3 Months Free Update
3 Months Free Update
3 Months Free Update
Which of the following is a console-based 802.11 layer2 wireless network detector, sniffer, and intrusion detection system?
Which of the following IDs is used to reassemble the fragments of a datagram at the destination point?
Which of the following techniques is used to identify attacks originating from a botnet?
You are the Network Administrator and your company has recently implemented encryption for all emails. You want to check to make sure that the email packages are being encrypted.
What tool would you use to accomplish this?
Which of the following is the function of the editcap utility of Wireshark?
Which of the following tools is used to analyze the files produced by several popular packetcapture programs such as tcpdump, WinDump, Wireshark, and EtherPeek?
Which of the following would allow you to automatically close connections or restart a server or service when a DoS attack is detected?
Which of the following devices are used to implement Network Address Translation (NAT)?
You work as a Forensic Investigator.
Which of the following rules will you follow while working on a case?
Each correct answer represents a part of the solution. (Choose all that apply.)
Which of the following firewalls filters the traffic based on the header of the datagram?
You run the tcpdump command line utility and get a report produced by tcpdump.
What information does this report include?
Each correct answer represents a complete solution. (Choose three.)
Mark has been assigned a project to configure a wireless network for a company. The network should contain a Windows 2003 server and 30 Windows XP client computers. Mark has a single dedicated Internet connection that has to be shared among all the client computers and the server. The configuration needs to be done in a manner that the server should act as a proxy server for the client computers.
Which of the following programs can Mark use to fulfill this requirement?
As a professional hacker, you want to crack the security of secureserver.com. For this, in the information gathering step, you performed scanning with the help of nmap utility to retrieve as many different protocols as possible being used by the secureserver.com so that you could get the accurate knowledge about what services were being used by the secure server.com.
Which of the following nmap switches have you used to accomplish the task?
You work as the Security Administrator for Prodotxiss Inc. You want to ensure the security of your Wi-Fi enterprise network against the wireless snooping attacks.
Which of the following measures will you take over the site network devices of the network?
Which of the following TShark options is used to set capture buffer size in MB?
You work as a Network Administrator for Rick International. The company has a TCP/IP-based network. A user named Kevin wants to set an SSH terminal at home to connect to the company's network. You have to configure your company's router for it.
By default, which of the following standard ports does the SSH protocol use for connection?
Which of the following are packet filtering tools for the Linux operating system?
Each correct answer represents a complete solution. (Choose all that apply.)
An attacker makes an attempt against a Web server. The result is that the attack takes the form of URLs. These URLs search for a certain string that identifies an attack against the Web server.
Which IDS/IPS detection method do the URLs use to detect and prevent an attack?
Which of the following technologies is used to detect unauthorized attempts to access and manipulate computer systems locally or through the Internet or an intranet?
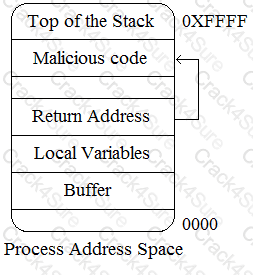
An attacker changes the address of a sub-routine in such a manner that it begins to point to the address of the malicious code. As a result, when the function has been exited, the application can be forced to shift to the malicious code. The image given below explains this phenomenon:
Which of the following tools can be used as a countermeasure to such an attack?
Which of the following algorithms is used as a default algorithm for ESP extension header in IPv6?
Which of the following components are used in the implementation of a wireless intrusion prevention system?
Each correct answer represents a part of the solution. (Choose three.)
You work as a Network Administrator for Tech Perfect Inc. You are required to verify security policies configured in the company's networks.
Which of the following applications will you use to accomplish the task?
You are implementing passive OS fingerprinting in a network.
Which of the following aspects are required to be configured there?
Each correct answer represents a part of the solution. (Choose all that apply.)
You work as a Network Administrator for ABC Inc. The company has a TCP/IP-based routed network. Two routers have been configured on the network. A router receives a packet.
Which of the following actions will the router take to route the incoming packet?
Each correct answer represents a part of the solution. (Choose two.)
Audit trail or audit log is a chronological sequence of audit records, each of which contains evidence directly pertaining to and resulting from the execution of a business process or system function.
Under which of the following controls does audit control come?
An organization has more than a couple of external business, and exchanges dynamic routing information with the external business partners. The organization wants to terminate all routing from a partner at an edge router, preferably receiving only summary routes from the partner.
Which of the following will be used to change all partner addresses on traffic into a range of locally assigned addresses?
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. John wants to redirect all TCP port 80 traffic to UDP port 40, so that he can bypass the firewall of the We-are-secure server.
Which of the following tools will John use to accomplish his task?
You work as a Network Administrator for Net Perfect Inc. The company has a TCP/IP network. You have been assigned a task to configure security mechanisms for the network of the company. You have decided to configure a packet filtering firewall.
Which of the following may be the reasons that made you choose a packet filtering firewall as a security mechanism?
Each correct answer represents a complete solution. (Choose all that apply.)
You are implementing a host based intrusion detection system on your web server. You feel that the best way to monitor the web server is to find your baseline of activity (connections, traffic, etc.) and to monitor for conditions above that baseline.
This type of IDS is called __________.
Jain works as a professional Ethical Hacker. He has been assigned the project of testing the security of testing the security of www.abc.com. Jain notices that the ABC network is vulnerable to a man-in-the-middle attack since the key exchange process of the cryptographic algorithm it is using does not authenticate participants.
Which of the following cryptographic algorithms is being used by the ABC server?
Fill in the blank with the appropriate tool name.
______________ is a network protocol analyzer tool that is used to capture packet data from an existing network or examine packet data from a pre-saved file.
Which of the following Wireless LAN standard devices is least affected by interference from domestic appliances such as microwave ovens?
This is a Windows-based tool that is used for the detection of wireless LANs using the IEEE 802.11a, 802.11b, and 802.11g standards. The main features of these tools are as follows:
• It displays the signal strength of a wireless network, MAC address, SSID, channel details, etc.
• It is commonly used for the following purposes:
a) War driving
b) Detecting unauthorized access points
c) Detecting causes of interference on a WLAN
d) WEP ICV error tracking
e) Making Graphs and Alarms on 802.11 Data, including Signal Strength
This tool is known as __________.