We at Crack4sure are committed to giving students who are preparing for the ECCouncil 312-39 Exam the most current and reliable questions . To help people study, we've made some of our Certified SOC Analyst (CSA v2) exam materials available for free to everyone. You can take the Free 312-39 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Which of the following technique protects from flooding attacks originated from the valid prefixes (IP addresses) so that they can be traced to its true source?
SecureTech Inc. operates critical infrastructure and applications in AWS. The SOC detects suspicious activities such as unexpected API calls, unusual outbound traffic from instances, and DNS requests to potentially malicious domains. They need a fully managed AWS security service that continuously monitors for malicious activity, analyzes CloudTrail logs, VPC Flow Logs, and DNS query logs, leverages machine learning and threat intelligence, and provides actionable findings. Which AWS service best fits?
Properly applied cyber threat intelligence to the SOC team help them in discovering TTPs.
What does these TTPs refer to?
Which of the following directory will contain logs related to printer access?
A major financial institution has strict policies preventing unauthorized data transfers. As a SOC analyst, during routine log analysis you detect an anomaly: an employee workstation initiates large file transfers outside business hours, involving highly sensitive customer financial records. You discover remote access from an unfamiliar IP address and an unauthorized USB device connection on the workstation. Given the likelihood of data exfiltration, what should be your first step in responding?
Katie is a SOC analyst at an international financial corporation. Her team needs functionality so the system continuously scans logs for anomalies, identifies suspicious activities, notifies analysts when predefined security thresholds are reached, and generates incidents or tickets to ensure immediate response. It must provide details such as event type, duration, affected device, and OS version. Which function should she configure to achieve this?
John, a SOC analyst, while monitoring and analyzing Apache web server logs, identified an event log matching Regex /(\.|(%|%25)2E)(\.|(%|%25)2E)(\/|(%|%25)2F|\\|(%|%25)5C)/i.
What does this event log indicate?
A SOC analyst receives an alert indicating that the system time on a critical Windows server was changed at 3:00 AM. There are no scheduled maintenance tasks at this time. Unauthorized time changes can be used to evade security controls, such as altering timestamps to obscure malicious activity. The analyst must identify the relevant event codes that log system time modifications and related suspicious behavior. Which of the following Windows Security Event Codes should the analyst review to investigate potential tampering?
An attacker exploits the logic validation mechanisms of an e-commerce website. He successfully purchases a product worth $100 for $10 by modifying the URL exchanged between the client and the server.
Original URL: http://www.buyonline.com/product.aspx?profile=12 &debit=100 Modified URL: http://www.buyonline.com/product.aspx?profile=12 &debit=10
Identify the attack depicted in the above scenario.
Which of the following data source will a SOC Analyst use to monitor connections to the insecure ports?
Where will you find the reputation IP database, if you want to monitor traffic from known bad IP reputation using OSSIM SIEM?
The Security Operations Center (SOC) team is investigating a suspected malware incident during the Analysis Phase of their incident response process. Their primary goal is to validate the initial detection, ensure the threat is real, and gather critical intelligence to understand the scope of the attack. Which action should the SOC team take to confirm initial findings and eliminate false alarms?
The Syslog message severity levels are labelled from level 0 to level 7.
What does level 0 indicate?
A financial services company hosts an online banking platform accessible via a public web portal. The SOC team has deployed Snort IDS to monitor HTTP traffic for potential attacks targeting the login page. One day, a user attempts to log in multiple times, generating a series of failed authentication events. During this time, Snort IDS triggers an alert based on the following rule:
alert tcp any any -> any 80 (msg:"SQL Injection attempt detected"; content:"' OR T=T"; nocase; sid:1000001; rev:1;)
The alert indicates that an incoming HTTP request contained the classic SQL injection payload ' OR T=T, which is commonly used to bypass login authentication by always evaluating to true. The SIEM, integrated with Snort, receives this alert and correlates it with multiple failed login attempts from the same source IP. This triggers an automated response, temporarily blocking the suspicious IP address and notifying the SOC team. Which detection method is used by this rule?
A multinational cybersecurity firm wants to enhance its threat intelligence capabilities by integrating real-time threat feeds into Microsoft Sentinel. These feeds include malicious IPs, domains, file hashes, and attack patterns. The firm requires a standardized protocol that allows automated threat intelligence sharing so Sentinel continuously receives updated indicators from external sources in a structured format. Which Microsoft Sentinel data connector should be implemented to integrate threat intelligence feeds using an industry-standard protocol?
An organization with a complex IT infrastructure is planning to implement a SIEM solution to improve its threat detection and response capabilities. Due to the scale and complexity of its systems, the organization opts for a phased deployment approach to ensure a smooth implementation and reduce potential risks. Which of the following should be the first phase in their SIEM deployment strategy?
Which of the following factors determine the choice of SIEM architecture?
