3 Months Free Update
3 Months Free Update
3 Months Free Update
You work as a Software Developer for ABC Inc. You develop an application using Visual Studio .NET 2005. You want to print the contents of a document named MyFile1.doc located on the local computer. Therefore, you use the printing controls in the application. Which of the following events will you use in the application code to accomplish the task?
You work as a Software Developer for ABC Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You are creating an application using .NET Framework 2.0. The application will be used by all the branches of the company. You sometimes require a variable number of arguments to be passed to a method. For example, you may require a sum method, which calculates the total of the numbers passed to it no matter how many numbers are passed. What will you do to accomplish the task?
You work as a Software Developer for ManSoft Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You create an application that will be used by all the branches of the company. You use the Regex class in the application to validate some strings. You want to search an input string for an occurrence of a regular expression. Which of the following methods of the Regex class will you use to accomplish the task?
Allen works as a Software Developer for ABC Inc. He develops a Windows application. He adds a form to the application named Form1, which contains a Label control named Label1. A text file named File1.txt contains a list of products. File1.txt is located in the application directory. Each product name is listed in a new line in File1.txt. Allen wants to retrieve a list of products from File1.txt and display it in Label1. He adds the following code to the application:
1. StreamReader Reader1 = new StreamReader((Stream)File.OpenText(Server.MapPath
("File1.txt")));
2. Stream MyStream;
3. string InputString;
4. // Insert statement here.
5. while (InputString != null)
6. {
7. Label1.Text = String.Format("{0}{1}", Label1.Text, InputString);
8. Reader1.ReadLine();
9. }
10. Reader1.Close();
Which of the following statements will Allen add at line 4 to accomplish the task?
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You create an application for the company. You need to validate the phone number passed to a class as a parameter in the application. Which of the following is the most effective way to verify that the format of the data matches a phone number?
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2008 as its application development platform. You create an ASP.NET Web application using the .NET Framework 3.5. The application uses Session objects. You are changing the application to run on a Web farm. You want to make sure that the application can access the Session objects from all the servers in the Web farm. You also make sure that when any server in the Web farm restarts or stops responding, the Session objects are not lost. What will you do?
Which of the following code snippets is an example of tight encapsulation?
Mark works as a Software Developer for GenTech Inc. He develops an application, named App1, using Visual Studio .NET. The application contains a Form control, named Form1, which enables users to edit information in a SQL Server database. Mark wants to save all the changes made by users in the database. He defines a boolean variable, named DataIsSaved, in the application code. DataIsSaved indicates whether or not all data are saved in the database. Mark wants to prevent Form1 from closing until all the changes are saved in the database. Which of the following code will he use to accomplish this?
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create the definition for a Car class by using the following code segment:
public class Car {
[XmlAttribute(AttributeName = "category")]
public string CarType;
public string model;
[XmlIgnore]
public int year;
[XmlElement(ElementName = "mileage")]
public int miles;
public ConditionType condition;
public Car() {
}
public enum ConditionType {
[XmlEnum("Poor")] BelowAverage,
[XmlEnum("Good")] Average,
[XmlEnum("Excellent")] AboveAverage
}}
You create an instance of the Car class. You fill the public fields of the Car class as shown in the table below:
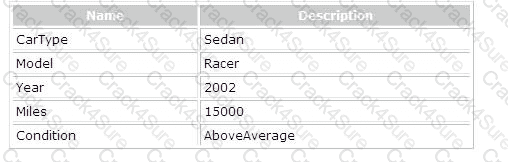
You are required to recognize the XML block that is produced by the Car class after serialization. Which of the following XML blocks represents the output of serializing the Car class?
You work as a Software Developer for ABC Inc. You develop a .NET application form for
registered users. You want to ensure that the form is able to validate data and provide feedback to a user whenever an invalid data is entered by him. According to you, which of the following user feedback mechanisms will be most appropriate?
Julia works as a Software Developer for Mansoft Inc. She develops an application using Visual Studio .NET. The application uses a method named MyMethod, which is located in an unmanaged DLL. Julia wants MyMethod to require the application to allocate unmanaged memory, fill the data, and pass the memory address to the application. She also wants to ensure that on returning from MyMethod, the application de-allocates the unmanaged memory. What will Julia do to accomplish the task?
