We at Crack4sure are committed to giving students who are preparing for the Cisco 300-215 Exam the most current and reliable questions . To help people study, we've made some of our Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR) exam materials available for free to everyone. You can take the Free 300-215 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
An organization experienced a ransomware attack that resulted in the successful infection of their workstations within their network. As part of the incident response process, the organization's cybersecurity team must prepare a comprehensive root cause analysis report. This report aims to identify the primary factor or factors responsible for the successful ransomware attack and to formulate effective strategies to prevent similar incidents in the future. In this context, what should the cybersecurity engineer emphasize in the root cause analysis report to demonstrate the underlying cause of the incident?
A security analyst receives a notification from SIEM that an internal host has active connections to Tor exit nodes. The analyst investigates SIEM events related to the workstation and identifies that the host scans networks for servers with an opened TCP port 1433 An antivirus scan of the workstation does not determine any suspicious activity Which two actions must the analyst take to mitigate this behavior? (Choose two.)
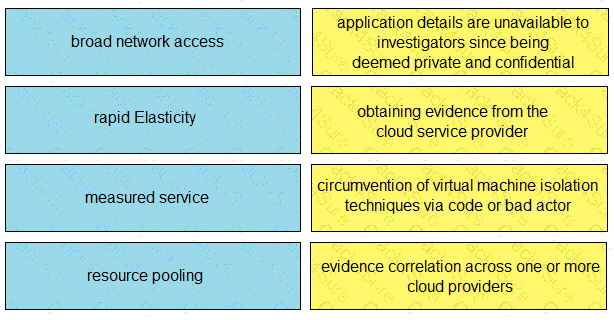
Drag and drop the cloud characteristic from the left onto the challenges presented for gathering evidence on the right.
Which information is provided about the object file by the “-h” option in the objdump line command objdump –b oasys –m vax –h fu.o?
An attacker embedded a macro within a word processing file opened by a user in an organization’s legal department. The attacker used this technique to gain access to confidential financial data. Which two recommendations should a security expert make to mitigate this type of attack? (Choose two.)
What is the purpose of YARA rules in malware analysis and now do the rules atd in identifying, classifying, and documenting malware?
Refer to the exhibit.
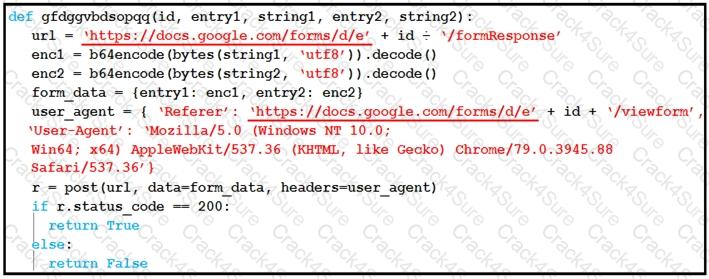
Which type of code is being used?
A threat intelligence report identifies an outbreak of a new ransomware strain spreading via phishing emails that contain malicious URLs. A compromised cloud service provider, XYZCloud, is managing the SMTP servers that are sending the phishing emails. A security analyst reviews the potential phishing emails and identifies that the email is coming from XYZCloud. The user has not clicked the embedded malicious URL. What is the next step that the security analyst should take to identify risk to the organization?
Which scripts will search a log file for the IP address of 192.168.100.100 and create an output file named parsed_host.log while printing results to the console?
