We at Crack4sure are committed to giving students who are preparing for the CompTIA CAS-003 Exam the most current and reliable questions . To help people study, we've made some of our CompTIA Advanced Security Practitioner (CASP) Exam exam materials available for free to everyone. You can take the Free CAS-003 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
The Chief Executive Officer (CEO) of a fast-growing company no longer knows all the employees and is concerned about the company's intellectual property being stolen by an employee. Employees are allowed to work remotely with flexible hours, creating unpredictable schedules. Roles are poorly defined due to frequent shifting needs across the company. Which of the following new initiatives by the information security team would BEST secure the company and mitigate the CEO's concerns?
A security appliance vendor is reviewing an RFP that is requesting solutions for the defense of a set of web-based applications. This RFP is from a financial institution with very strict performance requirements. The vendor would like to respond with its solutions.
Before responding, which of the following factors is MOST likely to have an adverse effect on the vendor’s qualifications?
A developer is reviewing the following transaction logs from a web application:
Username: John Doe
Street name: Main St.
Street number: <script>alert(‘test’)
Which of the following code snippets should the developer implement given the above transaction logs?
A security engineer is analyzing an application during a security assessment to ensure it is configured to protect against common threats. Given the output below:
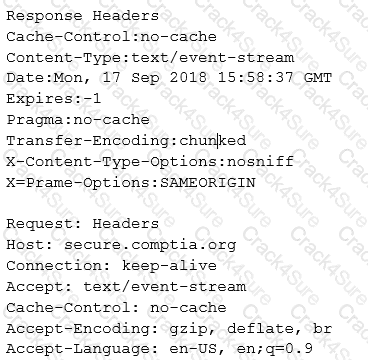
Which of the following tools did the security engineer MOST likely use to generate this output?
A company relies on an ICS to perform equipment monitoring functions that are federally mandated for operation of the facility. Fines for non-compliance could be costly. The ICS has known vulnerabilities and can no longer be patched or updated. Cyber-liability insurance cannot be obtained because insurance companies will not insure this equipment.
Which of the following would be the BEST option to manage this risk to the company's production environment?
A security engineer is working to secure an organization’s VMs. While reviewing the workflow for creating VMs on demand, the engineer raises a concern about the integrity of the secure boot process of the VM guest.
Which of the following would BEST address this concern?
A company recently implemented a variety of security services to detect various types of traffic that pose a threat to the company. The following services were enabled within the network:
• Scan of specific subsets for vulnerabilities
• Categorizing and logging of website traffic
• Enabling specific ACLs based on application traffic
• Sending suspicious files to a third-party site for validation
A report was sent to the security team that identified multiple incidents of users sharing large amounts of data from an on-premise server to a public site. A small percentage of that data also contained malware and spyware
Which of the following services MOST likely identified the behavior and sent the report?
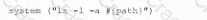
A Chief information Security Officer (CISO) is developing corrective-action plans based on the following from a vulnerability scan of internal hosts:
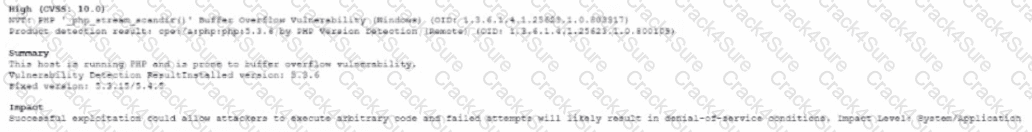
Which of the following MOST appropriate corrective action to document for this finding?
An analyst discovers the following while reviewing some recent activity logs:

Which of the following tools would MOST likely identify a future incident in a timely manner?
Which of the following controls primarily detects abuse of privilege but does not prevent it?
The credentials of a hospital's HVAC vendor were obtained using credential-harvesting malware through a phishing email. The HVAC vendor has administrative privileges m the SCADA network. Which of the following would prevent this from happening again in the future?
