We at Crack4sure are committed to giving students who are preparing for the CompTIA CV0-004 Exam the most current and reliable questions . To help people study, we've made some of our CompTIA Cloud+ (V4) exam materials available for free to everyone. You can take the Free CV0-004 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Which of the following is true of SSDs?
A cloud engineer is troubleshooting an application that consumes multiple third-party REST APIs. The application is randomly experiencing high latency. Which of the following would best help determine the source of the latency?
A cloud administrator deploys new VMs in a cluster and discovers they are getting IP addresses in the range of 169.254.0.0/16. Which of the following is the most likely cause?
A cloud engineer has provisioned a VM for a high-frequency trading application. After the VM is put into production, users report high latency in trades. The engineer checks the last six hours of VM metrics and sees the following:
• CPU utilization is between 30% to 60%.
• Networkln is between 50Kbps and 70Kbps.
• NetworkOut is between 3.000Kpbs and 5.000Kbps.
• DiskReadOps is at 30.
• DiskWriteOps is at 70
• Memory utilization is between 50% and 70%.
Which of the following steps should the engineer take next to solve the latency issue?
Which of the following models will best reduce the cost of running short-term, non-critical workloads?
Which of the following describes the main difference between public and private container repositories?
A cloud engineer was deploying the company's payment processing application, but it failed with the following error log:
ERFOR:root: Transaction failed http 429 response, please try again Which of the following are the most likely causes for this error? (Select two).
A company implements a web farm with 100 servers behind an application load balancer. Dunng scaling events, new web servers that are placed in service have not loaded all their modules, which causes some requests to the web farm to fail. Which of the following should the cloud engineer implement to address the scaling issue?
A customer is migrating applications to the cloud and wants to grant authorization based on the classification levels of each system. Which of the following should the customer implement to ensure authorisation to systems is granted when the user and system classification properties match? (Select two).
An organization needs to retain its data for compliance reasons but only when required. Which of the following would be the most cost-effective type of tiered storage?
Which of the following cloud deployment strategies is best for an organization that wants to run open-source workloads with other organizations that are sharing the cost?
Which of the following application migration strategies will best suit a customer who wants to move a simple web application from an on-premises server to the cloud?
A cloud engineer wants to implement a monitoring solution to detect cryptojacking and other cryptomining malware on cloud instances. Which of the following metrics would most likely be used to identify the activity?
A user's assigned cloud credentials are locked, and the user is unable to access the project's application. The cloud administrator reviews the logs and notices several attempts to log in with the user's account were made to a different application after working hours. Which of the following is the best approach for the administrator to troubleshoot this issue?
Which of the following is the most cost-effective way to store data that is infrequently accessed?
The change control board received a request to approve a configuration change 10 deploy in the cloud production environment. Which of the following should have already been competed?
An on-call cloud engineer receives a critical alert about an e-commerce web server being unresponsive. Which of the following steps should the engineer take first?
A manager wants information about which users signed in to a certain VM during the past month. Which of the following can the cloud administrator use to obtain this information?
A DevOps engineer is integrating multiple systems. Each system has its own API that exchanges data based on different application-level transactions. Which of the following
delivery mechanisms would best support this integration?
Which of the following refers to the idea that data should stay within certain borders or territories?
A newly configured VM fails to run application updates despite having internet access. The updates download automatically from a third-party network. Given the following output:
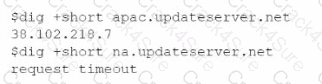
Which of the following troubleshooting steps would be best to take?
A cross-site request forgery vulnerability exploited a web application that was hosted in a public laaS network. A security engineer determined that deploying a WAF in blocking mode at a CDN would prevent the application from being exploited again. However, a week after implementing the WAF, the application was exploited again. Which of the following should the security engineer do to make the WAF control effective?
A cloud administrator needs to distribute workloads across remote data centers for redundancy reasons. Which of the following deployment strategies would eliminate downtime, accelerate deployment, and remain cost efficient?