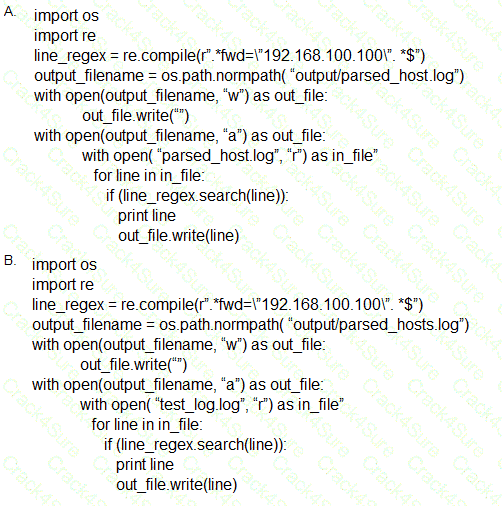
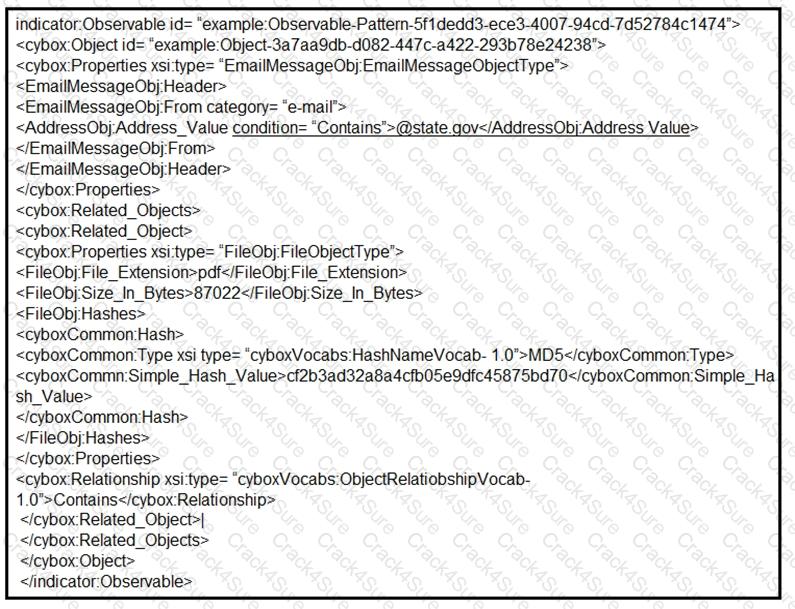
Refer to the exhibit.
What is occurring?
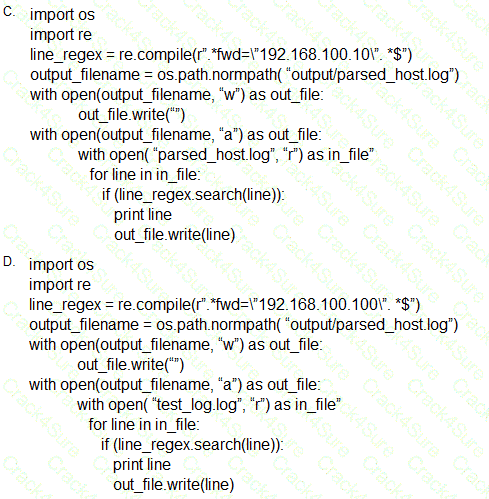
Refer to the exhibit.
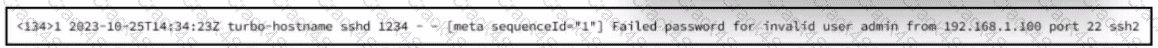
A security analyst is reviewing alerts from the SIEM system that was just implemented and notices a possible indication of an attack because the SSHD system just went live and there should be nobody using it. Which action should the analyst take to respond to the alert?
In a secure government communication network, an automated alert indicates the presence of anomalous DLL files injected into the system memory during a routine update of communication protocols. These DLL files are exhibiting beaconing behavior to a satellite IP known for signal interception risks. Concurrently, there is an uptick in encrypted traffic volumes that suggests possible data exfiltration. Which set of actions should the security engineer prioritize?
