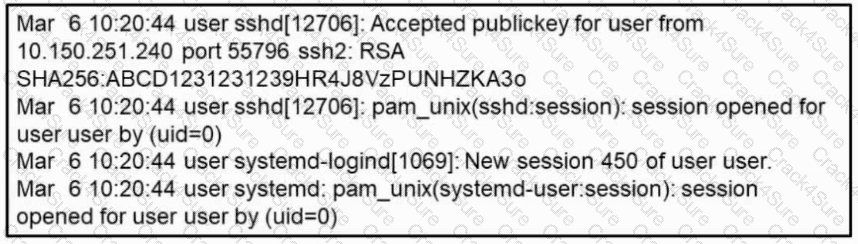
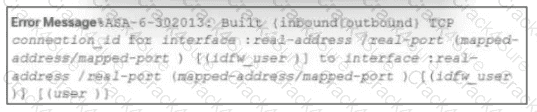
Refer to the exhibit.
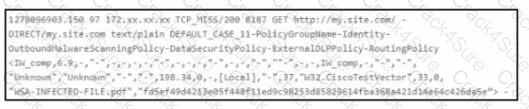
Which technology produced the log?
In digital communications, which method is recommended for securely exchanging public keys between users T0n2262144790 and D4n4126220794?
What is the purpose of command and control for network-aware malware?
Which evasion method is being used when TLS is observed between two endpoints?
What is the impact of encryption?
What is rule-based detection when compared to statistical detection?
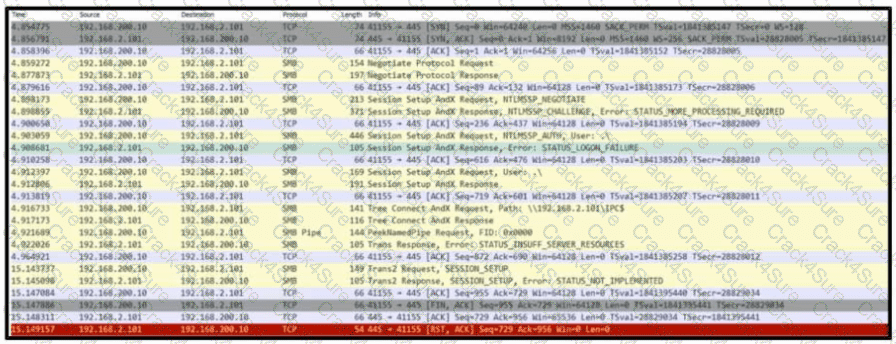
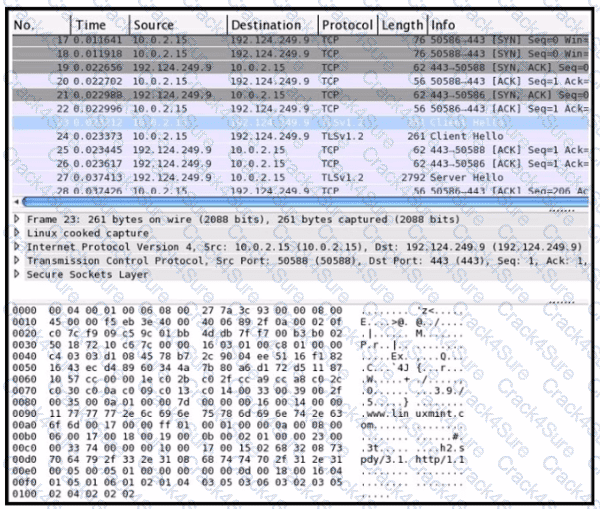
Refer to the exhibit. Based on the .pcap file, which protocol's vulnerability has been exploited to establish a session?
What describes the public key infrastructure (PKI)?
Which type of attack involves sending input commands to a web server to access data?
What is a difference between signature-based and behavior-based detection?
Which option describes indicators of attack?
What is a difference between tampered and untampered disk images?
Which type of evasion technique is accomplished by separating the traffic into smaller segments before transmitting across the network?
Refer to the exhibit.
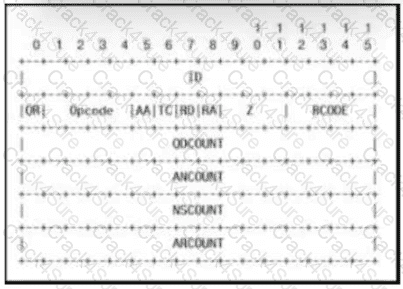
Which field contains DNS header information if the payload is a query or a response?
An engineer must investigate suspicious connections. Data has been gathered using a tcpdump command on a Linux device and saved as sandboxmatware2022-12-22.pcaps file.The engineer is trying to open the tcpdump in the Wireshark tool. What is the expected result?
Which signature impacts network traffic by causing legitimate traffic to be blocked?
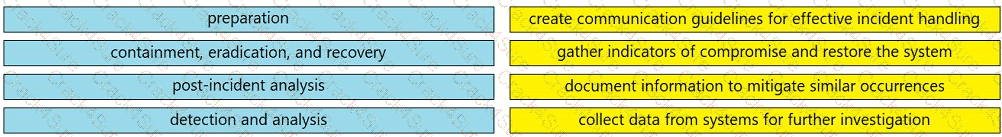
Drag and drop the elements from the left into the correct order for incident handling on the right.
