We at Crack4sure are committed to giving students who are preparing for the Cisco 300-715 Exam the most current and reliable questions . To help people study, we've made some of our Implementing and Configuring Cisco Identity Services Engine (SISE) v4.0 (300-715 SISE) exam materials available for free to everyone. You can take the Free 300-715 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
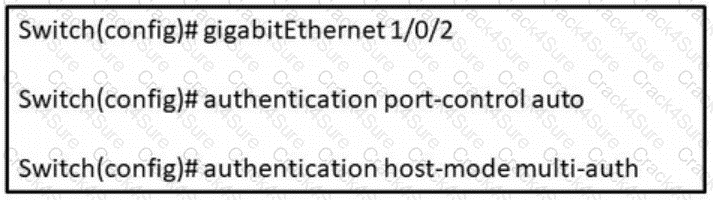
Refer to the exhibit. In which scenario does this switch configuration apply?
An engineer is assigned to enhance security across the campus network. The task is to enable MAB across all access switches in the network. Which command must be entered on the switch to enable MAB?
The security engineer for a company has recently deployed Cisco ISE to perform centralized authentication of all network device logins using TACACS+ against the local AD domain. Some of the other network engineers are having a hard time remembering to enter their AD account password instead of the local admin password that they have used for years. The security engineer wants to change the password prompt to "Use Local AD Password:" as a way of providing a hint to the network engineers when logging in. Under which page in Cisco ISE would this change be made?
An engineer is creating a new authorization policy to give the endpoints access to VLAN 310 upon successful authentication The administrator tests the 802.1X authentication for the endpoint and sees that it is authenticating successfully What must be done to ensure that the endpoint is placed into the correct VLAN?
Which two responses from the RADIUS server to NAS are valid during the authentication process? (Choose two)
When planning for the deployment of Cisco ISE, an organization's security policy dictates that they must use network access authentication via RADIUS. It also states that the deployment provide an adequate amount of security and visibility for the hosts on the network. Why should the engineer configure MAB in this situation?
An engineer is configuring web authentication and needs to allow specific protocols to permit DNS traffic. Which type of access list should be used for this configuration?
An engineer is configuring a guest password policy and needs to ensure that the password complexity requirements are set to mitigate brute force attacks. Which two requirement complete this policy? (Choose two)
A policy is being created in order to provide device administration access to the switches on a network. There is a requirement to ensure that if the session is not actively being used, after 10 minutes, it will be disconnected. Which task must be configured in order to meet this requirement?
An engineer is starting to implement a wired 802.1X project throughout the campus. The task is for failed authentication to be logged to Cisco ISE and also have a minimal impact on the users. Which command must the engineer configure?
A network engineer needs to deploy 802.1x using Cisco ISE in a wired network environment where thin clients download their system image upon bootup using PXE. For which mode must the switch ports be configured?
Which type of identity store allows for creating single-use access credentials in Cisco ISE?
An administrator needs to allow guest devices to connect to a private network without requiring usernames and passwords. Which two features must be configured to allow for this? (Choose two.)
A Cisco ISE administrator needs to ensure that guest endpoint registrations are only valid for one day When testing the guest policy flow, the administrator sees that the Cisco ISE does not delete the endpoint in the Guest Endpoints identity store after one day and allows access to the guest network after that period. Which configuration is causing this problem?
An engineer is configuring TACACS+ within Cisco ISE for use with a non-Cisco network device. They need to send special attributes in the Access-Accept response to ensure that the users are given the appropriate access. What must be configured to accomplish this'?
MacOS users are complaining about having to read through wordy instructions when remediating their workstations to gam access to the network Which alternate method should be used to tell users how to remediate?
An engineer must use Cisco ISE to provide network access to endpoints that cannot support 802.1X. The endpoint MAC addresses must be allowlisted by configuring an endpoint identity group. These configurations were performed:
• configured an identity group named allowlist
• configured the endpoints to use the MAC address of incompatible 802.1X devices
• added the endpoints to the allowlist identity group
• configured an authentication policy for MAB users
What must be configured?
A network administrator adds network access devices to Cisco ISE. After a security breach, the management team mandates that all network devices must comply with certain standards. All network devices must authenticate through Cisco ISE. Some devices use nondefault CoA ports.
What must be configured in Cisco ISE?
An administrator is configuring posture with Cisco ISE and wants to check that specific services are present on the workstations that are attempting to access the network. What must be configured to accomplish this goal?
A network security administrator wants to integrate Cisco ISE with Active Directory. Which configuration action must the security administrator take to accomplish the task?