Sandra works as a Software Developer for ABC Inc. She develops an application named MyApp that contains a data-bound control named MyDataControl. She wants to use an Oracle database in order to bind data to MyDataControl. Which of the following GUI-based data sources will Sandra use to accomplish the task?
You work as a Web Application Developer for SunInfo Inc. The company uses Visual Studio 2008 as its application development platform. You create a Web application using .NET Framework 3.5. You want to implement state management in your application. In which of the following stages of the application life cycle will your application actually start?
John works as a Web Developer for ABC Inc. He develops an ASP.NET application, named MyApp1, using Visual Studio .NET. The application will be used in the Sales department to generate monthly reports. The company uses Microsoft Windows authentication. All users are in the TESTPRO1 domain. John wants to ensure that all users except Mark, Roger, and David are allowed to access the application. Which of the following code will he use in the application's Web.config file to accomplish the task?
You work as an Application Developer for ABC. The company uses Visual Studio .NET Framework 3.5 as its application development platform. You are working on enhancements to an existing WPF application. One problem you have been encountering is that users of the current version routinely enter invalid data, and since the controls use data binding, that data either gets put in the database incorrectly, or in some cases generates a database error. You want to incorporate validation with your data bound controls. Which of the following choices is the best way to accomplish this goal?
You work as a Web Application Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a Web application using .NET Framework 2.0. The application is for members only. The behavior of the Web application varies according to the role of the user. The Web application uses the ASP.NET Membership control for creation of user accounts. You are required to find out whether a user is a member of a specific role. What will you do?
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2008 as its application development platform. You create an ASP.NET Web application using the .NET Framework 3.5. The application is used to map HTTP requests to HTTP handlers based on a file name extension. You need to ensure that each HTTP handler processes individual HTTP URLs or groups of URL extensions in the application.
Which of the following built-in HTTP handlers will you use to accomplish this task?
Each correct answer represents a part of the solution. Choose all that apply.
Maria works as a Software Developer for BlueWell Inc. She develops an application, named App1, using Visual C# .NET. The application displays employee details from a SQL Server database. Maria wants to use a string array, named MyArray, in the application code to store employee names. Which of the following statements will she use to declare MyArray?
You work as a Software Developer for ABC Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You are creating an application using .NET Framework 2.0. You want to authenticate users before using the application. Therefore, you decide to use the authentication method that uses encryption to authenticate users. What will you do to accomplish the task?
Allen works as a Software Developer for Mansoft Inc. He develops a Web application using Visual Studio .NET. He adds a Web reference to an XML Web service named MyWebService in the application. MyWebService includes a method named MyMethod, which takes user identification number as a parameter and returns a DataSet object containing user information. The System.ArgumentException is thrown if the user identification number does not lie between 1 and 500. Allen writes a try and catch block to capture the exception thrown by the Web service. Which of the following exceptions will the try and catch block catch if a user calls MyMethod passing 501 as a parameter?
Samantha works as a Software Developer for InfoWorld Inc. She develops a Web page named SalesReport.aspx for the employees of the company. However, she wants to ensure that all the requests for a particular employee are not stored on the server's memory. She also wants to ensure that no data is lost even after each user session has expired. Which of the following actions will Samantha take to accomplish the task?
Maria works as a Software Developer for MarcLync Inc. She creates an XML Web service, named MyWebService, using Visual Studio .NET. Maria wants to debug MyWebService. Therefore, she attaches a debugger to the Web service process. However, Maria notices that whenever MyWebService is executed, it throws an exception System.Net.WebException after a certain time period. The exception displays the message "The current operation has timed-out." Maria wants to modify the code in MyWebService. Which of the following actions will Maria take in order to resolve this issue?
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You create an application named StringRW using .NET Framework. You store some characters into an array of Unicode characters. You need to write all or some of these characters into a String object. Which of the following code segments will you choose to accomplish this task?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You create an application for the company. You need to validate the phone number passed to a class as a parameter in the application. Which of the following is the most effective way to verify that the format of the data matches a phone number?
Sam works as a Software Developer for BlueWell Inc. He creates a .NET Remoting object named MyObj using Visual Studio .NET. He wants to configure MyObj to send and receive confidential information from an XML file stored in an encrypted hard drive. What will he do to accomplish the task?
Each correct answer represents a part of the solution. Choose two.