A Chief Information Security Officer (CISO) wants to set up a SOC to respond to security threats and events more quickly. The SOC must have the following capacities:
• Real-time response
• Visualization
• Threat intelligence integration
• Cross-referencing from multiple sources
• Deduplication
Which of the following technologies would BEST meet these requirements?
A company recently developed a new mobile application that will be used to access a sensitive system. The application and the system have the following requirements:
• The application contains sensitive encryption material and should not be accessible over the network
• The system should not be exposed to the Internet
• Communication must be encrypted and authenticated by both the server and the client
Which of the following can be used to install the application on the mobile device? (Select TWO).
A security analyst is responsible for the completion of a vulnerability assessment at a regional healthcare facility The analyst reviews the following Nmap output:
nmap -v -p scription=SMB-check-value ---scription-ags=unsafe =1 192.168.1.0/24
Which of the following is MOST likely what the security analyst is reviewing?
A newly hired systems administrator is trying to connect a new and fully updated, but very customized, Android device to access corporate resources. However, the MDM enrollment process continually fails. The administrator asks a security team member to look into the issue.
Which of the following is the MOST likely reason the MDM is not allowing enrollment?
Following a recent data breach, a company has hired a new Chief Information Security Officer (CISO). The CISO is very concerned about the response time to the previous breach and wishes to know how the security team expects to react to a future attack. Which of the following is the BEST method to achieve this goal while minimizing disruption?
Ann, a member of the finance department at a large corporation, has submitted a suspicious email she received to the information security team. The team was not expecting an email from Ann, and it contains a PDF file inside a ZIP compressed archive. The information security learn is not sure which files were opened. A security team member uses an air-gapped PC to open the ZIP and PDF, and it appears to be a social engineering attempt to deliver an exploit.
Which of the following would provide greater insight on the potential impact of this attempted attack?
A company is acquiring incident response and forensic assistance from a managed security service provider in the event of a data breach. The company has selected a partner and must now provide required documents to be reviewed and evaluated.
Which of the following documents would BEST protect the company and ensure timely assistance? (Choose two.)
A security engineer is designing a system in which offshore, outsourced staff can push code from the development environment to the production environment securely. The security engineer is concerned with data loss, while the business does not want to slow down its development process. Which of the following solutions BEST balances security requirements with business need?
An engineer is evaluating the control profile to assign to a system containing PII, financial, and proprietary data.
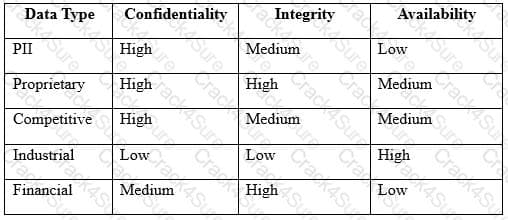
Based on the data classification table above, which of the following BEST describes the overall classification?
A software development team is conducting functional and user acceptance testing of internally developed web applications using a COTS solution. For automated testing, the solution uses valid user credentials from the enterprise directory to authenticate to each application. The solution stores the username in plain text and the corresponding password as an encoded string in a script within a file, located on a globally accessible network share. The account credentials used belong to the development team lead.
To reduce the risks associated with this scenario while minimizing disruption to ongoing testing, which of the following are the BEST actions to take? (Choose two.)
A Chief Information Security Officer (CISO is reviewing and revising system configuration and hardening guides that were developed internally and have been used several years to secure the organization’s systems. The CISO knows improvements can be made to the guides.
Which of the following would be the BEST source of reference during the revision process?
A security manager recently categorized an information system. During the categorization effort, the manager determined the loss of integrity of a specific information type would impact business significantly. Based on this, the security manager recommends the implementation of several solutions. Which of the following, when combined, would BEST mitigate this risk? (Select TWO.)
Engineers at a company believe a certain type of data should be protected from competitors, but the data owner insists the information is not sensitive. An information security engineer is implementing controls to secure the corporate SAN. The controls require dividing data into four groups: non-sensitive, sensitive but accessible, sensitive but export-controlled, and extremely sensitive. Which of the following actions should the engineer take regarding the data?