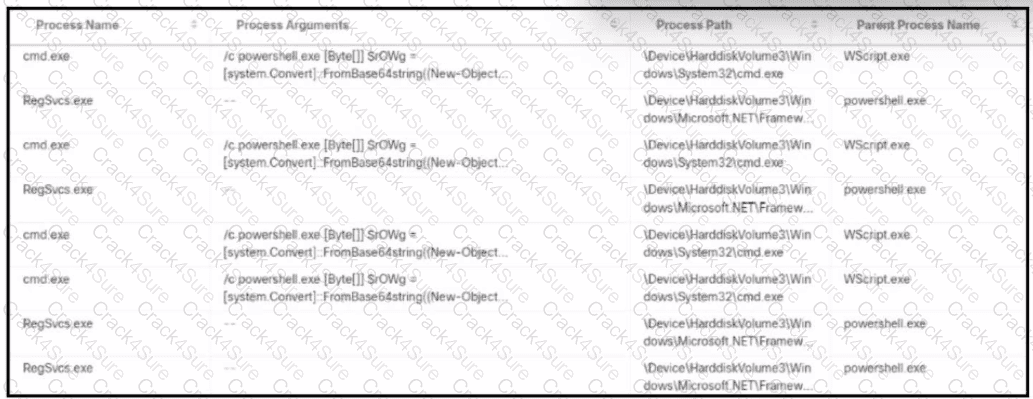
Refer to the exhibit.
Refer to the exhibit. 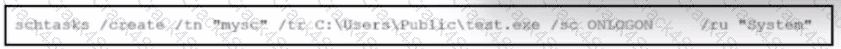
What is occurring?
An insider scattered multiple USB flash drives with zero-day malware in a company HQ building. Many employees connected the USB flash drives to their workstations. An attacker was able to get access to endpoints from outside, steal user credentials, and exfiltrate confidential information from internal web resources. Which two steps prevent these types of security incidents in the future? (Choose two.)
Refer to the exhibit.
Which two actions should be taken as a result of this information? (Choose two.)
A cybersecurity analyst must identify an unknown service causing high CPU on a Windows server. What tool should be used?
multiple machines behave abnormally. A sandbox analysis reveals malware. What must the administrator determine next?
An employee receives an email from a “trusted” person containing a hyperlink that is malvertising. The employee clicks the link and the malware downloads. An information analyst observes an alert at the SIEM and engages the cybersecurity team to conduct an analysis of this incident in accordance with the incident response plan. Which event detail should be included in this root cause analysis?
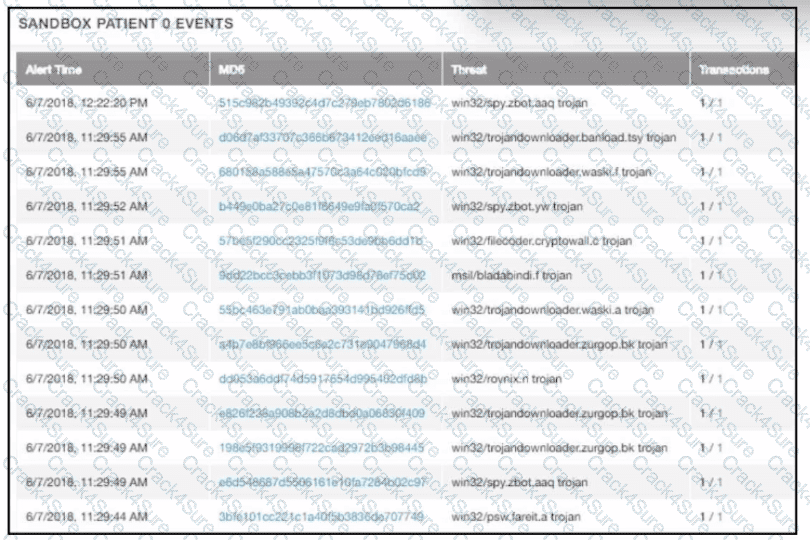
Refer to the exhibit.
An alert came with a potentially suspicious activity from a machine in HR department. Which two IOCs should the security analyst flag? (Choose two.)
An engineer is analyzing a ticket for an unexpected server shutdown and discovers that the web-server ran out of useable memory and crashed.
Which data is needed for further investigation?
A security team received an alert of suspicious activity on a user’s Internet browser. The user’s anti-virus software indicated that the file attempted to create a fake recycle bin folder and connect to an external IP address. Which two actions should be taken by the security analyst with the executable file for further analysis? (Choose two.)
What can the blue team achieve by using Hex Fiend against a piece of malware?