Why is encryption challenging to security monitoring?
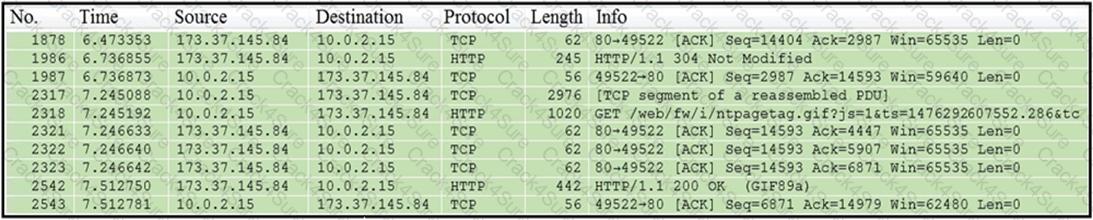
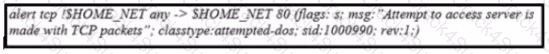
Refer to the exhibit.
Which application-level protocol is being targeted?
What describes a buffer overflow attack?
Refer to the exhibit.
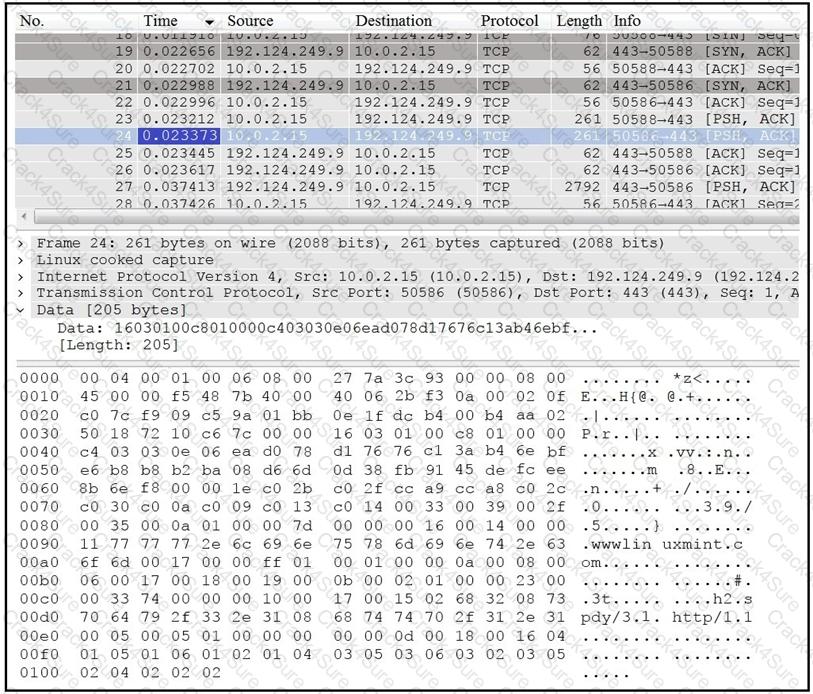
Which application protocol is in this PCAP file?
Refer to the exhibit.
Which packet contains a file that is extractable within Wireshark?
The SOC team has confirmed a potential indicator of compromise on an endpoint. The team has narrowed the executable file's type to a new trojan family. According to the NIST Computer Security Incident Handling Guide, what is the next step in handling this event?
What is the difference between deep packet inspection and stateful inspection?
Refer to the exhibit.
What does this output indicate?
Refer to the exhibit.
What is the outcome of the command?
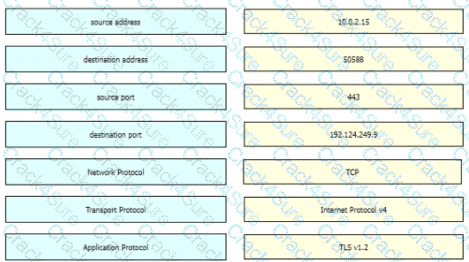
Refer to the exhibit Drag and drop the element names from the left onto the corresponding pieces of the PCAP file on the right.
What is the difference between an attack vector and an attack surface?
A security analyst reviews the firewall and observes the large number of frequent events. The analyst starts the packet capture with the Wireshark and identifies that TCP port reuse was detected incorrectly as a TCP split-handshake attack by the firewall. How must an impact from this event be categorized?
Which technique obtains information about how the system works without knowing it's design details?
A company had a recent breach and lost confidential data to a competitor. An internal investigation found out that a new junior accounting specialist logged in to the accounting server with their user ID and stole confidential data. The junior accounting specialist denies the action and claims that the attempt was done by someone else. During court proceedings, the company presents logs and CCTV camera recordings that show the malicious insider in action. Which type of evidence has the company presented?
Which list identifies the information that the client sends to the server in the negotiation phase of the TLS handshake?
