3 Months Free Update
3 Months Free Update
3 Months Free Update
Which of the following is generally practiced by the police or any other recognized governmental authority?
What Windows log should be checked to troubleshoot a Windows service that is falling to start?
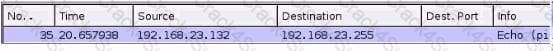
You are examining a packet capture session in Wire shark and see the packet shown in the accompanying image. Based on what you see, what is the appropriate protection against this type of attempted attack?
What does Authentication Header (AH) add to the packet in order to prevent an attacker from lying about the source?
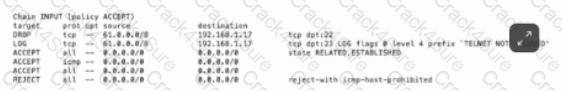
Based on the iptables output below, which type of endpoint security protection has host 192.168.1.17 implemented for incoming traffic on TCP port 22 (SSH) and TCP port 23 (telnet)?
Which class of IDS events occur when the IDS fails to alert on malicious data?
Which of the following SIP methods is used to setup a new session and add a caller?
Which of the following choices accurately describes how PGP works when encrypting email?
Which of the following utilities provides an efficient way to give specific users permission to use specific system commands at the root level of a Linux operating system?
Which of the following hardware devices prevents broadcasts from crossing over subnets?
Which of the following proxy servers provides administrative controls over the content?
What is the unnoticed theft of sensitive data from a laptop owned by an organization's CEO an example of in information warfare?
You work as a Network Administrator for NetTech Inc. The company wants to encrypt its e-mails. Which of the following will you use to accomplish this?
Which of the following are used to suppress gasoline and oil fires? Each correct answer represents a complete solution. Choose three.
The previous system administrator at your company used to rely heavily on email lists, such as vendor lists and Bug Traq to get information about updates and patches. While a useful means of acquiring data, this requires time and effort to read through. In an effort to speed things up, you decide to switch to completely automated updates and patching. You set up your systems to automatically patch your production servers using a cron job and a scripted apt-get upgrade command. Of the following reasons, which explains why you may want to avoid this plan?
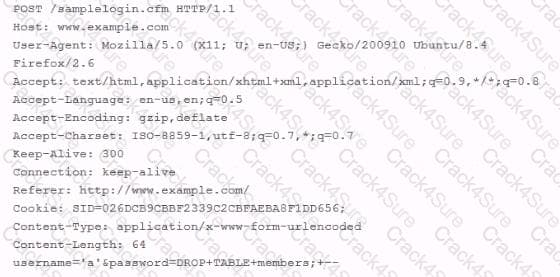
While using Wire shark to investigate complaints of users being unable to login to a web application, you come across an HTTP POST submitted through your web application. The contents of the POST are listed below. Based on what you see below, which of the following would you recommend to prevent future damage to your database?
Which of the following commands is used to change file access permissions in Linux?
Two clients connecting from the same public IP address (for example - behind the same NAT firewall) can connect simultaneously to the same web server on the Internet, provided what condition is TRUE?
If Linux server software is a requirement in your production environment which of the following should you NOT utilize?
What would the following IP tables command do?
IP tables -I INPUT -s 99.23.45.1/32 -j DROP
A US case involving malicious code is brought to trial. An employee had opened a helpdesk ticket to report specific instances of strange behavior on her system. The IT helpdesk representative collected information by interviewing the user and escalated the ticket to the system administrators. As the user had regulated and sensitive data on her computer, the system administrators had the hard drive sent to the company's forensic consultant for analysis and configured a new hard drive for the user. Based on the recommendations from the forensic consultant and the company's legal department, the CEO decided to prosecute the author of the malicious code. During the court case, which of the following would be able to provide direct evidence?
A system administrator sees the following URL in the webserver logs:
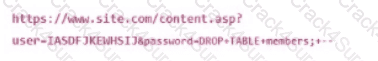
Which action will mitigate against this attack?