After multiple availability issues a systems administrator is reviewing the following metrics from the web server farm, which is configured to serve the company's e-commerce site:
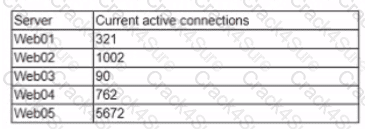
To reduce the availability risk the company should implement a new:
A legacy SCADA system is m place in a manufacturing facility to ensure proper facility operations Recent industry reports made available to the security team state similar legacy systems are being used as part of an attack chain in the same industry market Due to the age of these devices security control options are limned Which of the following would BEST provide continuous monitoring for these threats'
A company is updating its acceptable use and security policies to allow personal devices to be connected to the network as king as certain security parameters can be enforced Which of the following describes this new policy change?
A company protects privileged accounts by using hardware keys as a second factor. A security engineer receives an error while attempting to authenticate with a hardware key for the first time. The engineer confirms the credentials are valid by logging Into a system while MFA is disabled. Which of the following is the MOST likely reason the login is failing?
A new identity management program was recently initialed to reduce risk and improve the employee experience. The environment is complex it does not support rest APIs but has multiple identity stores Password resets are the help desk's top ticket item and it takes the organization weeks to manually create access for new employees. The applications in the scope of the program are the enterprise service bus SaaS web portals and internal web portal. The goals of the program include
• Reducing costs by centralizing authentication and authorization
• Streamlining business processes
• Enabling employees to have immediate access
• Reducing password reset tickets by 90%
To meet the above goals and the business case which of the following authentication and authorization capabilities does the security architect need to implement?
Company policy mandates the secure disposal of sensitive data at the end of the useful lifespan of IT equipment. The IT department donates old devices to charity and recycles truly obsolete equipment In addition to deleting workstations from the systems responsible for monitoring network connections which of the following actions should the company implement? (Select TWO)
A security analyst is examining threats with the following code function:
Which of the following threats should the security analyst report1?
The Chief information Security Officer (CISO) of a small locate bank has a compliance requirement that a third-party penetration test of the core banking application must be conducted annually. Which of the following services would fulfill the compliance requirement with the LOWEST resource usage?
A small company is implementing a new technology that promises greater performance but does not abide by accepted RFCs. Which of the following should the company do to ensure the risks associated with Implementing the standard-violating technology is addressed?
A Chief Information Security Officer (CISO) wants to obtain data from other organizations in the same industry related to recent attacks against industry targets A partner firm m the industry provides information that discloses the attack vector and the affected vulnerability that impacted other firms. The CISO then works with that firm's CERT to evaluate the organization for applicability associated with the intelligence provided. This activity is an example of:
A security analyst is reviewing the following pseudo-output snippet after running the command less /tmp/file,tmp.
The information above was obtained from a public-facing website and used to identify military assets. Which of the following should be implemented to reduce the risk of a similar compromise?
A security auditor needs to review the manner in which an entertainment device operates. The auditor is analyzing the output of a port scanning tool to determine the next steps in the security review. Given the following log output.
The best option for the auditor to use NEXT is:

A security engineer has just been embedded in an agile development team to ensure security practices are maintained during frequent release cycles. A new web application includes an input form. Which of the following would work BEST to allow the security engineer to test how the application handles error conditions?
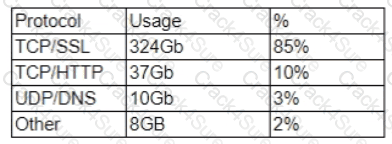
A security researcher at an organization is reviewing potential threats to the VolP phone system infrastructure which uses a gigabit Internet connection. The researcher finds a vulnerability and knows placing an IPS in front of the phone system will mitigate the risk. The researcher gathers the following information about various IPS systems:
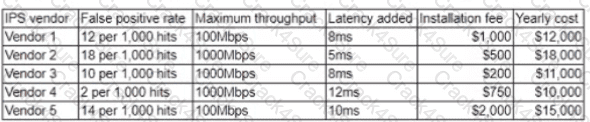
The organization is concerned about cost, but call quality is critical to its operations Which of the foAotmng vendors would be BEST for the organization to choose?