Mark Reynolds, a SOC analyst at a healthcare organization, is monitoring the SIEM system when he detects a potential security threat: a series of unusual login attempts targeting critical patient data servers. After investigating the alerts and collaborating with the incident response team, the SOC determines that the threat has a “Likely” chance of occurring and could cause “Significant” damage, including operational disruptions, financial loss due to data breaches, and regulatory penalties under HIPAA. Using a standard Risk Matrix, how would this risk be categorized in terms of overall severity?
What does the HTTP status codes 1XX represents?
What does HTTPS Status code 403 represents?
A company's SIEM is generating a high number of alerts, overwhelming the SOC team with false positives and irrelevant notifications. This reduces efficiency as analysts struggle to identify genuine incidents. To address this, the security team refines their approach by defining clear threat detection scenarios aligned with their environment and risk profile. This is expected to improve detection accuracy and streamline incident response. Which process is the team implementing?
SecureTech Solutions, a managed security service provider (MSSP), is optimizing its log management architecture to enhance log storage, retrieval, and analysis efficiency. The SOC team needs logs stored in a structured or semi-structured format for easy parsing, querying, and correlation. They choose a format that organizes data in a text file in a tabular structure, where each log entry is stored in rows and columns, and that supports easy export to databases or spreadsheet analysis while maintaining readability. Which log format should they choose?
What does the Security Log Event ID 4624 of Windows 10 indicate?
A financial institution suspects an insider threat due to unauthorized access attempts on restricted databases. However, SIEM alerts lack sufficient information to differentiate between legitimate and malicious access. The SOC manager recommends integrating contextual data to improve detection. Which contextual data source should be integrated in this scenario?
Daniel is a member of an IRT, which was started recently in a company named Mesh Tech. He wanted to find the purpose and scope of the planned incident response capabilities.
What is he looking for?
Identify the attack in which the attacker exploits a target system through publicly known but still unpatched vulnerabilities.
Sarah Chen is a Level 1 SOC analyst at Centex Healthcare. The SOC detected a potential data breach involving unauthorized access to patient records. Multiple departments need constant updates: Legal needs HIPAA compliance implications, HR needs to coordinate staff training responses, and the MSSP requires technical details to assist containment. Which role serves as the central point of communication between these stakeholders?
The SOC team at GlobalTech has finished patching a critical vulnerability exploited during a ransomware attack. The team is now restoring 2.3 TB of encrypted data from their Veeam backup system, rebuilding 23 compromised workstations identified through SIEM logs, and re-enabling network access for the finance department after validating systems are clean. Which Incident Response phase is this?
What type of event is recorded when an application driver loads successfully in Windows?
Jannet works in a multinational corporation that operates multiple data centers, cloud environments, and on-premises systems. As a SOC analyst, she notices that security incidents are taking too long to detect and investigate. After analyzing this, she discovers that logs from firewalls, endpoint security solutions, authentication servers, and cloud applications are scattered across different systems in various formats. Her team has to manually convert logs into a readable format before investigating incidents. What approach should she implement to accept logs from heterogeneous sources with different formats, convert them into a common format, and improve incident detection and response time?
Which of the following Windows features is used to enable Security Auditing in Windows?
What does Windows event ID 4740 indicate?
A health corporation is implementing a SIEM solution to improve detection and response and comply with HIPAA requirements. They need the SIEM to efficiently collect, analyze, and correlate security events from network devices, servers, and security applications, and generate timely alerts for potential HIPAA violations. Which capability is needed to meet these needs?
You are working in a Cybersecurity Operations Center for PayOnline, which handles payment gateways for multiple applications. Your team monitors logs across firewalls, authentication servers, and endpoint detection tools. The team currently relies on manual log reviews, but the volume of raw, unstructured logs makes the process inefficient and error-prone. During a recent incident, the team struggled to extract relevant details from disorganized logs, delaying detection and response. The team decides to implement an automated log parsing solution that can transform unstructured logs into a structured format. Which log parsing technique should you implement to improve log data structuring and enable efficient querying and analysis?
Which of the following formula represents the risk levels?
Which of the following framework describes the essential characteristics of an organization's security engineering process that must exist to ensure good security engineering?
During a routine security audit, analysts discover several web servers still use a vulnerable third-party library flagged for a zero-day exploit. The vulnerability was identified previously and patches were deployed, but the application team rolled back patches due to instability and compatibility issues. The vulnerability remains unaddressed, and no alternative mitigations are in place. How should the security team classify this risk in the context of web application security?
Mark Reynolds, a SOC analyst at a global financial institution, is working on the eradication phase after detecting phishing attacks targeting employees. To ensure attackers cannot reuse malicious infrastructure, Mark implements a technique that blocks known malicious IP addresses used for sending spam emails at the Domain Name System (DNS) level. Which technique is best suited?
A government agency needs to monitor its network for unusual data exfiltration attempts. Traditional log data is insufficient to identify traffic anomalies, so the SIEM team integrates traffic flow data to detect large transfers and unexpected spikes. The team must choose the appropriate protocol to collect IP traffic information from routers and switches. Which protocol should be used?
