We at Crack4sure are committed to giving students who are preparing for the CyberArk ACCESS-DEF Exam the most current and reliable questions . To help people study, we've made some of our CyberArk Defender Access (ACC-DEF) exam materials available for free to everyone. You can take the Free ACCESS-DEF Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
A user's account information required for multi-factor authentication is not set up properly and is preventing the user from logging in.
What should you do?
On which operating systems can the CyberArk Authenticator desktop application be installed? (Choose two.)
Which 2FA/MFA options can fulfill the "Something you are" requirement? (Choose two.)
Which Custom Template app connectors are appropriate to use if a website does not require user authentication?
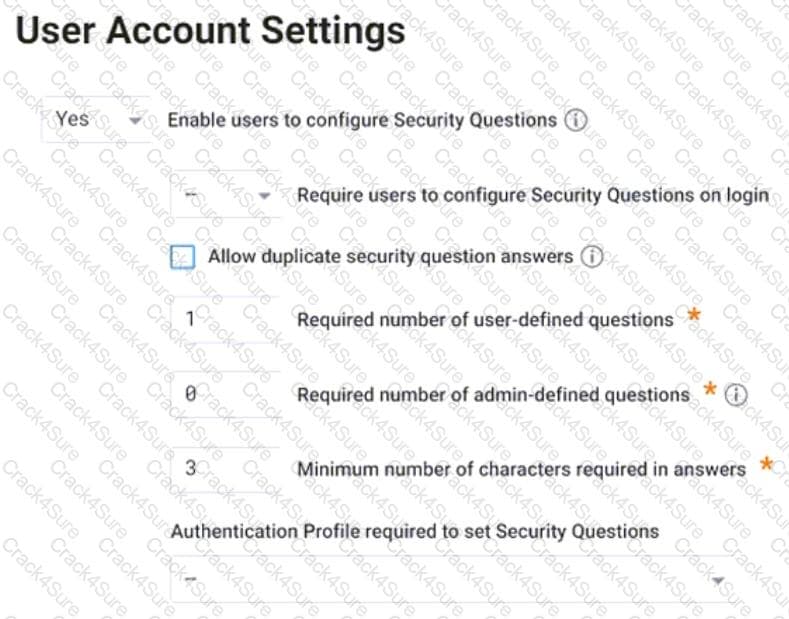
Refer to the exhibit.
Which statement is correct about this configuration shown?
Which settings can help minimize the number of 2FA / MFA prompts? (Choose two.)
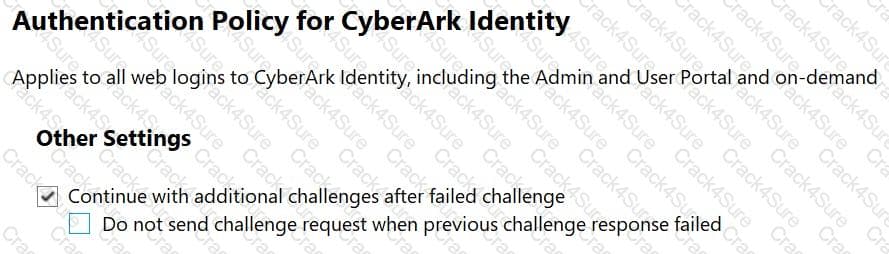
Refer to the exhibit.
Which statements are correct regarding this Authentication Policy? (Choose two.)
Which HR system supports synchronization to both Active Directory and CyberArk Identity Cloud Directory?
CyberArk Identity has created a CLI integration with which vendor?
What is the purpose of the Infinite Apps feature offered by CyberArk Identity?
Which CyberArk Identity supported web standard is commonly used for enterprise Single Sign-On and issues XML tokens for authentication?
You are tasked to enforce certificate based authentication onto all the domain-joined Windows machines within your organization. Based on the inventory record, there are 1000 Windows machines, which include 150 standalone Windows machines. The enrollment will be conducted from either the office network or through the Virtual Private Network (VPN).
Which parameter(s) should you define within the enrollment code to ensure the security of the code and that only the authorized endpoints get registered?
Which risk factors contribute to the user behavior risk score? (Choose two.)
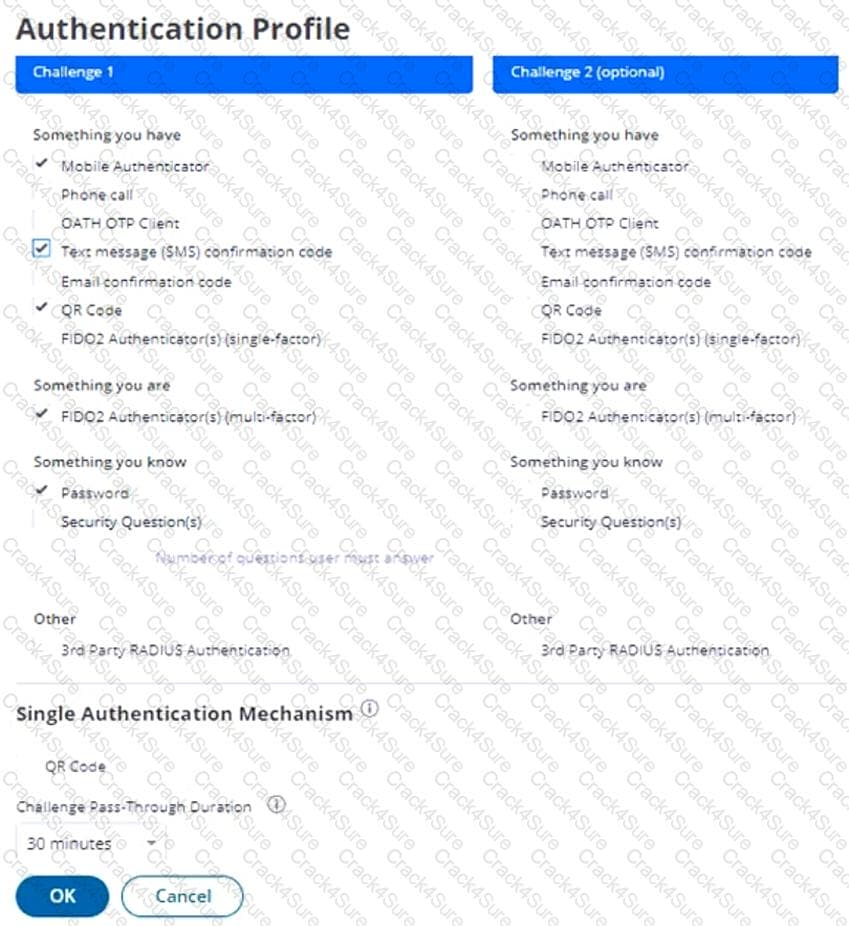
Refer to the exhibit.
How should you configure this default authentication policy to ensure users must authenticate every time they try to access the CyberArk Identity portal or web applications?
3 Months Free Update
3 Months Free Update
3 Months Free Update