Employees who travel internationally have been issued corporate mobile devices When traveling through border security employees report border police officers have asked them to power on and unlock the* phones and tablets for inspection Non-compliance with these requests may lead to the devices being confiscated After the phones have been unlocked, the police connect them to laptops for several minutes The company rs concerned about potential exposure of IP financial data or other sensitive information Which of the following is MOST likely to protect the company's data m future situations''
A software development company recently implemented a new policy and control ruleset. The control ruleset defines the following:
• Account naming standards
• Password complexity standards
• SOLC practices
• Encryption baselines and standards
A review of the current applications used and developed by the company shows many production and mission-critical applications are not compliant with the new policies and control ruleset. Which of the following actions should be performed''
A company’s existing forward proxies support software-based TLS decryption, but are currently at 60% load just dealing with AV scanning and content analysis for HTTP traffic. More than 70% outbound web traffic is currently encrypted. The switching and routing network infrastructure precludes adding capacity, preventing the installation of a dedicated TLS decryption system. The network firewall infrastructure is currently at 30% load and has software decryption modules that can be activated by purchasing additional license keys. An existing project is rolling out agent updates to end-user desktops as part of an endpoint security refresh.
Which of the following is the BEST way to address these issues and mitigate risks to the organization?
Company.org has requested a black-box security assessment be performed on key cyber terrain. On area of concern is the company’s SMTP services. The security assessor wants to run reconnaissance before taking any additional action and wishes to determine which SMTP server is Internet-facing.
Which of the following commands should the assessor use to determine this information?
During a security event investigation, a junior analyst fails to create an image of a server’s hard drive before removing the drive and sending it to the forensics analyst. Later, the evidence from the analysis is not usable in the prosecution of the attackers due to the uncertainty of tampering. Which of the following should the junior analyst have followed?
A security analyst is reviewing the corporate MDM settings and notices some disabled settings, which consequently permit users to download programs from untrusted developers and manually install them. After some conversations, it is confirmed that these settings were disabled to support the internal development of mobile applications. The security analyst is now recommending that developers and testers have a separate device profile allowing this, and that the rest of the organization’s users do not have the ability to manually download and install untrusted applications. Which of the following settings should be toggled to achieve the goal? (Choose two.)
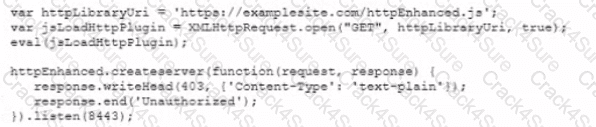
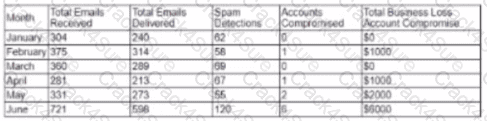
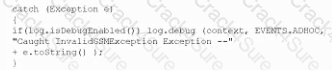
Given the code snippet below:
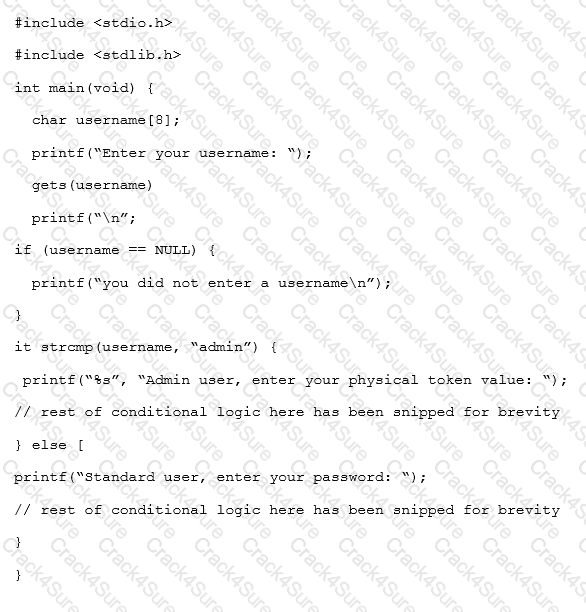
Which of the following vulnerability types in the MOST concerning?
