We at Crack4sure are committed to giving students who are preparing for the Exin SCNS Exam the most current and reliable questions . To help people study, we've made some of our SCNS Tactical Perimeter Defense exam materials available for free to everyone. You can take the Free SCNS Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
When installing a firewall, what is the process by which you remove un-needed services and features from a machine to reduce the risk of vulnerabilities to the underlying OS called?
Your company has recently become security conscious and wishes to protect it's electronic assets.
What is the first thing you should have in place before configuring rules for your company's firewall?
After installing Snort on your Windows machine that is destined to be your IDS, you need to edit the configuration file to customize it to your needs. What is the name of that configuration file?
After a meeting between the IT department leaders and a security consultant, they decide to implement
a new IDS in your network. You are later asked to explain to your team the type of IDS that is going to be implemented. Which of the following best describes the process of Host-Based Intrusion Detection Systems?
Your organization has extensive resources that you must make available to authorized users, through your ISA Server 2006. From the following answers, select the one that is not a feature of ISA Server Content Publishing:
You are configuring a L2TP solution between your office and your primary branch office. The CEO has requested a report on the benefits of using this technology. Which of the following benefits does L2TP (with IPSec) provide?
You have been hired at a large company to manage network security issues. Prior to your arrival, there was no one dedicated to security, so you are starting at the beginning. You hold a meeting and are discussing the main functions and features of network security. One of your assistants asks what the function of Confidentiality in network security is. Which of the following best describes Confidentiality?
You are a host in a network segment that has IP addresses in the range of 10.0.16.1~10.0.31.254. You need to create an access control list that will filter your segment of addresses. Which of the following is the wildcard mask that will be used to filter your network segment?
There are several options available to you for your new wireless networking technologies, and you are examining how different systems function. What transmission system uses short bursts combined together as a channel?
The main reason you have been hired at a company is to bring the network security of the organization up to current standards. A high priority is to have a full security audit of the network as soon as possible. You have chosen an Operational Audit and are describing it to your coworkers. Which of the following best describes an Operational audit?
You have decided to implement SSH for communicating to your router. What does SSH use to establish a secure channel of communication?
Network Monitor was run on a Windows Server 2003. The exhibit shows the actual contents of a Network
Monitor capture file.
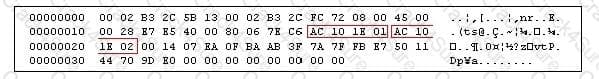
What are the IP addresses of the source and destination hosts involved in this communication? To help you determine the two hosts, they have been outlined within the captured content.
You have been chosen to manage the new security system that is to be implemented next month in your network. You are determining the type of access control to use. What are the two types of Access Control that may be implemented in a network?
Your network is going to implement a new IPSec solution. Which of the following IPSec components is used to define the security environment in which the two hosts communicate?
What is the function of the following configuration fragment?
Router#configure terminal
Router(config)#line vty 0 4
Router(config-line)#transport input ssh telnet
Router(config-line)#^Z
Router#
For the new Snort rules you are building, it will be required to have Snort examine inside the content of the packet. Which keyword is used to tell Snort to ignore a defined number of bytes before looking inside the packet for a content match?
If you configure an access-list to block the following networks, what are you trying to protect against?
Network 127.0.0.0/8, Network 0.0.0.0/0 Network 10.0.0.0/8 Network 172.16.0.0/16, and Network 168.0.0/16.
In order to add to your layered defense, you wish to implement some security configurations on your router. If you wish to have the router work on blocking TCP SYN attacks, what do you add to the end of an ACL statement?
You are considering your options for a new firewall deployment. At which three layers of the OSI model does a stateful packet filtering firewall operate?
During a network capture in Wireshark, you capture some IP traffic. In the IP Datagram, what is the function of the Protocol field?
The main reason you have been hired at a company is to bring the network security of the organization up to current standards. A high priority is to have a full security audit of the network as soon as possible. You have chosen an Independent Audit and are describing it to your coworkers. Which of the following best describes an Independent Audit?
You are monitoring the network traffic on your Frame-Relay Internet connection. You notice a large amount of unauthorized traffic on port 21. You examine the packets, and notice there are no files being transferred. Traffic on what other port must be examined to view any file contents?
You have just installed a new IDS and are creating the analysis options. Since you wish for your options to be based on time, which of the following will be able to meet your analysis needs?
You have recently been contracted to implement a new firewall solution at a client site. What are the two basic forms of firewall implementations?
You are evaluating the security of different wireless media, and are considering an infrared solution. If an attacker is trying to gain access to an infrared transmission, what will the attacker need?
You are configuring your new IDS machine, and are creating new rules. You enter the following rule:
Alert tcp any any -> 10.0.10.0/24 any (msg: "SYN-FIN scan detected"; flags: SF;)
What is the effect of this rule?
You have decided to install Snort on your Windows Server 2003 and are making changes to the default configuration file. You see the following two lines:
include classification.config
include reference.config
What should these two lines read, after you make your changes, on a default installation?
You are reconfiguring your networks firewall to create a DMZ using three network interfaces. After configuring the addresses on the interfaces, you are making the required changes in ISA Server 2006. You are going to use Network Template during this configuration change. What Network Template is designed for this firewall topology?
You are a host in a network segment that has IP addresses in the range of 168.16.1~192.168.31.254. You need to create an access control list that will filter your segment of addresses. Which of the following is the wildcard mask that will be used to filter your network segment?