A company's man web application is no longer accessible via the internet. The cloud administrator investigates and discovers the application is accessible locally and only via an IP access. Which of the following was misconfigured?
An administrator needs to adhere to the following requirements when moving a customer's data to the cloud:
• The new service must be geographically dispersed.
• The customer should have local access to data
• Legacy applications should be accessible.
Which of the following cloud deployment models is most suitable?
Which of the following is the correct order of the steps to take when a system is suspected of being vulnerable?
A company hosts various containerized applications for business uses. A client reports that one of its routine business applications fails to load the web-based login prompt hosted in the company cloud.
Click on each device and resource. Review the configurations, logs, and characteristics of each node in the architecture to diagnose the issue. Then, make the necessary changes to the WAF configuration to remediate the issue.
A company uses containers to implement a web application. The development team completed internal testing of a new feature and is ready to move the feature to the production
environment. Which of the following deployment models would best meet the company's needs while minimizing cost and targeting a specific subset of its users?
Servers in the hot site are clustered with the main site.
A company runs a discussion forum that caters to global users. The company's monitoring system reports that the home page suddenly is seeing elevated response times, even
though internal monitoring has reported no issues or changes. Which of the following is the most likely cause of this issue?
A company wants to create a few additional VDIs so support vendors and contractors have a secure method to access the company's cloud environment. When a cloud
administrator attempts to create the additional instances in the new locations, the operation is successful in some locations but fails in others. Which of the following is the
most likely reason for this failure?
Which of the following is a field of computer science that enables computers to identify and understand objects and people in images and videos?
Department supervisors have requested a report that will help them understand the utilization of cloud resources, make decisions about budgeting for the following year, and reduce
costs. Which of the following are the most important requisite steps to create the report? (Select two).
A company has ten cloud engineers working on different manual cloud deployments. In the past, engineers have had difficulty keeping deployments consistent. Which of the following is the best method to address this issue?
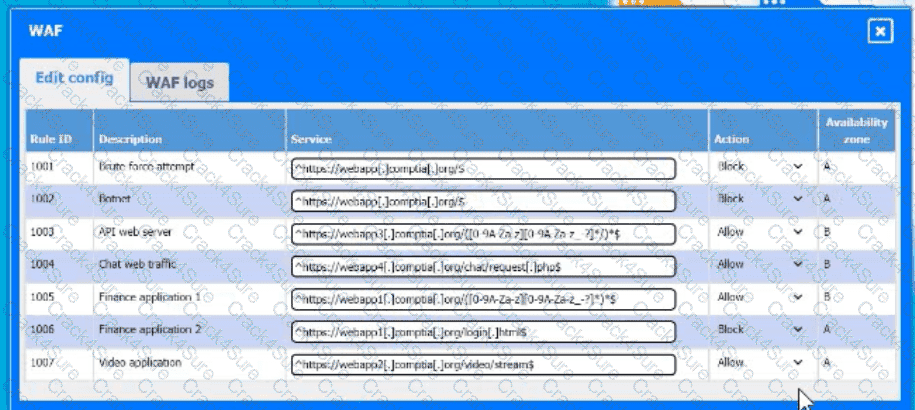
A developer is building a new application version using a CI/CD pipeline. The developer receives the following error message log when the build fails:
Which of the following is the most likely cause of this failure?
A cloud security analyst is looking for existing security vulnerabilities on software applications. Which of the following describes this vulnerability management phase?
Which of the following technologies should be used by a person who is visually impaired to access data from the cloud?
A DevOps engineer is performing maintenance on the mail servers for a company's web application. Part of this maintenance includes checking core operating system updates. The servers are currently running version 3.2 of the operating system. The engineer has two update options—one to version 4.1 and the other to version 3.7. Both versions are fully supported by the operating system manufacturer. Which of the following best describes the action the engineer should take?
A cloud solutions architect needs to have consistency between production, staging, and development environments. Which of the following options will best achieve this goal?