An organization just merged with an organization in another legal jurisdiction and must improve its network security posture in ways that do not require additional resources to implement data isolation. One recommendation is to block communication between endpoint PCs. Which of the following would be the BEST solution?
Given the following information about a company’s internal network:
User IP space: 192.168.1.0/24
Server IP space: 192.168.192.0/25
A security engineer has been told that there are rogue websites hosted outside of the proper server space, and those websites need to be identified. Which of the following should the engineer do?
A security analyst is inspecting pseudocode of the following multithreaded application:
1. perform daily ETL of data
1.1 validate that yesterday’s data model file exists
1.2 validate that today’s data model file does not exist
1.2 extract yesterday’s data model
1.3 transform the format
1.4 load the transformed data into today’s data model file
1.5 exit
Which of the following security concerns is evident in the above pseudocode?
The Chief Information Officer (CISO) is concerned that certain systems administrators will privileged access may be reading other users’ emails. Review of a tool’s output shows the administrators have used web mail to log into other users’ inboxes.
Which of the following tools would show this type of output?
A systems administrator at a medical imaging company discovers protected health information (PHI) on a general purpose file server. Which of the following steps should the administrator take NEXT?
An organization implemented a secure boot on its most critical application servers which produce content and capability for other consuming servers A recent incident, however led the organization to implement a centralized attestation service for these critical servers. Which of the following MOST likely explains the nature of the incident that caused the organization to implement this remediation?
A bank is initiating the process of acquiring another smaller bank. Before negotiations happen between the organizations, which of the following business documents would be used as the FIRST step in the process?
Several corporate users returned from an international trip with compromised operating systems on their cellular devices Additionally. intelligence reports confirm some international carriers are able to modify firmware unexpectedly even when the WDM policy is set to disable FOTA updates Which of the following mitigations is operationally feasible and MOST likely to reduce the risk of firmware compromise by a carrier white traveling internationally?
An aircraft manufacturer is developing software that will perform automatic flight control (auto-pilot) Given the high safety criticality of the software the developer can BEST prove software correctness to a requirement’s specification by employing:
A security tester is performing a Mack-box assessment of an RFID access control system. The tester has a handful of RFID tags and is able to access the reader However, the tester cannot disassemble the reader because it is in use by the company. Which of the following shows the steps the tester should take to assess the RFID access control system m the correct order?
A cybersecurity analyst is conducting packet analysis on the following:
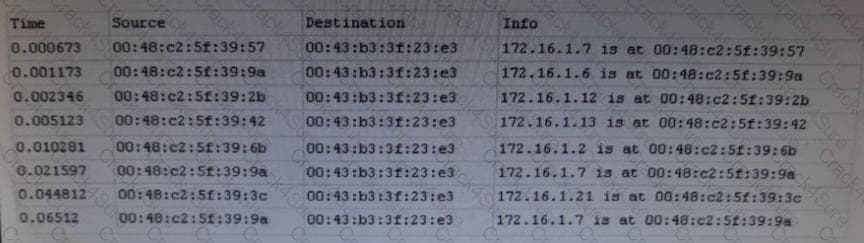
Which of the following is occurring in the given packet capture?
