We at Crack4sure are committed to giving students who are preparing for the Cisco 350-401 Exam the most current and reliable questions . To help people study, we've made some of our Implementing Cisco Enterprise Network Core Technologies (350-401 ENCOR) exam materials available for free to everyone. You can take the Free 350-401 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
How can an engineer prevent basic replay attacks from people who try to brute force a system via REST API?
A wireless administrator must create a new web authentication corporate SSID that will be using ISE as the external RADIUS server. The guest VLAN must be specified after the authentication completes. Which action must be performed to allow the ISE server to specify the guest VLAN?
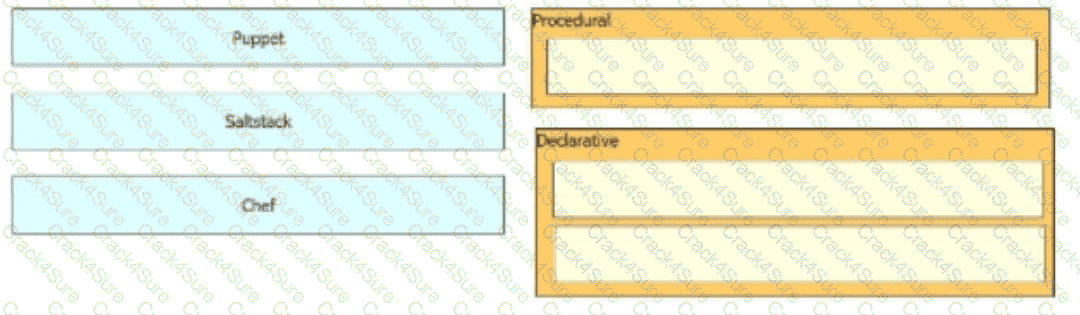
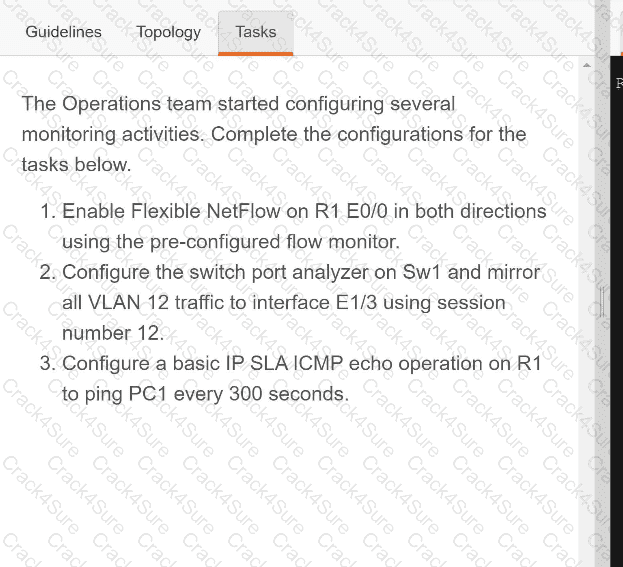
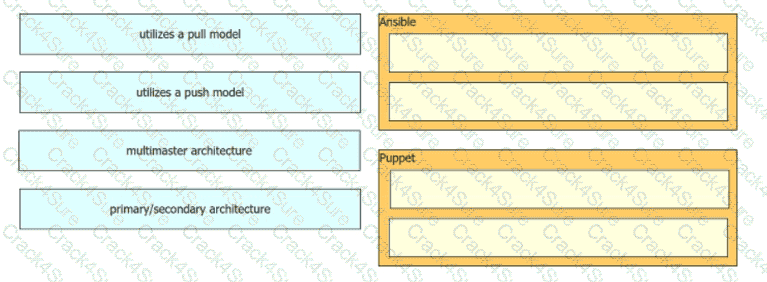
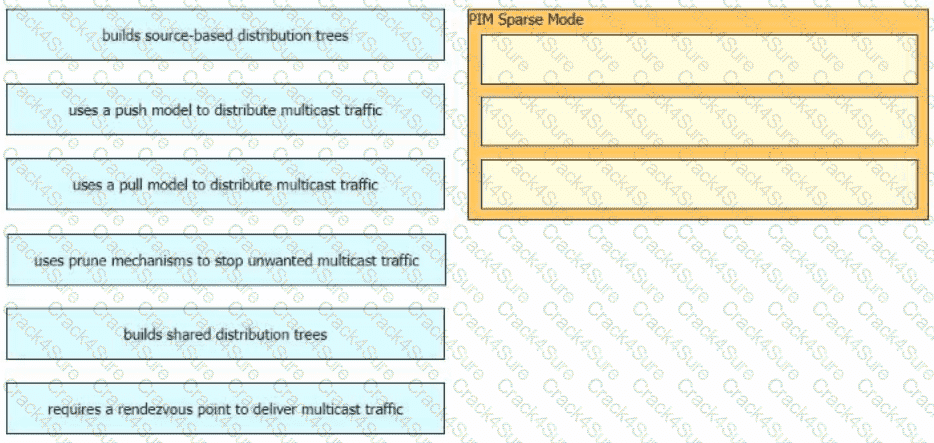
