3 Months Free Update
3 Months Free Update
3 Months Free Update
Which of the following attacks is any form of cryptanalysis where the attacker can observe the operation of a cipher under several different keys whose values are initially unknown, but where some mathematical relationship connecting the keys is known to the attacker?
In which of the following Person-to-Person social engineering attacks does an attacker pretend to be an outside contractor, delivery person, etc., in order to gain physical access to the organization?
Which of the following terms describes the statement given below?
"It is a service on a computer system (usually a server) that delays incoming connections for as long as possible. The technique was developed as a defense against a computer worm, and the idea is that network abuses, such as spamming or broad scanning, are less effective if they take too long."
What is another term that can be assigned to the pre-program analysis and research to determine if a program should be initiated?
Ryan wants to create an ad hoc wireless network so that he can share some important files with another employee of his company. Which of the following wireless security protocols should he choose for setting up an ad hoc wireless network?
Each correct answer represents a part of the solution. Choose two.
Which of the following processes is described in the statement below?
"It is the process of implementing risk response plans, tracking identified risks, monitoring residual risk, identifying new risks, and evaluating risk process effectiveness throughout the project."
Part of your change management plan details what should happen in the change control system for your project. Theresa, a junior project manager, asks what the configuration management activities are for scope changes. You tell her that all of the following are valid configuration management activities except for which one?
You work as an Exchange Administrator for McRobert Inc. You are configuring a new Exchange 2000 Server computer and two storage groups, group A and group B, on your network. You have to configure the physical disks on the Exchange 2000 Server computer to provide better performance and availability. Which configuration will you use to achieve this?
You work as a Network Administrator for Net World Inc. The company has a Windows Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2003. A Public Key Infrastructure (PKI) is installed on a server in the domain. You are planning to go on vacation for two weeks. Your team has three assistant administrators. You are required to accomplish the following tasks:
• Delegate the authority to the assistant administrators to issue, approve, and revoke certificates.
• The solution must involve least administrative burden.
Which of the following steps will you take to accomplish the tasks?
You are the project manager of the Workstation Improvement Project for your organization. This project will replace 925 workstations with new computers for your company's employees. Mark Jones, the sales manager, has requested that your project add 250 laptops as part of this project as his employees do not have workstations as they travel as part of the sales process. Mark insists that his department in the company can pay for the cost of the laptops. All of the following are components that will be affected by this change request except for which one?
In which of the following malicious hacking steps does email tracking come under?
Which of the following statements about Secure Shell (SSH) are true?
Each correct answer represents a complete solution. Choose three.
Which of the following terms describes an attempt to transfer DNS zone data?
You are the project manager of the GYG Project. A new scope change is being considered for your project. You are concerned, however, that the scope change may add costs, risks, and adversely affect the project schedule. What project management process is responsible for evaluating the full effect of a proposed scope change on your project?
John, a malicious hacker, forces a router to stop forwarding packets by flooding it with many open connections simultaneously so that all hosts behind it are effectively disabled. Which of the following attacks is John performing?
Mark works as a Network Administrator for Technet Inc. The company has a Windows 2003 domainbased network. The network has a file server that uses a RAID-5 volume. The RAID-5 volume is configured with five hard disk drives. Over the weekend, a drive in the RAID-5 volume fails. What will Mark do to restore the RAID-5 volume?
You are responsible for securing the network at a law firm. They are particularly interested in ensuring that sensitive documents are not disclosed to outside parties. In securing the printers and scanners, which of the following statements are true?
Each correct answer represents a complete solution. Choose three.
You work as a Network Administrator for Perfect Solutions Inc. The company has a Linux-based network. You are working as a root user on the Linux operating system. Your company is facing an IP spoofing attack. Which of the following tools will you use to get an alert saying that an upcoming IP packet is being spoofed?
Which of the following evidences are the collection of facts that, when considered together, can be used to infer a conclusion about the malicious activity/person?
You work as a professional Ethical Hacker. You are assigned a project to perform blackbox testing of the security of www.we-are-secure.com. Now you want to perform banner grabbing to retrieve information about the Webserver being used by we-are-secure. Which of the following tools can you use to accomplish the task?
Which of the following methods will free up bandwidth in a Wireless LAN (WLAN)?
Which of the following uses a variable-length Initialization Vector (IV), where the encrypted data begins?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He finds that the We-are-secure server is vulnerable to attacks. As a countermeasure, he suggests that the Network Administrator should remove the IPP printing capability from the server. He is suggesting this as a countermeasure against __________.
