3 Months Free Update
3 Months Free Update
3 Months Free Update
Refer to the exhibits.
Exhibit A shows a network diagram. Exhibit B shows the firewall policy configuration and a VIP object configuration.
The WAN (port1) interface has the IP address 10.200.1.1/24.
The LAN (port3) interface has the IP address 10.0.1.254/24.
The administrator disabled the WebServer firewall policy.

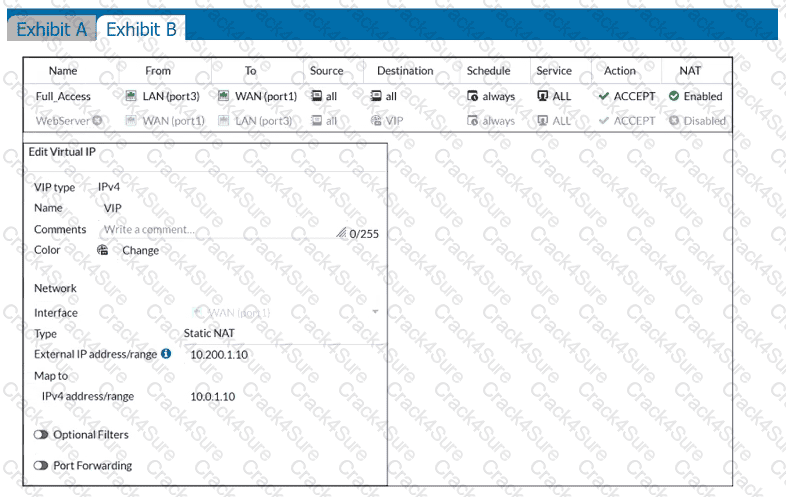
Which IP address will be used to source NAT the traffic, if a user with address 10.0.1.10 connects over SSH to the host with address 10.200.3.1?
An administrator needs to increase network bandwidth and provide redundancy.
What interface type must the administrator select to bind multiple FortiGate interfaces?
34
The HTTP inspection process in web filtering follows a specific order when multiple features are enabled in the web filter profile. What order must FortiGate use when the web filter profile has features enabled, such as safe search?
An administrator has configured the following settings:
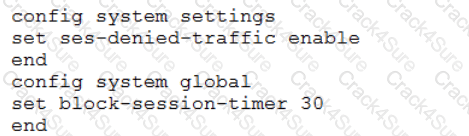
What are the two results of this configuration? (Choose two.)
73
If Internet Service is already selected as Source in a firewall policy, which other configuration objects can be added to the Source filed of a firewall policy?
By default, FortiGate is configured to use HTTPS when performing live web filtering with FortiGuard servers.
Which CLI command will cause FortiGate to use an unreliable protocol to communicate with FortiGuard servers for live web filtering?
Refer to the exhibit.
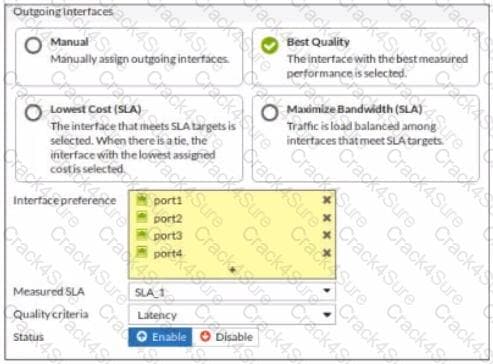
The exhibit contains the configuration for an SD-WAN Performance SLA, as well as the output of diagnose sys virtual-wan-link health-check . Which interface will be selected as an outgoing interface?
Refer to exhibit.
An administrator configured the web filtering profile shown in the exhibit to block access to all social networking sites except Twitter. However, when users try to access twitter.com, they are redirected to a FortiGuard web filtering block page.
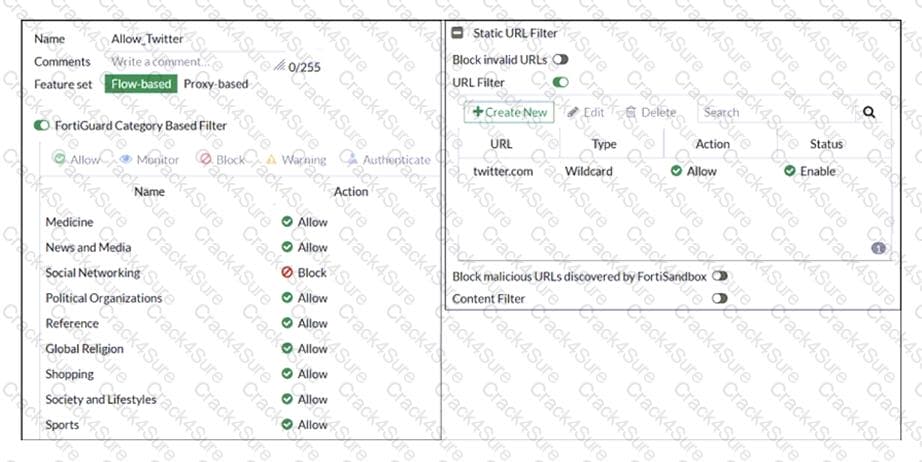
Based on the exhibit, which configuration change can the administrator make to allow Twitter while blocking all other social networking sites?