A network engineer needs to ensure that the access credentials are not exposed during the 802.1x authentication among components. Which two protocols should complete this task?
An engineer must use Cisco ISE to provide network access to endpoints that cannot support 802.1X. The endpoint MAC addresses must be allowlisted by configuring an endpoint identity group. These configurations were performed:
Configured an identity group named allowlist
Configured the endpoints to use the MAC address of incompatible 802.1X devices
Added the endpoints to the allowlist identity group
Configured an authentication policy for MAB users
What must be configured?
What is an advantage of TACACS+ versus RADIUS authentication when reviewing reports in Cisco ISE?
An engineer is working with a distributed deployment of Cisco ISE and needs to configure various network probes to collect a set of attributes from the used to accomplish this task?
What is a valid status of an endpoint attribute during the device registration process?
What service can be enabled on the Cisco ISE node to identity the types of devices connecting to a network?
Which two endpoint compliance statuses are possible? (Choose two.)
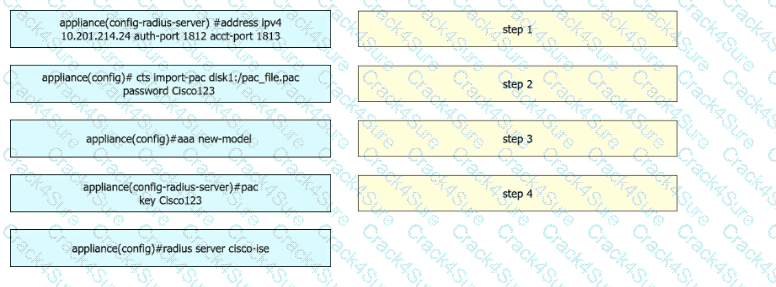
A security engineer configures a Cisco Catalyst switch to use Cisco TrustSec. The engineer must define the PAC key to authenticate the switch to Cisco IISE. Drag and drop the commands from the left into sequence on the right. Not all options are used.
Refer to the exhibit:
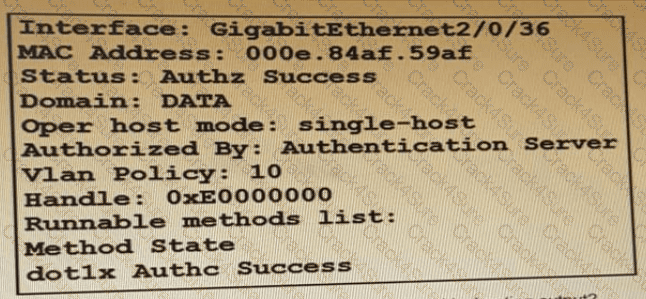
Which command is typed within the CU of a switch to view the troubleshooting output?
An administrator plans to use Cisco ISE to deploy posture policies to assess Microsoft Windows endpoints that run Cisco Secure Client. The administrator wants to minimize the occurrence of messages related to unknown posture profiles if Cisco ISE fails to determine the posture of the endpoint. Secure Client is deployed to all the endpoints. and all the required Cisco ISE authentication, authorization, and posture policy configurations were performed. Which action must be taken next to complete the configuration?
A Cisco device has a port configured in multi-authentication mode and is accepting connections only from hosts assigned the SGT of SGT_0422048549 The VLAN trunk link supports a maximum of 8 VLANS What is the reason for these restrictions?
Which two features must be used on Cisco ISE to enable the TACACS. feature? (Choose two)
Which use case validates a change of authorization?
What must match between Cisco ISE and the network access device to successfully authenticate endpoints?
An organization is adding nodes to their Cisco ISE deployment and has two nodes designated as primary and secondary PAN and MnT nodes. The organization also has four PSNs An administrator is adding two more PSNs to this deployment but is having problems adding one of them What is the problem?
An administrator is editing a csv list of endpoints and wants to reprofile some of the devices indefinitely before importing the list into Cisco ISE. Which field and Boolean value must be changed for the devices before the list is reimported?
A network engineer is configuring Cisco TrustSec and needs to ensure that the Security Group Tag is being transmitted between two devices Where in the Layer 2 frame should this be verified?
An engineer is assigned to enhance security across the campus network. The task is to enable MAB across all access switches in the network. Which command must be entered on the switch to enable MAB?
Which platform does a Windows-based device download the Network Assistant Manager from?
What does the dot1x system-auth-control command do?