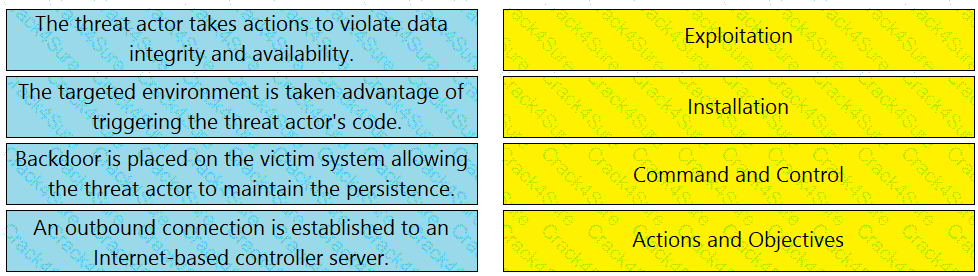
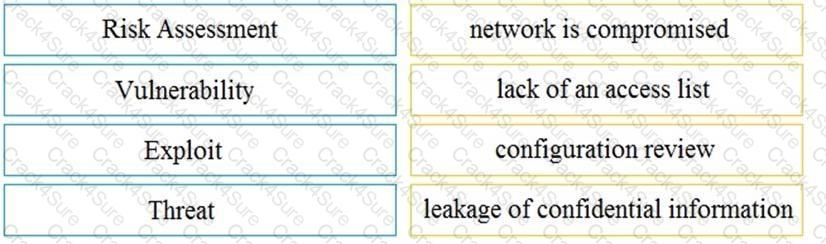
Drag and drop the event term from the left onto the description on the right.
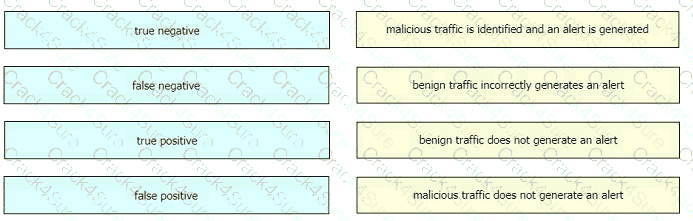
Drag and drop the definition from the left onto the phase on the right to classify intrusion events according to the Cyber Kill Chain model.
When trying to evade IDS/IPS devices, which mechanism allows the user to make the data incomprehensible without a specific key, certificate, or password?
How does statistical detection differ from rule-based detection?
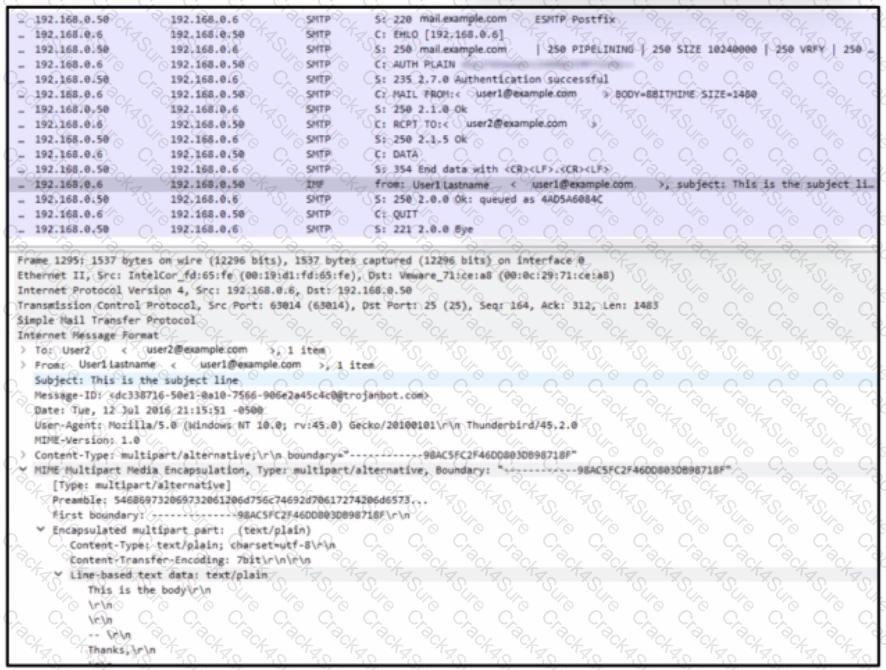
Refer to the exhibit.
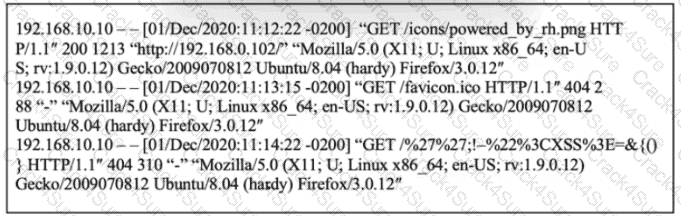
What is occurring?
An analyst is using the SIEM platform and must extract a custom property from a Cisco device and capture the phrase, "File: Clean." Which regex must the analyst import?
Which classification of cross-site scripting attack executes the payload without storing it for repeated use?
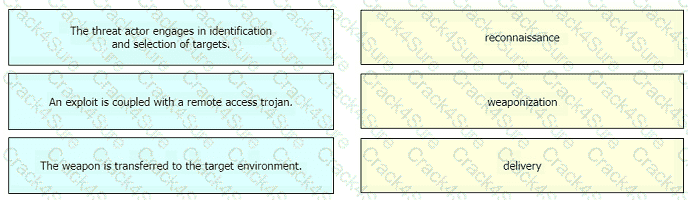
Drag and drop the definition from the left onto the phase on the right to classify intrusion events according to the Cyber Kill Chain model.