An administrator configures outgoing interface any in a firewall policy.
What is the result of the policy list view?
108
Which statement about the IP authentication header (AH) used by IPsec is true?
What is the limitation of using a URL list and application control on the same firewall policy, in NGFW policy-based mode?
An organization requires remote users to send external application data running on their PCs and access FTP resources through an SSL/TLS connection.
Which FortiGate configuration can achieve this goal?
An administrator does not want to report the logon events of service accounts to FortiGate. What setting on the collector agent is required to achieve this?
Refer to the exhibit.
The exhibit shows the output of a diagnose command.
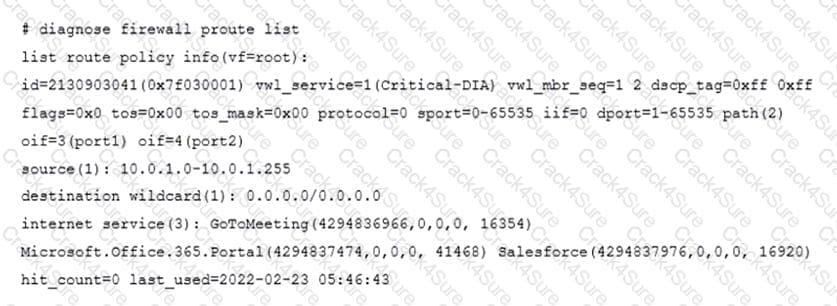
What does the output reveal about the policy route?
Which engine handles application control traffic on the next-generation firewall (NGFW) FortiGate?
6
Which three options are the remote log storage options you can configure on FortiGate? (Choose three.)
84
Which certificate value can FortiGate use to determine the relationship between the issuer and the certificate?
What are two benefits of flow-based inspection compared to proxy-based inspection? (Choose two.)
93
Which two statements are correct regarding FortiGate HA cluster virtual IP addresses? (Choose two.)
18
If the Issuer and Subject values are the same in a digital certificate, which type of entity was the certificate issued to?
Refer to the exhibit.
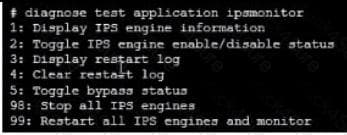
Examine the intrusion prevention system (IPS) diagnostic command.
Which statement is correct If option 5 was used with the IPS diagnostic command and the outcome was a decrease in the CPU usage?
An administrator wants to configure timeouts for users. Regardless of the userTMs behavior, the timer should start as soon as the user authenticates and expire after the configured value.
Which timeout option should be configured on FortiGate?
What is the limitation of using a URL list and application control on the same firewall policy, in NGFW policy-based mode?
40
Which CLI command will display sessions both from client to the proxy and from the proxy to the servers?
31
Which CLI command allows administrators to troubleshoot Layer 2 issues, such as an IP address conflict?
Which two statements about FortiGate FSSO agentless polling mode are true? (Choose two.)
Refer to the exhibit.
