3 Months Free Update
3 Months Free Update
3 Months Free Update
From a security perspective, how should the Root Bridge be determined in a Spanning Tree Protocol (STP) environment?
In order to determine if network traffic adheres to expected usage and complies with technical standards, an organization would use a device that provides which functionality?
To detect worms and viruses buried deep within a network packet payload, Gigabytes worth of traffic content entering and exiting a network must be checked with which of the following technologies?
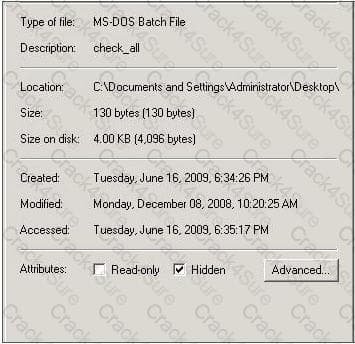
Which command tool can be used to change the read-only or hidden setting of the file in the screenshot?
A security device processes the first packet from 10.62.34.12 destined to 10.23.10.7 and recognizes a malicious anomaly. The first packet makes it to 10.23.10.7 before the security devices sends a TCP RST to 10.62.34.12. What type of security device is this?
What is needed to be able to use taskkill to end a process on remote system?
You are responding to an incident involving a Windows server on your company’s network. During the investigation you notice that the system downloaded and installed two files, iexplorer.exe and iexplorer.sys. Based on the behavior of the system you suspect that these files are part of a rootkit. If this is the case what is the likely purpose of the .sys file?
Which of the following is the best way to establish and verify the integrity of a file before copying it during an investigation?