Which of the following is required to be backed up on a domain controller to recover Active Directory?
What is the name of the Windows XP/2003 tool that you can use to schedule commands to be executed on remote systems during off-peak hours?
Which of the following processes Is used to prove a user Is who they claim to be based upon something they know, have, are, and/or their physical location?
Mark works as a Network Administrator for NetTech Inc. The company has a Windows 2003 domain- based network. The network contains ten Windows 2003 member servers, 150 Windows XP Professional client computers. According to the company's security policy, Mark needs to check whether all the computers in the network have all available security updates and shared folders. He also needs to check the file system type on each computer's hard disk. Mark installs and runs MBSACLI.EXE with the appropriate switches on a server. Which of the following tasks will he accomplish?
IPS devices that are classified as "In-line NIDS" devices use a combination of anomaly analysis, signature-based rules, and what else to identify malicious events on the network?
A Host-based Intrusion Prevention System (HIPS) software vendor records how the Firefox Web browser interacts with the operating system and other applications, and identifies all areas of Firefox functionality. After collecting all the data about how Firefox should work, a database is created with this information, and it is fed into the HIPS software. The HIPS then monitors Firefox whenever it's in use. What feature of HIPS is being described in this scenario?
An application developer would like to replace Triple DES in their software with a stronger algorithm of the same type. Which of the following should they use?
Which of the following are the types of access controls?
Each correct answer represents a complete solution. Choose three.
Which of the below choices should an organization start with when implementing an effective risk management process?
Which of the following TCP dump output lines indicates the first step in the TCP 3-way handshake?
Which of the following is a new Windows Server 2008 feature for the Remote Desktop Protocol (RDP)?
Which of the following defines the communication link between a Web server and Web applications?
In an Active Directory domain, which is the preferred method of keeping host computers patched?
Which of the following groups represents the most likely source of an asset loss through the inappropriate use of computers?
You work as a Network Administrator for McNeil Inc. You are installing an application. You want to view the log file whenever a new entry is added to the /var/log/messages log file. Which of the following commands will you use to accomplish this?
Which of the following statements about Network Address Translation (NAT) are true? Each correct answer represents a complete solution. Choose two.
Which of the following SIP INVITE lines indicates to the remote registrar the VoIP phone that initiated the call?
What is the term for a game in which for every win there must be an equivalent loss?
You work as a Network Administrator for Net Perfect Inc. The company has a Linux-based network. You are configuring an application server. An application named Report, which is owned by the root user, is placed on the server. This application requires superuser permission to write to other files. All sales managers of the company will be using the application. Which of the following steps will you take in order to enable the sales managers to run and use the Report application?
A folder D:\Files\Marketing has the following NTFS permissions:
• Administrators: Full Control
• Marketing: Change and Authenticated
• Users: Read
It has been shared on the server as "MARKETING", with the following share permissions:
• Full Control share permissions for the Marketing group
Which of the following effective permissions apply if a user from the Sales group accesses the \\FILESERVER\MARKETING shared folder?
Which access control mechanism requires a high amount of maintenance since all data must be classified, and all users granted appropriate clearance?
What technical control provides the most critical layer of defense if an intruder is able to bypass all physical security controls and obtain tapes containing critical data?
What type of attack can be performed against a wireless network using the tool Kismet?
While building multiple virtual machines on a single host operating system, you have determined that each virtual machine needs to work on the network as a separate entity with its own unique IP address on the same logical subnet. You also need to limit each guest operating system to how much system resources it has access to. Which of the following correctly identifies steps that must be taken towards setting up these virtual environments?
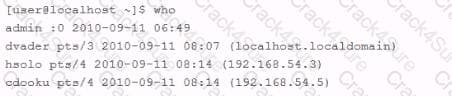
An employee is currently logged into the corporate web server, without permission. You log into the web server as 'admin" and look for the employee's username: "dmaul" using the "who" command. This is what you get back:
To be considered a strong algorithm, an encryption algorithm must be which of the following?