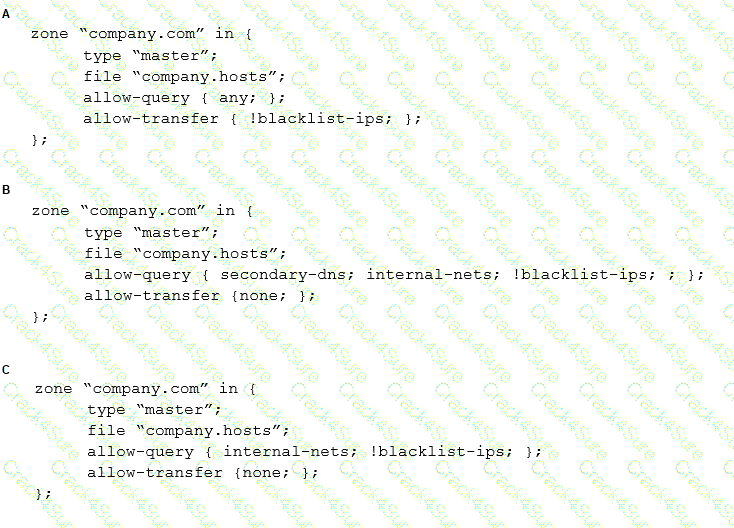
A security engineer is assessing the controls that are in place to secure the corporate-Internet-facing DNS server. The engineer notices that security ACLs exist but are not being used properly. The DNS server should respond to any source but only provide information about domains it has authority over. Additionally, the DNS administrator have identified some problematic IP addresses that should not be able to make DNS requests. Given the ACLs below:
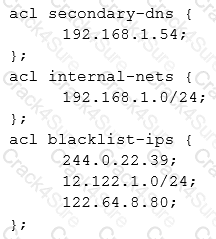
Which of the following should the security administrator configure to meet the DNS security needs?
Following a recent network intrusion, a company wants to determine the current security awareness of all of its employees. Which of the following is the BEST way to test awareness?
A corporate forensic investigator has been asked to acquire five forensic images of an employee database application. There are three images to capture in the United States, one in the United Kingdom, and one in Germany. Upon completing the work, the forensics investigator saves the images to a local workstation. Which of the following types of concerns should the forensic investigator have about this work assignment?
A manufacturing company employs SCADA systems to drive assembly lines across geographically dispersed sites. Therefore, the company must use the Internet to transport control messages and responses. Which of the following architectural changes when integrated will BEST reduce the manufacturing control system's attack surface? (Select TWO)
The audit team was only provided the physical and logical addresses of the network without any type of access credentials.
Which of the following methods should the audit team use to gain initial access during the security assessment? (Choose two.)
A security analyst has requested network engineers integrate sFlow into the SOC’s overall monitoring picture. For this to be a useful addition to the monitoring capabilities, which of the following must be considered by the engineering team?
A cloud architect is moving a distributed system to an external cloud environment. The company must be able to
•Administer the server software at OS and application levels
• Show the data being stored is physically separated from other tenants
• Provide remote connectivity for MSSPs
Which of the following configurations and architectures would BEST support these requirements?
A laptop is recovered a few days after it was stolen.
Which of the following should be verified during incident response activities to determine the possible impact of the incident?
The Chief Information Security Officer (CISO) has asked the security team to determine whether the organization is susceptible to a zero-day exploit utilized in the banking industry and whether attribution is possible. The CISO has asked what process would be utilized to gather the information, and then wants to apply signatureless controls to stop these kinds of attacks in the future. Which of the following are the MOST appropriate ordered steps to take to meet the CISO’s request?
A security incident responder discovers an attacker has gained access to a network and has overwritten key system files with backdoor software. The server was reimaged and patched offline.
Which of the following tools should be implemented to detect similar attacks?
An enterprise’s Chief Technology Officer (CTO) and Chief Information Security Officer (CISO) are meeting to discuss ongoing capacity and resource planning issues. The enterprise has experienced rapid, massive growth over the last 12 months, and the technology department is stretched thin for resources. A new accounting service is required to support the enterprise’s growth, but the only available compute resources that meet the accounting service requirements are on the virtual platform, which is hosting the enterprise’s website.
Which of the following should the CISO be MOST concerned about?
A company has decided to replace all the T-1 uplinks at each regional office and move away from using the existing MPLS network. All regional sites will use high-speed connections and VPNs to connect back to the main campus. Which of the following devices would MOST likely be added at each location?