In which of the following does a Web site store information such as user preferences to provide customized services to users?
Which of the following tools can be used to perform a whois query?
Each correct answer represents a complete solution. Choose all that apply.
Joseph works as a Network Administrator for WebTech Inc. He has to set up a centralized area on the network so that each employee can share resources and documents with one another. Which of the following will he configure to accomplish the task?
Which of the following is a process of monitoring data packets that travel across a network?
Your IDS discovers that an intruder has gained access to your system. You immediately stop that access, change passwords for administrative accounts, and secure your network. You discover an odd account (not administrative) that has permission to remotely access the network. What is this most likely?
Which of the following blocks unwanted advertisements and small windows that pop up suddenly in IE, without user's initiation?
Which of the following is a structured review of the procurement process originated at the Plan Procurements process?
Which of the following is the encryption subsystem of the NTFS file system?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He writes the following snort rule:
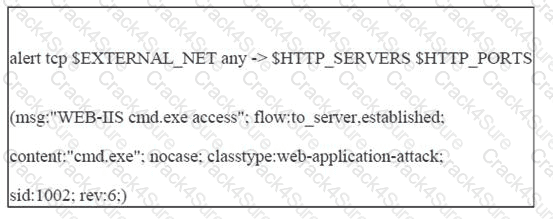
This rule can help him protect the We-are-secure server from the __________.
Which of the following are symptoms of a virus attack on your computer?
Each correct answer represents a complete solution. Choose two.
You are concerned about attackers simply passing by your office, discovering your wireless network, and getting into your network via the wireless connection. Which of the following are NOT steps in securing your wireless connection?
Each correct answer represents a complete solution. Choose two.
Which of the following honeypots captures limited amounts of information, mainly transactional data and some limited interaction?
You work as a Network Administrator in a company. The NIDS is implemented on the network. You want to monitor network traffic. Which of the following modes will you configure on the network interface card to accomplish the task?
Which of the following is a physical or logical subnetwork that contains and exposes external services of an organization to a larger network, usually the Internet?
Which of the following is used to communicate with an authentication server commonly used in UNIX networks?
Which of the following attacks allows the bypassing of access control lists on servers or routers, and helps an attacker to hide?
Each correct answer represents a complete solution. Choose two.
Which methodology is a method to analyze the involved tasks in completing a given project, especially the time needed to complete each task, and identifying the minimum time needed to complete the total project?
You work as Network and Security Manager for PassGuide Inc. The management of the company is quite concerned about the security of the network. The management has assigned this task to you to improve the security. Which of the following access methods will you use if the method is to be primarily based on pre-established access, and users cannot change it?
You are advising a school district on disaster recovery plans. In case a disaster affects the main IT centers for the district they will need to be able to work from an alternate location. However, budget is an issue. Which of the following is most appropriate for this client?
You are the program manager for your organization. You have proposed a program that will cost $750,000 and will last for four years. Management is concerned with the cost of the program in relation to the return your program will bring. If the rate of return is six percent what is the minimum value your project should return in four years based on the investment of the program?
You work as an Administrator for Bluesky Inc. The company has 145 Windows XP Professional client computers and eighty Windows 2003 Server computers. You want to install a security layer of WAP specifically designed for a wireless environment. You also want to ensure that the security layer provides privacy, data integrity, and authentication for client-server communications over a wireless network. Moreover, you want a client and server to be authenticated so that wireless transactions remain secure and the connection is encrypted. Which of the following options will you use to accomplish the task?
Janet is the project manager of the NHQ Project for her company. Janet is nearly done leading the project and there have been no cost or schedule overruns in the development of the new software for her company. The project team has been completing their work on time and there is still $75,000 left in the project budget. Janet decides to have the project team implement some extra features to the project scope to use all of the $75,000 in the budget even though the customer didn't specifically ask for the added features. This scenario is an example of which one of the following?
An intruder is trying to get user passwords by pretending to be help desk staff. Which of the following types of security attacks do you think it is?
Which of the following are considered Bluetooth security violations?
Each correct answer represents a complete solution. Choose two.
You are a project manager of a construction project. You are documenting project purchasing decisions, specifying the approach, and identifying potential sellers. You are in which of the following processes?
Which system is designed to analyze, detect, and report on security-related events?
Which of the following protocols is used as a transport protocol for Internet dial-up connections?
