3 Months Free Update
3 Months Free Update
3 Months Free Update
Maria works as the Chief Security Officer for passguide Inc. She wants to send secret messages to the CEO of the company. To secure these messages, she uses a technique of hiding a secret message within an ordinary message. The technique provides 'security through obscurity'. What technique is Maria using?
You work as a Network Administrator of a TCP/IP network. You are having DNS resolution problem. Which of the following utilities will you use to diagnose the problem?
You work as a Network Administrator for Net Perfect Inc. The company has a Windows Server2008 network environment. The network is configured as a Windows Active Directory-based single forest single domain network. The network is configured on IP version 6 protocol. All the computers on the network are connected to a switch device. One day, users complain that they are unable to connect to a file server. You try to ping the client computers from the server, but the pinging fails. You try to ping the server's own loopback address, but it fails to ping. You restart the server, but the problem persists.
What is the most likely cause?
By gaining full control of router, hackers often acquire full control of the network. Which of the following methods are commonly used to attack Routers?
Each correct answer represents a complete solution. Choose all that apply.
You work as a technician for Tech Perfect Inc. You are troubleshooting an Internet name resolution issue. You ping your ISP's DNS server address and find that the server is down. You want to continuously ping the DNS address until you have stopped the command. Which of the following commands will you use?
Which of the following commands will you use with the tcpdump command to capture the traffic from a filter stored in a file?
Victor wants to send an encrypted message to his friend. He is using certain steganography technique to accomplish this task. He takes a cover object and changes it accordingly to hide information. This secret information is recovered only when the algorithm compares the changed cover with the original cover. Which of the following Steganography methods is Victor using to accomplish the task?
Which of the following algorithms produces a digital signature which is used to authenticate the bit-stream images?
Which of the following tools performs comprehensive tests against web servers for multiple items, including over 6100 potentially dangerous files/CGIs?
Which of the following Web attacks is performed by manipulating codes of programming languages such as SQL, Perl, Java present in the Web pages?
Which of the following DNS resource records is used to resolve a host name to an IPv6 address?
Which of the following is the default port for Simple Network Management Protocol (SNMP)?
In which of the following attacks does a hacker imitate a DNS server and obtain the entire DNS database?
Which of the following are the two sub-layers present in Data Link layer of the OSI Reference model?
Mark works as a Network administrator for SecureEnet Inc. His system runs on Mac OS X. He wants to boot his system from the Network Interface Controller (NIC). Which of the following snag keys will Mark use to perform the required function?
Adam works as a Computer Hacking Forensic Investigator in a law firm. He has been assigned with his first project. Adam collected all required evidences and clues. He is now required to write an investigative report to present before court for further prosecution of the case. He needs guidelines to write an investigative report for expressing an opinion. Which of the following are the guidelines to write an investigative report in an efficient way?
Each correct answer represents a complete solution. Choose all that apply.
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. John wants to redirect all TCP port 80 traffic to UDP port 40, so that he can bypass the firewall of the We-are-secure server. Which of the following tools will John use to accomplish his task?
Which of the following can be applied as countermeasures against DDoS attacks?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following command-line utilities is used to show the state of current TCP/IP connections?
In which of the following IKE phases the IPsec endpoints establish parameters for a secure ISAKMP session?
Which of the following standard file formats is used by Apple's iPod to store contact information?
Which of the following tools allows an attacker to intentionally craft the packets to gain unauthorized access?
Each correct answer represents a complete solution. Choose two.
You are the Administrator for a Windows 2000 based network that uses DHCP to dynamically assign IP addresses to the clients and DNS servers. You want to ensure that the DNS servers can communicate with another DNS server. Which type of query will you run to achieve this?
Which of the following statements are true about an IPv6 network?
Each correct answer represents a complete solution. Choose all that apply.
Peter works as a Computer Hacking Forensic Investigator. He has been called by an organization to conduct a seminar to give necessary information related to sexual harassment within the work place. Peter started with the definition and types of sexual harassment. He then wants to convey that it is important that records of the sexual harassment incidents should be maintained, which helps in further legal prosecution. Which of the following data should be recorded in this documentation?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Network Administrator for Tech2tech Inc. You have configured a network-based IDS for your company.
You have physically installed sensors at all key positions throughout the network such that they all report to the command console.
What will be the key functions of the sensors in such a physical layout?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network. A firewall has been configured on the network. You configure a filter on the router. You verify that SMTP operations have stopped after the recent configuration. Which of the following ports will you have to open on the router to resolve the issue?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He has written the following snort signature:
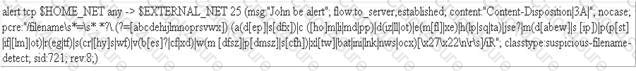
Which of the following statements about this snort signature is true?
You work as a Desktop Support Technician for umbrella Inc. The company uses a Windows-based network. An employee of the production department is facing the problem in the IP configuration of the network connection.