In preparation to do a vulnerability scan against your company's systems. You've taken the steps below:
You've notified users that there will be a system test.
You've priontized and selected your targets and subnets.
You've configured the system to do a deep scan.
You have a member of your team on call to answer questions.
Which of the following is a necessary step to take prior to starting the scan?
What is the maximum number of connections a normal Bluetooth device can handle at one time?
What is the discipline of establishing a known baseline and managing that condition known as?
A web application requires multifactor authentication when a user accesses the application from a home office but does not require this when the user is in the office. What access control model is this describing?
You are responsible for a Microsoft based network. Your servers are all clustered. Which of the following are the likely reasons for the clustering?
Each correct answer represents a complete solution. Choose two.
You work as a Linux technician for Tech Perfect Inc. You have lost the password of the root. You want to provide a new password. Which of the following steps will you take to accomplish the task?
Dilbert wants to have a script run on his Windows server every time Wally logs into it. Where should he place this script?
Which of the following tools is used to configure, control, and query the TCP/IP network interface parameters?
Which of the following would be a valid reason to use a Windows workgroup?
In PKI, when someone wants to verify that the certificate is valid, what do they use to decrypt the signature?
When using Pretty Good Privacy (PGP) to digitally sign a message, the signature is created in a two-step process. First, the message to be signed is submitted to PGP's cryptographic hash algorithm. What is one of the hash algorithms used by PGP for this process?
How can an adversary utilize a stolen database of unsalted password hashes?
An IT security manager is trying to quickly assess the risks associated with not implementing a corporate firewall system. What sort of risk assessment is most appropriate?
What is the function of the TTL (Time to Live) field in IPv4 and the Hop Limit field in IPv6 In an IP Packet header?
Which of the following networking topologies uses a hub to connect computers?
You have been hired to design a TCP/IP-based network that will contain both Unix and Windows computers. You are planning a name resolution strategy. Which of the following services will best suit the requirements of the network?
You work as a Network Administrator for McNeil Inc. The company has a Linux-based network. David, a Sales Manager, wants to know the name of the shell that he is currently using. Which of the following commands will he use to accomplish the task?
When are Group Policy Objects (GPOs) NOT applied automatically to workstations?
Which of the following elements is the most important requirement to ensuring the success of a business continuity plan?
Which of the following tasks is the responsibility of a Linux systems administrator who is deploying hardening scripts to his systems?
Critical information is encrypted within an application accessible only to a small group of administrators, with a separate group of administrators holding the decryption keys. What Defense in Depth approach is being used?
What are the two actions the receiver of a PGP email message can perform that allows establishment of trust between sender and receiver?
The Linux command to make the /etc/shadow file, already owned by root, readable only by root is which of the following?
Which of the following statements would be seen in a Disaster Recovery Plan?
You work as a Network Administrator for Perfect Solutions Inc. The company has a Linux-based network. You are required to search for the error messages in the /var/log/messages log file. Which of the following commands will you use to accomplish this?