Which of the following is the practice of a domain name registrant using the five-day "grace period" (the Add Grace Period or AGP) at the beginning of the registration of an ICANN-regulated second-level domain to test the marketability of the domain?
You are the project manager for your organization and are trying to determine which vendor your organization will use. You have determined that any vendor that would like to bid on your project work will need to have a Microsoft Certified System Engineer on staff, have eight years of Cisco experience, and have at least two references from similar projects. What have you created in this scenario?
Which of the following password authentication schemes enables a user with a domain account to log on to a network once, using a password or smart card, and to gain access to multiple computers in the domain without being prompted to log in again?
Which of the following features of IE prevent users from a type of scam that entice a user to disclose personal information such as social security number, bank account details, or credit card number?
A user has opened a Web site that automatically starts downloading malicious code onto his computer. What should he do to prevent this?
Each correct answer represents a complete solution. Choose two.
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He wants to use Kismet as a wireless sniffer to sniff the We-are-secure network. Which of the following IEEE-based traffic can be sniffed with Kismet?
Each correct answer represents a complete solution. Choose all that apply.
You work in an enterprise as a Network Engineer. Your enterprise has a secure internal network. You want to apply an additional network packet filtering device that is intermediate to your enterprise's internal network and the outer network (internet). Which of the following network zones will you create to accomplish this task?
Consider the following diagram:
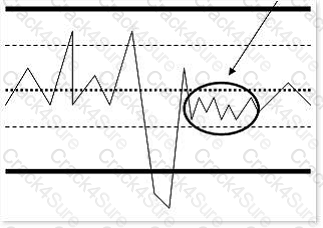
What is the highlighted area of the diagram known as?
Complete the following sentence: Quality control is a(n)_______________ process while quality assurance is a(n)________________ process.
Which of the following statements are true about an application-level gateway?
Each correct answer represents a complete solution. Choose all that apply.
John works as a professional Ethical Hacker. He is assigned a project to test the security of www.weare-secure.com. He enters a single quote in the input field of the login page of the We-are- secure Web site and receives the following error message:
Microsoft OLE DB Provider for ODBC Drivers error '0x80040E14'
This error message shows that the We-are-secure Website is vulnerable to __________.
You are the Network Administrator for a bank. In addition to the usual security issues, you are concerned that your customers could be the victim of phishing attacks that use fake bank Web sites.
Which of the following would protect against this?
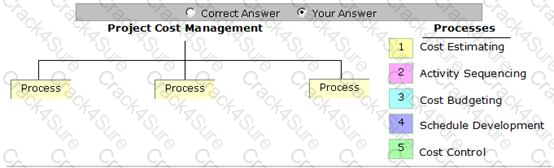
Place the processes that are grouped under the Project Cost Management Knowledge Area in the image below.
You are responsible for network security at a defense contractor. You are very concerned about sensitive data not getting out of your network. You have specific concerns about employees or contractors sending out files via FTP, or even spyware sending out data. You have blocked and monitored ports (as many as you can) on your firewall, and of course, run an anti spyware package.
Which of the following is another step you should take in preventing sensitive data from being sent out of your network without authorization?
Which of the following types of attacks occurs when an attacker successfully inserts an intermediary software or program between two communicating hosts?
You have inserted a Trojan on your friend's computer and you want to put it in the startup so that whenever the computer reboots the Trojan will start to run on the startup. Which of the following registry entries will you edit to accomplish the task?
Which of the following types of cryptography algorithms uses the MD series of encryption algorithms?
John is a malicious attacker. He illegally accesses the server of We-are-secure Inc. He then places a backdoor in the We-are-secure server and alters its log files. Which of the following steps of malicious hacking includes altering the server log files?
PassGuide Research and Training Center is developing its new network model. Which of the following protocols should be implemented in the new network? (Click the Exhibit button on the toolbar to see the case study.) Each correct answer represents a complete solution. Choose two.
A war dialer is a tool that is used to scan thousands of telephone numbers to detect vulnerable modems. It provides an attacker unauthorized access to a computer. Which of the following tools can an attacker use to perform war dialing?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following tasks can be performed by a malicious bot/botnet?
Each correct answer represents a complete solution. Choose all that apply.
The Project Scope Management knowledge area focuses on which of the following processes?
Each correct answer represents a complete solution. Choose all that apply.
When no anomaly is present in an Intrusion Detection, but an alarm is generated, the response is known as __________.