Which statement describes threat hunting?
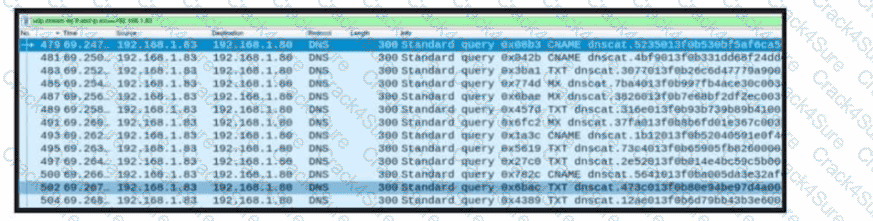
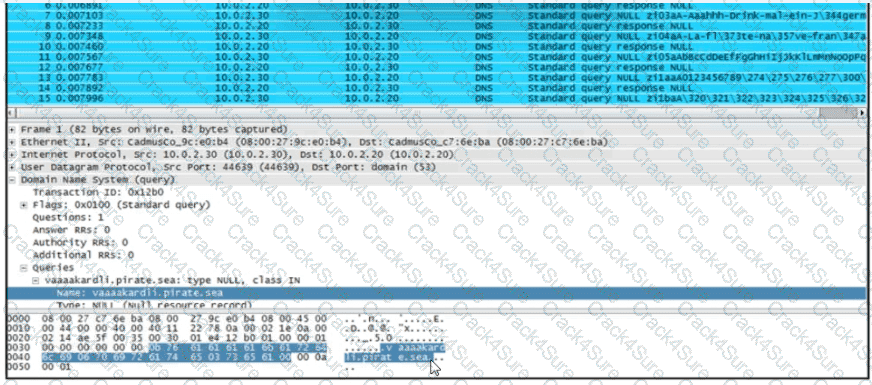
Refer to the exhibit. A network engineer received a report that a host is communicating with unknown domains on the internet. The network engineer collected packet capture but could not determine the technique or the payload used. What technique is the attacker using?
How does certificate authority impact a security system?
A user received a targeted spear-phishing email and identified it as suspicious before opening the content. To which category of the Cyber Kill Chain model does to this type of event belong?
What is the impact of encapsulation on the network?
What is a difference between SIEM and SOAR?
Which step in the incident response process researches an attacking host through logs in a SIEM?
A system administrator is ensuring that specific registry information is accurate.
Which type of configuration information does the HKEY_LOCAL_MACHINE hive contain?
Which metric is used to capture the level of access needed to launch a successful attack?
The SOC team detected an ongoing port scan. After investigation, the team concluded that the scan was targeting the company servers. According to the Cyber Kill Chain model, which step must be assigned to this type of event?
What is the difference between a threat and an exploit?
What is an attack surface as compared to a vulnerability?
What do host-based firewalls protect workstations from?
Which regular expression is needed to capture the IP address 192.168.20.232?
Refer to the exhibit.
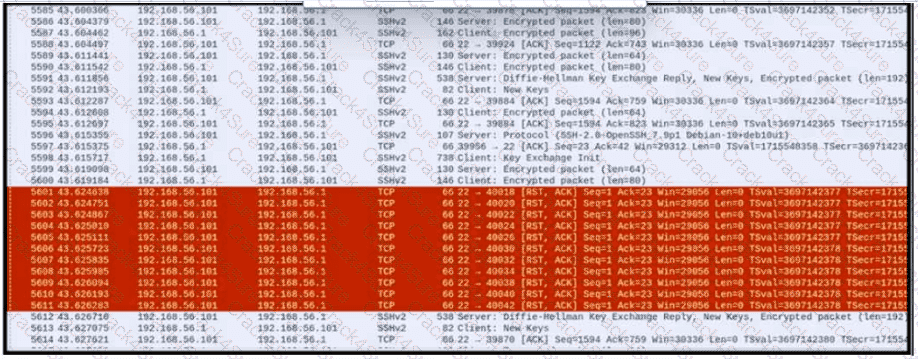
An engineer is analyzing a PCAP file after a recent breach An engineer identified that the attacker used an aggressive ARP scan to scan the hosts and found web and SSH servers. Further analysis showed several SSH Server Banner and Key Exchange Initiations. The engineer cannot see the exact data being transmitted over an encrypted channel and cannot identify how the attacker gained access How did the attacker gain access?
What is the key difference between mandatory access control (MAC) and discretionary access control (DAC)?
What is the difference between statistical detection and rule-based detection models?
What does the Zero Trust security model signify?
How is NetFlow different from traffic mirroring?
If a web server accepts input from the user and passes it to a bash shell, to which attack method is it vulnerable?
An engineer configured regular expression “.”\.(pd][Oo][Cc)|[Xx][LI][Ss]|[Pp][Pp][Tt]) HTTP/1 .[01]" on Cisco ASA firewall. What does this regular expression do?
Refer to the exhibit.
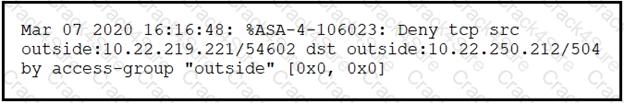
Which technology generates this log?