Drag and drop the configuration management tools from the left onto the configuration styles they use on the right
What does the statement print(format(0.8, \0%')) display?
Which message type is valid for IGMPv3?
In a Cisco SD-Access network architecture, which access layer cabling design is optimal for the underlay network?
Which characteristics applies to Cisco SD-Access?
Which two functions is an edge node responsible for? (Choose two.)
What are two device roles in Cisco SD-Access fabric? (Choose two.)
What is a characteristics of Wi-Fi channels?
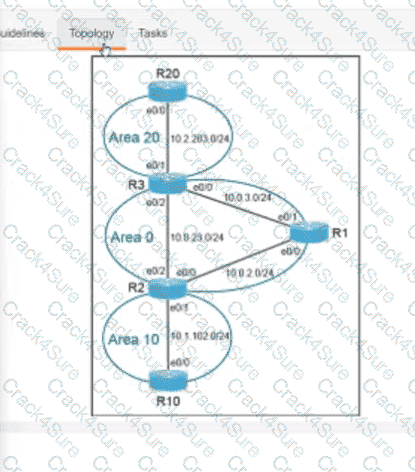
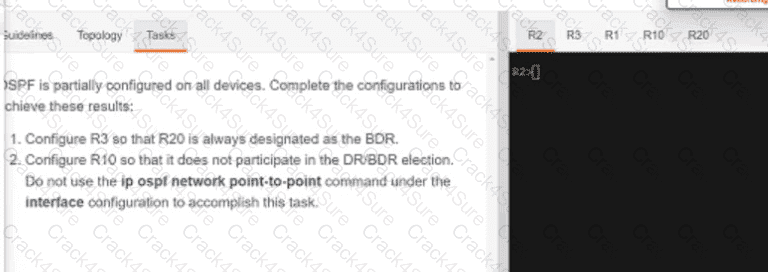
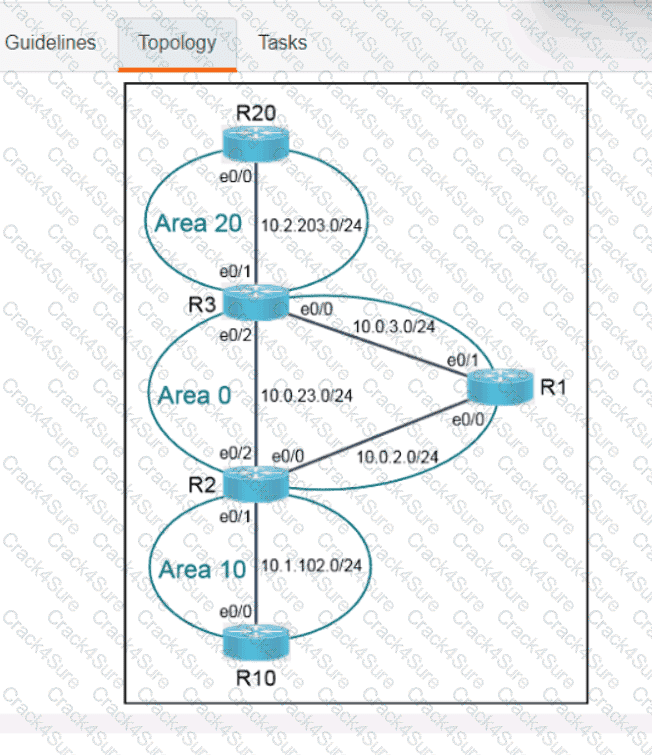
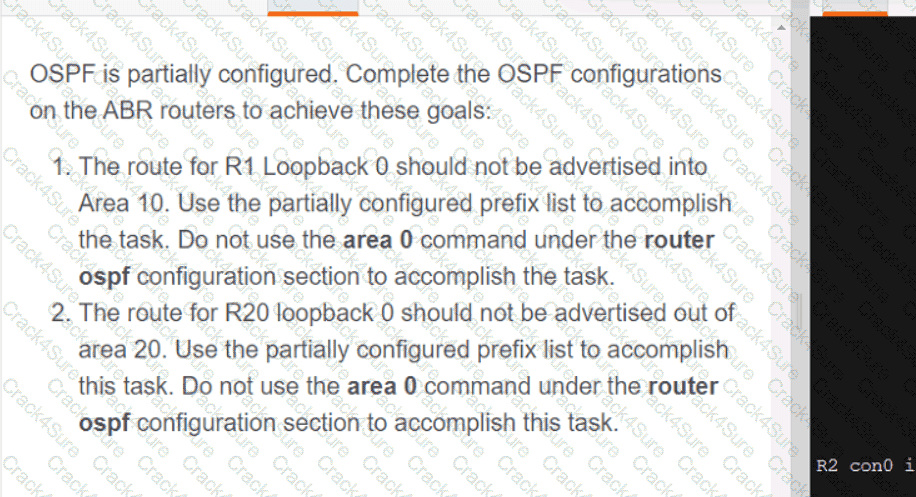
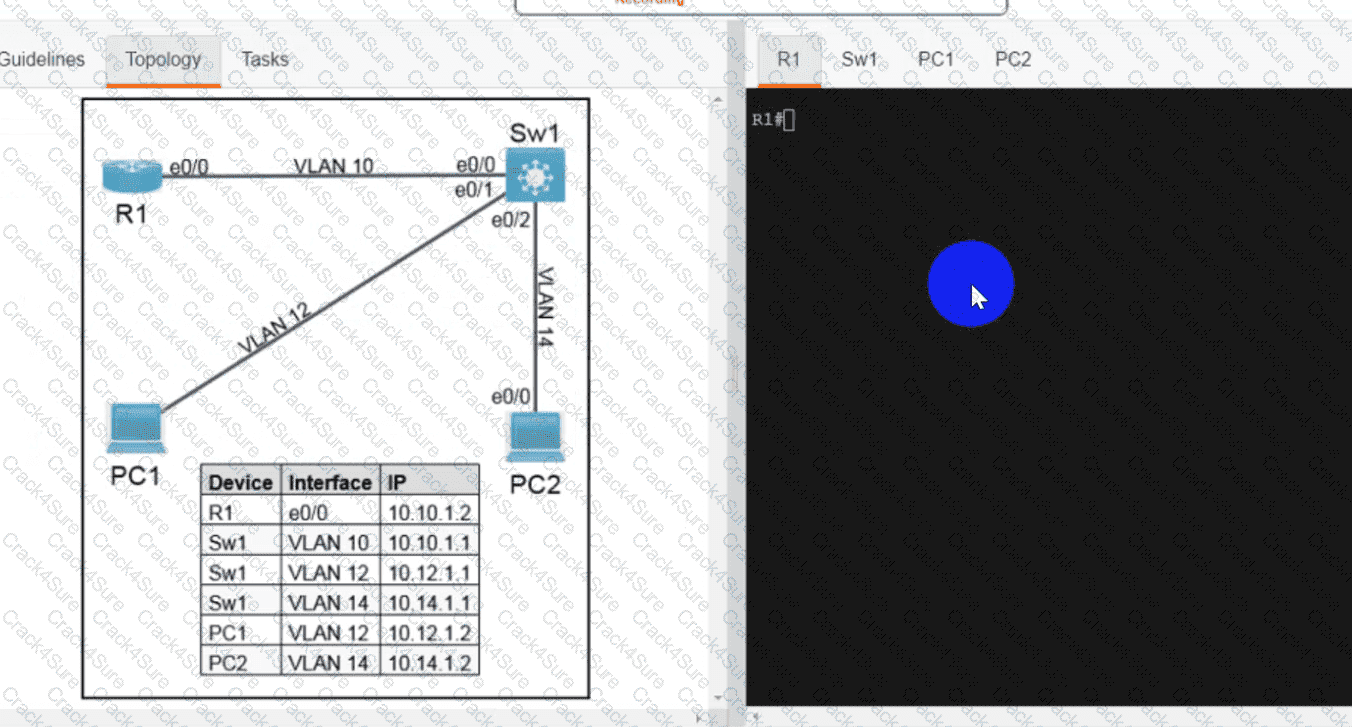
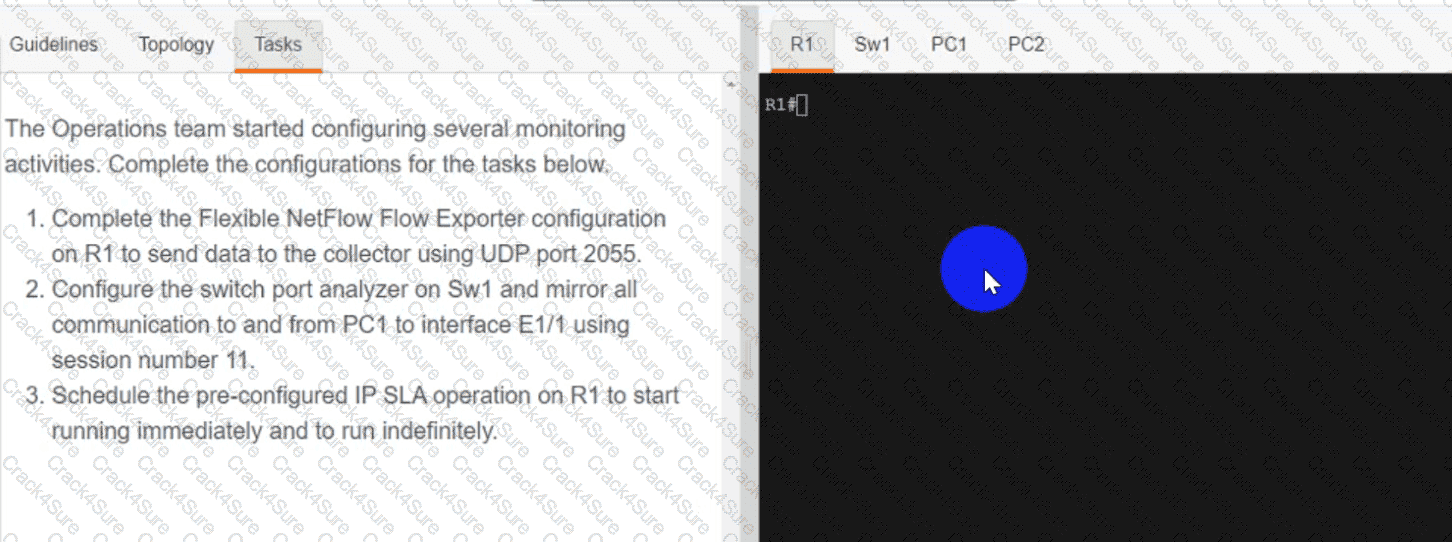
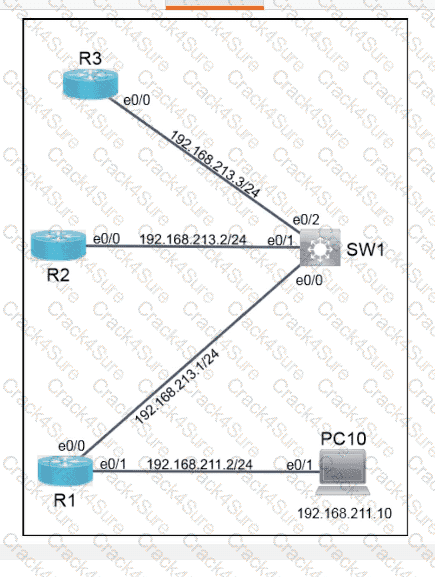
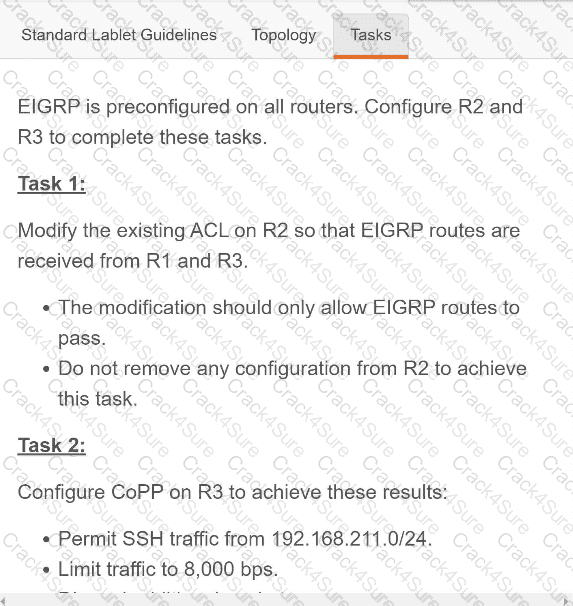
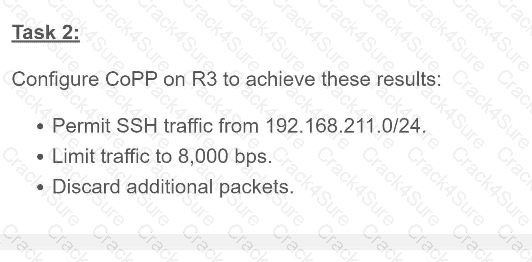
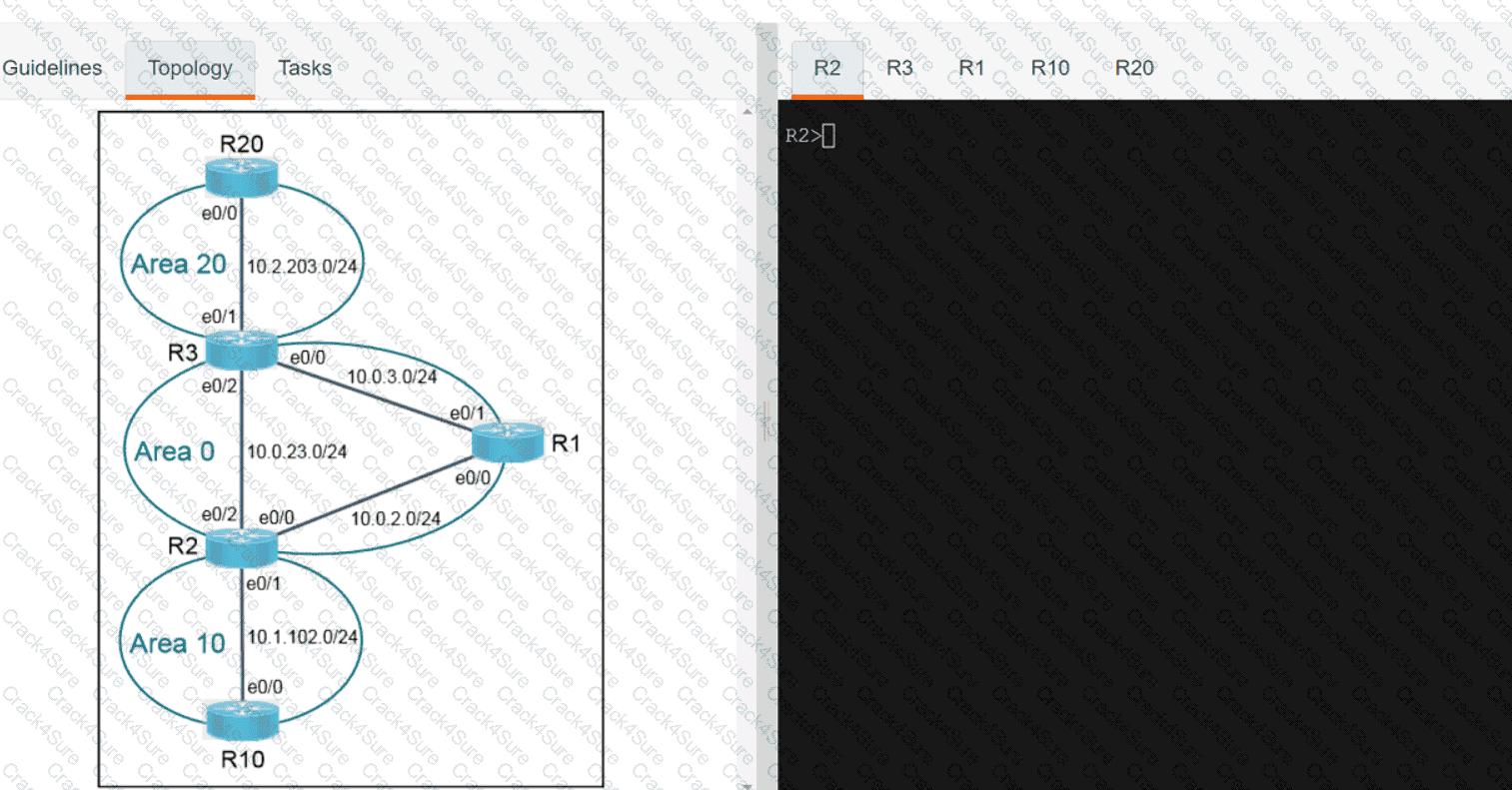
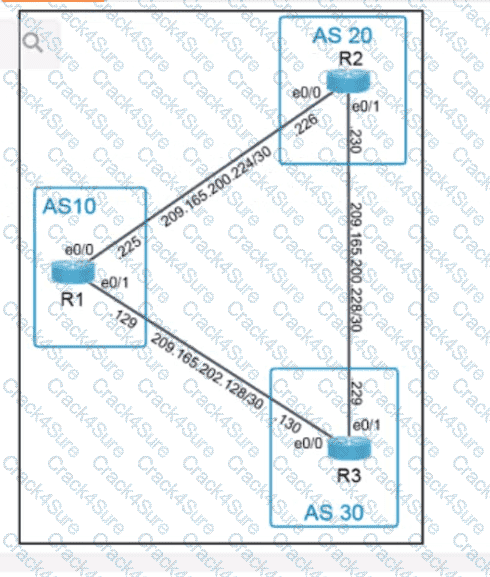
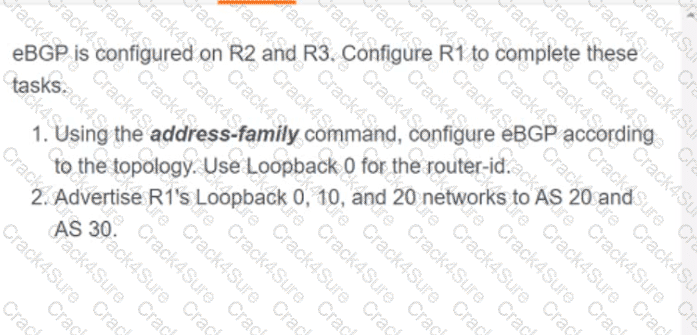
