3 Months Free Update
3 Months Free Update
3 Months Free Update
During a penetration test you discover a valid set of SSH credentials to a remote system. How can this be used to your advantage in a Nessus scan?
You've been contracted by the owner of a secure facility to try and break into their office in the middle of the night. Your client requested photographs of any sensitive information found as proof of your accomplishments. The job you've been hired to perform is an example of what practice?
Which of the following TCP packet sequences are common during a SYN (or half-open) scan?
You have been contracted to perform a black box pen test against the Internet facing servers for a company. They want to know, with a high level of confidence, if their servers are vulnerable to external attacks. Your contract states that you can use all tools available to you to pen test the systems. What course of action would you use to generate a report with the lowest false positive rate?
By default Active Directory Controllers store password representations in which file?
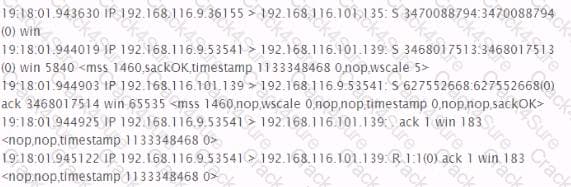
Analyze the excerpt from a packet capture between the hosts 192.168.116.9 and 192.168.116.101. What factual conclusion can the tester draw from this output?
The resulting business impact, of the penetration test or ethical hacking engagement is explained in what section of the final report?
Which of the following is a method of gathering user names from a Linux system?
What is the MOST important document to obtain before beginning any penetration testing?
Which of the following are the countermeasures against WEP cracking?
Each correct answer represents a part of the solution. Choose all that apply.
Which of the following techniques are NOT used to perform active OS fingerprinting?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following wireless security standards supported by Windows Vista provides the highest level of security?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He performs a Teardrop attack on the we-are-secure server and observes that the server crashes. Which of the following is the most likely cause of the server crash?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He has successfully performed the following steps of the preattack phase to check the security of the We-are-secure network:
Gathering information
Determining the network range
Identifying active systems
Now, he wants to find the open ports and applications running on the network. Which of the following tools will he use to accomplish his task?
In which of the following attacks is a malicious packet rejected by an IDS, but accepted by the host system?
Which of the following techniques are NOT used to perform active OS fingerprinting?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is the most common method for an attacker to spoof email?
Which of the following layers of TCP/IP model is used to move packets between the Internet Layer interfaces of two different hosts on the same link?
In which of the following attacks is a malicious packet rejected by an IDS, but accepted by the host system?
Which of the following tools is used for vulnerability scanning and calls Hydra to launch a dictionary attack?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network. Rick, your assistant, is configuring some laptops for wireless access. For security, WEP needs to be configured for wireless communication. By mistake, Rick configures different WEP keys in a laptop than that is configured on the Wireless Access Point (WAP). Which of the following statements is true in such situation?
Write the appropriate attack name to fill in the blank.
In a _____________ DoS attack, the attacker sends a spoofed TCP SYN packet in which the IP address of the target is filled in both the source and destination fields.
Which of the following tools is spyware that makes Windows clients send their passwords as clear text?
Which of the following tools is used to verify the network structure packets and confirm that the packets are constructed according to specification?
You run the following PHP script:
$password = mysql_real_escape_string($_POST["password"]);?>
What is the use of the mysql_real_escape_string() function in the above script.
Each correct answer represents a complete solution. Choose all that apply
Which of the following tools can be used to perform Windows password cracking, Windows enumeration, and VoIP session sniffing?
The scope of your engagement is to include a target organization located in California with a /24 block of addresses that they claim to completely own. Which site could you utilize to confirm that you have been given accurate information before starting reconnaissance activities?
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. He performs Web vulnerability scanning on the We-are-secure server.