STION NO: 102
Refer to the exhibit.
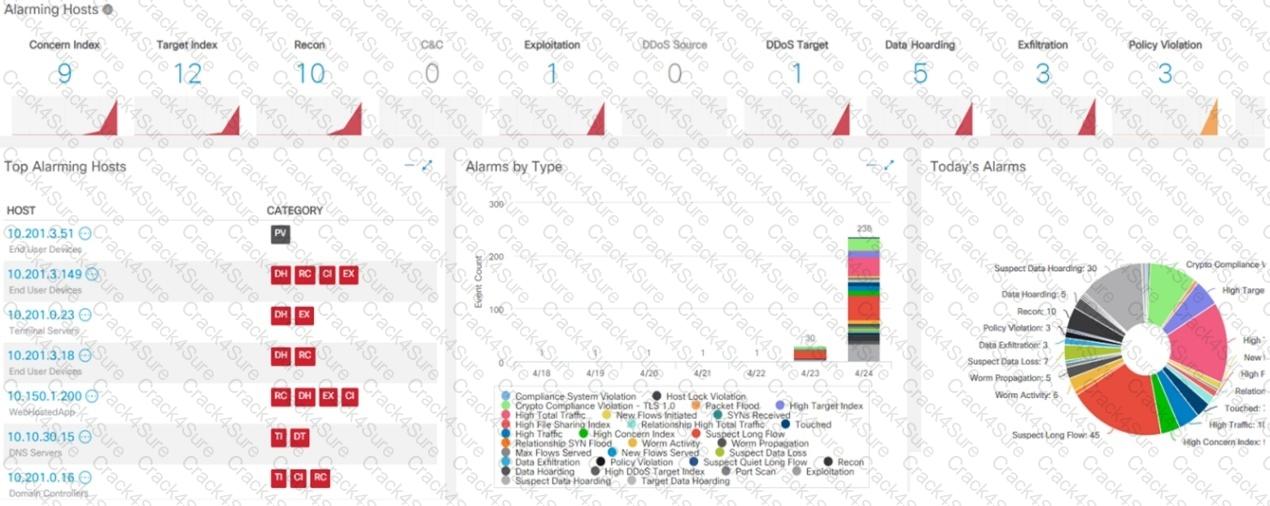
What is the potential threat identified in this Stealthwatch dashboard?
Drag and drop the security concept on the left onto the example of that concept on the right.
What is the difference between a threat and a risk?
A security specialist is investigating an incident regarding a recent major breach in the organization. The accounting data from a 24-month period is affected due to a trojan detected in a department's critical server. A security analyst investigates the incident and discovers that an incident response team member who detected a trojan during regular AV scans had made an image of the server for evidence purposes. The security analyst made animage again to compare the hashes of the two images, and they appeared to differ and do not match. Which type of evidence is the security analyst dealing with?
An offline audit log contains the source IP address of a session suspected to have exploited a vulnerability resulting in system compromise.
Which kind of evidence is this IP address?
An engineer received an alert affecting the degraded performance of a critical server Analysis showed a heavy CPU and memory load What is the next step the engineer should take to investigate this resource usage7
An engineer is working with the compliance teams to identify the data passing through the network. During analysis, the engineer informs the compliance team that external penmeter data flows contain records, writings, and artwork Internal segregated network flows contain the customer choices by gender, addresses, and product preferences by age. The engineer must identify protected data. Which two types of data must be identified'? (Choose two.)
What is a difference between tampered and untampered disk images?
A security team receives a ticket to investigate suspicious emails sent to company employees from known malicious domains. Further analysis shows that a targeted phishing attempt was successfully blocked by the company’s email antivirus. At which step of the Cyber Kill Chain did the security team mitigate this attack?
What describes the impact of false-positive alerts compared to false-negative alerts?
Which attack method is being used when an attacker tries to compromise a network with an authentication system that uses only 4-digit numeric passwords and no username?
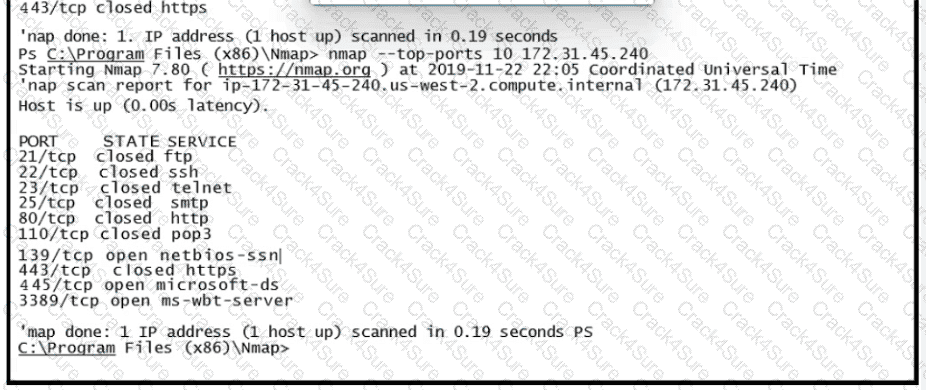
Refer to the exhibit.
