We at Crack4sure are committed to giving students who are preparing for the ECCouncil 312-50 Exam the most current and reliable questions . To help people study, we've made some of our Certified Ethical Hacker Exam exam materials available for free to everyone. You can take the Free 312-50 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Which type of Nmap scan is the most reliable, but also the most visible, and likely to be picked up by and IDS?
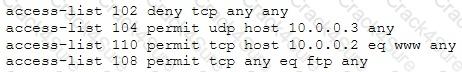
The security administrator of ABC needs to permit Internet traffic in the host 10.0.0.2 and UDP traffic in the host 10.0.0.3. Also he needs to permit all FTP traffic to the rest of the network and deny all other traffic. After he applied his ACL configuration in the router nobody can access to the ftp and the permitted hosts cannot access to the Internet. According to the next configuration what is happening in the network?
You have successfully compromised a machine on the network and found a server that is alive on the same network. You tried to ping it but you didn't get any response back.
What is happening?
Diffie-Hellman (DH) groups determine the strength of the key used in the key exchange process. Which of the following is the correct bit size of the Diffie-Hellman (DH) group 5?
A hacker is attempting to see which IP addresses are currently active on a network. Which NMAP switch would the hacker use?
What two conditions must a digital signature meet?
A botnet can be managed through which of the following?
A penetration tester is attempting to scan an internal corporate network from the internet without alerting the border sensor. Which is the most efficient technique should the tester consider using?
What is the broadcast address for the subnet 190.86.168.0/22?
Which of the following tools will scan a network to perform vulnerability checks and compliance auditing?
A computer technician is using a new version of a word processing software package when it is discovered that a special sequence of characters causes the entire computer to crash. The technician researches the bug and discovers that no one else experienced the problem. What is the appropriate next step?
A technician is resolving an issue where a computer is unable to connect to the Internet using a wireless access point. The computer is able to transfer files locally to other machines, but cannot successfully reach the Internet. When the technician examines the IP address and default gateway they are both on the 192.168.1.0/24. Which of the following has occurred?
Which of the following is a common Service Oriented Architecture (SOA) vulnerability?
Which element of Public Key Infrastructure (PKI) verifies the applicant?
Some passwords are stored using specialized encryption algorithms known as hashes. Why is this an appropriate method?
An attacker has captured a target file that is encrypted with public key cryptography. Which of the attacks below is likely to be used to crack the target file?
The intrusion detection system at a software development company suddenly generates multiple alerts regarding attacks against the company's external webserver, VPN concentrator, and DNS servers. What should the security team do to determine which alerts to check first?
Which vital role does the U.S. Computer Security Incident Response Team (CSIRT) provide?
Which of the following is optimized for confidential communications, such as bidirectional voice and video?
Which of the following levels of algorithms does Public Key Infrastructure (PKI) use?
An IT security engineer notices that the company’s web server is currently being hacked. What should the engineer do next?
Which of the following processes of PKI (Public Key Infrastructure) ensures that a trust relationship exists and that a certificate is still valid for specific operations?
A network security administrator is worried about potential man-in-the-middle attacks when users access a corporate web site from their workstations. Which of the following is the best remediation against this type of attack?
Employees in a company are no longer able to access Internet web sites on their computers. The network administrator is able to successfully ping IP address of web servers on the Internet and is able to open web sites by using an IP address in place of the URL. The administrator runs the nslookup command for www.eccouncil.org and receives an error message stating there is no response from the server. What should the administrator do next?
Which of the following is an example of IP spoofing?
Which statement is TRUE regarding network firewalls preventing Web Application attacks?
Which of the following can the administrator do to verify that a tape backup can be recovered in its entirety?
Which of the following is a hardware requirement that either an IDS/IPS system or a proxy server must have in order to properly function?
Bluetooth uses which digital modulation technique to exchange information between paired devices?
Which of the following programs is usually targeted at Microsoft Office products?
A large company intends to use Blackberry for corporate mobile phones and a security analyst is assigned to evaluate the possible threats. The analyst will use the Blackjacking attack method to demonstrate how an attacker could circumvent perimeter defenses and gain access to the corporate network. What tool should the analyst use to perform a Blackjacking attack?