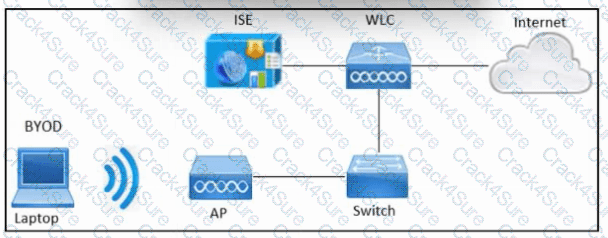
Refer to the exhibit. An engineer must configure BYOD in Cisco ISE. A single SSID must be used to allow BYOD devices to connect to the network. These configurations have been performed on Wireless LAN Controller already:
RADIUS server
BYOD-Dot1x SSID
Which two configurations must be done in Cisco ISE to meet the requirement? (Choose two.)
An engineer is configuring a new Cisco ISE node. Context-sensitive information must be shared between the Cisco ISE and a Cisco ASA. Which persona must be enabled?
An administrator is attempting to replace the built-in self-signed certificates on a Cisco ISE appliance. The CA is requesting some information about the appliance in order to sign the new certificate. What must be done in order to provide the CA this information?
An administrator is configuring the Native Supplicant Profile to be used with the Cisco ISE posture agents and needs to test the connection using wired devices to determine which profile settings are available. Which two configuration settings should be used to accomplish this task? (Choose two.)
An administrator is trying to collect metadata information about the traffic going across the network to gam added visibility into the hosts. This Information will be used to create profiling policies for devices us mg Cisco ISE so that network access policies can be used What must be done to accomplish this task?
Refer to the exhibit.
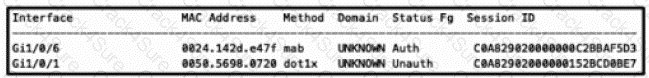
An engineer is configuring a client but cannot authenticate to Cisco ISE During troubleshooting, the show authentication sessions command was issued to display the authentication status of each port Which command gives additional information to help identify the problem with the authentication?
An engineer is deploying a new Cisco ISE environment for a company. The company wants the deployment to use TACACS+. The engineer verifies that Cisco ISE has a Device Administration license. What must be configured to enable TACACS+ operations?
Which two roles are taken on by the administration person within a Cisco ISE distributed environment? (Choose two.)
What should be considered when configuring certificates for BYOD?
An endpoint certificate is mandatory for the Cisco ISE BYOD
A network administrator is configuring a secondary cisco ISE node from the backup configuration of the primary cisco ISE node to create a high availability pair The Cisco ISE CA certificates and keys must be manually backed up from the primary Cisco ISE and copied into the secondary Cisco ISE Which command most be issued for this to work?
If a user reports a device lost or stolen, which portal should be used to prevent the device from accessing the network while still providing information about why the device is blocked?
An engineer must configure guest access on Cisco ISE for company visitors. Which step must be taken on the Cisco ISE PSNs before a guest portal is configured?
An administrator is adding a switch to a network that is running Cisco ISE and is only for IP Phones The phones do not have the ability to authenticate via 802 1X Which command is needed on each switch port for authentication?
An engineer is configuring a posture policy for Windows 10 endpoints and wants to ensure that users in each AD group have different conditions to meet to be compliant. What must be done to accomplish this task?
What is needed to configure wireless guest access on the network?
An engineer wants to learn more about Cisco ISE and deployed a new lab with two nodes. Which two persona configurations allow the engineer to successfully test redundancy of a failed node? (Choose two.)
In a Cisco ISE split deployment model, which load is split between the nodes?
What is the purpose of the ip http server command on a switch?
Which statement about configuring certificates for BYOD is true?
What is a difference between RADIUS versus TACACS+ with regards to packet encryption?
An administrator is configuring new probes to use with Cisco ISE and wants to use metadata to help profile the endpoints. The metadata must contain traffic information relating to the endpoints instead of industry-standard protocol information Which probe should be enabled to meet these requirements?
Which advanced option within a WLAN must be enabled to trigger Central Web Authentication for Wireless users on AireOS controller?
An administrator is configuring a switch port for use with 802 1X What must be done so that the port will allow voice and multiple data endpoints?
An engineer is starting to implement a wired 802.1X project throughout the campus. The task is to ensure that the authentication procedure is disabled on the ports but still allows all endpoints to connect to the network. Which port-control option must the engineer configure?
An engineer is working with a distributed deployment of Cisco ISE and needs to configure various network probes to collect a set of attributes from the endpoints on the network. Which node should be used to accomplish this task?
Which Cisco ISE deployment model provides redundancy by having every node in the deployment configured with the Administration. Policy Service, and Monitoring personas to protect from a complete node failure?