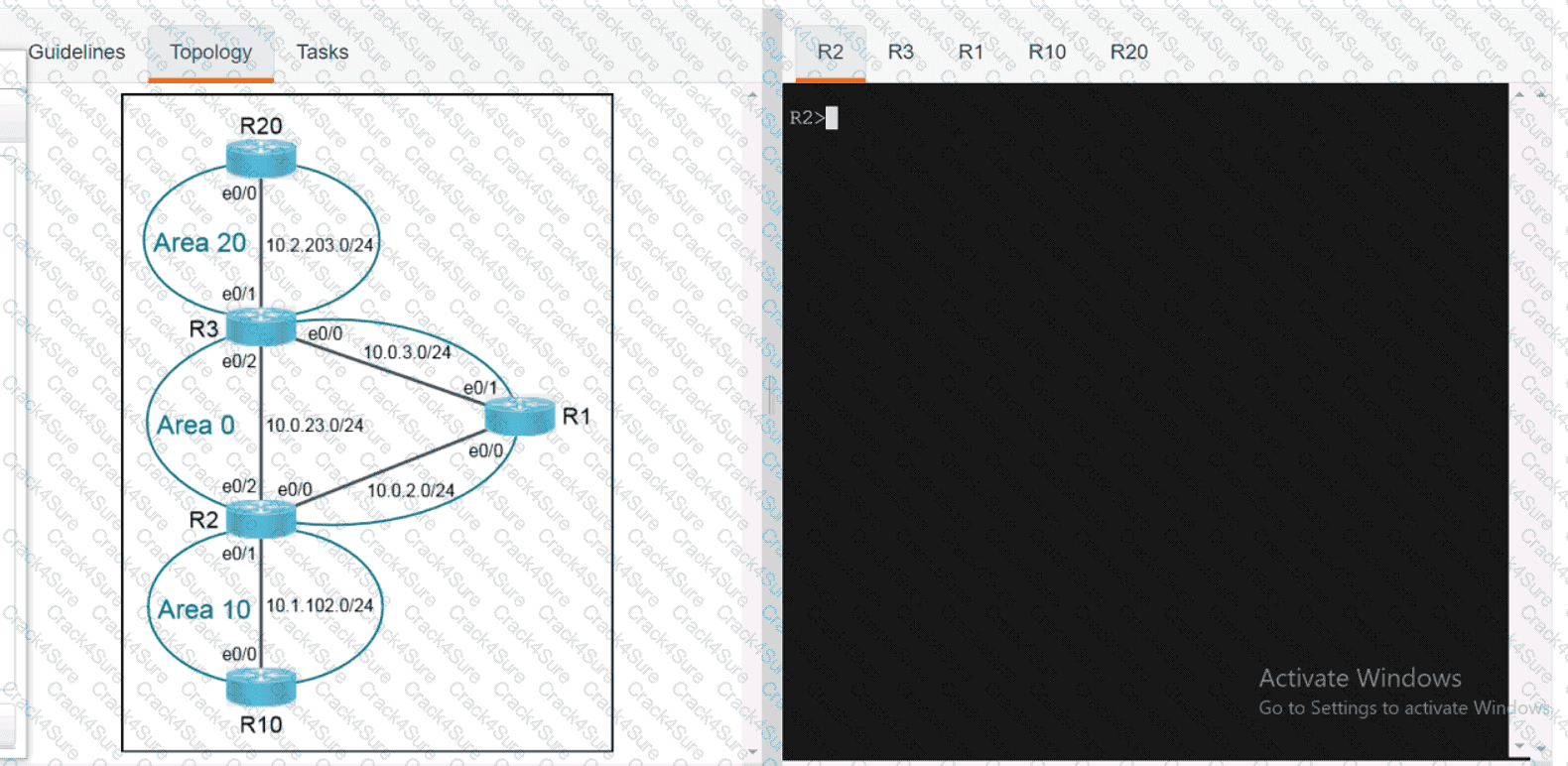
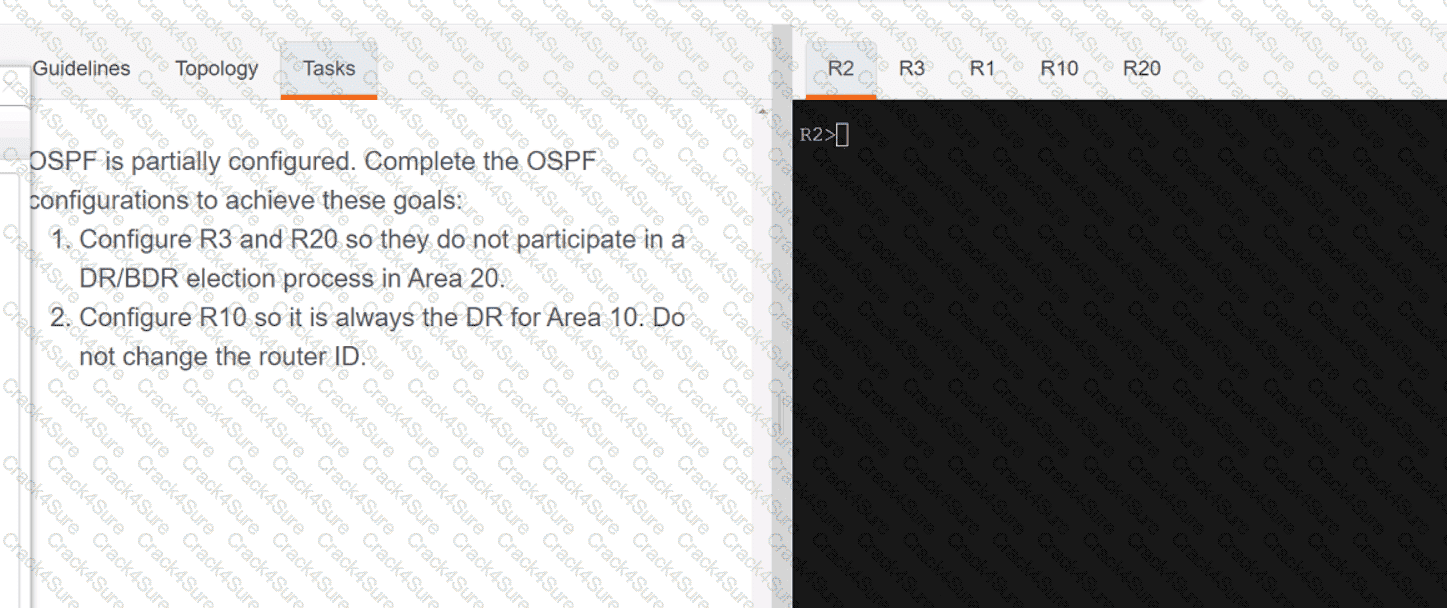
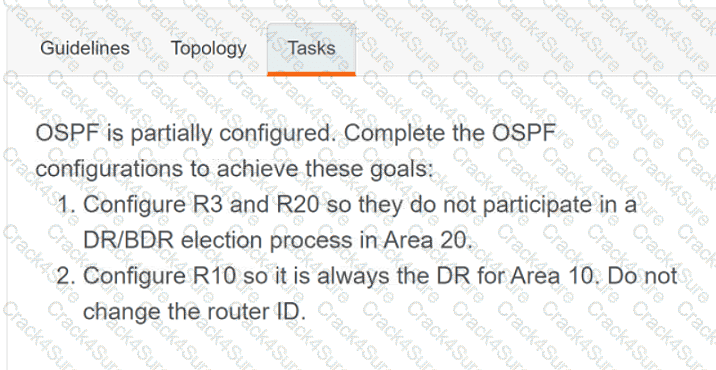
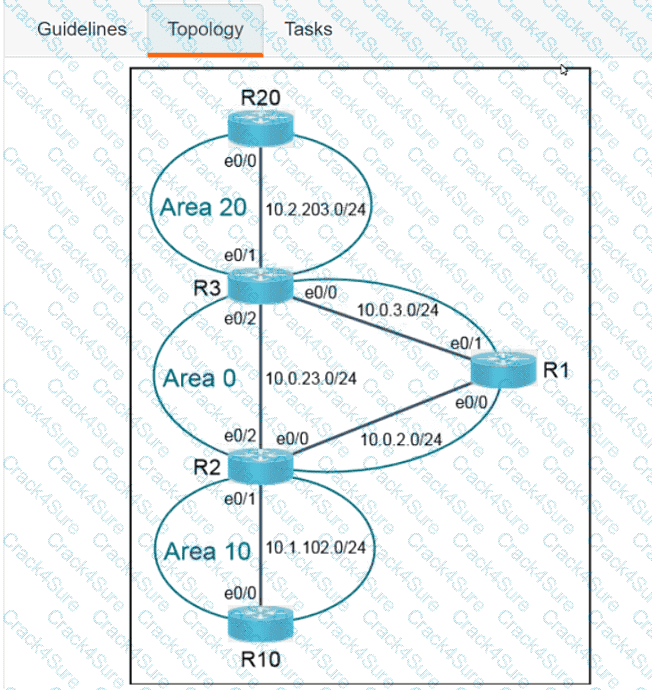
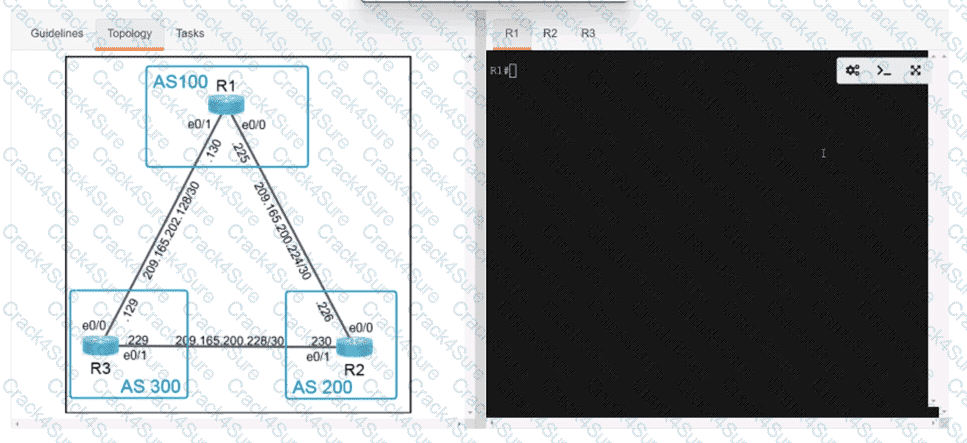
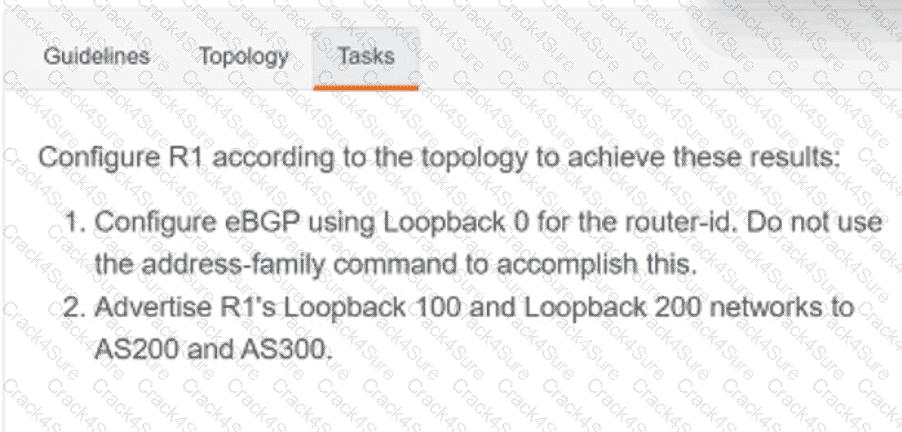
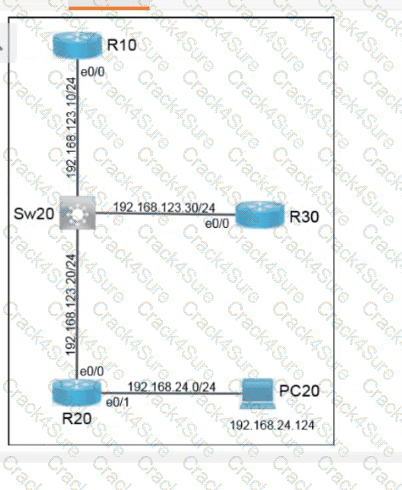
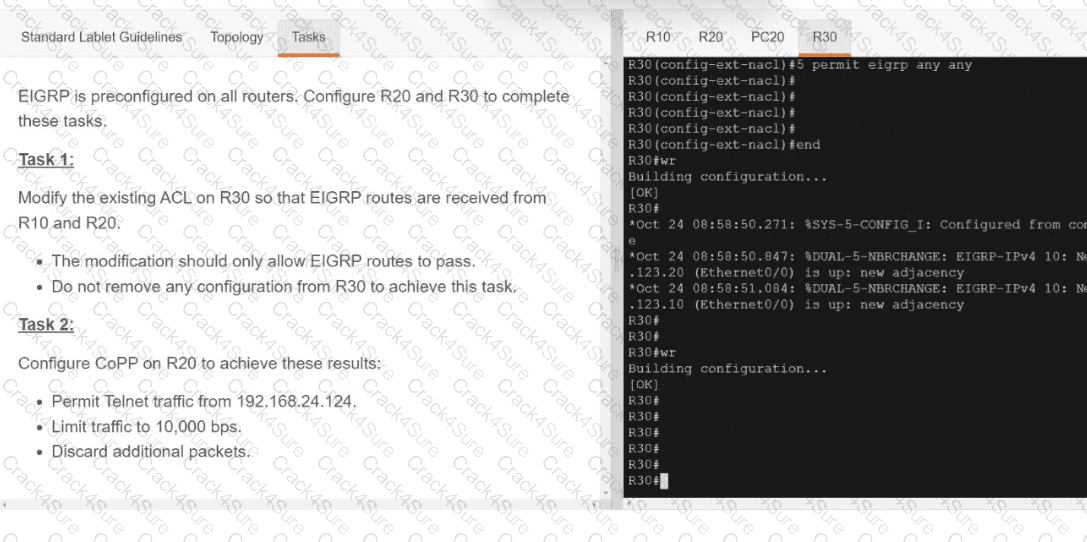
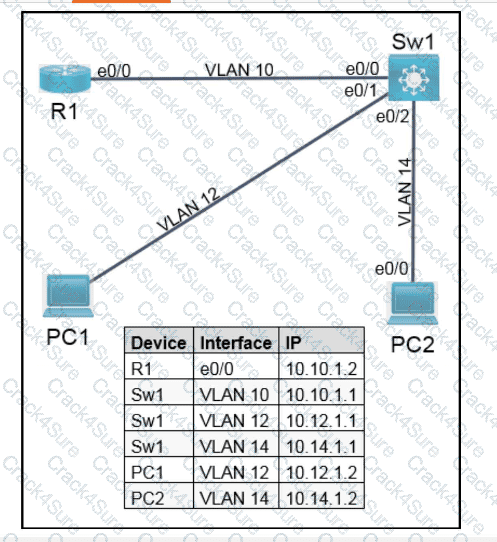
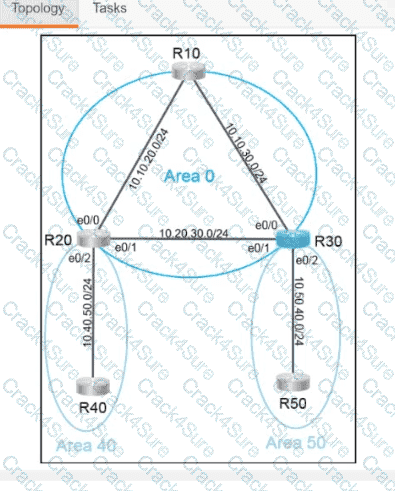
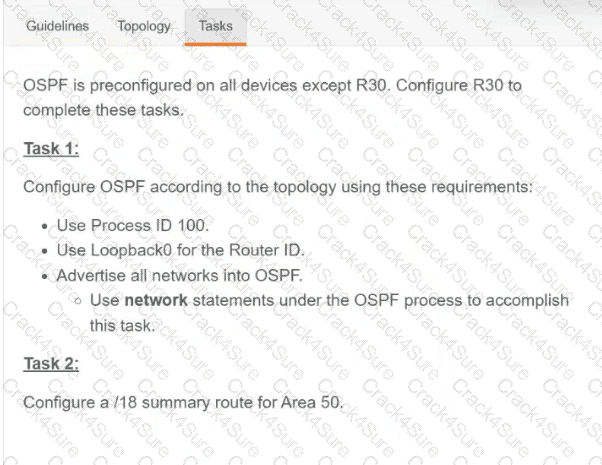
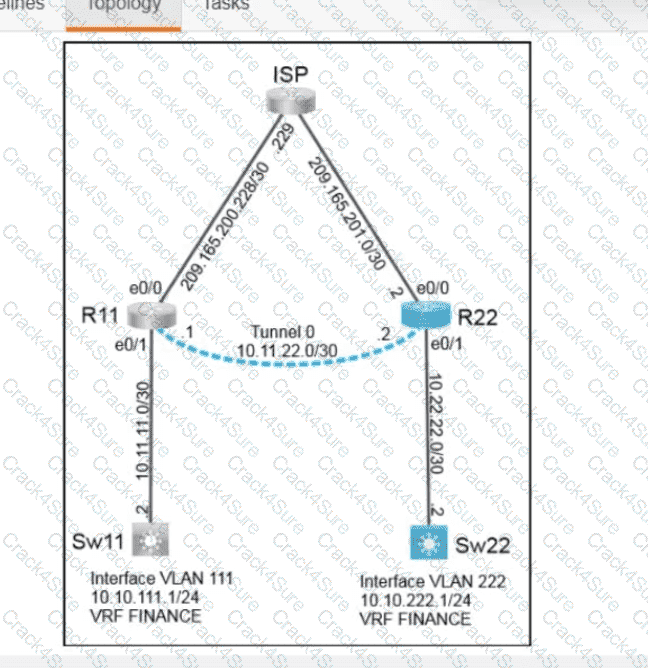