A company’s security policy states any remote connections must be validated using two forms of network-based authentication. It also states local administrative accounts should not be used for any remote access. PKI currently is not configured within the network. RSA tokens have been provided to all employees, as well as a mobile application that can be used for 2FA authentication. A new NGFW has been installed within the network to provide security for external connections, and the company has decided to use it for VPN connections as well. Which of the following should be configured? (Choose two.)
A company is the victim of a phishing and spear-phishing campaign Users are Clicking on website links that look like common bank sites and entering their credentials accidentally A security engineer decides to use a layered defense to prevent the phishing or lessen its impact Which of the following should the security engineer implement? (Select TWO)
The security administrator of a small firm wants to stay current on the latest security vulnerabilities and attack vectors being used by crime syndicates and nation-states. The information must be actionable and reliable. Which of the following would BEST meet the needs of the security administrator?
A security administrator is concerned about employees connecting their personal devices to the company network. Doing so is against company policy. The network does not have a NAC solution. The company uses a GPO that disables the firewall on all company-owned devices while they are connected to the internal network Additionally, all company-owned devices implement a standard naming convention that uses the device's serial number. The security administrator wants to identify active personal devices and write a custom script to disconnect them from the network Which of the following should the script use to BEST accomplish this task?
An administrator wants to ensure hard drives cannot be removed from hosts and men installed into and read by unauthorized hosts Which of the following techniques would BEST support this?
A company requires a task to be carried by more than one person concurrently. This is an example of:
A company suspects a web server may have been infiltrated by a rival corporation. The security engineer reviews the web server logs and finds the following:
The security engineer looks at the code with a developer, and they determine the log entry is created when the following line is run:
Which of the following is an appropriate security control the company should implement?
An information security officer reviews a report and notices a steady increase in outbound network traffic over the past ten months. There is no clear explanation for the increase The security officer interviews several business units and discovers an unsanctioned cloud storage provider was used to share marketing materials with potential customers. Which of the following services would be BEST for the security officer to recommend to the company?
A company's Chief Information Security Officer (CISO) is working with the product owners to perform a business impact assessment. The product owners provide feedback related to the critically of various business processes, personal, and technologies. Transitioning into risk assessment activities, which of the following types of information should the CISO require to determine the proper risk ranking? (Select TWO).
A financial institution has several that currently employ the following controls:
* The severs follow a monthly patching cycle.
* All changes must go through a change management process.
* Developers and systems administrators must log into a jumpbox to access the servers hosting the data using two-factor authentication.
* The servers are on an isolated VLAN and cannot be directly accessed from the internal production network.
An outage recently occurred and lasted several days due to an upgrade that circumvented the approval process. Once the security team discovered an unauthorized patch was installed, they were able to resume operations within an hour. Which of the following should the security administrator recommend to reduce the time to resolution if a similar incident occurs in the future?
A new security policy slates all wireless and wired authentication must include the use of certificates when connecting to internal resources within the enterprise LAN by all employees Which of the following should be configured to comply with the new security policy? (Select TWO).
A cybersecurity analyst created the following tables to help determine the maximum budget amount the business can justify spending on an improved email filtering system:

Which of the following meets the budget needs of the business?
A system engineer is reviewing output from a web application vulnerability scan. The engineer has determined data is entering the application from an untrusted source and is being used to construct a query dynamically. Which of the following code snippets would BEST protect the application against an SQL injection attack?
A)
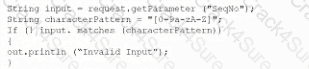
B)
C)
D)
A company runs a well –attended, on-premises fitness club for its employees, about 200 of them each day. Employees want to sync center’s login and attendance program with their smartphones. Human resources, which manages the contract for the fitness center, has asked the security architecture to help draft security and privacy requirements. Which of the following would BEST address these privacy concerns?