A cloud administrator is building a company-standard VM image, which will be based on a public image. Which of the following should the administrator implement to secure the image?
A company needs to deploy its own code directly in the cloud without provisioning additional infrastructure. Which of the following is the best cloud service model for the company to use?
A systems administrator is configuring backups on a VM and needs the process to run as quickly as possible, reducing the bandwidth on the network during all times from Monday through Saturday. In the event of data corruption, the management team expects the mean time to recovery to be as low as possible. Which of the following backup methods can the administrator use to accomplish these goals?
The performance of an e-commerce website decreases dramatically during random periods. The IT team is evaluating available resources to mitigate the situation. Which of the following is the best approach to effectively manage this scenario'?
An organization's security policy states that software applications should not exchange sensitive data in cleartext. The security analyst is concerned about a software application that uses Base64 to encode credit card data. Which of the following would be the best algorithm to replace Base64?
A cloud engineer wants to run a script that increases the volume storage size if it is below 100GB. Which of the following should the engineer run?
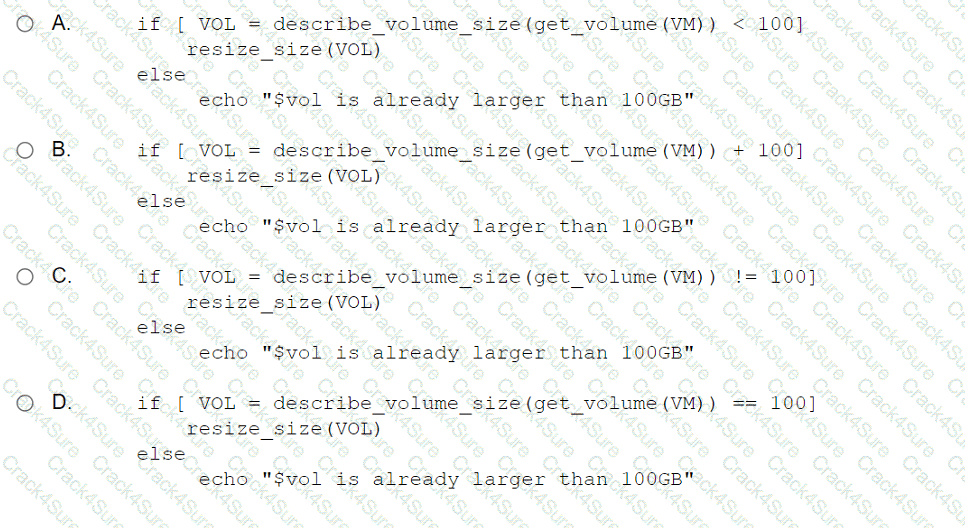
A CI/CD pipeline is used to deploy VMs to an laaS environment. Which of the following can be used to harden the operating system once the VM is running?
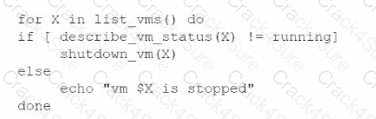
An administrator is creating a cron job that shuts down the virtual machines at night to save on costs. Which of the following is the best way to achieve this task?
A)
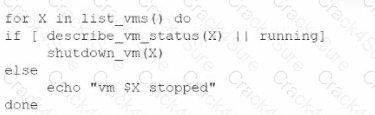
B)
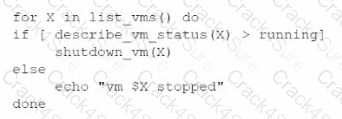
C)
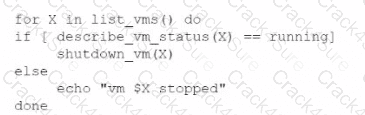
D)
A company's website suddenly crashed. A cloud engineer investigates the following logs:
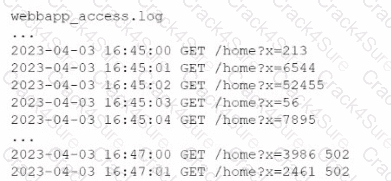
Which of the following is the most likely cause of the issue?
