We at Crack4sure are committed to giving students who are preparing for the Exin SCNP Exam the most current and reliable questions . To help people study, we've made some of our SCNP Strategic Infrastructure Security exam materials available for free to everyone. You can take the Free SCNP Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
You are conducting a security awareness session for some of the employees in your organization. The discussion moves to the use if the web browser, which is Internet Explorer 7.0 for all employees. What are the four Zones that are available in Internet Explorer 7.0?
Your network has been hit by a virus that is infecting the MBR on many of the systems in the network.
You are working to repair the damage this virus has done. After two days of non-stop work on the problem, you get things under control. What type of virus was in your network?
You are creating the User Account section of your organizational security policy. From the following options, select the questions to use for the formation of this section?
Your organization assigns an Annual Loss Expectancy to assets during a risk analysis meeting. You have a server which if down for a day will lose the company $35,000, and has a serious root access attack against it once per month. What is the ALE for this attack against this server?
Which of the following are symmetric encryption algorithms?
Microsoft has developed several security tools to help you with the security and configuration of the systems in your network. One of these tools is the Microsoft Security Baseline Analyzer (MBSA). In the command line options of the MBSA is the HFNetChk tool. What is the function of the HFNetChk tool, available with MBSA?
The Root-Level DNS servers have come under many attacks over the years. Due to attacks, such as the DDoS attack on the Root-Level DNS servers in October of 2002, which of the following systems was implemented to increase the security of the DNS servers for the Internet?
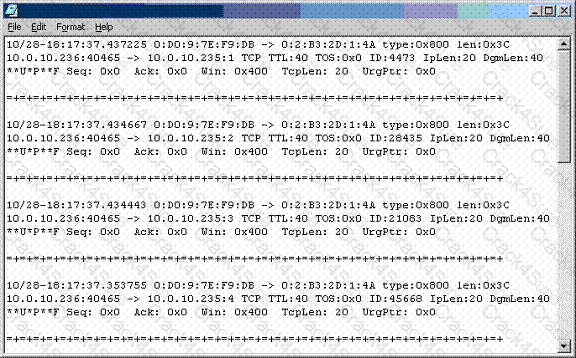
Recently, you have seen an increase in intrusion attempts and in network traffic. You decide to use Snort to run a packet capture and analyze the traffic that is present. Looking at the example, what type of traffic did Snort capture in this log file?
You work for a medium sized ISP and there have been several attacks of the DNS configuration recently.
You are particularly concerned with DNS Spoofing attacks. If an attacker is able to send out false data to a
DNS client before the response from the DNS server arrives, this is which type of DNS Spoofing?
Recently you have had meetings with an organization to design their security policy. There has been some resistance on their board concerning the need for a security policy. To help remove the resistance, you describe the many benefits to having a security policy. Which of the following are the benefits of a security policy?
What is a problem with symmetric key cryptography?
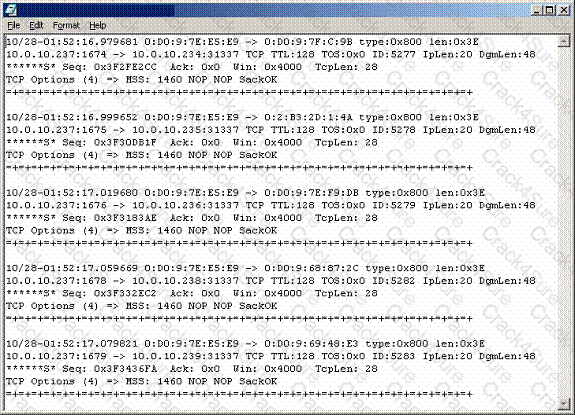
Recently, you have seen an increase in intrusion attempts and in network traffic. You decide to use
Snort to run a packet capture and analyze the traffic that is present. Looking at the example, what type of traffic did Snort capture in this log file?
You have a file on your Linux system, and you need to modify the file's permissions. The permissions you wish to apply are: Read and Write for the User; Read and Write for the Group: and Read for the Others.
What command will allow you to achieve this?
Which three of the following are examples of the reason that Message Authentication is needed?
When using the 3DES encryption ( C = EK1[DK2[EK1[P]]] ) , what is the function of P?