George works as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. George creates an application using the .NET Framework. He writes the following code snippet in the application:
public class FirstClass
{
public static int test=500;
}
public class SecondClass : FirstClass
{
public static void Main(String[] args)
{
SecondClass mb=new SecondClass();
mb.MyMethod();
}
public void MyMethod()
{
//Appropriate statement
}
}
George wants to modify the value of the test variable in MyMethod to 1000. Which of the following code segments will he place in MyMethod to accomplish this task?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET as its application development platform. You have recently finished development of an application using .NET Framework. The application used two threads named threadOne and threadTwo. You are required to modify the code of the application to prevent the execution of threadOne until threadTwo completes execution. What will you do to accomplish this task?
You work as a Software Developer for ManSoft Inc. You create an application using Visual Studio .NET
2005. You write the following code snippet in the application:
int amt = 50;
String s = "John gave me " + amt + " dollars";
Console.WriteLine(s);
What will be the output of the above code?
Mark works as a Web Developer for ABC Inc. He develops an ASP.NET application, named MyApp1, using Visual Studio .NET. MyApp1 allows users to view and purchase company products.
It includes several pages. The start-up page of the application is Page1.aspx. He configures the application's Web.config file to use form-based authentication.
Mark wants users to log on to Page1.aspx by providing their user names and passwords. To accomplish this, he creates an ASP.NET page named UsersLogIn.aspx that allows each user to specify a user name and password. He then writes the following syntax in the Web.config filE.
loginUrl="/UsersLogIn.aspx" protection="All" timeout="60" slidingExpiration="true">
What will be the result?
Each correct answer represents a part of the solution. Choose two.
Allen works as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2008 as its application development platform. Allen develops an application using .NET Framework 3.5. The application connects to a SQL Server database using a SqlConnection object named Connection1. He creates some stored procedures in the database, which are used to update the data. Allen finds that sometimes, the update operation does not affect any row. He wants to add an error handling code to the application. Which of the following code segments will he use to accomplish the task?
Mark works as a Software Developer for BlueWell Inc. The company uses Visual Studio .NET as its application development platform. He develops four applications using the .NET Framework.. All the four applications use an assembly named MyAssembly. He deploys the applications on the company's intranet. Later, Mark modifies MyAssembly and wants to ensure that all applications use the latest version of MyAssembly. What will he do to accomplish this?
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create an application using the .NET Framework. You create a class named Master that contains numerous child objects. The Master class contains a method named ProcessChild that executes actions on the child objects. The Master class objects will be serializable. You must ensure that the ProcessChild method is executed subsequent to the Master class object and all its child objects are reformed. Which of the following actions will you take to accomplish the task?
Each correct answer represents a part of the solution. Choose two.
Charles works as a Web Developer for TechNet Inc. He develops an application named AdAgentsApp for advertising agents by using Visual Studio .NET. AdAgentsApp uses several Web services provided by the company. The employees in the IT department use only the existing port numbers 80 (HTTP protocol) and 443 (HTTPS protocol) for firewall security. However, they are forbidden to open any other new ports. These ports have been used to ensure the highest security level of authentication.
Which of the following actions should Charles take to maintain the highest security?
Each correct answer represents a part of the solution. Choose two.
Kathy works as a Software Developer for BlueWell Inc. She creates a serviced component named
Com1. She wants to ensure that all the employees of the company are able to use Com1. Therefore, she wants to install Com1 in the Global Assembly Cache (GAC). Before the installation, she wants to register the serviced component manually with COM+. Which of the following tools will Kathy use to register Com1?
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You are developing an application that will manage rental properties for a property management agency. When a property is rented, a lease agreement is created. At that time a new lease is entered into the application, the starting date of the lease may not yet be known.
You need to write code that stores the lease start date entered by a user in a variable. The variable that stores the lease start date should contain no value, by default. If no lease start date is entered, the variable should have no value assigned to it.
Which code segment should you choose?
You work as a Software Developer for Mansoft Inc. The company uses Visual Studio.NET as its application development platform. You create an application, which will be used for e-commerce.
You want to ensure that the transactions are highly secured. For this purpose, you have to create a system to verify the identity of a potential customer. Which of the following security techniques will you use to accomplish this task?