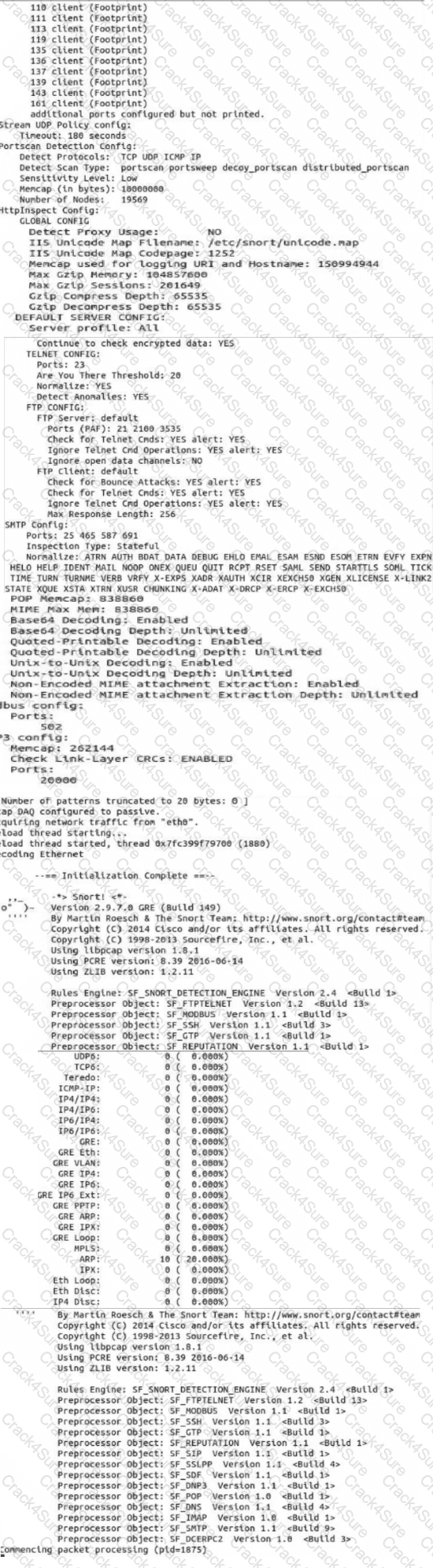
Use sudo to launch Snort with the, /etc /snort /snort.conf file In full mode to generate alerts based on incoming traffic to echo. What is the source IP address of the traffic triggering an alert with a destination port of 156?
Note: Snort Is configured to exit after It evaluates 50 packets.
Which of the following is the FIRST step in performing an Operational Security (OP5EC) Vulnerabilities Assessment?
Which command would allow an administrator to determine if a RPM package was already installed?
What does an attacker need to consider when attempting an IP spoofing attack that relies on guessing Initial Sequence Numbers (ISNs)?
You work as a Network Administrator for McRobert Inc. You want to know the NetBIOS name of your computer. Which of the following commands will you use?
Which of the following is a standard Unix command that would most likely be used to copy raw file system data for later forensic analysis?
A Windows administrator wants to automate local and remote management tasks in Active Directory. Which tool is most appropriate for this?
During a scheduled evacuation training session the following events took place in this order:
1. Evacuation process began by triggering the building fire alarm.
2a. The meeting point leader arrived first at the designated meeting point and immediately began making note of who was and was not accounted for.
2b. Stairwell and door monitors made it to their designated position to leave behind a box of flashlights and prop the stairway doors open with a garbage can so employees can find exits and dispose of food and beverages.
2c. Special needs assistants performed their assigned responsibility to help employees out that require special assistance.
3. The safety warden communicated with the meeting point leader via walkie talkie to collect a list of missing personnel and communicated this information back to the searchers.
4. Searchers began checking each room and placing stick-it notes on the bottom of searched doors to designate which areas were cleared.
5. All special need assistants and their designated wards exited the building.
6. Searchers complete their assigned search pattern and exit with the Stairwell/door monitors.
Given this sequence of events, which role is in violation of its expected evacuation tasks?
Your organization is developing a network protection plan. No single aspect of your network seems more important than any other. You decide to avoid separating your network into segments or categorizing the systems on the network. Each device on the network is essentially protected in the same manner as all other devices.
This style of defense-in-depth protection is best described as which of the following?
Which aspect of UNIX systems was process accounting originally developed for?
Which of the following activities would take place during the containment phase?
Which of the following fields CANNOT be hashed by Authentication Header (AH) in transport mode?
Your system has been infected by malware. Upon investigation, you discover that the malware propagated primarily via email. The malware attacked known vulnerabilities for which patches are available, but due to problems with your configuration management system you have no way to know which systems have been patched and which haven't, slowing your progress in patching your network. Of the following, which solution would you use to protect against this propagation vector?