You are the main person responsible for the security of a mid-sized company. To have control over all the aspects of the security of the network, you study and analyze each component thoroughly. Your network is running all Windows 2003 servers, and you are studying the logon process. You know there are many components of the process, and are now at the point where you are analyzing the Security Accounts Manager (SAM). What is the SAM?
You are creating a new Auditing and Logging policy for your network. On a Windows 2003 system, if you wish to audit events like the computer restarting, which of the following options would you use?
While configuring TCP Wrappers on your Linux system, you desire to create a line that will effect the single host 10.20.23.45 accessing the telnet service. Which of the following lines will achieve this desired result?
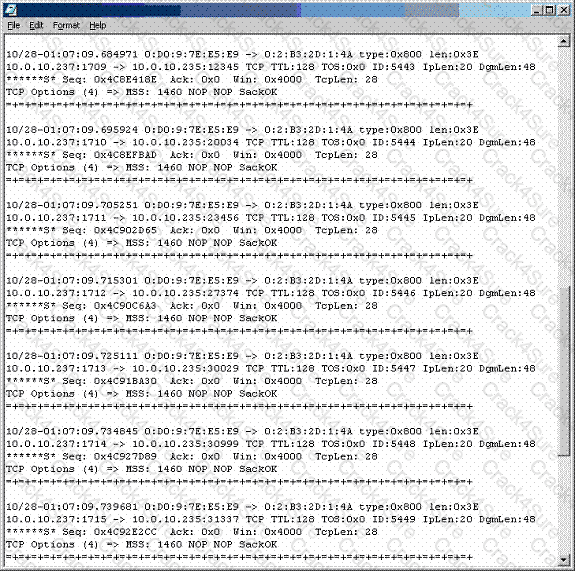
Recently, you have seen an increase in intrusion attempts and in network traffic. You decide to use
Snort to run a packet capture and analyze the traffic that is present. Looking at the example, what type of traffic did Snort capture in this log file?
You are making changes to your Windows Server 2003 file server, to increase security. You are aware from your auditing that attackers have been trying to map your network and perform reconnaissance. You wish to stop attackers from enumerating share names. What can you do to stop this?
You are setting the permissions on a new file in Linux. What will be the level of permission given to the user if you assign an Octal value of 7?
You are examining the Event IDs in your Windows 2003 network. There have been a large number of failed attempts at logon in the network. What is the Event ID for a failed attempt at Logon due to an unknown username or bad password?
The computer you are currently using is running Linux, and you are logged into the system with your normal user account. An application you wish to run requires root access to execute. Which of the following can you do to have the application execute, and not have the security of the system lowered?
When a cryptanalyst is using linguistic patterns to decrypt ciphertext, what is the analyst doing?
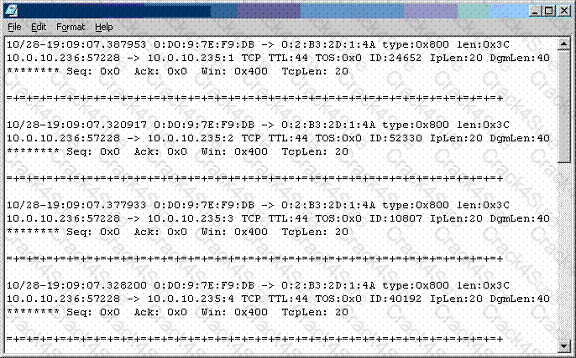
Recently, you have seen an increase in intrusion attempts and in network traffic. You decide to use
Snort to run a packet capture and analyze the traffic that is present. Looking at the example, what type of traffic did Snort capture in this log file?
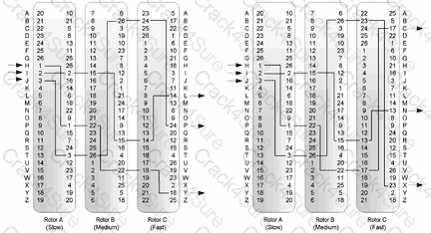
What type of cryptographic system is represented in this image?
As per the guidelines in the ISO Security Policy standard, what is the purpose of the section on Physical and Environmental Security?
When a new user account is created in Linux, what values are assigned to the user account?
Windows 2003 Server can utilize many different forms of authentication, from standard passwords to Smart Cards. What are the advantages of using NTLM Authentication over LM Authentication in Windows?