Which of the following is an application that requires a host application for replication?
Which of the following describes the characteristics of a Boot Sector Virus?
In order to show improvement of security over time, what must be developed?
When utilizing technical assessment methods to assess the security posture of a network, which of the following techniques would be most effective in determining whether end-user security training would be beneficial?
Which system consists of a publicly available set of databases that contain domain name registration contact information?
Passive reconnaissance involves collecting information through which of the following?
A penetration tester was hired to perform a penetration test for a bank. The tester began searching for IP ranges owned by the bank, performing lookups on the bank's DNS servers, reading news articles online about the bank, watching what times the bank employees come into work and leave from work, searching the bank's job postings (paying special attention to IT related jobs), and visiting the local dumpster for the bank's corporate office. What phase of the penetration test is the tester currently in?
An NMAP scan of a server shows port 69 is open. What risk could this pose?
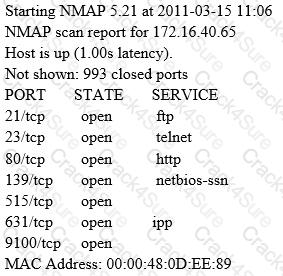
A penetration tester is conducting a port scan on a specific host. The tester found several ports opened that were confusing in concluding the Operating System (OS) version installed. Considering the NMAP result below, which of the following is likely to be installed on the target machine by the OS?
Which of the following techniques will identify if computer files have been changed?
Least privilege is a security concept that requires that a user is
A penetration tester is hired to do a risk assessment of a company's DMZ. The rules of engagement states that the penetration test be done from an external IP address with no prior knowledge of the internal IT systems. What kind of test is being performed?
A Security Engineer at a medium-sized accounting firm has been tasked with discovering how much information can be obtained from the firm's public facing web servers. The engineer decides to start by using netcat to port 80.
The engineer receives this output:
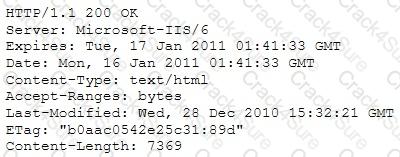
Which of the following is an example of what the engineer performed?
John the Ripper is a technical assessment tool used to test the weakness of which of the following?
The following is a sample of output from a penetration tester's machine targeting a machine with the IP address of 192.168.1.106:
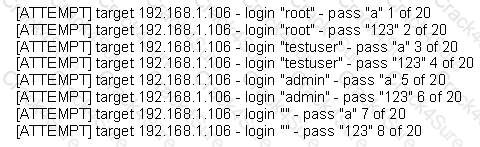
What is most likely taking place?
Which of the following is a preventive control?
How do employers protect assets with security policies pertaining to employee surveillance activities?
Which of the following ensures that updates to policies, procedures, and configurations are made in a controlled and documented fashion?
Which type of security document is written with specific step-by-step details?
Which United States legislation mandates that the Chief Executive Officer (CEO) and the Chief Financial Officer (CFO) must sign statements verifying the completeness and accuracy of financial reports?
Which of the following guidelines or standards is associated with the credit card industry?
When does the Payment Card Industry Data Security Standard (PCI-DSS) require organizations to perform external and internal penetration testing?
Which method can provide a better return on IT security investment and provide a thorough and comprehensive assessment of organizational security covering policy, procedure design, and implementation?
How can a policy help improve an employee's security awareness?
International Organization for Standardization (ISO) standard 27002 provides guidance for compliance by outlining
Which of the following tools would be the best choice for achieving compliance with PCI Requirement 11?
An attacker attaches a rogue router in a network. He wants to redirect traffic to a LAN attached to his router as part of a man-in-the-middle attack. What measure on behalf of the legitimate admin can mitigate this attack?
Which of the following command line switch would you use for OS detection in Nmap?
The "gray box testing" methodology enforces what kind of restriction?
During a penetration test, a tester finds that the web application being analyzed is vulnerable to Cross Site Scripting (XSS). Which of the following conditions must be met to exploit this vulnerability?
Low humidity in a data center can cause which of the following problems?