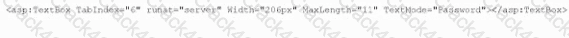
A security engineer is helping the web developers assess a new corporate web application The application will be Internet facing so the engineer makes the following recommendation:
In an htaccess file or the site config add:
or add to the location block:
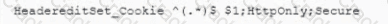
Which of the following is the security engineer trying to accomplish via cookies? (Select TWO)
A researcher is working to identify what appears to be a new variant of an existing piece of malware commonly used in ransomware attacks While it is not identical to the malware previously evaluated. it has a number of similarities including language, payload. and algorithms. Which of the following would help the researcher safely compare the code base of the two variants?
The email administrator must reduce the number of phishing emails by utilizing more appropriate security controls The following configurations already are in place
• Keyword Mocking based on word lists
• URL rewriting and protection
• Stopping executable files from messages
Which of the following is the BEST configuration change for the administrator to make?
A security administrator is investigating an incident involving suspicious word processing documents on an employee's computer, which was found powered off in the employee's office. Which of the following tools is BEST suited for extracting full or partial word processing documents from unallocated disk space?
A company’s IT department currently performs traditional patching, and the servers have a significant longevity that may span over five years. A security architect is moving the company toward an immune server architecture in which servers are replaced rather than patched. Instead of having static servers for development, test, and production, the severs will move from environment to environment dynamically. Which of the following are required to move to this type of architecture? (Select Two.)
Ann, a CIRT member, is conducting incident response activities on a network that consists of several hundred virtual servers and thousands of endpoints and users. The network generates more than 10,000 log messages per second. The enterprise belong to a large, web-based cryptocurrency startup, Ann has distilled the relevant information into an easily digestible report for executive management . However, she still needs to collect evidence of the intrusion that caused the incident. Which of the following should Ann use to gather the required information?
A cloud architect needs to isolate the most sensitive portion of the network while maintaining hosting in a public cloud Which of the following configurations can be employed to support this effort?
An application development company implements object reuse to reduce life-cycle costs for the company and its clients Despite the overall cost savings, which of the following BEST describes a security risk to customers inherent within this model?
A security analyst is reviewing an endpoint that was found to have a rookit installed. The rootkit survived multiple attempts to clean the endpoints, as well as an attempt to reinstall the QS. The security analyst needs to implement a method to prevent other endpoint from having similar issues. Which of the following would BEST accomplish this objective?
A smart switch has the ability to monitor electrical levels and shut off power to a building in the event of power surge or other fault situation. The switch was installed on a wired network in a hospital and is monitored by the facilities department via a cloud application. The security administrator isolated the switch on a separate VLAN and set up a patching routine. Which of the following steps should also be taken to harden the smart switch?
A security engineer is troubleshooting an issue in which an employee is getting an IP address in the range on the wired network. The engineer plus another PC into the same port, and that PC gets an IP address in the correct range. The engineer then puts the employee’ PC on the wireless network and finds the PC still not get an IP address in the proper range. The PC is up to date on all software and antivirus definitions, and the IP address is not an APIPA address. Which of the following is MOST likely the problem?
Several days after deploying an MDM for smartphone control, an organization began noticing anomalous behavior across the enterprise Security analysts observed the following:
• Unauthorized certificate issuance
• Access to mutually authenticated resources utilizing valid but unauthorized certificates
• Granted access to internal resources via the SSL VPN
To address the immediate problem security analysts revoked the erroneous certificates. Which of the following describes the MOST likely root cause of the problem and offers a solution?
A company's Internet connection is commonly saturated during business hours, affecting Internet availability. The company requires all Internet traffic to be business related After analyzing the traffic over a period of a few hours, the security administrator observes the following:
The majority of the IP addresses associated with the TCP/SSL traffic resolve to CDNs Which of the following should the administrator recommend for the CDN traffic to meet the corporate security requirements?
A security administrator wants to implement an MDM solution to secure access to company email and files in a BYOD environment. The solution must support the following requirements:
* Company administrators should not have access to employees' personal information.
* A rooted or jailbroken device should not have access to company sensitive information.
Which of the following BEST addresses the associated risks?