What is the function of a disassembler?
A company had a recent data leak incident. A security engineer investigating the incident discovered that a malicious link was accessed by multiple employees. Further investigation revealed targeted phishing attack attempts on macOS systems, which led to backdoor installations and data compromise. Which two security solutions should a security engineer recommend to mitigate similar attacks in the future? (Choose two.)
Refer to the exhibit.
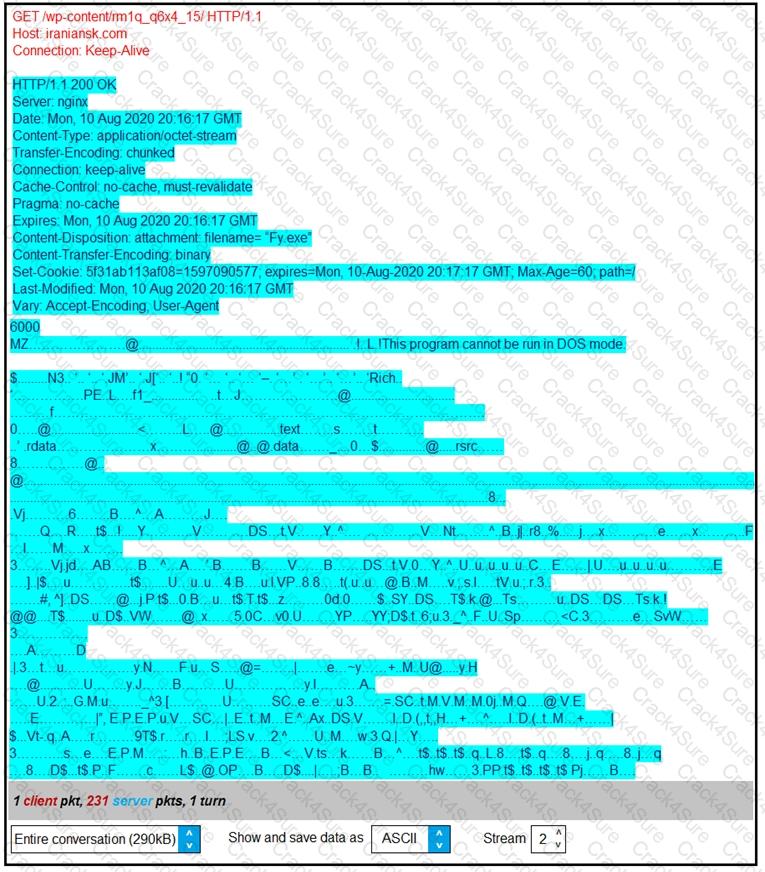
According to the Wireshark output, what are two indicators of compromise for detecting an Emotet malware download? (Choose two.)
A website administrator has an output of an FTP session that runs nightly to download and unzip files to a local staging server. The download includes thousands of files, and the manual process used to find how many files failed to download is time-consuming. The administrator is working on a PowerShell script that will parse a log file and summarize how many files were successfully downloaded versus ones that failed. Which script will read the contents of the file one line at a time and return a collection of objects?
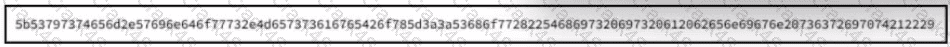
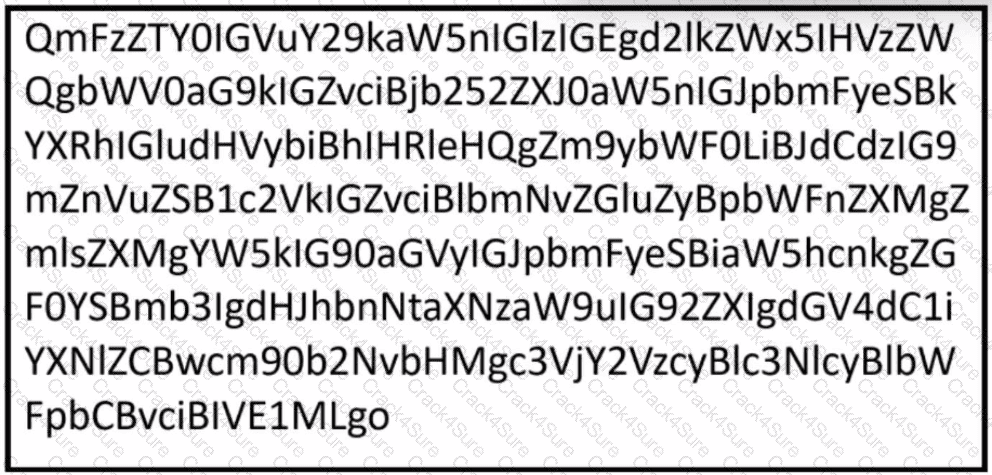
Refer to the exhibit.
