We at Crack4sure are committed to giving students who are preparing for the EMC DEA-1TT5 Exam the most current and reliable questions . To help people study, we've made some of our Associate - Information Storage and Management Exam exam materials available for free to everyone. You can take the Free DEA-1TT5 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
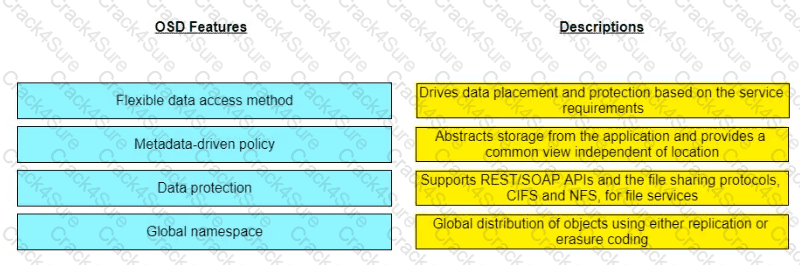
Match the object-based storage device (OSD) features with their descriptions.
An organization is planning to adopt pre integrated systems to deploy compute, network, storage, and management functions as a single engineered solution.
Which approach should the organization adopt?
Which Connectrix FC switch model supports NVMe in a 32Gb/s SAN fabric exclusively?
An organization is interested in a cloud service that provides middleware, development tools, and database management systems for application development and deployment.
Which cloud service model meets these requirements?
A company is using an intrusion detection and prevention system (IDPS) to scan and analyze intrusion events.
Which IDPS technique uses a database that contains known attack patterns?
Which VMware product has pre-defined workflows that helps to automate and coordinate the service delivery and operational functions in a storage infrastructure?
Refer to the Exhibit:

What type of process, when performed on data, would produce the result shown?
A user lost access to a key VM due to a hardware failure. A proxy server regularly takes PIT snapshots of the VM to protect the data.
What type of data protection method is this called'?
What is the effect of implementing link aggregation in an FC SAN environment?
What set of components are part of a block-based storage array controller?
In a NAS environment, which file system enables file sharing with Windows clients and uses the TCP/IP protocol?
An organization is planning to secure the connection between the data center and cloud while performing data backup and replication.
Which security control mechanism will help organization to achieve the desired security?
How should vulnerabilities be managed in a data center environment? (Verify the Correct answer from Associate - Information Storage and Management Study Manual from dellemc.com)
In an SDS environment, which protocol supports the resource-oriented architecture for the development of scalable and lightweight web applications while adhering to a set of constraints?
Which network performance attribute is achieved when using flow control in FOP?
Based on the exhibit, what does the "X" represent in the FCIP tunnel configuration?

Why is it important for organizations lo deploy business continuity solutions in their data center environment?
What is a benefit of differential backup over incremental backup?
What is a function of VM hardening?
What is true about storage system-based replication?
Why is it important for organizations to implement a multi-site remote replication solution?
In continuous data protection, what does the amount of journal space determine?
What is a benefit of performing local replication?
A company's assets are continuously under attack.
To deploy a security control mechanism to protect these assets, what should be considered?
What is an accurate statement about the Do-It-Yourself approach for building modern Infrastructure?
Which standard provides FCoE with a lossless Ethernet network?
A host sends one write /O to the RAID 1 array.
How many writes does it take for the array to store the data?
Which management monitoring parameter involves examining the amount of infrastructure resources used?
An organization wants to protect data from accidental deletion, application crashes, data corruption, and disaster.
Which solution should the organization adopt?
Which three parameters define information availability in a modern data center environment?
What is the functionality of the application server in a Mobile Device Management?
What is the key advantage of cloning a VM?
A backup administrator has defined a backup policy The policy requires full backups to be performed at 9 PM every Sunday and incremental backups performed at 9 PM the remaining days If files were accidentally deleted Thursday morning, how many backup copies are required to restore the files?
What is the result of increasing the number of FC switches in a full mesh topology?
What is the key advantage of RAID 6 compared to RAID 5?
A Fibre Channel switch has eight ports and all ports must be operational from 6 AM to 6 PM, Monday through Friday.
However, a failure of Port 4 occurs with the week as follows:
Monday= 11 AM to 1 PM
Wednesday= 5 PM to 10 PM
Thursday= 7 AM to 10 AM
Saturday= 11 AM to 1 PM
What is the availability of Port 4 in that week?
What is a goal of cyber recovery?