View the exhibit:

The client cannot connect to the HTTP web server. The administrator ran the FortiGate built-in sniffer and got the following output:

What should be done next to troubleshoot the problem?
During the digital verification process, comparing the original and fresh hash results satisfies which security requirement?
Which of the following statements are true when using WPAD with the DHCP discovery method? (Choose two.)
View the exhibit.

Which users and user groups are allowed access to the network through captive portal?
Which of the following statements are best practices for troubleshooting FSSO? (Choose two.)
Examine the routing database shown in the exhibit, and then answer the following question:
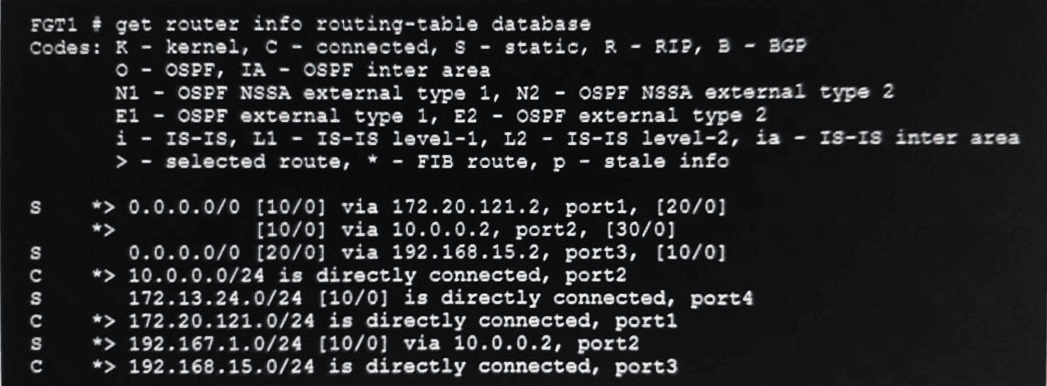
Which of the following statements are correct? (Choose two.)
When override is enabled, which of the following shows the process and selection criteria that are used to elect the primary FortiGate in an HA cluster?
An administrator has configured a dialup IPsec VPN with XAuth. Which statement best describes what occurs during this scenario?
An administrator observes that the port1 interface cannot be configured with an IP address. What can be the reasons for that? (Choose three.)
To complete the final step of a Security Fabric configuration, an administrator must authorize all the devices on
which device?
Examine the exhibit, which contains a virtual IP and firewall policy configuration.



The WAN (port1) interface has the IP address 10.200.1.1/24. The LAN (port2) interface has the IP address 10.0.1.254/24.
The first firewall policy has NAT enabled on the outgoing interface address. The second firewall policy is configured with a VIP as the destination address.
Which IP address will be used to source NAT the Internet traffic coming from a workstation with the IP address 10.0.1.10/24?
Examine this FortiGate configuration:

Examine the output of the following debug command:

Based on the diagnostic outputs above, how is the FortiGate handling the traffic for new sessions that require inspection?
View the exhibit.

A user behind the FortiGate is trying to go to http://www.addictinggames.com (Addicting Games). Based on this configuration, which statement is true?
View the exhibit.

VDOM1 is operating in transparent mode VDOM2 is operating in NAT Route mode. There is an inteface VDOM link between both VDOMs. A client workstation with the IP address 10.0.1.10/24 is connected to port2. A web server with the IP address 10.200.1.2/24 is connected to port1.
What is required in the FortiGate configuration to route and allow connections from the client workstation to the web server? (Choose two.)