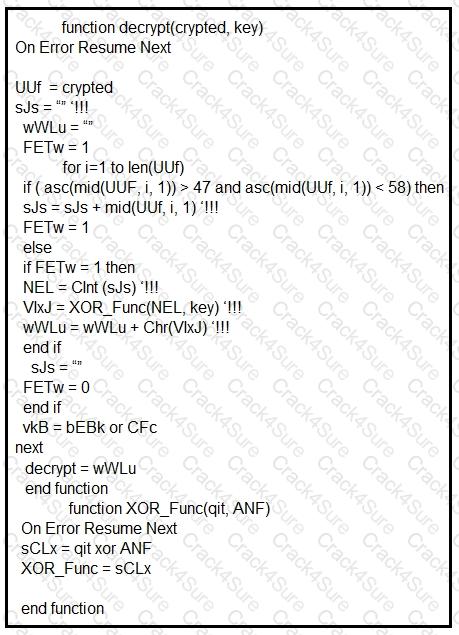
Which type of code created the snippet?
A scanner detected a malware-infected file on an endpoint that is attempting to beacon to an external site. An analyst has reviewed the IPS and SIEM logs but is unable to identify the file’s behavior. Which logs should be reviewed next to evaluate this file further?
Refer to the exhibit.
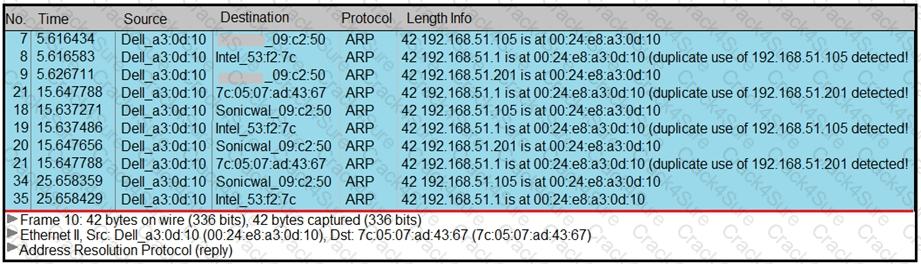
A security analyst notices unusual connections while monitoring traffic. What is the attack vector, and which action should be taken to prevent this type of event?
What is an issue with digital forensics in cloud environments, from a security point of view?
Refer to the exhibit.

Which type of code is shown?
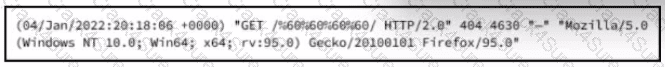
Rotor to the exhibit.
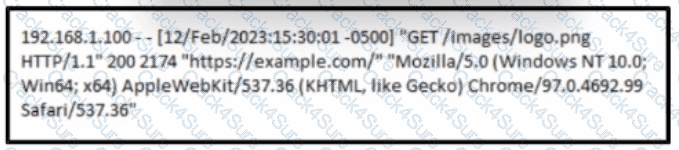
A cybersecurity analyst must analyst the logs from an Apache server for the client. The concern is that an offboarded employee home IP address was potentially used to access the company web server via a still active VPN connection Based on this log entry, what should an analyst conclude?
3 Months Free Update
3 Months Free Update
3 Months Free Update