We at Crack4sure are committed to giving students who are preparing for the ECCouncil 312-96 Exam the most current and reliable questions . To help people study, we've made some of our Certified Application Security Engineer (CASE) JAVA exam materials available for free to everyone. You can take the Free 312-96 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
A developer to handle global exception should use _________ annotation along with @ExceptionHandler method annotation for any class
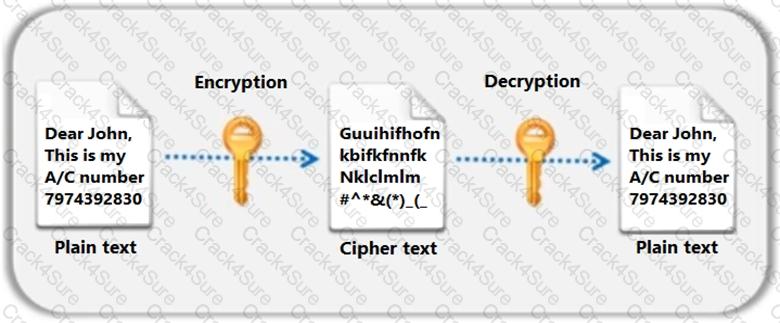
Identify the type of encryption depicted in the following figure.
Which of the following configuration settings in server.xml will allow Tomcat server administrator to impose limit on uploading file based on their size?
Alice, a Server Administrator (Tomcat), wants to ensure that Tomcat can be shut down only by the user who owns the Tomcat process. Select the appropriate setting of the CATALINA_HOME/conf in server.xml that will enable him to do so.
Which of the following relationship is used to describe security use case scenario?
Which of the following state management method works only for a sequence of dynamically generated forms?
Which of the following method will help you check if DEBUG level is enabled?
Which of the risk assessment model is used to rate the threats-based risk to the application during threat modeling process?
Jacob, a Security Engineer of the testing team, was inspecting the source code to find security vulnerabilities.
Which type of security assessment activity Jacob is currently performing?
3 Months Free Update
3 Months Free Update
3 Months Free Update