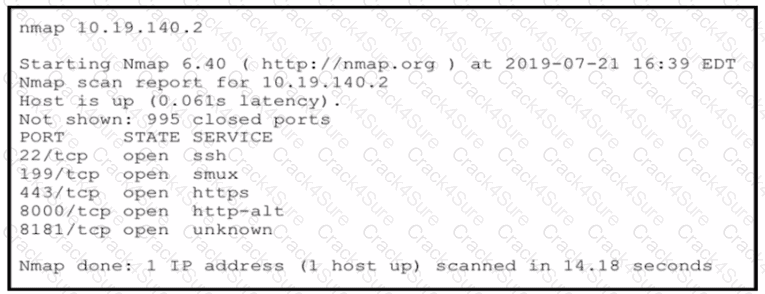
An attacker gained initial access to the company s network and ran an Nmap scan to advance with the lateral movement technique and to search the sensitive data Which two elements can an attacker identify from the scan? (Choose two.)
What are two differences and benefits of packet filtering, stateful firewalling, and deep packet inspections? (Choose two.)
What is the difference between the ACK flag and the RST flag in the NetFlow log session?
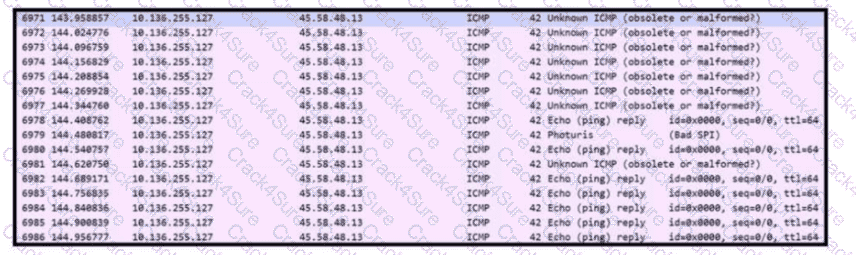
Refer to the exhibit. An engineer received a ticket to analyze unusual network traffic. What is occurring?
A security analyst notices a sudden surge of incoming traffic and detects unknown packets from unknown senders After further investigation, the analyst learns that customers claim that they cannot access company servers According to NIST SP800-61, in which phase of the incident response process is the analyst?
An automotive company provides new types of engines and special brakes for rally sports cars. The company has a database of inventions and patents for their engines and technical information Customers can access the database through the company's website after they register and identify themselves. Which type of protected data is accessed by customers?
Refer to the exhibit.
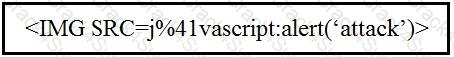
Which kind of attack method is depicted in this string?
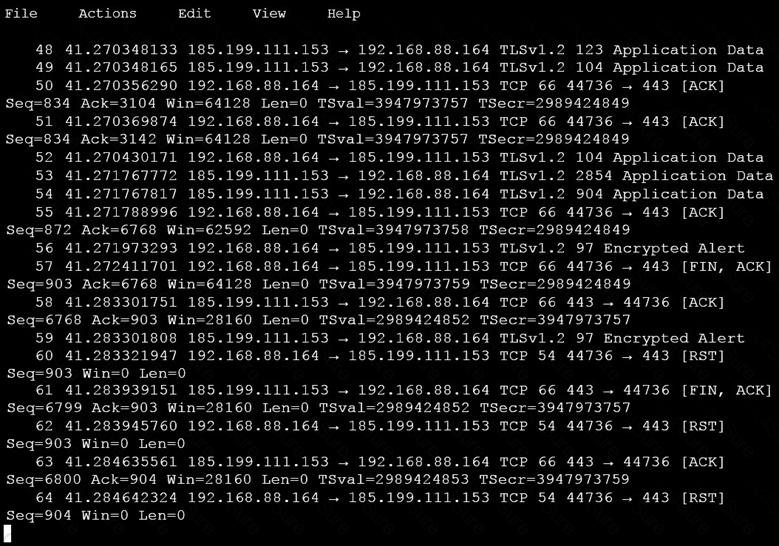
Refer to the exhibit.
What is shown in this PCAP file?
Which attack method intercepts traffic on a switched network?
A company recently encountered a breach. Critical services went through a disturbance and the integrity of the data was altered. An engineer is investigating the issue and searching through the logs in the SIEM. Which phase of the incident response is an engineer working on?
At which layer is deep packet inspection investigated on a firewall?
An analyst performs traffic analysis to detect data exfiltration and identifies a high frequency of DNS requests in a small period of time Which technology makes this behavior feasible?
Which event is a vishing attack?
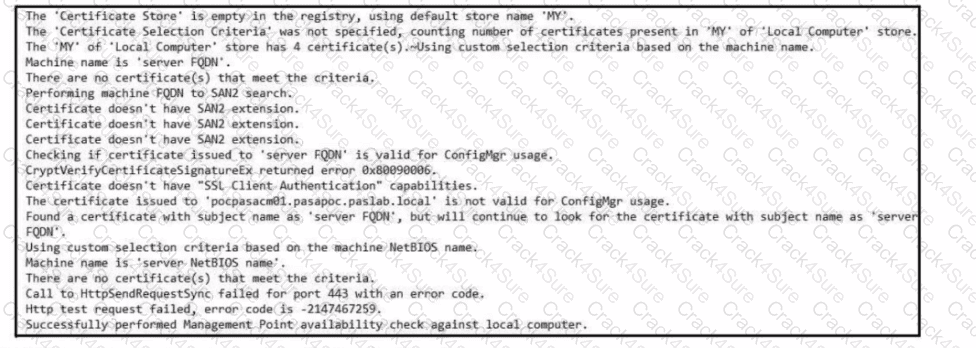
Refer to the exhibit. Which set of actions must an engineer perform to identify and fix this issue?