When creating a security program, which approach would be used if senior management is supporting and enforcing the security policy?
During a penetration test, the tester conducts an ACK scan using NMAP against the external interface of the DMZ firewall. NMAP reports that port 80 is unfiltered. Based on this response, which type of packet inspection is the firewall conducting?
What is the main difference between a “Normal” SQL Injection and a “Blind” SQL Injection vulnerability?
Which of the following conditions must be given to allow a tester to exploit a Cross-Site Request Forgery (CSRF) vulnerable web application?
Which type of scan measures a person's external features through a digital video camera?
What is the main reason the use of a stored biometric is vulnerable to an attack?
A consultant has been hired by the V.P. of a large financial organization to assess the company's security posture. During the security testing, the consultant comes across child pornography on the V.P.'s computer. What is the consultant's obligation to the financial organization?
Which initial procedure should an ethical hacker perform after being brought into an organization?
A certified ethical hacker (CEH) completed a penetration test of the main headquarters of a company almost two months ago, but has yet to get paid. The customer is suffering from financial problems, and the CEH is worried that the company will go out of business and end up not paying. What actions should the CEH take?
An ethical hacker for a large security research firm performs penetration tests, vulnerability tests, and risk assessments. A friend recently started a company and asks the hacker to perform a penetration test and vulnerability assessment of the new company as a favor. What should the hacker's next step be before starting work on this job?
A certified ethical hacker (CEH) is approached by a friend who believes her husband is cheating. She offers to pay to break into her husband's email account in order to find proof so she can take him to court. What is the ethical response?
The precaution of prohibiting employees from bringing personal computing devices into a facility is what type of security control?
How can telnet be used to fingerprint a web server?
In the software security development life cycle process, threat modeling occurs in which phase?
While performing data validation of web content, a security technician is required to restrict malicious input. Which of the following processes is an efficient way of restricting malicious input?
A company has hired a security administrator to maintain and administer Linux and Windows-based systems. Written in the nightly report file is the following:
Firewall log files are at the expected value of 4 MB. The current time is 12am. Exactly two hours later the size has decreased considerably. Another hour goes by and the log files have shrunk in size again.
Which of the following actions should the security administrator take?
Firewalk has just completed the second phase (the scanning phase) and a technician receives the output shown below. What conclusions can be drawn based on these scan results?
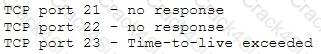
Which of the following cryptography attack methods is usually performed without the use of a computer?
When analyzing the IDS logs, the system administrator noticed an alert was logged when the external router was accessed from the administrator's computer to update the router configuration. What type of an alert is this?
The network administrator for a company is setting up a website with e-commerce capabilities. Packet sniffing is a concern because credit card information will be sent electronically over the Internet. Customers visiting the site will need to encrypt the data with HTTPS. Which type of certificate is used to encrypt and decrypt the data?
What is the correct PCAP filter to capture all TCP traffic going to or from host 192.168.0.125 on port 25?
Which command lets a tester enumerate alive systems in a class C network via ICMP using native Windows tools?
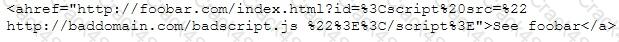
A security administrator notices that the log file of the company’s webserver contains suspicious entries:
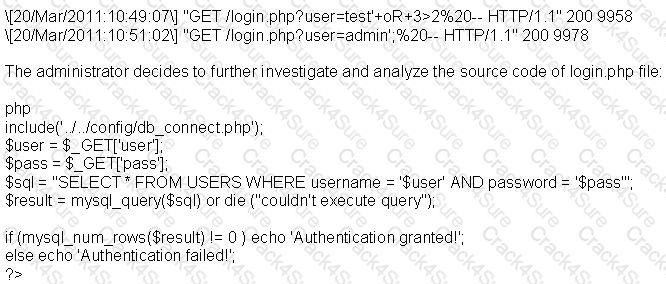
Based on source code analysis, the analyst concludes that the login.php script is vulnerable to
Which of the following is a client-server tool utilized to evade firewall inspection?