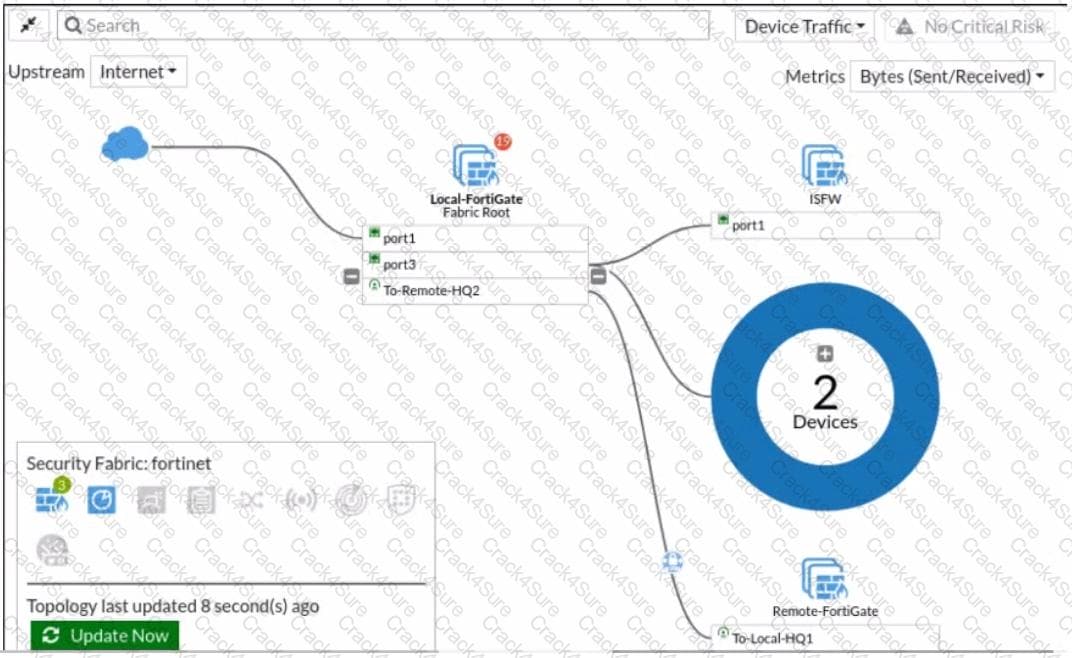
Given the security fabric topology shown in the exhibit, which two statements are true? (Choose two.)
Which statement is correct regarding the use of application control for inspecting web applications?
Which two statements are correct about NGFW Policy-based mode? (Choose two.)
Refer to the web filter raw logs.

Based on the raw logs shown in the exhibit, which statement is correct?
7
An administrator has a requirement to keep an application session from timing out on port 80. What two changes can the administrator make to resolve the issue without affecting any existing services running through FortiGate? (Choose two.)
An administrator has configured two-factor authentication to strengthen SSL VPN access. Which additional best practice can an administrator implement?
87
Which of the following are valid actions for FortiGuard category based filter in a web filter profile ui proxy-based inspection mode? (Choose two.)
68
If the Services field is configured in a Virtual IP (VIP), which statement is true when central NAT is used?
Which of the following SD-WAN load balancing method use interface weight value to distribute traffic? (Choose two.)
A network administrator is troubleshooting an IPsec tunnel between two FortiGate devices. The administrator has determined that phase 1 fails to come up. The administrator has also re-entered the pre-shared key on both FortiGate devices to make sure they match.
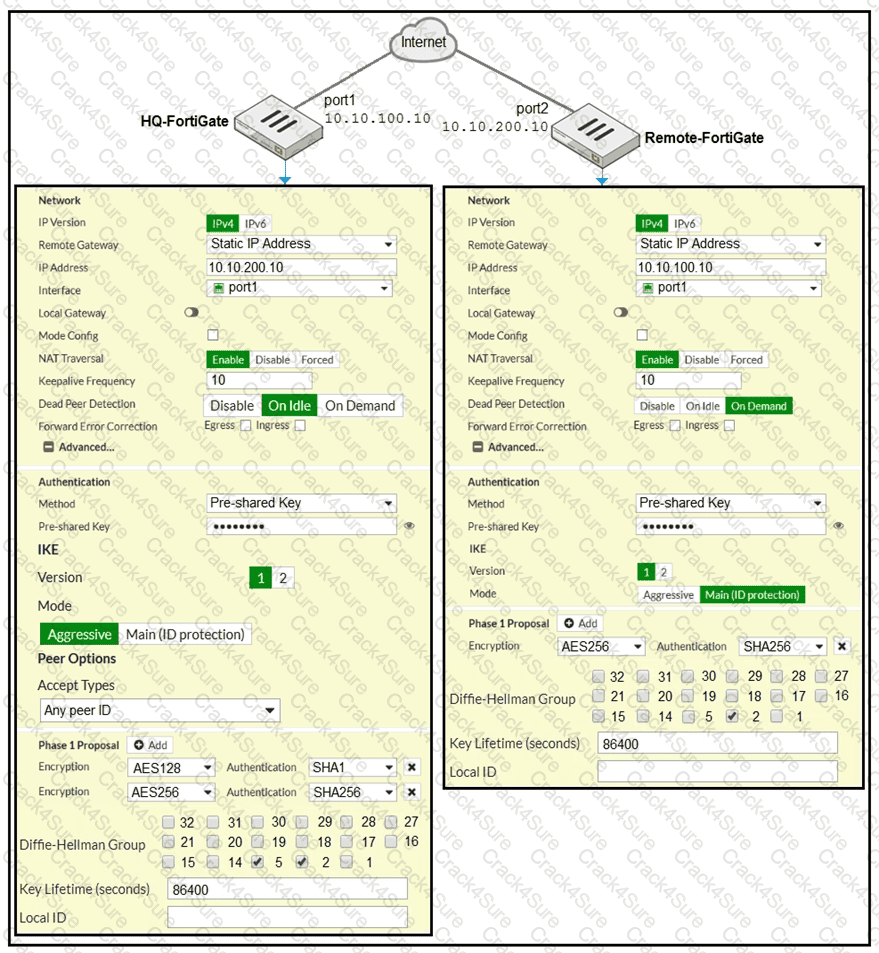
Based on the phase 1 configuration and the diagram shown in the exhibit, which two configuration changes will bring phase 1 up? (Choose two.)