You work as a Software Developer for ManSoft Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You are creating a global application that will be used by all the branches of the company. You want to perform the encoding of Unicode characters with error detection capability. Which of the following classes will you use to accomplish the task?
Each correct answer represents a complete solution. Choose three.
You work as an Enterprise Application Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create an ASP.NET application using .NET Framework 3.5. You have already created a data contract for a WCF service and the ASP.NET Web application, which consumes the WCF service. The application has the following requirements:
l On low network bandwidth the serialized format of the data contract type should be minimum.
l The application uses AJAX to retrieve the data from the WCF service.
l Use the least amount of development effort.
What will you do?
You work as a Software Developer for Mansoft Inc. You create an application and use it to create code access security policies. Which of the following tools will you use to examine and modify code access security policies from a batch file?
Which of the following classes will you use to specify that a string must be centered when drawn?
Allen works as a Software Developer for ABC Inc. The company uses Visual Studio.NET as its application development platform. He creates an application using .NET Framework. He wants to encrypt all his e-mails that he sends to anyone. Which of the following will he use to accomplish the task?
You work as an Enterprise Application Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create a logging utility class using .NET Framework 3.5. The utility class writes logs to event log services. You are required to ensure that the client applications that use the utility class can create an instance of the utility class only if they have access rights to write to the event log services.
What will you do?
Which of the following is not a method of controlling traffic through a firewall?
You work as a Windows Application Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a Windows application using .NET Framework 2.0. The application allows computer engineers to design circuit boards for different types of hardware. You create a custom control that represents the design surface. You are required to highlight the vacant areas on the design surface where a component can be dropped. Which of the following events will you use to accomplish this task?
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You have recently finished the development of an ASP.NET Web application using .NET Framework 3.5. The application must be deployed by using the http://www.ABC.com/ URL. The application has several Web forms.
You need to implement Really Simple Syndication (RSS) feeds functionality. The RSS feeds will be used by the http://www.ABC.com/Updates.rss URL. You must ensure that the application displays the RSS-formatted information when accessing the given URL. What will you do to accomplish this?
Each correct answer represents a part of the solution. Choose two.
Allen works as a Software Developer for ABC Inc. The company uses Visual Studio.NET as its application development platform. He creates an application using .NET Framework. He wants to encrypt all his e-mails that he sends to anyone. Which of the following will he use to accomplish the task?
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a method to call a COM component using the .NET Framework. You want to use declarative security to request the runtime to run a complete stack walk. You need to ensure that all callers be obliged to level of trust for COM interop before the callers execute the method. Which of the following attributes will you place on the method to accomplish the task?
You work as a Software Developer for ABC Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You have recently finished the development of an application using .NET Framework 2.0. The application can be used only for cryptography. Therefore, you have implemented the application on a computer. What will you call the computer that implemented cryptography?
You work as a .NET Trainer for ABC Inc. The Company uses .NET Framework as its application development platform. You are creating an application to demonstrate the use of datatypes. You create an unsigned Short datatype in the application. Which of the following values can be assigned to the unsigned Short datatype?
Each correct answer represents a complete solution. Choose three.
Which of the following modes can be used to configure the Remote Debugging Monitor for remote debugging?
Which of the following algorithms supports key lengths from 128 bits to 192 bits in increments of 64 bits?
You work as a Software Developer for ManSoft Inc. You use C# .NET to create an assembly named TestAssembly that will be used by other applications, including a standard COM client application. You must deploy the assembly on the COM application to a client computer. You must ensure that the COM applications can instantiate components within the assembly as COM components. Which of the following options will you use to accomplish this task?
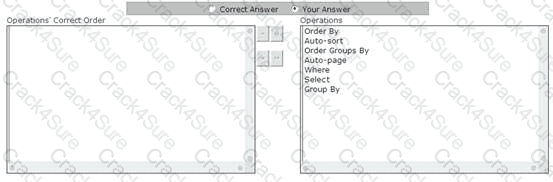
You work as a Windows Application Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create a Windows Forms application using .NET Framework 3.5. The application contains a data-bound control. You use the LinqDataSource control to use LINQ in the ASP.NET application by setting properties in markup text. The LinqDataSource control uses LINQ to SQL to automatically generate the data commands. You are required to perform data operations by using the LinqDataSource control. What is the correct order in which data operations are applied?