Which attack works like a dictionary attack, but adds some numbers and symbols to the words from the dictionary and tries to crack the password?
Lisa Carter, a SOC analyst at a financial services firm, is performing a risk assessment following suspicious alerts detected by the SIEM. She evaluates three key factors: the likelihood of an attack succeeding based on current threat intelligence, the impact on critical business operations if the breach occurs, and the value of the assets targeted (e.g., customer data, financial systems). Using the standard risk assessment approach, which scenario represents the highest risk to the organization?
A Security Operations Center (SOC) analyst receives a high-priority alert indicating unusual user activity. An employee account is attempting to access company resources from a different country and outside of their normal working hours. This behavior raises concerns about potential account compromise or unauthorized access. To automate the initial response and quickly restrict access while further investigating the incident, which SOAR playbook would be relevant to adapt and implement?
CyberBank has experienced phishing, insider threats, and attempted data breaches targeting customer financial records. The bank operates across multiple regions and needs a solution offering continuous security monitoring, rapid threat detection, and centralized visibility across all branches. Which solution will provide automated alerting, digital forensics capabilities, and active threat hunting?
An organization wants to implement a SIEM deployment architecture. However, they have the capability to do only log collection and the rest of the SIEM functions must be managed by an MSSP.
Which SIEM deployment architecture will the organization adopt?
Identify the HTTP status codes that represents the server error.
Emmanuel is working as a SOC analyst in a company named Tobey Tech. The manager of Tobey Tech recently recruited an Incident Response Team (IRT) for his company. In the process of collaboration with the IRT, Emmanueljust escalated an incident to the IRT.
What is the first step that the IRT will do to the incident escalated by Emmanuel?
Jony, a security analyst, while monitoring IIS logs, identified events shown in the figure below.
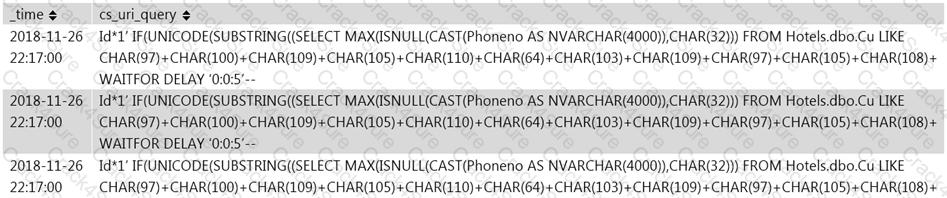
What does this event log indicate?
ABC is a multinational company with multiple offices across the globe, and you are working as an L2 SOC analyst. You are implementing a centralized logging solution to enhance security monitoring. You must ensure that log messages from routers, firewalls, and servers across multiple remote offices are efficiently collected and forwarded to a central syslog server. To streamline this process, an intermediate component is deployed to receive log messages from different devices and forward them to the main syslog server. Which component in the syslog infrastructure performs this function?
Which of the following formula is used to calculate the EPS of the organization?
In a large corporation, the HR department receives an urgent email from someone impersonating a high-level executive, requesting immediate transfer of sensitive employee data. The email includes an official-looking document and a phone number for verification. Feeling pressured, the HR manager calls the number and “confirms” the request, then transfers the data. Investigation later confirms the email was fraudulent and the executive had no knowledge of the request. What type of attack did the HR department face?
NationalHealth, a government agency responsible for managing sensitive patient health records, is subject to strict data sovereignty regulations requiring all data to be stored and processed within the country’s borders. Leadership is concerned about outsourcing security operations and needs complete control over patient data handling. The agency faces increasing cyber threats and requires 24/7 security monitoring. They have a large budget and can hire many security professionals. Which SOC model is most suitable?
Jackson & Co., a mid-sized law firm, is concerned about web-based cyber threats. The IT team implements a solution that serves as an intermediary for all HTTP and HTTPS requests. This allows the SOC to inspect, filter, and control web traffic to detect and block malicious websites, phishing attempts, and other online threats before they reach users. Which containment method is the organization using to gain visibility and control over web traffic?
A large financial organization has experienced an increase in sophisticated cyber threats, including zero-day attacks and APTs. Traditional detection relies heavily on signatures and manual intervention, causing delays. The CISO is exploring AI-driven solutions that can automatically analyze large datasets, detect anomalies, and adapt to evolving threats in real time—identifying suspicious activity without predefined signatures and with minimal human oversight. Which key AI technology should the organization focus on?
Which of the following threat intelligence is used by a SIEM for supplying the analysts with context and "situational awareness" by using threat actor TTPs, malwarecampaigns, tools used by threat actors.
1.Strategic threat intelligence
2.Tactical threat intelligence
3.Operational threat intelligence
4.Technical threat intelligence
Which of the following is a set of standard guidelines for ongoing development, enhancement, storage, dissemination and implementation of security standards for account data protection?
3 Months Free Update
3 Months Free Update
3 Months Free Update