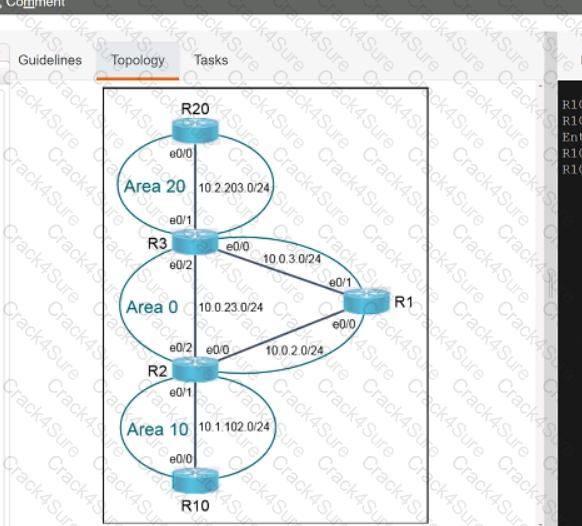
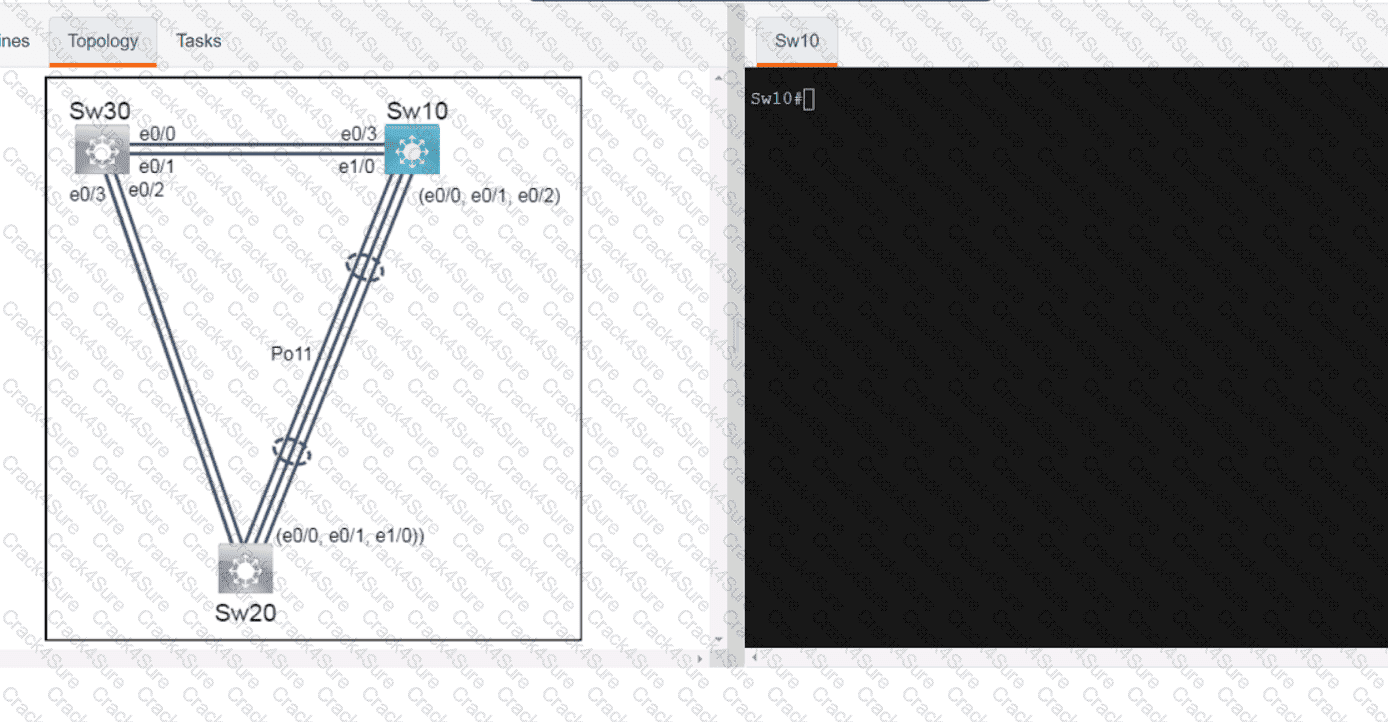
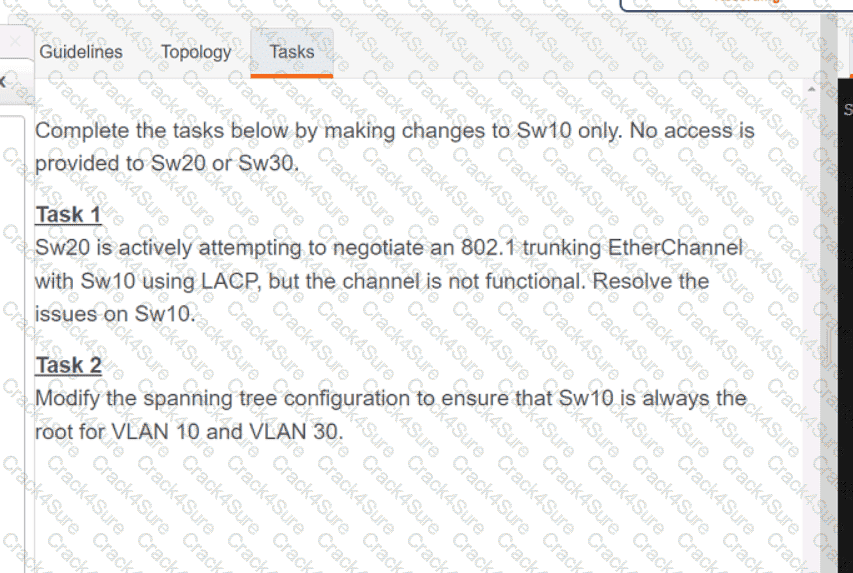
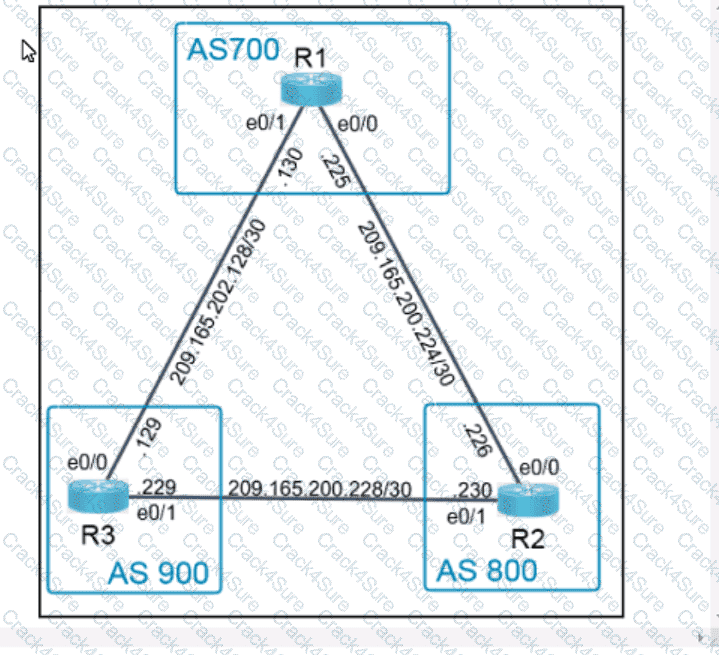
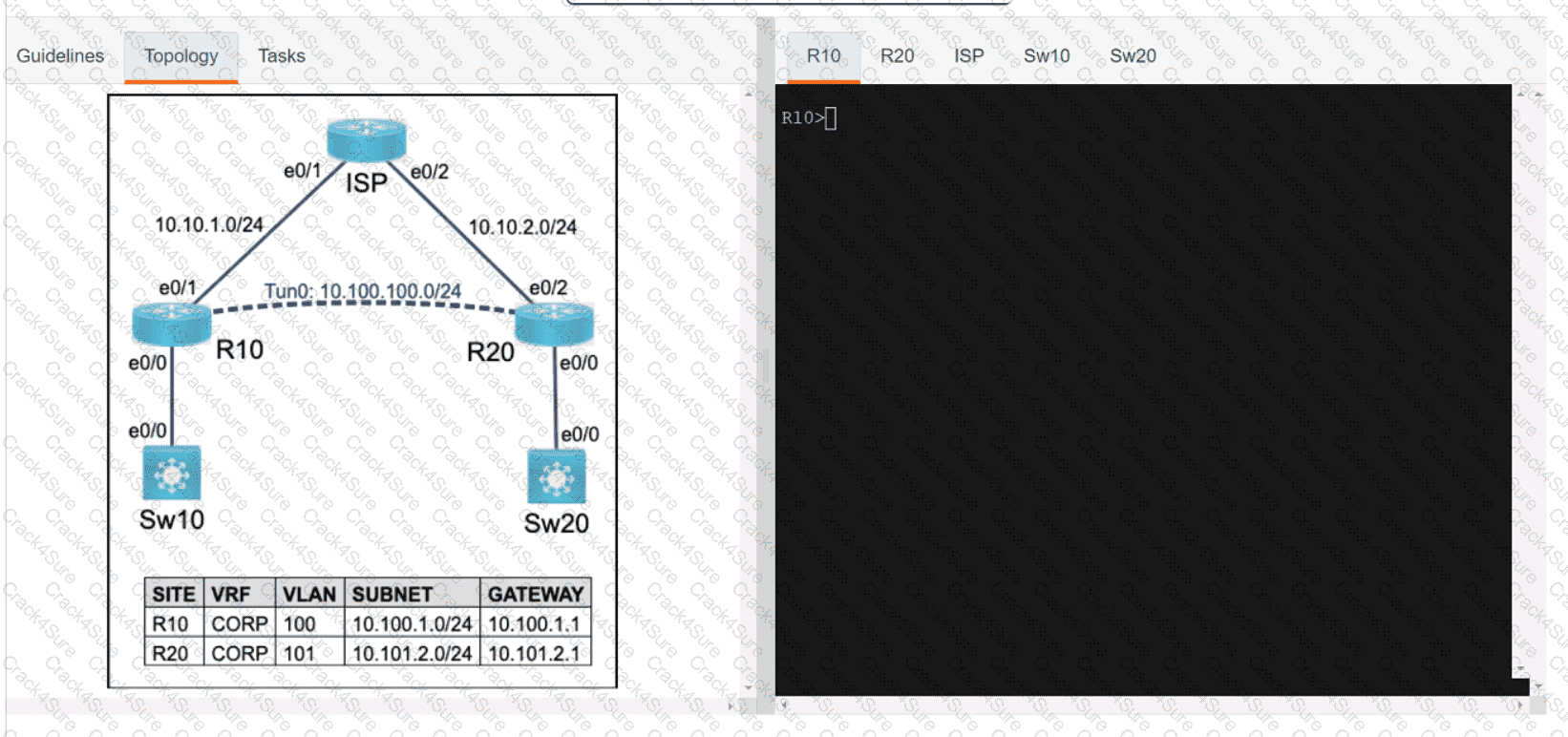
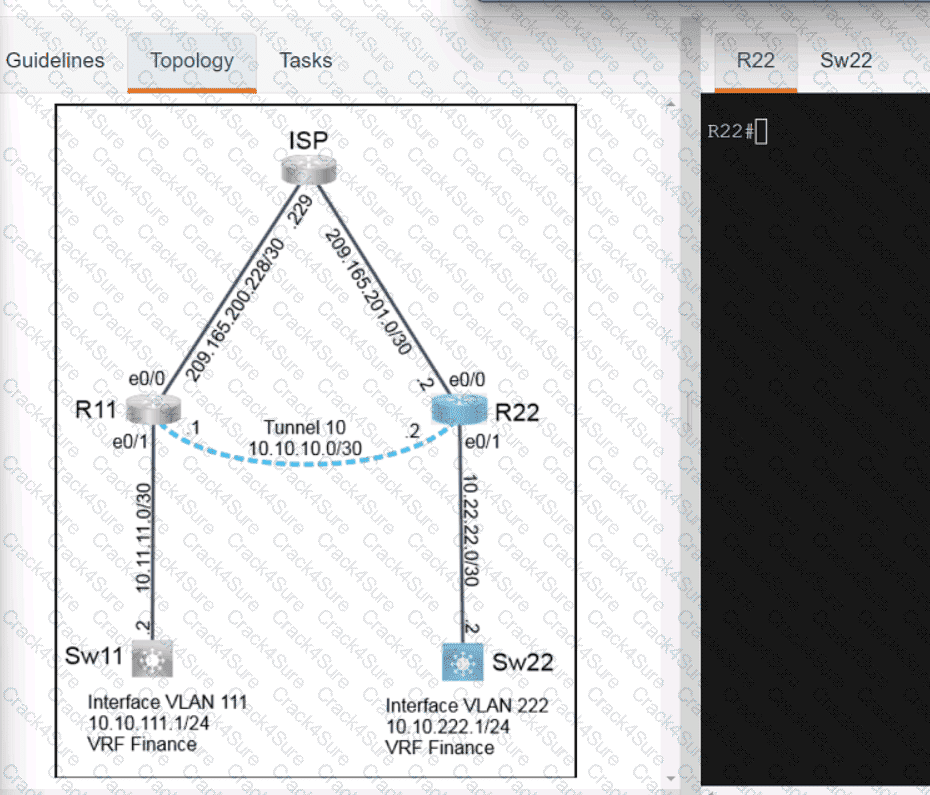
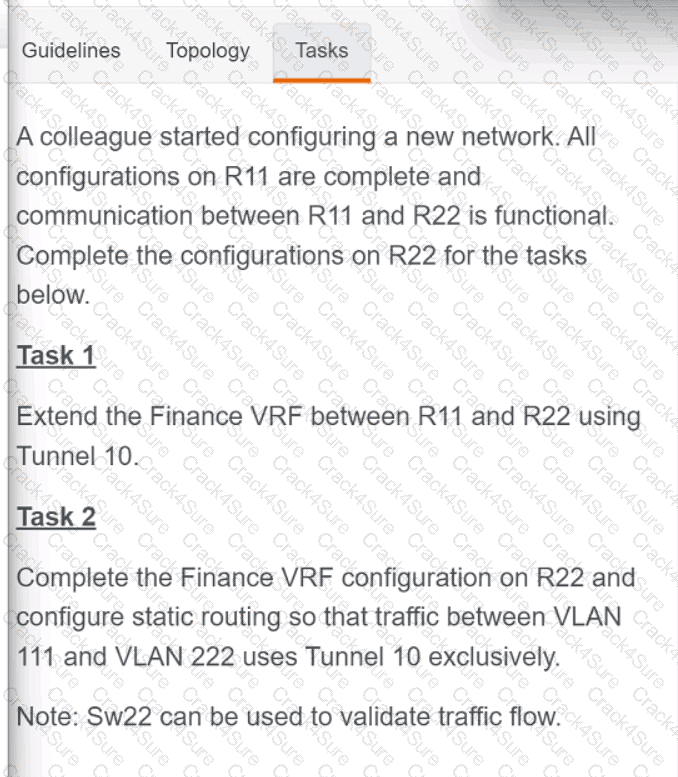
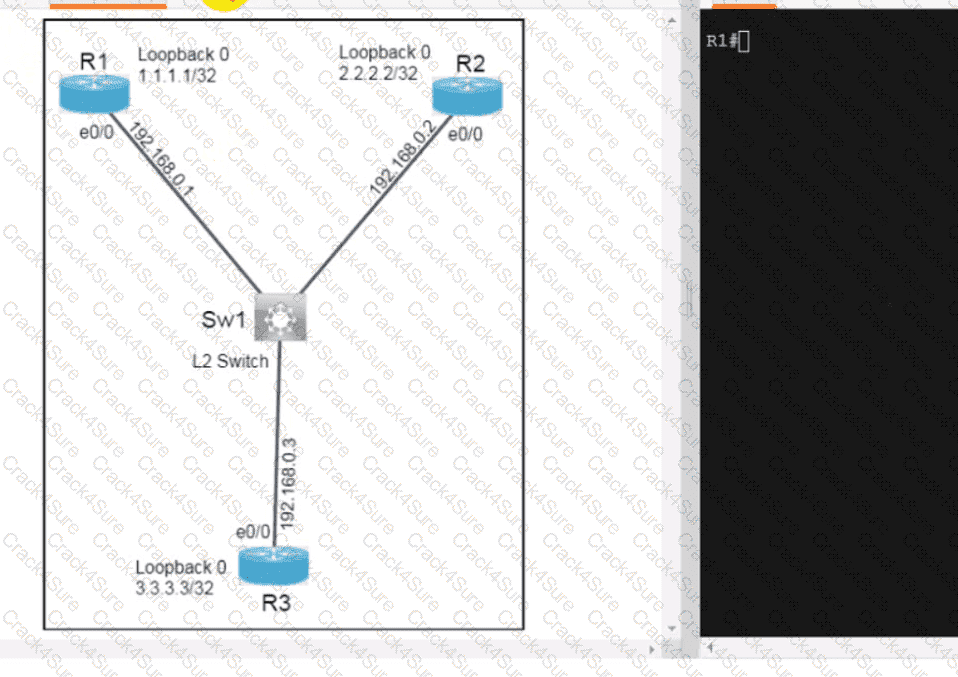
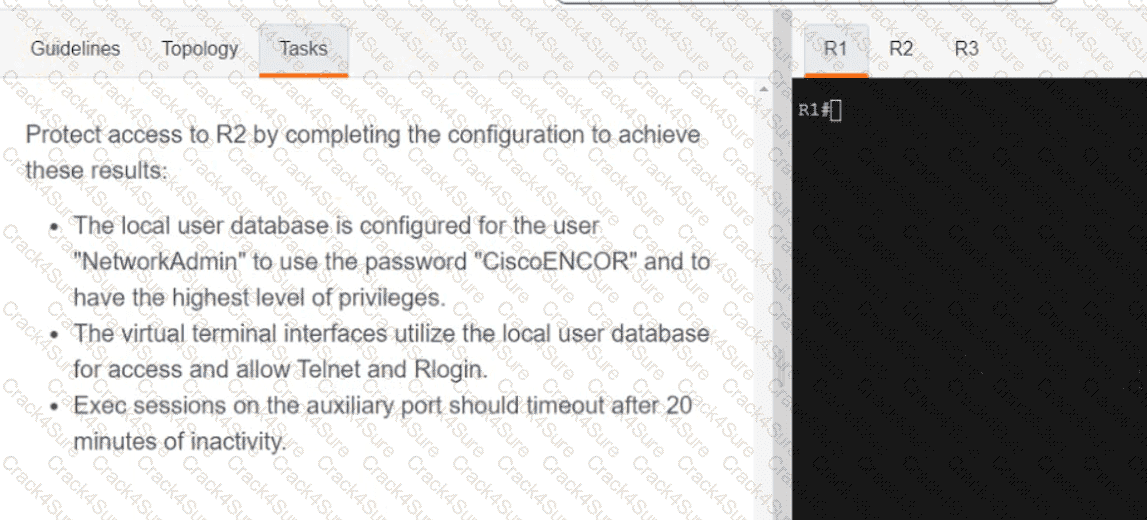
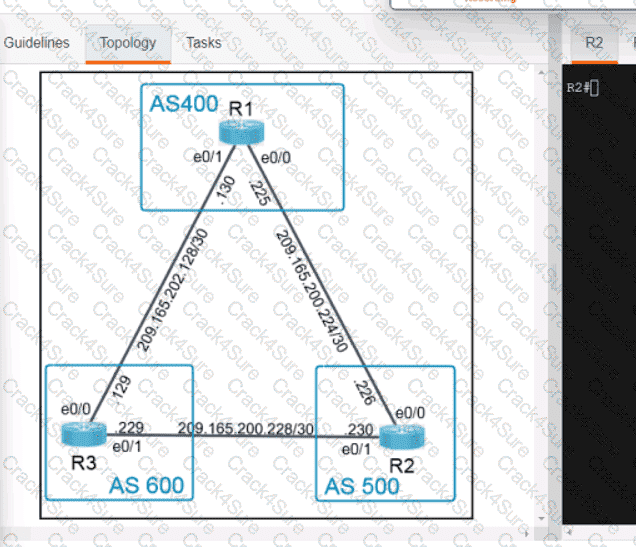
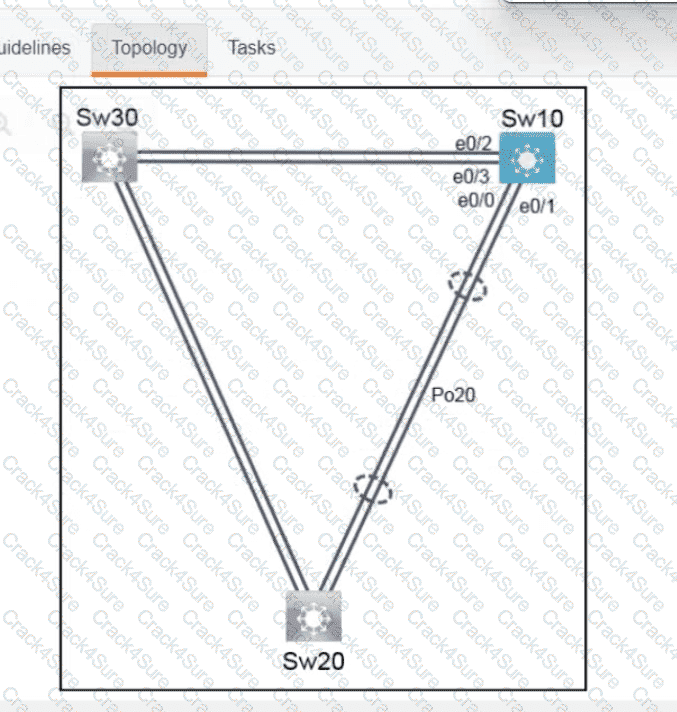
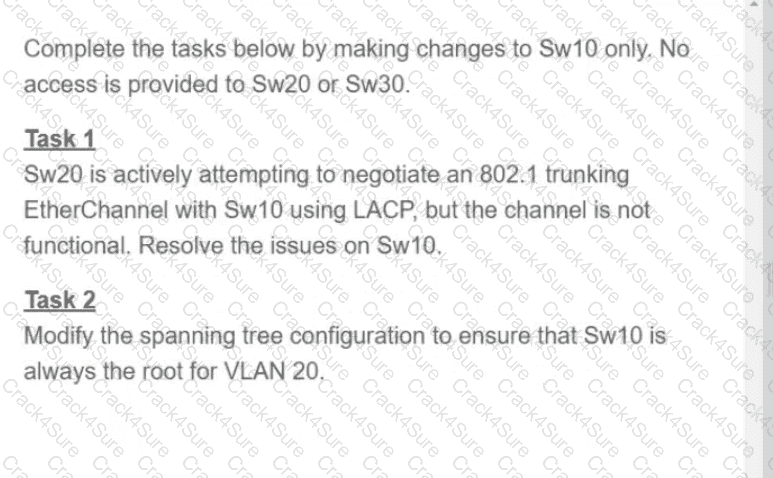
