What is the effect of the set cmp parameter –cmpBypassPct 70 command if compression is enabled on the NetScaler?
Scenario: A Citrix Administrator has a NetScaler SDX with four VPX instances configured. The SDX has a 10GB bandwidth license that has been configured with dedicated bandwidth of 2GB for each instance. However, the administrator found that three instances do NOT ever reach the bandwidth limit, while one instance reaches the limit and needs 1 GB more bandwidth to accommodate increased traffic requests.
What can the administrator change on the instance that requires more bandwidth, to meet traffic requirements?
View the Exhibit.
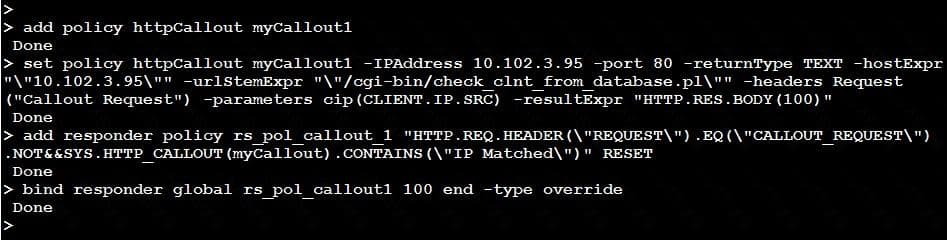
A Citrix Administrator has implemented the HTTP Callout.
Click on the ‘Exhibit’ button to view the screenshot of the command-line interface.
Which part of the configuration is responsible for triggering the call to HTTP Callout server?
Scenario: A Citrix Administrator has made changes to the NetScaler, deleting parts of the configuration, and then saved the new configurations. The changes caused an outage which needs to be resolved as quickly as possible. There is no NetScaler backup.
What does the administrator need to do to recover the configuration quickly?
Scenario: A Citrix Administrator has a NetScaler SDX appliance with several instances configured. The administrator needs one instance with two interfaces connected to forward packets that are NOT destined for its MAC address. Hence, the administrator has enabled Layer 2 mode. After enabling Layer 2 mode, the administrator found the interface status going up and down.
What can the administrator perform to resolve this issue?
A Citrix Administrator notices that the NetScaler is sending the IP addresses of all the active services in the DNS response.
The administrator can use the set gslb vserver
Scenario: A Citrix Administrator has executed the following command:
set csv server Vserver-CS-1 –caseSensitive ON
add cs action CS_Act_1 –targetLBVserver MYVPN_http
add cs policy CS_Pol_1 –rule “http.REQ.HOSTNAME.CONTAINS (\ “server.citrix.lab\”)” –action CS_Act_1
bind csv server CS-vserver1 –policyName CS_Pol_1 –priority 100
What will be the outcome of this configuration?
Which feature can a Citrix Administrator use to create a consistent set of front-end SSL parameters across multiple SSL virtual servers?
Scenario: A Citrix Administrator needs to implement a Content Filter policy to ensure the following conditions are met:
Which policy expression will meet this requirement if the policy action is RESET and the policy is bound to the server (VIP:10.10.10.1)?
Which two options would provide an end-to-end encryption of data, while allowing the NetScaler to optimize the responses? (Choose two.)
Scenario: A Citrix Administrator would like to grant access to a Junior Administrator on the NetScaler. The administrator would like to grant full access to everything except the following:
Which pre-existing command policy would meet the needs of the scenario?
Scenario: A Citrix Administrator is troubleshooting a NetScaler issue. The administrator goes to the command line and from the Shell, tails the ns.log to view the log in real time to find the issue. After a few minutes, the administrator noticed that the logs stopped scrolling and the issue was missed.
How can troubleshooting continue using the ns.log?
Scenario: A Citrix Administrator has configured a NetScaler active-passive high availability (HA) pair. When the HA pair fails over, customers are unable to access the hosted websites. After some troubleshooting, the administrator found that the upstream router was NOT updating its ARP table.
What can the administrator configure to resolve this issue?