Refer to the exhibits.


The exhibits show the SSL and authentication policy (Exhibit A) and the security policy (Exhibit B) tor Facebook.
Users are given access to the Facebook web application. They can play video content hosted on Facebook but they are unable to leave reactions on videos or other types of posts.
Which part of the policy configuration must you change to resolve the issue?
An administrator has configured two-factor authentication to strengthen SSL VPN access. Which additional best practice can an administrator implement?
Refer to the exhibit.
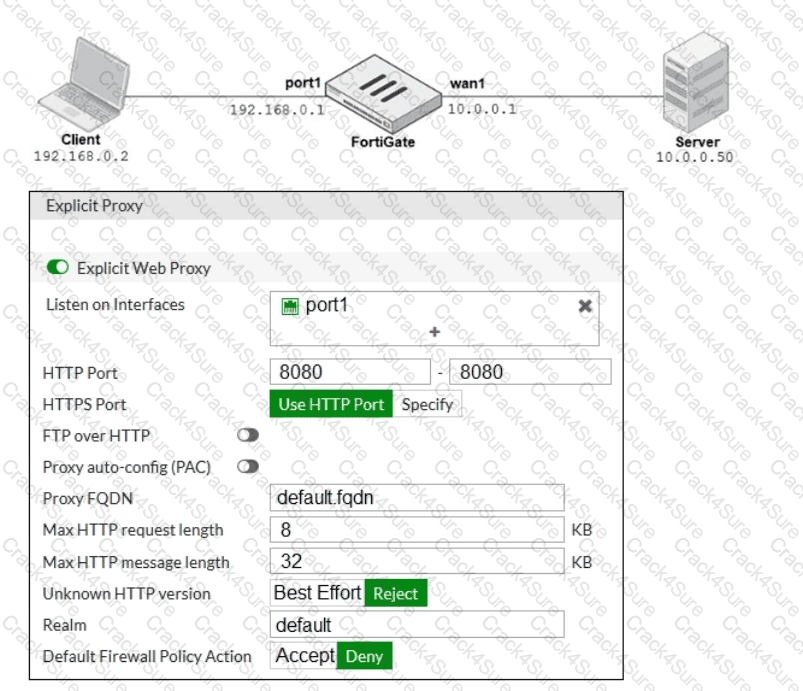
The exhibits show a network diagram and the explicit web proxy configuration.
In the command diagnose sniffer packet, what filter can you use to capture the traffic between the
client and the explicit web proxy?
Which downstream FortiGate VDOM is used to join the Security Fabric when split-task VDOM is enabled on all FortiGate devices?
An administrator has a requirement to keep an application session from timing out on port 80. What two changes can the administrator make to resolve the issue without affecting any existing services running through FortiGate? (Choose two.)
By default, FortiGate is configured to use HTTPS when performing live web filtering with FortiGuard servers.
Which two CLI commands will cause FortiGate to use an unreliable protocol to communicate with FortiGuard servers for live web filtering? (Choose two.)
If Internet Service is already selected as Source in a firewall policy, which other configuration objects can be added to the Source filed of a firewall policy?
Which three methods are used by the collector agent for AD polling? (Choose three.)
Examine this PAC file configuration.
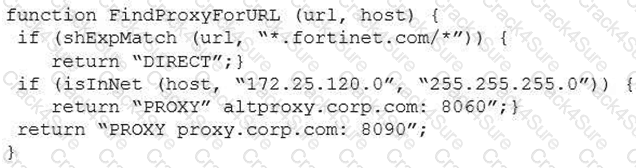
Which of the following statements are true? (Choose two.)
Which of the following are purposes of NAT traversal in IPsec? (Choose two.)
Refer to the exhibit.
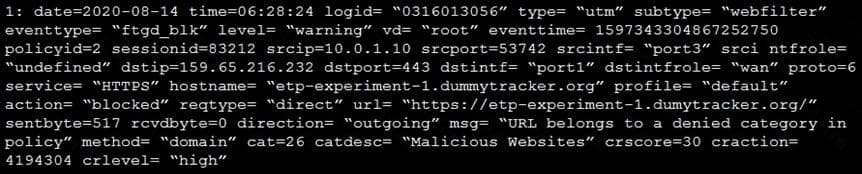
Based on the raw log, which two statements are correct? (Choose two.)
Which two inspection modes can you use to configure a firewall policy on a profile-based next-generation firewall (NGFW)? (Choose two.)
When a firewall policy is created, which attribute is added to the policy to support recording logs to a FortiAnalyzer or a FortiManager and improves functionality when a FortiGate is integrated with these devices?
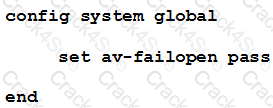
An administrator has configured the following settings:
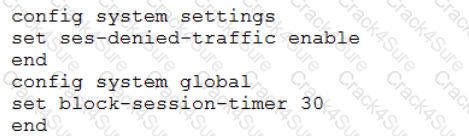
What are the two results of this configuration? (Choose two.)
An organization’s employee needs to connect to the office through a high-latency internet connection.
Which SSL VPN setting should the administrator adjust to prevent the SSL VPN negotiation failure?
Examine this FortiGate configuration:
Examine the output of the following debug command:
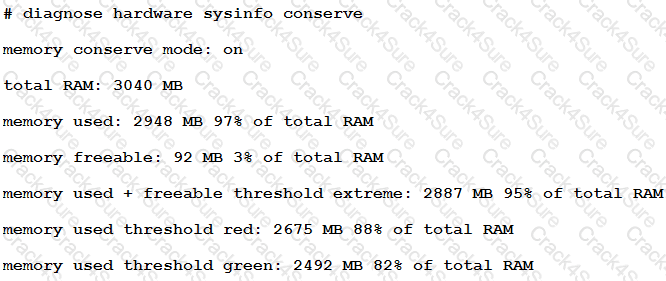
Based on the diagnostic outputs above, how is the FortiGate handling the traffic for new sessions that require inspection?
Which three pieces of information does FortiGate use to identify the hostname of the SSL server when SSL certificate inspection is enabled? (Choose three.)
Which Security rating scorecard helps identify configuration weakness and best practice violations in your network?