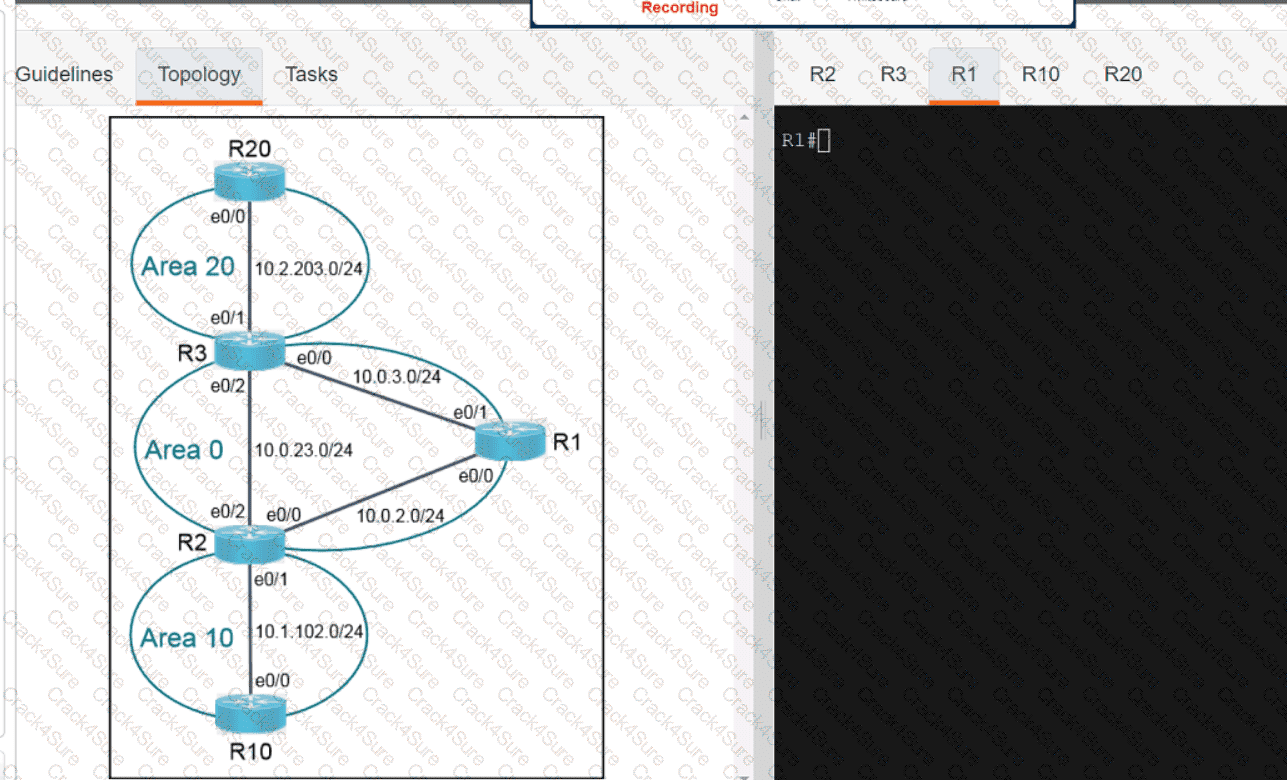
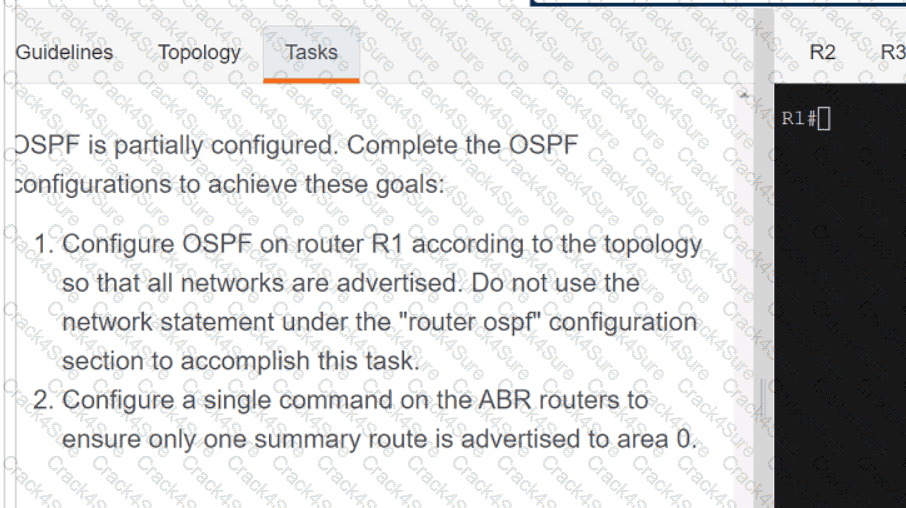
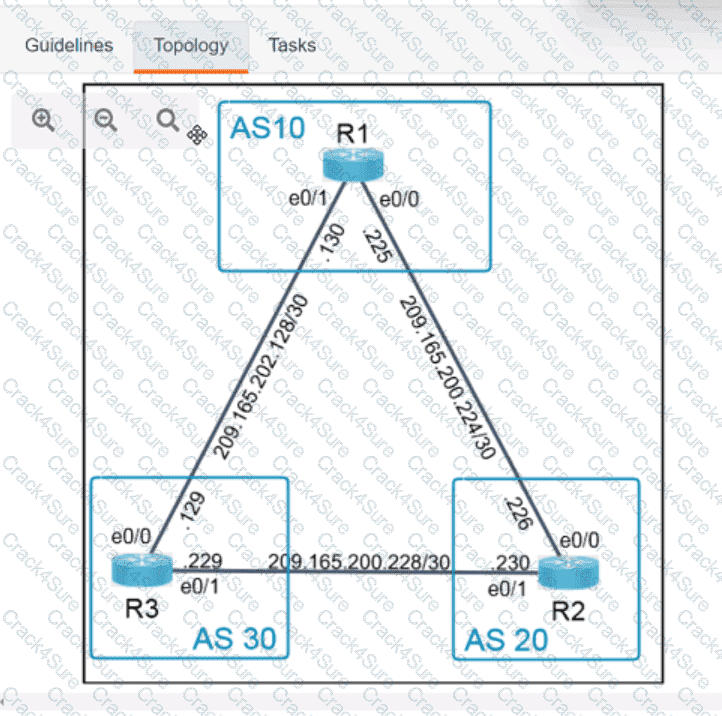
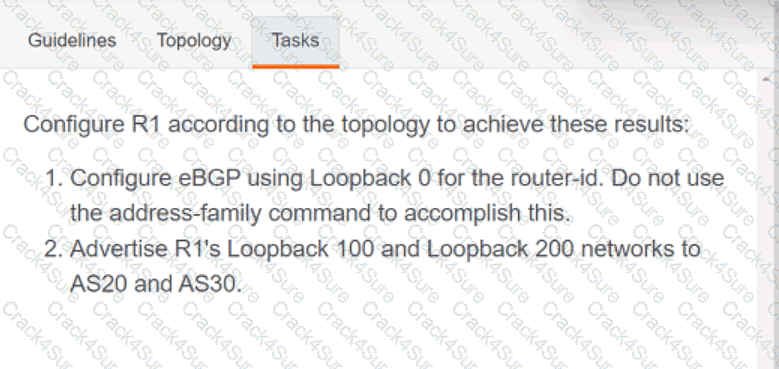
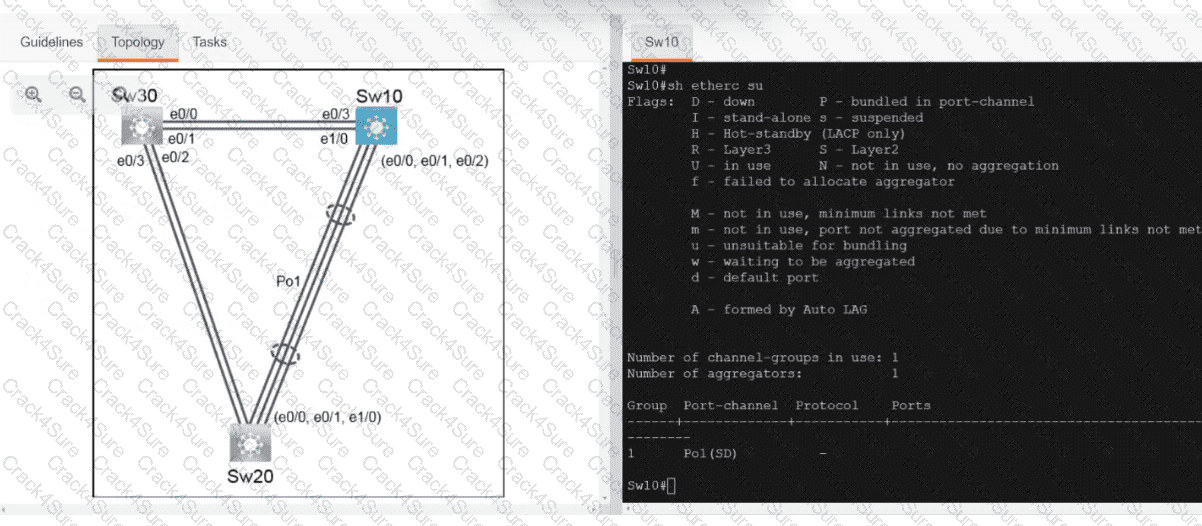
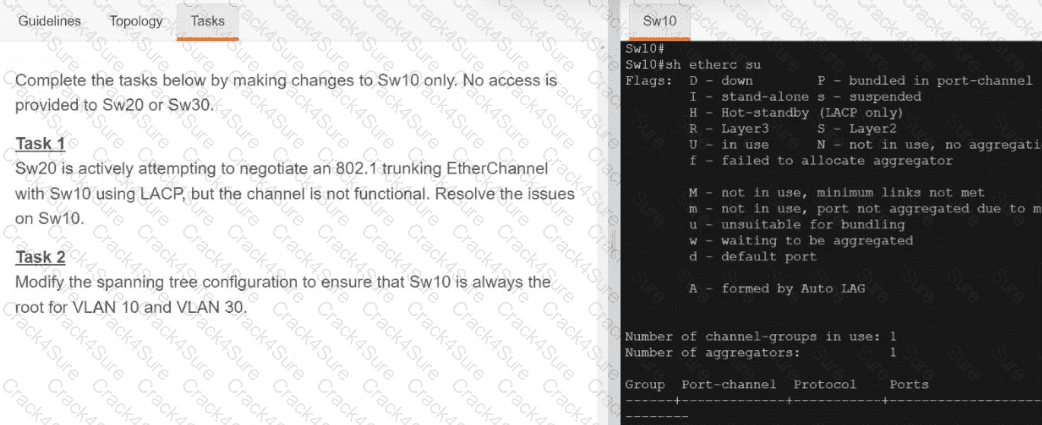
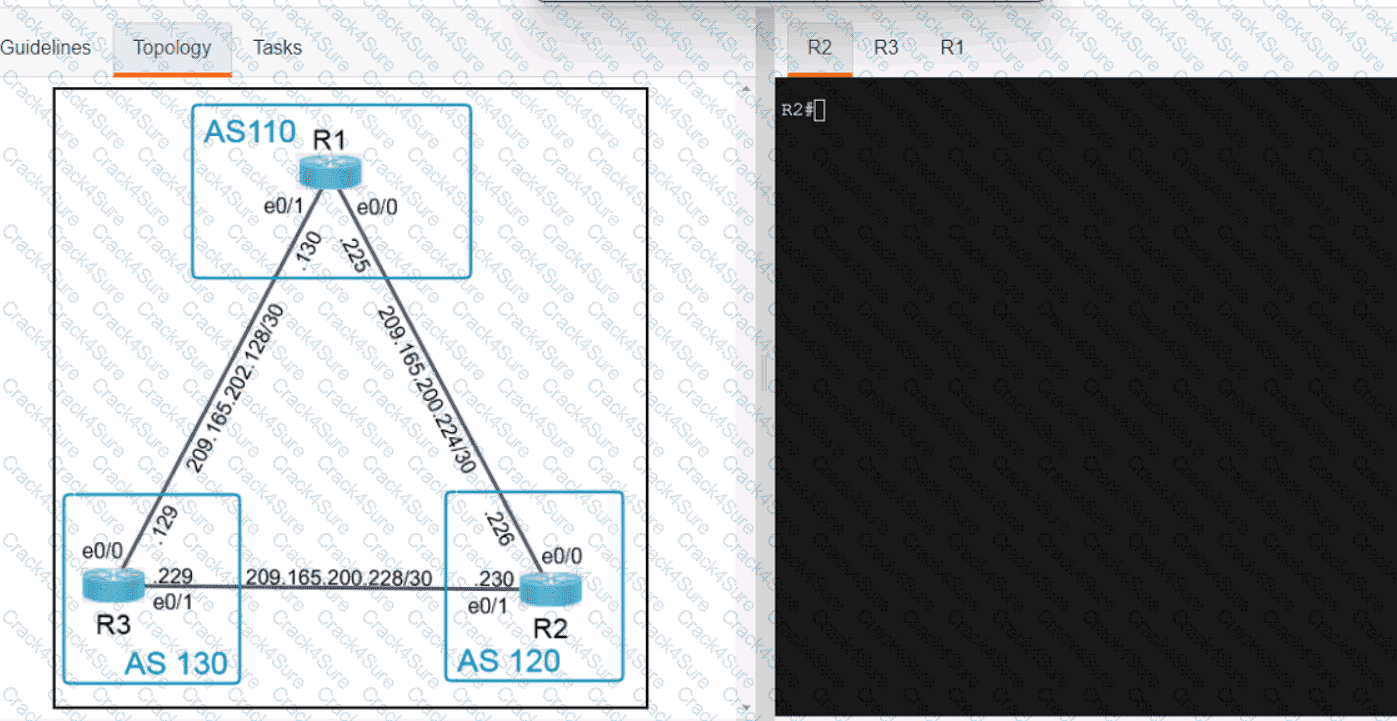
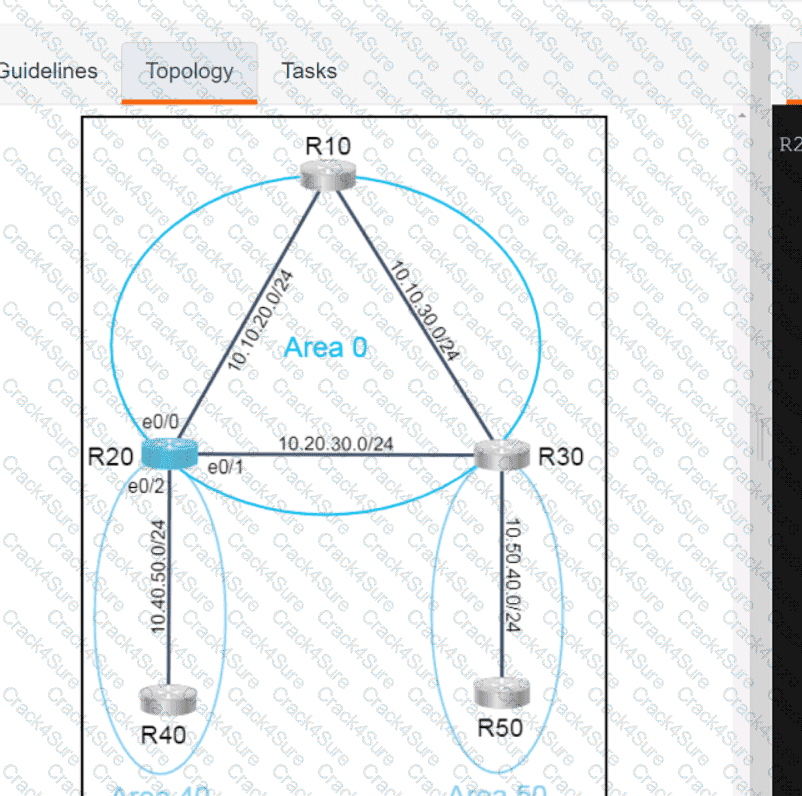
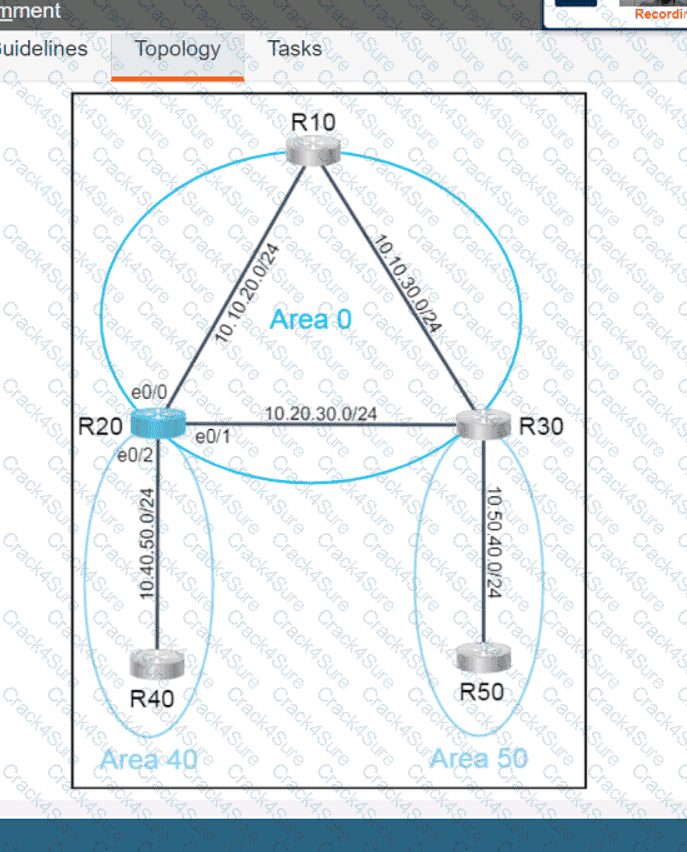
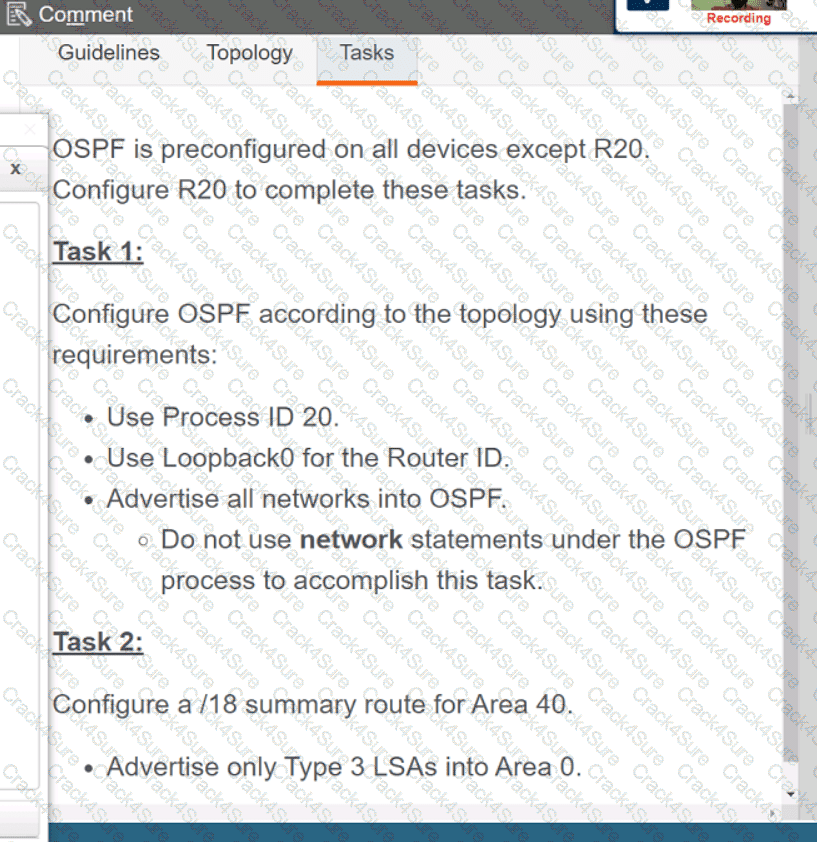
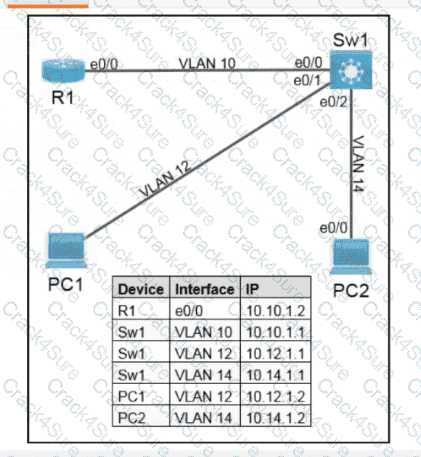
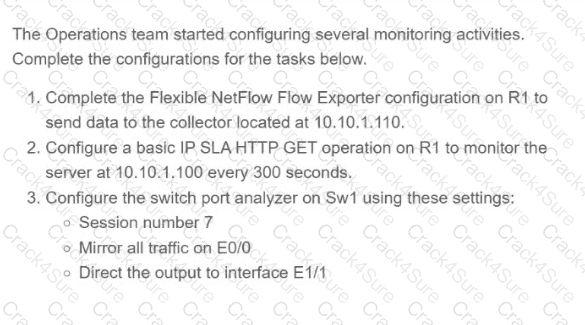
Refer to the exhibit.