He called you to resolve the issue. You suspect that the IP configuration is not configured properly. You want to use the ping command to ensure that IPv4 protocol is working on a computer. While running the ping command from the command prompt, you find that Windows Firewall is blocking the ping command. You enter the following command in the elevated command prompt on the computer:
netsh advfirewall firewall add rule name="ICMPv4" protocol=icmpv4:any,any dir=in action=allow
Which of the following actions will this command perform?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based routed network. You have recently come to know about the Slammer worm, which attacked computers in 2003 and doubled the number of infected hosts every 9 seconds or so. Slammer infected 75000 hosts in the first 10 minutes of the attack. To mitigate such security threats, you want to configure security tools on the network. Which of the following tools will you use?
Which of the following techniques is used to identify attacks originating from a botnet?
Which of the following work as traffic monitoring tools in the Linux operating system?
Each correct answer represents a complete solution. Choose all that apply.
Mark has been assigned a project to configure a wireless network for a company. The network should contain a Windows 2003 server and 30 Windows XP client computers. Mark has a single dedicated Internet connection that has to be shared among all the client computers and the server. The configuration needs to be done in a manner that the server should act as a proxy server for the client computers. Which of the following programs can Mark use to fulfill this requirement?
Which of the following is the default port for Simple Network Management Protocol (SNMP)?
You are concerned about outside attackers penetrating your network via your company Web server. You wish to place your Web server between two firewalls. One firewall between the Web server and the outside world. The other between the Web server and your network. What is this called?
Which of the following types of Intrusion detection systems (IDS) is used for port mirroring?
Which of the following partitions contains the system files that are used to start the operating system?
Which of the following wireless network standards operates on the 5 GHz band and transfers data at a rate of 54 Mbps?
Which of the following is NOT the functional area of a forensic laboratory?
Which of the following firewalls depends on the three-way handshake of the TCP protocol?
You work as a Network Administrator for McNeil Inc. The company has a TCP/IP-based network.
You are configuring an Internet connection for your company. Your Internet service provider (ISP) has a UNIX-based server. Which of the following utilities will enable you to access the UNIX server, using a text-based connection?
In which of the following IDS evasion attacks does an attacker send a data packet such that IDS accepts the data packet but the host computer rejects it?
Which of the following statements is NOT true about FAT16 file system?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following are the types of intrusion detection systems?
Each correct answer represents a complete solution. Choose all that apply.
John works as a Security Administrator for NetPerfect Inc. The company uses Windows-based systems. A project has been assigned to John to track malicious hackers and to strengthen the company's security system. John configures a computer system to trick malicious hackers into thinking that it is the company's main server, which in fact is a decoy system to track hackers.
Which system is John using to track the malicious hackers?
Which of the following is an expression of interference that triggers a false positive signal during an intrusion detection process performed by IDS?
Which of the following methods is used by forensic investigators to acquire an image over the network in a secure manner?
Which of the following switches is used with Pslist command on the command line to show the statistics for all active threads on the system, grouping these threads with their owning process?
Andrew, a bachelor student of Faulkner University, creates a gmail account. He uses 'Faulkner' as the password for the gmail account. After a few days, he starts receiving a lot of e-mails stating that his gmail account has been hacked. He also finds that some of his important mails have been deleted by someone. Which of the following methods has the attacker used to crack Andrew's password?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Network Administrator for Net Perfect Inc. The company has a TCP/IP-based network. The network is connected to the Internet through a firewall. A user complains that he is unable to access the abc.com site. However, he can access all other sites. Which of the following tools will help you diagnose the problem?
What netsh command should be run to enable IPv6 routing?
Each correct answer represents a part of the solution. Choose two.
Which of the following password cracking attacks is based on a pre-calculated hash table to retrieve plain text passwords?
Which of the following is computed from an arbitrary block of digital data for the purpose of detecting accidental errors?
Which of the following is the best method of accurately identifying the services running on a victim host?
You work as a Desktop Support Technician for umbrella Inc. The company uses a Windows-based network. An employee from the sales department is facing problem in the IP configuration of the network connection. He called you to resolve the issue. You suspect that the IP configuration is not configured properly. You want to use the ping command to ensure that IPv4 protocol is working on a computer. While running the ping command from the command prompt, you find that Windows Firewall is blocking the ping command. What is the cause of the issue?
Which of the following IP packet elements is responsible for authentication while using IPSec?
Which of the following processes is used to convert plain text into cipher text?
You work as a Network Administrator for McRobert Inc. You want to know the NetBIOS name of your computer. Which of the following commands will you use?
Ryan, a malicious hacker submits Cross-Site Scripting (XSS) exploit code to the Website of Internet forum for online discussion. When a user visits the infected Web page, code gets automatically executed and Ryan can easily perform acts like account hijacking, history theft etc. Which of the following types of Cross-Site Scripting attack Ryan intends to do?
Which of the following ICMPv6 neighbor discovery messages is sent by hosts to request an immediate router advertisement, instead of waiting for the next scheduled advertisement?