What makes HTTPS traffic difficult to monitor?
When communicating via TLS, the client initiates the handshake to the server and the server responds back with its certificate for identification.
Which information is available on the server certificate?
What is the impact of false positive alerts on business compared to true positive?
Which open-sourced packet capture tool uses Linux and Mac OS X operating systems?
Refer to the exhibit.
What is occurring?
Refer to the exhibit.
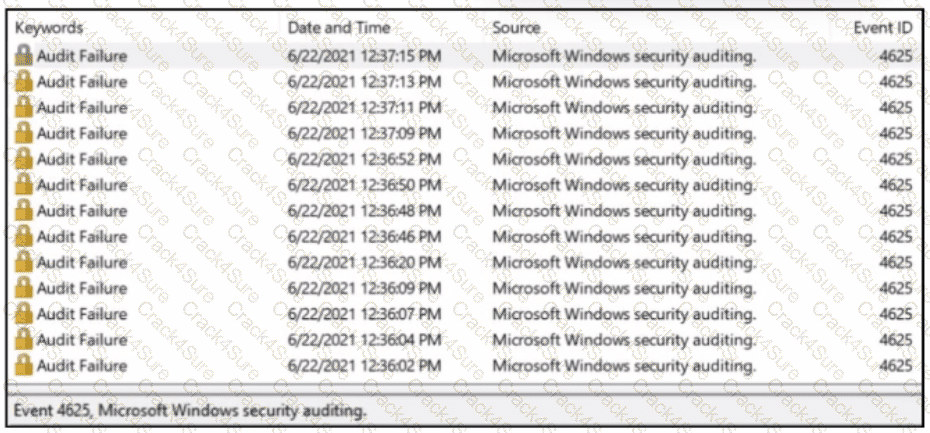
A SOC analyst received a message from SIEM about abnormal activity on the Windows server The analyst checked the Windows event log and saw numerous Audit Failures logs. What is occurring?
What is the definition of threat intelligence in the context of cybersecurity?
What is the difference between the ACK flag and the RST flag?
Refer to exhibit.
An engineer is Investigating an Intrusion and Is analyzing the pcap file. Which two key elements must an engineer consider? (Choose two.)
What is the difference between inline traffic interrogation and traffic mirroring?
A security engineer must protect the company from known issues that trigger adware. Recently new incident has been raised that could harm the system. Which security concepts are present in this scenario?
Which access control should a chief information security officer select to protect extremely sensitive data categorized at various levels of confidentiality?
Refer to the exhibit. What occurred on this system based on this output?
At a company party a guest asks questions about the company’s user account format and password complexity. How is this type of conversation classified?
A security analyst received a ticket about suspicious traffic from one of the workstations. During the investigation, the analyst discovered that the workstation was communicating with an external IP. The analyst could not investigate further and escalated the case to a T2 security analyst. What are the two data visibility challenges that the security analyst should identify? (Choose two.)
Which category relates to improper use or disclosure of PII data?
What is a difference between a threat and a risk?
While viewing packet capture data, an analyst sees that one IP is sending and receiving traffic for multiple devices by modifying the IP header.
Which technology makes this behavior possible?
A security engineer notices confidential data being exfiltrated to a domain "Ranso4134-mware31-895" address that is attributed to a known advanced persistent threat group The engineer discovers that the activity is part of a real attack and not a network misconfiguration. Which category does this event fall under as defined in the Cyber Kill Chain?
An engineer received an alert affecting the degraded performance of a critical server Analysis showed a heavy CPU and memory load. What is the next step the engineer should take to investigate this resource usage?
What is a key difference between a tampered and an untampered disk image during a forensic investigation?
What is a difference between authorization and authentication from an access control perspective?
What describes the vulnerability management process?
A company encountered a breach on its web servers using IIS 7 5 Dunng the investigation, an engineer discovered that an attacker read and altered the data on a secure communication using TLS 1 2 and intercepted sensitive information by downgrading a connection to export-grade cryptography. The engineer must mitigate similar incidents in the future and ensure that clients and servers always negotiate with the most secure protocol versions and cryptographic parameters. Which action does the engineer recommend?
An analyst is investigating a host in the network that appears to be communicating to a command and control server on the Internet. After collecting this packet capture, the analyst cannot determine the technique and payload used for the communication.
Which obfuscation technique is the attacker using?
What describes the defense-m-depth principle?
What is a benefit of agent-based protection when compared to agentless protection?
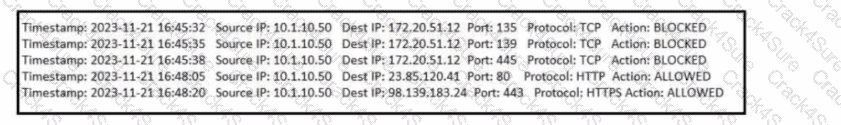
Refer to the exhibit. What type of event is occurring?