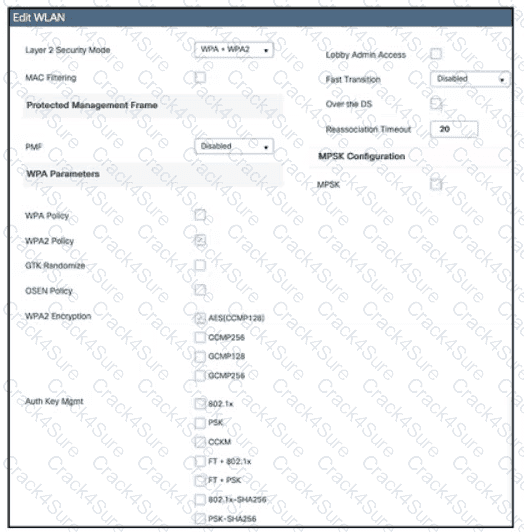
Which action must be taken to configure a WLAN for WPA2-AES with PSK and allow only 802.11r-capable clients to connect?
Which two conditions occur when the primary route processor fails on a switch thatisusing dual route processors with stateful switchover? (Choose two.)
Which AP mode allows a supported AP to function like a WLAN client would, associating and identifying client connectivity issues?
To support new clients in the environment, an engineer must enable Fast Transition on the corporate WLAN. Which command must be applied on a Cisco Catalyst 9800 Series WLC?
Drag and drop the characteristics from the left onto the orchestration tools they describe on the right.
What is a benefit of data modeling languages like YANG?
Which definition describes JWT in regard to REST API security?
Which type of roaming event occurs when a client roams across multiple mobility groups?
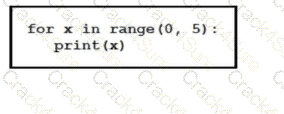
Refer to the exhibit. What is output by this code?
How does NETCONF YANG represent data structures?
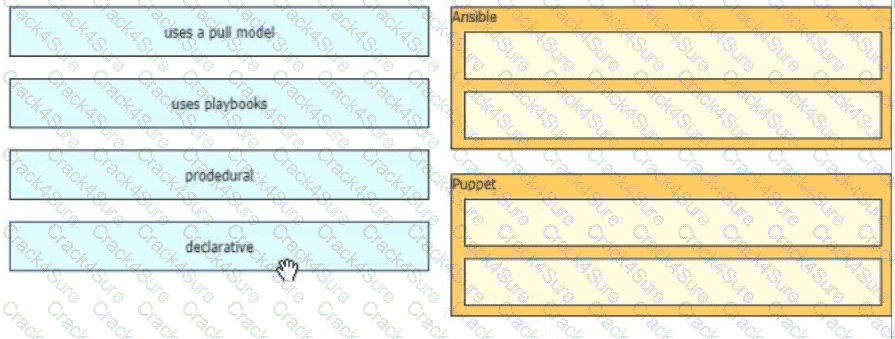
Drag and drop the characteristics from the left onto the orchestration tools that they describe on the right.
What does the LAP send when multiple WLCs respond to the CISCO_CAPWAP-CONTROLLER.localdomain hostname during the CAPWAP discovery and join process?
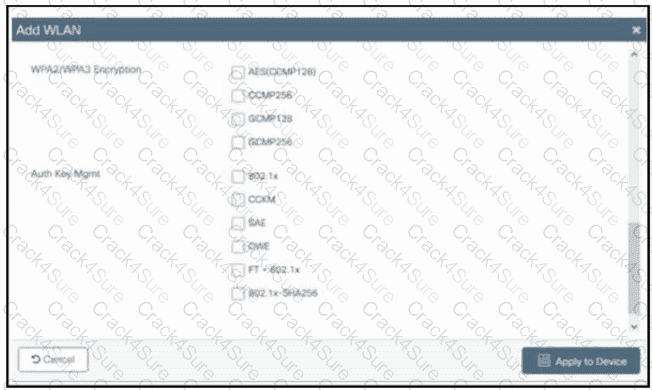
Refer to the exhibit. A customer asks an engineer to create a new secure WLAN to support only WPA3. Users must connect using a passphrase. Which encryption and key management configuration is required?
Which feature works with SSO to continue forwarding packets after a route processor failure until the control plane recovers?
Why does the vBond orchestrator have a public IP?
Why does the vBond orchestrator have a public IP?
Which security feature does stateless authentication and authorization use for REST API calls?
What is the structure of a JSON web token?
Which tool functions in a push model, supports languages like Python or Ruby, and does not require an agent to be installed per host?
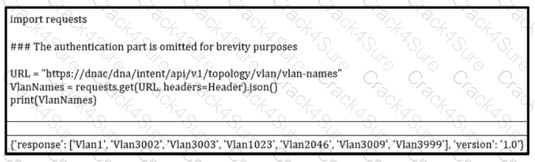
Refer to the exibit. How should the programmer access the list of VLANs that are recevied via the API call?
Which solution should be used in a high-density wireless environment to increase bandwidth for each user?
What is a characteristic of a traditional WAN?
Which Cisco WLC feature allows a wireless device to perform a Layer 3 roam between two separate controllers without changing the client IP address?
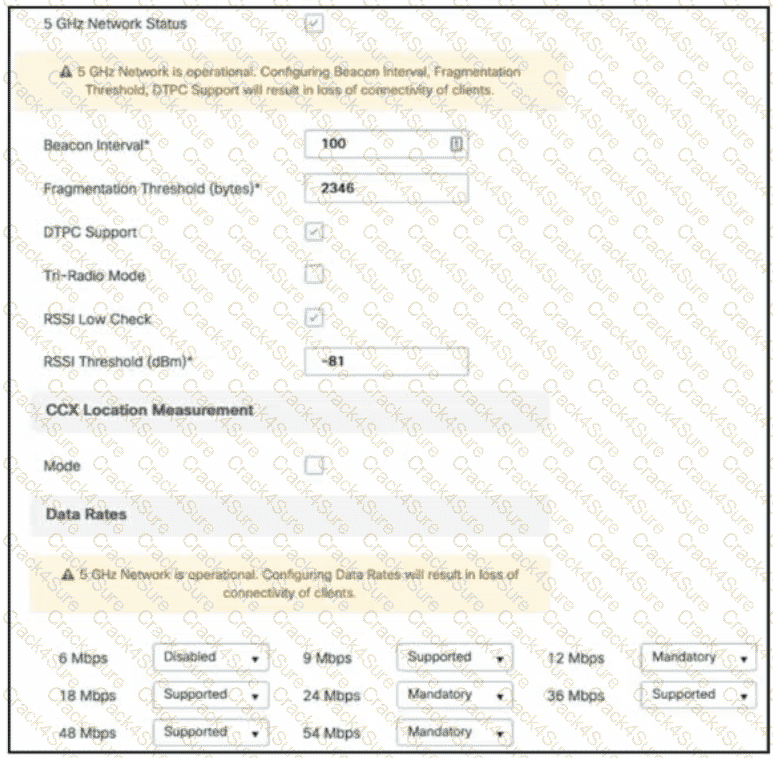
Refer to the exhibit. A customer reports that many wireless clients cannot reliably receive multicast audio. Which action resolves this issue?
Which NGFW mode block flows crossing the firewall?
What is a characteristic of Layer 3 roaming?
Which two Cisco SD-Access components provide communication between traditional network elements and the controller layer? (Choose two.)
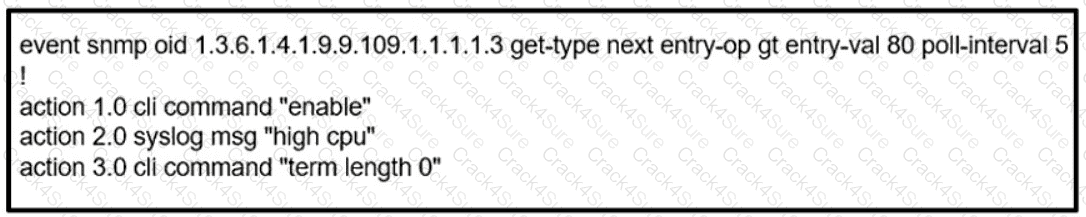
Refer to the exhibit. An engineer must create a script that appends the output of the show process cpu sorted command to a file.
Which technique is used to protect end user devices and data from unknown file behavior?
In Cisco CatalystCenter(formerly DNA Center) Inventory, the Software Version of a networkdevice displays a status of OUTDATED. What does It me?
What is two characteristic of Cisco DNA Center and vManage northbound APIs?
Which function does a Cisco SD-Access extended node perform?
Which mobility role is assigned to a client in the client table of the new controller after a Layer 3 roam?
In a Cisco SD-Access wireless architecture, which device manages endpoint ID to edge node bindings?
What is one characteristic of Cisco SD-Access networks?
Which solution supports end-to-end line-rate encryption between two sites?
What is a capability of the Cisco DNA Center southbound API?
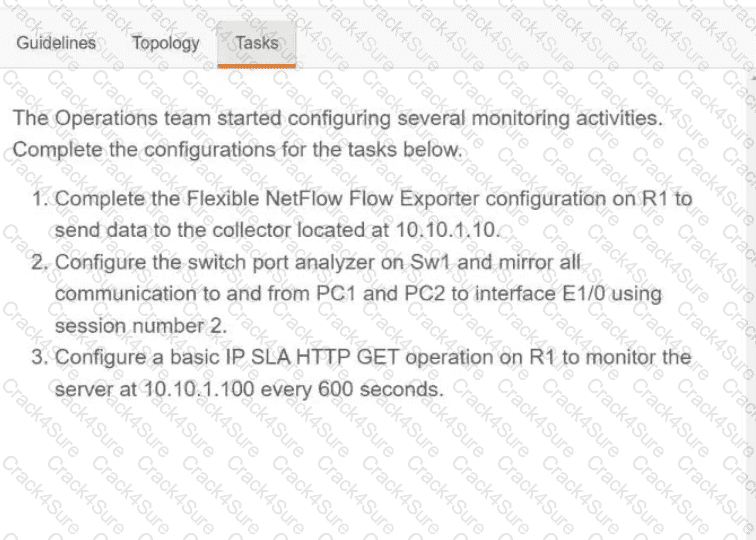
Drag and drop the characteristics of PIM Sparse Mode from the left to the right. Not all options are used.
Which First Hop Redundancy Protocol should be used to meet a design requirements for more efficient default bandwidth usage across multiple devices?
Which deployment option of Cisco NGFW provides scalability?
What is the recommended minimum SNR for data applications on wireless networks?
What is the primary responsibility of the vBond orchestrator?
When deploying Cisco SD-Access Fabric APs, where does the data plane VXLAN tunnel terminate?
Which device is responsible for finding EID-to-RLOC mappings when traffic is sent to a LISP-capable site?
Which method does FastLocate use to collect location-based information?
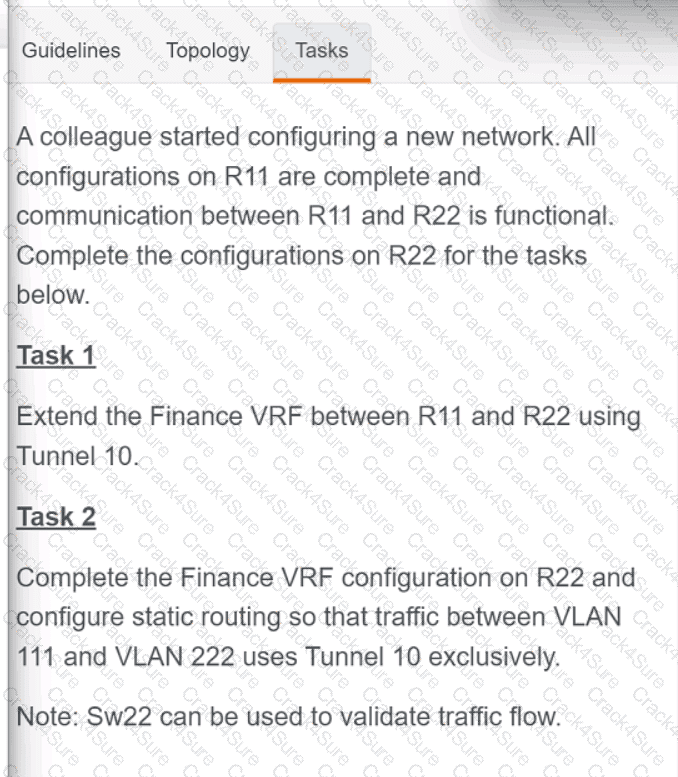
Refer to the exhibit. POSTMAN is showing an attempt to retrieve network device information from Cisco Catalyst Center (formerly DNA Center) API. What is the issue?
OR
3 Months Free Update
3 Months Free Update
3 Months Free Update