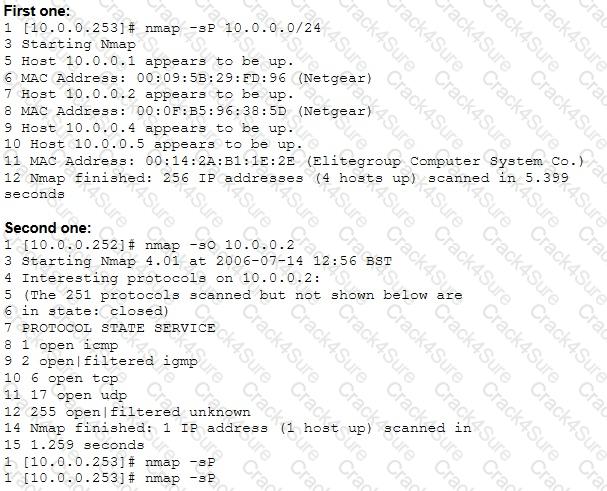
From the two screenshots below, which of the following is occurring?
A company has five different subnets: 192.168.1.0, 192.168.2.0, 192.168.3.0, 192.168.4.0 and 192.168.5.0. How can NMAP be used to scan these adjacent Class C networks?
Which tool is used to automate SQL injections and exploit a database by forcing a given web application to connect to another database controlled by a hacker?
Which of the following identifies the three modes in which Snort can be configured to run?
Which of the following items of a computer system will an anti-virus program scan for viruses?
A hacker is attempting to see which ports have been left open on a network. Which NMAP switch would the hacker use?
Fingerprinting VPN firewalls is possible with which of the following tools?
Which of the following viruses tries to hide from anti-virus programs by actively altering and corrupting the chosen service call interruptions when they are being run?
What is the outcome of the comm”nc -l -p 2222 | nc 10.1.0.43 1234"?
What is a NULL scan?
The practical realities facing organizations today make risk response strategies essential. Which of the following is NOT one of the five basic responses to risk?
Backing up data is a security must. However, it also has certain level of risks when mishandled. Which of the following is the greatest threat posed by backups?
You are the Systems Administrator for a large corporate organization. You need to monitor all network traffic on your local network for suspicious activities and receive notifications when an attack is occurring. Which tool would allow you to accomplish this goal?
Which of the following programming languages is most susceptible to buffer overflow attacks, due to its lack of a built-in-bounds checking mechanism?
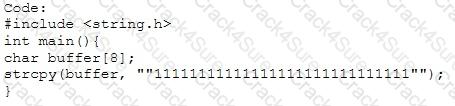
Output:
Segmentation fault
In which phase of the ethical hacking process can Google hacking be employed? This is a technique that involves manipulating a search string with specific operators to search for vulnerabilities.
Example:
allintitle: root passwd
Risks = Threats x Vulnerabilities is referred to as the:
This is an attack that takes advantage of a web site vulnerability in which the site displays content that includes un-sanitized user-provided data.
What is this attack?
Which of the following types of firewalls ensures that the packets are part of the established session?
What would you type on the Windows command line in order to launch the Computer Management Console provided that you are logged in as an admin?
It is a regulation that has a set of guidelines, which should be adhered to by anyone who handles any electronic medical data. These guidelines stipulate that all medical practices must ensure that all necessary measures are in place while saving, accessing, and sharing any electronic medical data to keep patient data secure.
Which of the following regulations best matches the description?
An IT employee got a call from one of our best customers. The caller wanted to know about the company's network infrastructure, systems, and team. New opportunities of integration are in sight for both company and customer. What should this employee do?
Why would an attacker want to perform a scan on port 137?
_________ is a set of extensions to DNS that provide to DNS clients (resolvers) origin authentication of DNS data to reduce the threat of DNS poisoning, spoofing, and similar attacks types.
While doing a Black box pen test via the TCP port (80), you noticed that the traffic gets blocked when you tried to pass IRC traffic from a web enabled host. However, you also noticed that outbound HTTP traffic is being allowed. What type of firewall is being utilized for the outbound traffic?
3 Months Free Update
3 Months Free Update
3 Months Free Update