An administrator is configuring sponsored guest access using Cisco ISE Access must be restricted to the sponsor portal to ensure that only necessary employees can issue sponsored accounts and employees must be classified to do so What must be done to accomplish this task?
An engineer is configuring sponsored guest access and needs to limit each sponsored guest to a maximum of two devices. There are other guest services in production that rely on the default guest types. How should this configuration change be made without disrupting the other guest services currently offering three or more guest devices per user?
An engineer is working on a switch and must tag packets with SGT values such that it learns via SXP. Which command must be entered to meet this requirement?
An adminístrator is migrating device administration access to Cisco ISE from the legacy TACACS+ solution that used only privilege 1 and 15 access levels. The organization requires more granular controls of the privileges and wants to customize access levels 2-5 to correspond with different roles and access needs. Besides defining a new shell profile in Cisco ISE. what must be done to accomplish this configuration?
An engineer is deploying a new guest WLAN for a company. The company wants this WLAN to use a sponsored guest portal for secure guest access. The wireless LAN controller must direct the guests to a web page on Cisco ISE for authentication. Which type of authentication must be configured for the guest portal in Cisco ISE?
An engineer is configuring Cisco ISE to reprofile endpoints based only on new requests of INIT-REBOOT and SELECTING message types. Which probe should be used to accomplish this task?
Which two components are required for creating a Native Supplicant Profile within a BYOD flow? (Choose two)
The Cisco Wireless LAN Controller and guest portal must be set up in Cisco ISE. These configurations were performed:
• configured all the required Cisco Wireless LAN Controller configurations
• added the wireless controller to Cisco ISE network devices
• created an endpoint identity group
• configured credentials to be sent by email
• configured the SMTP server
• configured an authorization profile with redirection to the guest portal and redirected the access control list
• configured an authentication policy for MAB users
• created an authorization policy
Which two components would be required to complete the configuration? (Choose two.)
A network administrator must configura endpoints using an 802 1X authentication method with EAP identity certificates that are provided by the Cisco ISE When the endpoint presents the identity certificate to Cisco ISE to validate the certificate, endpoints must be authorized to connect to the network Which EAP type must be configured by the network administrator to complete this task?
An administrator must provide wired network access to unidentified Cisco devices that fail 802.1X authentication. Cisco ISE profiling services must be configured to gather Cisco Discovery Protocol and LLDP endpoint information from a Cisco switch. These configurations were performed:
• configured switches to accept SNMP queries from Cisco ISE
• enabled Cisco Discovery Protocol and LLDP on the switches
• added the switch as a NAD to Cisco ISE
What must be enabled to complete the configuration?
What is the default port used by Cisco ISE for NetFlow version 9 probe?
An engineer is configuring Central Web Authentication in Cisco ISE to provide guest access. When an authentication rule is configured in the Default Policy Set for the Wired_MAB or Wireless_MAB conditions, what must be selected for the "if user not found" setting?
Which profiling probe collects the user-agent string?
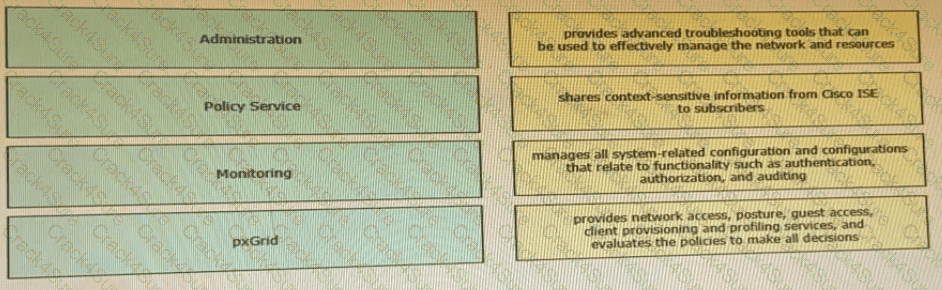
Drag the Cisco ISE node types from the left onto the appropriate purposes on the right.
A network engineer must enforce access control using special tags, without re-engineering the network design. Which feature should be configured to achieve this in a scalable manner?
A Cisco ISE server sends a CoA to a NAD after a user logs in successfully using CWA Which action does the CoA perform?
How is policy services node redundancy achieved in a deployment?
An engineer is configuring web authentication using non-standard ports and needs the switch to redirect traffic to the correct port. Which command should be used to accomplish this task?
3 Months Free Update
3 Months Free Update
3 Months Free Update