Which data format is the most efficient to build a baseline of traffic seen over an extended period of time?
Refer to the exhibit.
During the analysis of a suspicious scanning activity incident, an analyst discovered multiple local TCP connection events Which technology provided these logs?
What is a difference between SOAR and SIEM?
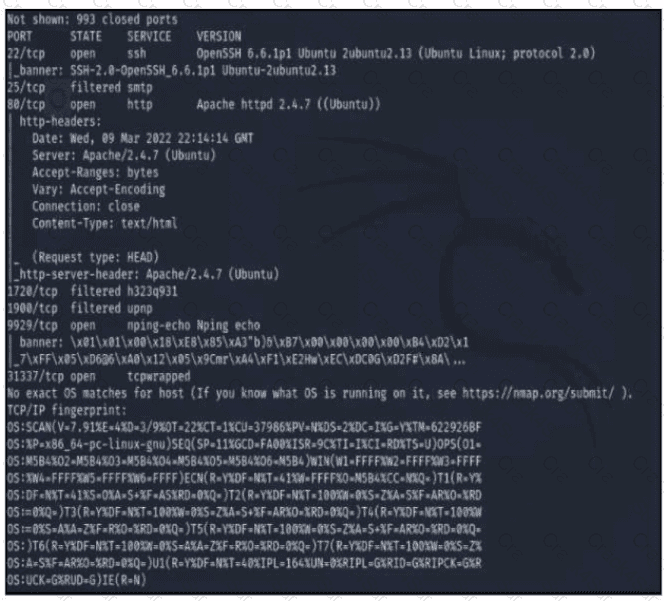
Refer to the exhibit A penetration tester runs the Nmap scan against the company server to uncover possible vulnerabilities and exploit them Which two elements can the penetration tester identity from the scan results? (Choose two.)
Which type of access control depends on the job function of the user?
An investigator is examining a copy of an ISO file that is stored in CDFS format. What type of evidence is this file?
A threat actor penetrated an organization's network. Using the 5-tuple approach, which data points should the analyst use to isolate the compromised host in a grouped set of logs?
According to the September 2020 threat intelligence feeds a new malware called Egregor was introduced and used in many attacks. Distnbution of Egregor is pnmanly through a Cobalt Strike that has been installed on victim's workstations using RDP exploits Malware exfiltrates the victim's data to a command and control server. The data is used to force victims pay or lose it by publicly releasing it. Which type of attack is described?
Which data capture includes payload and header information?
What is the difference between mandatory access control (MAC) and discretionary access control (DAC)?
What is the difference between discretionary access control (DAC) and role-based access control (RBAC)?
What is a Heartbleed vulnerability?
What is the dataflow set in the NetFlow flow-record format?
Which evasion method involves performing actions slower than normal to prevent detection?
Which action matches the weaponization step of the Cyber Kill Chain Model?
Refer to the exhibit.
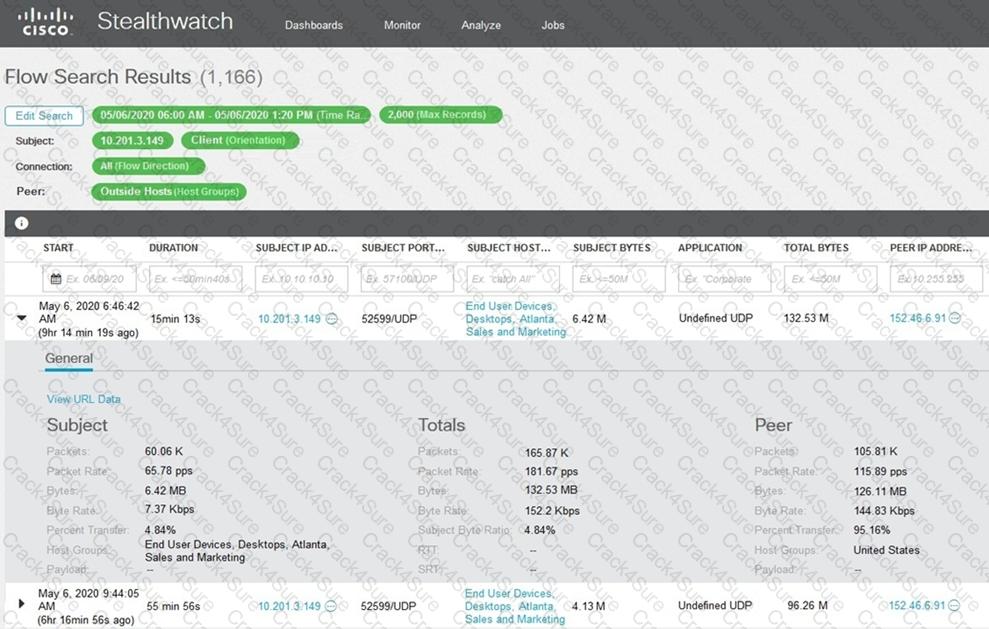
What is the potential threat identified in this Stealthwatch dashboard?
What is an incident response plan?
What is the difference between deep packet inspection and stateful inspection?
3 Months Free Update
3 Months Free Update
3 Months Free Update