3 Months Free Update
3 Months Free Update
3 Months Free Update
Which of the following attacks can be mitigated by providing proper training to the employees in an organization?
Adam works as a professional Computer Hacking Forensic Investigator. A project has been assigned to him to investigate computer of an unfaithful employee of SecureEnet Inc. Suspect's computer runs on Windows operating system. Which of the following sources will Adam investigate on a Windows host to collect the electronic evidences?
Each correct answer represents a complete solution. Choose all that apply.
The promiscuous mode is a configuration of a network card that makes the card pass all traffic it receives to the central processing unit rather than just packets addressed to it. Which of the following tools works by placing the host system network card into the promiscuous mode?
Which of the following statements about Access control list (ACL) is true?
Each correct answer represents a complete solution. Choose three.
Which of the following is a version of netcat with integrated transport encryption capabilities?
Which of the following responsibilities does not come under the audit process?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following tools is used to detect spam email without checking the content?
Which of the following devices are used to implement Network Address Translation (NAT)?
You work as a Network Security Administrator for NetPerfect Inc. The company has a Windowsbased network. You are incharge of the data and network security of the company. While performing a threat log analysis, you observe that one of the database administrators is pilfering confidential data. What type of threat is this?
Which of the following is used for debugging the network setup itself by determining whether all necessary routing is occurring properly, allowing the user to further isolate the source of a problem?
Which of the following tools detects certain types of packet filters and NAT setups?
When no anomaly is present in an Intrusion Detection, but an alarm is generated, the response is known as __________.
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He wants to send malicious data packets in such a manner that one packet fragment overlaps data from a previous fragment so that he can perform IDS evasion on the We-are-secure server and execute malicious data. Which of the following tools can he use to accomplish the task?
Which of the following configuration schemes in IPv6 allows a client to automatically configure its own IP address with or without IPv6 routers?
Sam works as a Security Manager for GenTech Inc. He has been assigned a project to detect reconnoitering activities. For this purpose, he has deployed a system in the network that attracts the attention of an attacker. Which of the following rulebases will he use to accomplish the task?
Which of the following programs can be used to detect stealth port scans performed by a malicious hacker?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following devices works as a transparent bridge between the wireless clients and the wired network?
Which of the following is a hardware/software platform that is designed to analyze, detect and report on security related events. NIPS is designed to inspect traffic and based on its configuration or security policy, it can drop the malicious traffic?
You work as a Network Administrator for Tech Perfect Inc. You are required to verify security policies configured in the company's networks. Which of the following applications will you use to accomplish the task?
Which of the following applications cannot proactively detect anomalies related to a computer?
As a professional hacker, you want to crack the security of secureserver.com. For this, in the information gathering step, you performed scanning with the help of nmap utility to retrieve as many different protocols as possible being used by the secureserver.com so that you could get the accurate knowledge about what services were being used by the secure server.com. Which of the following nmap switches have you used to accomplish the task?
Which of the following statements about a host-based intrusion prevention system (HIPS) are true?
Each correct answer represents a complete solution. Choose two.
Peter works as a Computer Hacking Forensic Investigator. He has been called by an organization to conduct a seminar to give necessary information related to sexual harassment within the work place. Peter started with the definition and types of sexual harassment. He then wants to convey that it is important that records of the sexual harassment incidents should be maintained, which helps in further legal prosecution. Which of the following data should be recorded in this documentation?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following attacks sends false ICMP packets in an attempt to cripple a system using random fake Internet source addresses?
You work as a Security Manger for Tech Perfect Inc. The company has a Windows-based network.
You want to scroll real-time network traffic to a command console in a readable format. Which of the following command line utilities will you use to accomplish the task?
Which of the following Intrusion Detection Systems (IDS) is used to monitor rogue access points and the use of wireless attack tools?
Which of the following is a maintenance protocol that permits routers and host computers to swap basic control information when data is sent from one computer to another?
Which of the following can be monitored by using the host intrusion detection system (HIDS)?
Each correct answer represents a complete solution. Choose two.
When client data is encapsulated into an LWAPP header, the wireless LAN controller improves the coverage areas. Which information does the wireless LAN controller check?
Each correct answer represents a part of the solution. Choose two.
Which of the following parts of IP header is used to specify the correct place of the fragment in the original un-fragmented datagram?
A scenario involves a pool of users with private IP addresses who need to access the Internet; however, the company has a limited number of IP addresses and needs to ensure users occupy only one public IP address.
Which technology is used to allow a pool of users to share one global IP address for Internet access?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based routed network. Two routers have been configured on the network. A router receives a packet. Which of the following actions will the router take to route the incoming packet?
Each correct answer represents a part of the solution. Choose two.
Which of the following tools performs comprehensive tests against web servers for multiple items, including over 6100 potentially dangerous files/CGIs?
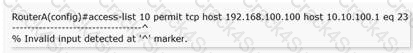
Choose the best explanation for the resulting error when entering the command below.
Which of the following are the reasons that network administrators use Access Control Lists?
Each correct answer represents a complete solution. Choose two.
You work as a Network Administrator for BlueTech Inc. You want to configure Snort as an IDS for your company's wireless network, but you are concerned that Snort does not support all types of traffic. What traffic does Snort support?
Each correct answer represents a complete solution. Choose all that apply.
Sam works as a Network Administrator for Gentech Inc. He has been assigned a project to develop the rules that define the IDP policy in the rulebase. Which of the following will he define as the components of the IDP policy rule?
Each correct answer represents a complete solution. Choose all that apply.
You are implementing passive OS fingerprinting in a network. Which of the following aspects are required to be configured there?
Each correct answer represents a part of the solution. Choose all that apply.
You are configuring a public access wireless connection. Which of the following is the best way to secure this connection?
Which of the following algorithms is used as a default algorithm for ESP extension header in IPv6?
Which of the following commands configures a router to encrypt all passwords entered after the command has been executed, as well as all passwords already on the running configuration?
You work as a technician for Net Perfect Inc. You are troubleshooting a connectivity issue on a network. You are using the ping command to verify the connectivity between two hosts. You want ping to send larger sized packets than the usual 32-byte ones. Which of the following commands will you use?
Which of the following statements about the traceroute utility are true?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following types of Intrusion Detection Systems consists of an agent on a host that identifies intrusions by analyzing system calls, application logs, file-system modifications (binaries, password files, capability/acl databases) and other host activities and state?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network.
A firewall has been configured on the network. You configure a filter on the router. You verify that SMTP operations have stopped after the recent configuration. Which of the following ports will you have to open on the router to resolve the issue?
John works as the Security Manager for PassGuide Inc. He wants to create the Profiler database that stores information about the network activity at Layer 3, Layer 4, and Layer 7. Which of the following will he use to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
You have to ensure that your Cisco Router is only accessible via telnet and ssh from the following hosts and subnets:
10.10.2.103
10.10.0.0/24
Which of the following sets of commands will you use to accomplish the task?
John works as a Security Manager for Gentech Inc. He uses an IDP engine to detect the type of interactive traffic produced during an attack in which the attacker wants to install the mechanism on a host system that facilitates the unauthorized access and breaks the system confidentiality.
Which of the following rulebases will he use to accomplish the task?