Which of the following session and instancing modes will you set if you require a sessionfull binding and want to create a new instance object for each client request?
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You need to write a code segment that transfers the contents of a byte array named ToSend by using a NetworkStream object named NetStr. You want to use a cache of size only 8,192 bytes. Which of the following code segments will you use to accomplish the task?
Allen works as a Software Developer for ABC Inc. The company uses Visual Studio.NET as its application development platform. He creates an application using .NET Framework. He wants to encrypt all his e-mails that he sends to anyone. Which of the following will he use to accomplish the task?
Which of the following data structures is used for storing reference data types?
George works as a Software Developer for GenTech Inc. He creates an application named App1 using Visual Studio .NET. App1 uses the version 2.0.0.0 of an assembly named Assembly1. However, he wants App1 to use a new version i.e. 2.1.0.0 of Assembly1. Therefore, he needs to specify Assembly1's location so that App1 can use version 2.1.0.0 of Assembly1. What will George use to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You are creating an assembly. The assembly contains a public method. The Global Assembly Cache contains a second assembly. You require that the public method is only called from the second assembly. Which of the following permission classes will you use to accomplish this task?
Mark works as a Software Developer for BlueWell Inc. He is required to create a class, named Members. Each element of this class has a unique ID stored in a database field, named Member_ID. Which of the following options will he use to represent Member_ID, while designing the Members class?
Allen works as a Software Developer for ABC Inc. The company uses Visual Studio.NET as its application development platform. He creates an application using the .NET Framework.. He writes the following code segment in the application:
01 class gClass
02 {
03 public gClass(int k)
04 {
05 //Write code here
06 }
07 }
08 public class gSub : gClass
09 {
10 public static void Main(String[] argv)
11 {
12 gSub gs=new gSub(20);
13 }
14 gSub(int j):base(j)
15 {
16 //Write Code here
17 }
18 gSub(string st, int j):this(j)
19 {
20 gClass ss=new gClass();
21 }
22 }
When you execute the above code segment, you get an error at line 20. Which of the following code segments will he place at line 20 to execute the code successfully?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Software Developer for ABC Inc. You develop a Windows application named
MyApp1. MyApp1 contains a Windows form named MyWinForm1. The form uses several controls such as Button, TextBox, and Label. You want mouse click events to be raised in the form. You want to use the mouse events that pass an instance of EventArgs in the signature of the event handler of a Button control. Which of the following events will you use in the application to accomplish the task?
Each correct answer represents a complete solution. Choose three.
Patrick works as a Software Developer for GenTech Inc. He develops an application, named App1, using Visual C# .NET. He implements security using the security classes of the .NET Framework. He defines the following statements in the application:
PrincipalPermission Principal_Perm1 = new PrincipalPermission("Nick", "General
Manager");
PrincipalPermission Principal_Perm2 = new PrincipalPermission("Jack", "Accountant");
Patrick wants to check whether all demands that succeed for Principal_Perm1 also succeed for Principal_Perm2. Which of the following methods of the PrincipalPermission class will he use to accomplish this?
You work as a Software Developer for ManSoft Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You are creating a global application that will be used by all the branches of the company. You want to perform the encoding of Unicode characters. Which of the following classes will you use to accomplish the task?
Each correct answer represents a complete solution. Choose three.
You work as a Software Developer for SunSoft Inc. The company uses Visual Studio .NET 2005 as its application development platform. You use .NET Framework 2.0 to create several Windows applications. All applications use a common class library assembly named Customers. You deploy the application to the client computers on your company's intranet. Later, you modify the assembly. Any application that uses version 1.0.0.0 must now use version 2.0.0.0. Which of the following options will you use to accomplish the task?
You work as a Software Developer for ManSoft Inc. The company uses Visual Studio .NET as its application development platform. You create an application named MyRandomGen. You use the System.Security.Cryptography namespace. You want to create a code that randomly rolls the dice fifty times and displays the results on the screen. Which of the following code segments will you use to accomplish this task?
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create an ASP.NET Web application using .NET Framework 3.5. You create a Web form in the application that permits users to provide personal information. You add a DropDownList control to the Web form to retrieve the residential status of users. The default item that the DropDownList control displays is the "Select Country" option. You have to ensure that users select a country other than the default option. Which of the following validation controls should you use to accomplish this task?