A cloud engineer is exploring options to reduce the management overhead of the servers and network. Which of the following cloud service models should the engineer implement?
An on-premises data center is located in an earthquake-prone location. The workload consists of real-time, online transaction processing. Which ot the following data protection strategies should be used to back up on-premises data to the cloud while also being cost effective?
A log-parsing application requires significant processing power to ingest the logs streaming from web servers. The engineering team presents the cloud architect with four proposals
using the same underlying hardware. Which of the following should the cloud architect select in order to minimize the impact of an instance failure while keeping the cost as low as
possible?
An organization's web application experiences penodic bursts of traffic when a new video is launched. Users are reporting poor performance in the middle of the month. Which of the following scaling approaches should the organization use to scale based on forecasted traffic?
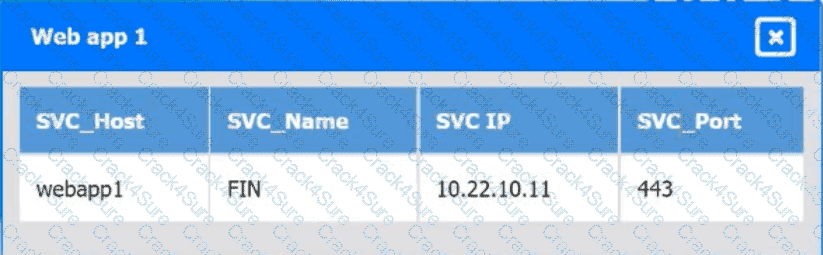
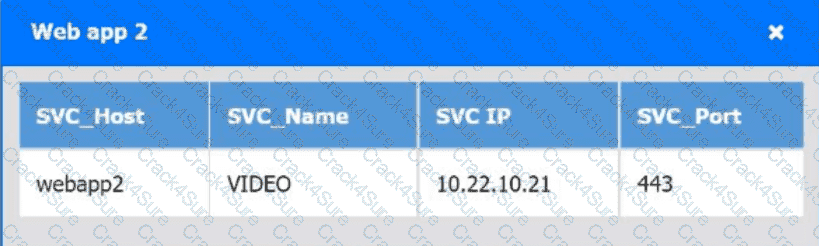
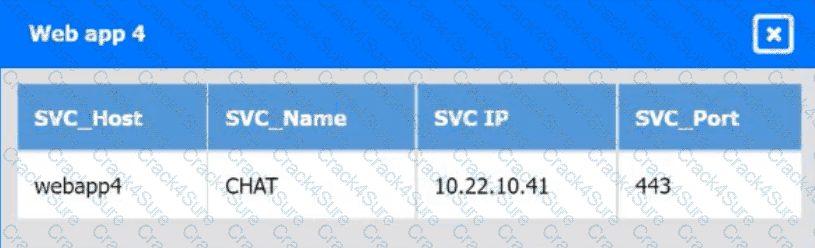
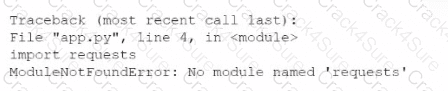