The output of the scanning test is as follows:
C:\whisker.pl -h target_IP_address
-- whisker / v1.4.0 / rain forest puppy / www.wiretrip.net -- = - = - = - = - =
= Host: target_IP_address
= Server: Apache/1.3.12 (Win32) ApacheJServ/1.1
mod_ssl/2.6.4 OpenSSL/0.9.5a mod_perl/1.22
+ 200 OK: HEAD /cgi-bin/printenv
John recognizes /cgi-bin/printenv vulnerability ('Printenv' vulnerability) in the We_are_secure server. Which of the following statements about 'Printenv' vulnerability are true?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following tasks can be performed by using netcat utility?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following attacks allows an attacker to sniff data frames on a local area network (LAN) or stop the traffic altogether?
Anonymizers are the services that help make a user's own Web surfing anonymous. An anonymizer removes all the identifying information from a user's computer while the user surfs the Internet. It ensures the privacy of the user in this manner. After the user anonymizes a Web access with an anonymizer prefix, every subsequent link selected is also automatically accessed anonymously. Which of the following are limitations of anonymizers?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Penetration Tester for the Infosec Inc. Your company takes the projects of security auditing. Recently, your company has assigned you a project to test the security of the we-aresecure. com Web site. For this, you want to perform the idle scan so that you can get the ports open in the we-are-secure.com server. You are using Hping tool to perform the idle scan by using a zombie computer. While scanning, you notice that every IPID is being incremented on every query, regardless whether the ports are open or close. Sometimes, IPID is being incremented by more than one value. What may be the reason?
Which of the following vulnerability scanner scans from CGI, IDA, Unicode, and Nimda vulnerabilities?
You work as a Web developer in the IBM Inc. Your area of proficiency is PHP. Since you have proper knowledge of security, you have bewared from rainbow attack. For mitigating this attack, you design the PHP code based on the following algorithm:
key = hash(password + salt)
for 1 to 65000 do
key = hash(key + salt)
Which of the following techniques are you implementing in the above algorithm?
You work as a Penetration Tester for the Infosec Inc. Your company takes the projects of security auditing. Recently, your company has assigned you a project to test the security of the we-aresecure. com Website. The we-are-secure.com Web server is using Linux operating system. When you port scanned the we-are-secure.com Web server, you got that TCP port 23, 25, and 53 are open. When you tried to telnet to port 23, you got a blank screen in response. When you tried to type the dir, copy, date, del, etc. commands you got only blank spaces or underscores symbols on the screen. What may be the reason of such unwanted situation?
TCP/IP stack fingerprinting is the passive collection of configuration attributes from a remote device during standard layer 4 network communications. The combination of parameters may then be used to infer the remote operating system (OS fingerprinting), or incorporated into a device fingerprint. Which of the following Nmap switches can be used to perform TCP/IP stack fingerprinting?
You work as an IT Technician for uCertify Inc. You have to take security measures for the wireless network of the company. You want to prevent other computers from accessing the company's wireless network. On the basis of the hardware address, which of the following will you use as the best possible method to accomplish the task?
Which of the following characters will you use to check whether an application is vulnerable to an SQL injection attack?
Which of the following statements are true about session hijacking?
Each correct answer represents a complete solution. Choose all that apply.
LM hash is one of the password schemes that Microsoft LAN Manager and Microsoft Windows versions prior to the Windows Vista use to store user passwords that are less than 15 characters long. If you provide a password seven characters or less, the second half of the LM hash is always
__________.
You have changed the RestrictAnonymous registry setting from 0 to 1 on your servers to secure your Windows 2000 system so that any malicious user cannot establish a null session on the server. However, when you test the security using userinfo tool, you got that you can still establish the null session. What may be its reason?
Which of the following is generally practiced by the police or any other recognized governmental authority?
You have received a file named new.com in your email as an attachment. When you execute this file in your laptop, you get the following message:
'EICAR-STANDARD-ANTIVIRUS-TEST-FILE!'
When you open the file in Notepad, you get the following string:
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
What step will you take as a countermeasure against this attack?
John, a novice web user, makes a new E-mail account and keeps his password as "apple", his favorite fruit. John's password is vulnerable to which of the following password cracking attacks?
Each correct answer represents a complete solution. Choose all that apply.
Adam is a novice Internet user. He is using Google search engine to search documents of his interest. Adam wants to search the text present in the link of a Website. Which of the following operators will he use in his query to accomplish the task?