Which three security features require the intrusion prevention system (IPS) engine to function? (Choose three.)
Refer to the exhibit.
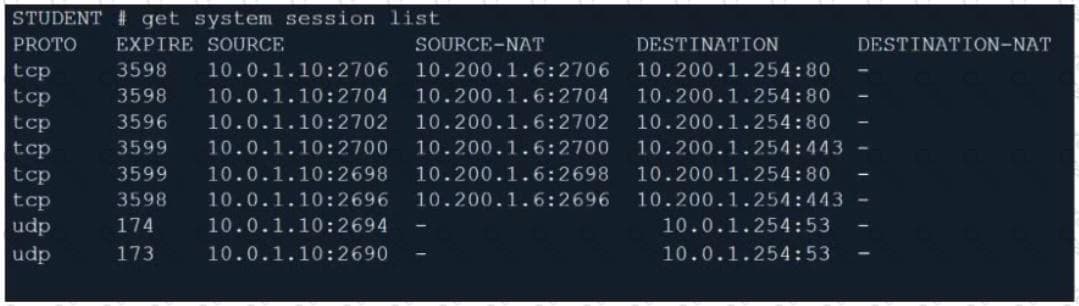
Which contains a session list output. Based on the information shown in the exhibit, which statement is true?
An administrator must disable RPF check to investigate an issue.
Which method is best suited to disable RPF without affecting features like antivirus and intrusion prevention system?
Refer to the exhibit.
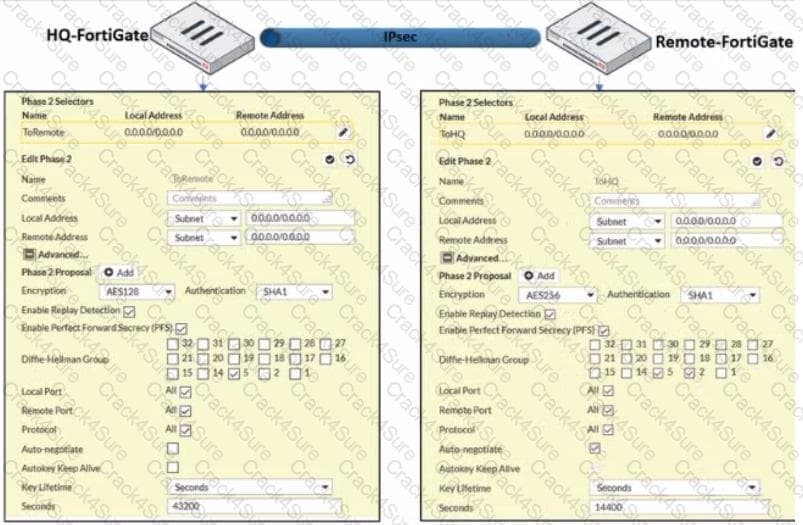
A network administrator is troubleshooting an IPsec tunnel between two FortiGate devices. The administrator has determined that phase 1 status is up. but phase 2 fails to come up.
Based on the phase 2 configuration shown in the exhibit, what configuration change will bring phase 2 up?
27
Which feature in the Security Fabric takes one or more actions based on event triggers?
Refer to the exhibits.


The exhibits show the SSL and authentication policy (Exhibit A) and the security policy (Exhibit B) for Facebook .
Users are given access to the Facebook web application. They can play video content hosted on Facebook but they are unable to leave reactions on videos or other types of posts.
Which part of the policy configuration must you change to resolve the issue?