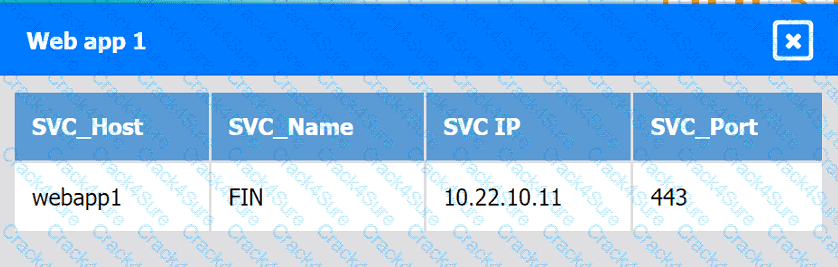
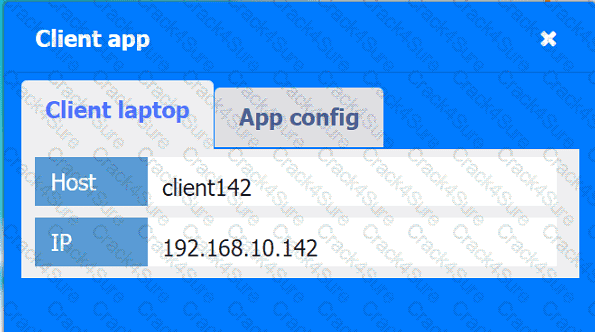
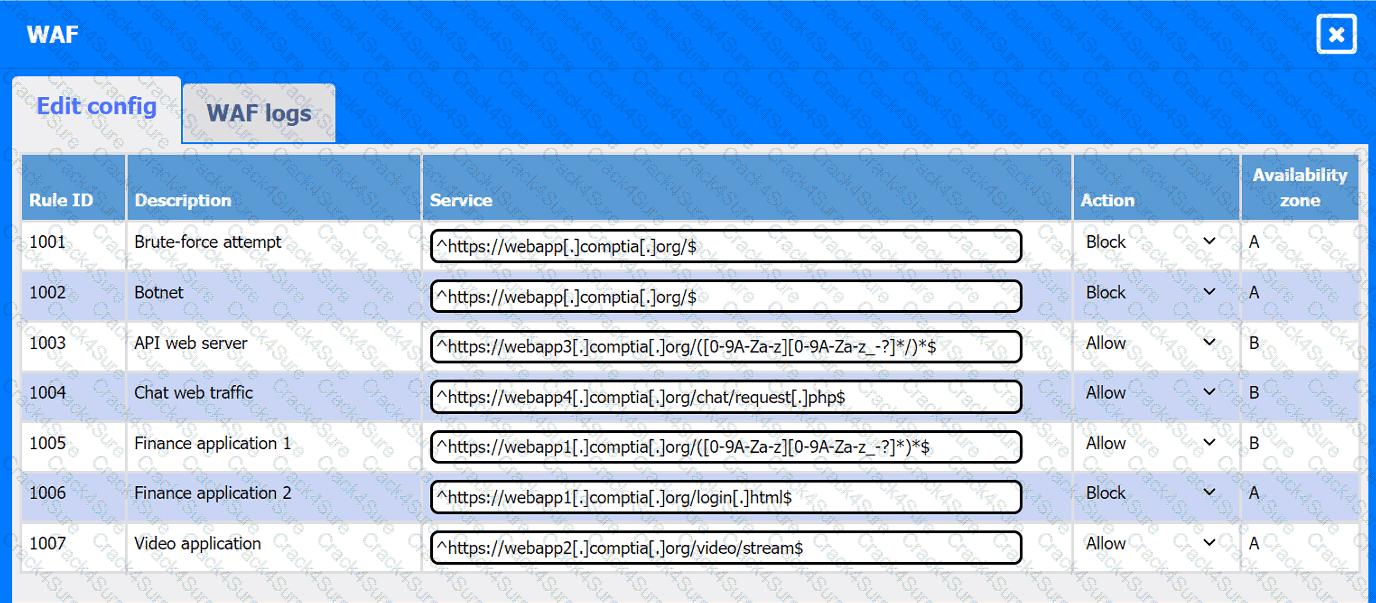
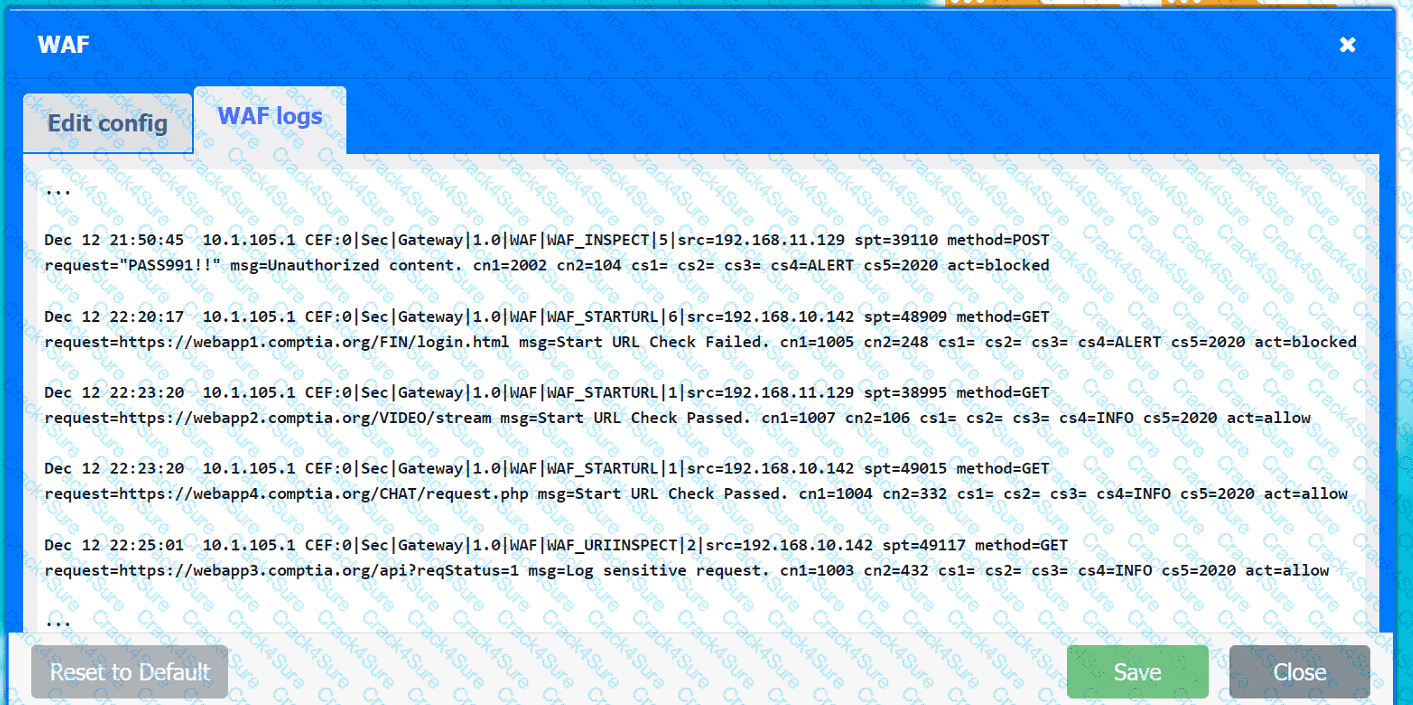
A company hosts various containerized applications for business uses. A client reports that one of its routine business applications fails to load the web-based login prompt hosted in the company cloud.
INSTRUCTIONS
Click on each device and resource. Review the configurations, logs, and characteristics of each node in the architecture to diagnose the issue. Then, make the necessary changes to the WAF configuration to remediate the issue.
Web app 1
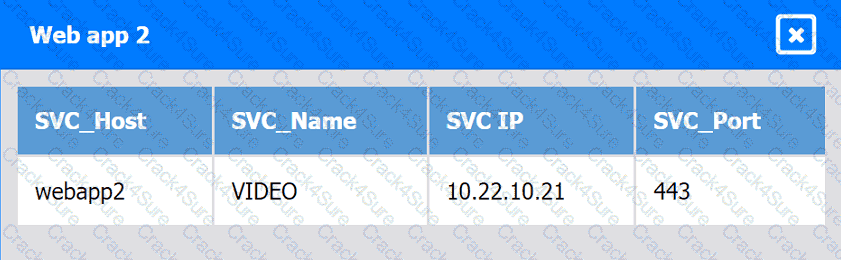
Web app 2
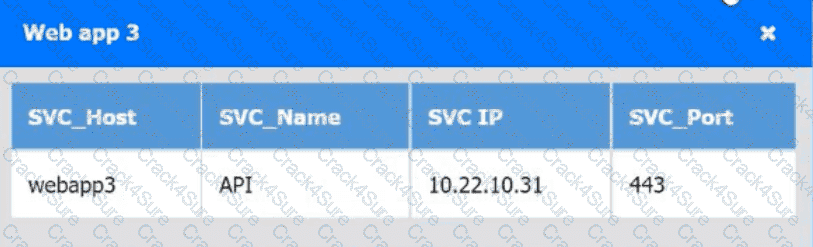
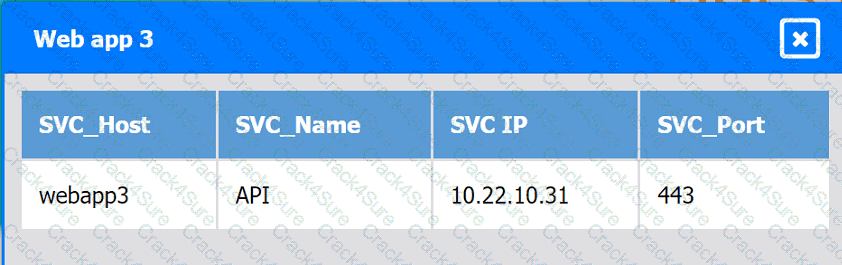
Web app 3
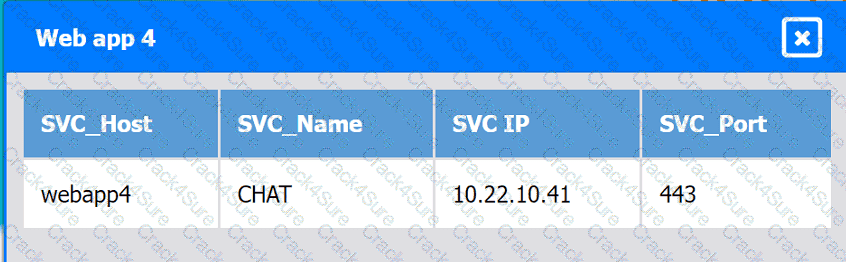
Web app 4
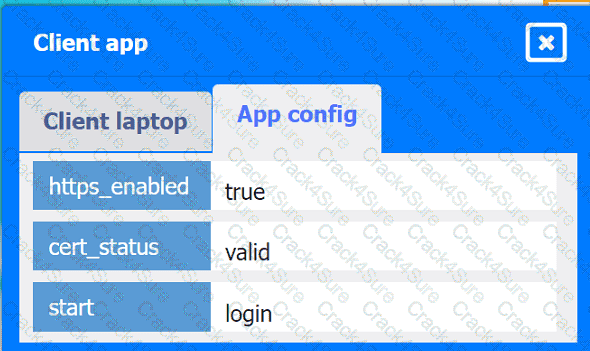
Client app
A developer is testing code that will be used to deploy a web farm in a public cloud. The main code block is a function to create a load balancer and a loop to create 1.000 web servers, as shown below:
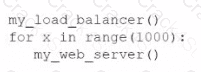
The developer runs the code against the company's cloud account and observes that the load balancer is successfully created, but only 100 web servers have been created. Which of the following should the developer do to fix this issue?
A security engineer recently discovered a vulnerability in the operating system of the company VMs. The operations team reviews the issue and decides all VMs need to be updated
from version 3.4.0 to 3.5. Which of the following best describes the type of update that will be applied?
A systems engineer tries to mount an iSCSI LUN to a VM host in a data center, but the host does not discover any iSCSI targets. A sample of the switch configuration is shown in the following image:
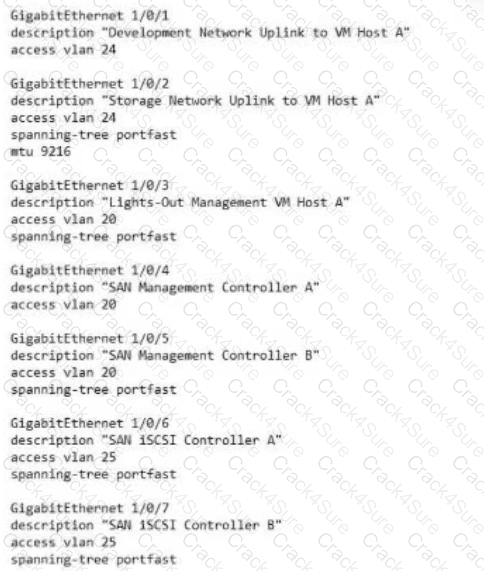
Which of the following configuration changes would most likely resolve the discovery issues?
A cloud engineer is concerned about command-and-control (C2) communication leaving a cloud network over HTTPS. Which of the following should the cloud engineer implement to most efficiently identify this type of communication?
A cloud administrator learns that a major version update. 4.6.0. is available for a business-critical application. The application is currently on version 4.5.2. with additional minor versions 3, 4, and 5 available. The administrator needs to perform the update while minimizing downtime. Which of the following should the administrator do first?
A company’s cybersecurity team receives the following alert that a production VM was deleted from the virtual network:
21 September 09:19:08 (GMT-5)
Resource with ID: PROD-WEB001 was deleted by User: Logging Service
The console to manage virtual network resources uses directory authentication. Only users in a particular directory group can interactively access the virtual network management console. The logging service account is not part of this group and requires some local administration privileges to aggregate logs from various resources. The cybersecurity team discovers the logging service account was previously given full directory administrator privileges and sees the following entry:
21 September 09:10:55 (GMT-5)
User with ID: Logging Service was added to the Group: VNet Console Administrators by actor: Logging Service.
The cybersecurity team removes the compromised service account from the directory group. Which of the following should the cybersecurity team do next to prevent repeat instances of this issue?
A software engineer at a cybersecurity company wants to access the cloud environment. Per company policy, the cloud environment should not be directly accessible via the internet. Which of the following options best describes how the software engineer can access the cloud resources?
Which of the following storage resources provides higher availability and speed for currently used files?
Which of the following should be used on containers to process data and keep the output in files for later review?
Which of the following strategies requires the development of new code before an application can be successfully migrated to a cloud provider?
An organization has been using an old version of an Apache Log4j software component in its critical software application. Which of the following should the organization use to
calculate the severity of the risk from using this component?
Which of the following describes what CRUD is typically used for?
A cloud service provider requires users to migrate to a new type of VM within three months. Which of the following is the best justification for this requirement?
A company recently migrated to a public cloud provider. The company's computer incident response team needs to configure native cloud services tor detailed logging. Which of the following should the team implement on each cloud service to support root cause analysis of past events? {Select two).
A cloud engineer wants containers to run the latest version of a container base image to reduce the number of vulnerabilities. The applications in use requite Python 3.10 and ate not compatible with any other version. The containers' images are created every time a new version is released from the source image. Given the container Dockerfile below:
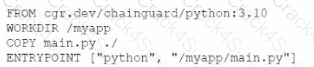
Which of the following actions will achieve the objectives with the least effort?
A high-usage cloud resource needs to be monitored in real time on specific events to guarantee its availability. Which of the following actions should be used to meet this requirement?
A systems engineer is migrating a batch of 25 VMs from an on-premises compute cluster to a public cloud using the public cloud's migration agent. The migration job shows data
copies at a rate of 250Mbps. After five servers migrate, the data copies at a rate of 25Mbps. Which of the following should the engineer review first to troubleshoot?
A cloud solution needs to be replaced without interruptions. The replacement process can be completed in phases, but the cost should be kept as low as possible. Which of the
following is the best strategy to implement?
3 Months Free Update
3 Months Free Update
3 Months Free Update