We at Crack4sure are committed to giving students who are preparing for the Guidance Software GD0-110 Exam the most current and reliable questions . To help people study, we've made some of our Certification Exam for EnCE Outside North America exam materials available for free to everyone. You can take the Free GD0-110 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Using good forensic practices, when seizing a computer at a business running Windows 2000 Server you should:
Which of the following is commonly used to encode e-mail attachments?
By default, what color does EnCase use for the contents of a logical file?
You are examining a hard drive that has Windows XP installed as the operating system. You see a file that has a date and time in the deleted column. Where does that date and time come from?
When undeleting a file in the FAT file system, EnCase will check the _____________ to see if it has already been overwritten.
The default export folder remains the same for all cases.
If cases are worked on a lab drive in a secure room, without any cleaning of the contents of the drive, which of the following areas would be of most concern?
What files are reconfigured or deleted by EnCase during the creation of an EnCase boot disk?
A suspect typed a file on his computer and saved it to a floppy diskette. The filename was MyNote.txt. You receive the floppy and the suspect's computer. The suspect denies that the floppy disk belongs to him. You search the suspect's computer and locate only the filename within a .LNK file. The .LNK file is located in the folder C:\Windows\Recent. How you would use the .LNK file to establish a connection between the file on the floppy diskette and the suspect computer?
When Unicode is selected for a search keyword, EnCase:
Pressing the power button on a computer that is running could have which of the following results?
You are investigating a case involving fraud. You seized a computer from a suspect who stated that the computer is not used by anyone other than himself. The computer has Windows 98 installed on the hard drive. You find the filename C:\downloads\check01.jpg?that EnCase shows as being moved. The starting extent is 0C4057. You find another filename C:\downloads\chk1.dll with the starting extent 0C4057, which EnCase also shows as being moved. In the C:\windows\System folder you find an allocated file named chk1.dll with the starting extent 0C4057. The chk1.dll file is a JPEG image of a counterfeit check. Could this information be used to refute the suspect claim that he never knew it was on the computer?
How are the results of a signature analysis examined?
Two allocated files can occupy one cluster, as long as they can both fit within the allotted number of bytes.
Creating an image of a hard drive that was seized as evidence:
In DOS and Windows, how many bytes are in one FAT directory entry?
The maximum file segment size for an EnCase evidence file is:
Which of the following would most likely be an add-in card?
When a document is printed using EMF in Windows, what file(s) are generated in the spooling process?
The EnCase case file can be best described as:
The following keyword was typed in exactly as shown. Choose the answer(s) that would be found. All search criteria have default settings. Tom
Changing the filename of a file will change the hash value of the file.
To undelete a file in the FAT file system, EnCase obtains the starting extent from the:
Searches and bookmarks are stored in the evidence file.
RAM is tested during which phase of the power-up sequence?
A logical file would be best described as:
The following GREP expression was typed in exactly as shown. Choose the answer(s) that would result. Jan 1 st , 2?0?00
To later verify the contents of an evidence file?
When a file is deleted in the FAT or NTFS file systems, what happens to the data on the hard drive?
In Unicode, one printed character is composed of ____ bytes of data.
Which of the following would be a true statement about the function of the BIOS?
Which of the following statements is more accurate?
EnCase is able to read and examine which of the following file systems?
The EnCase default export folder is:
How many copies of the FAT are located on a FAT 32, Windows 98-formatted partition?
EnCase can build a hash set of a selected group of files.
The signature table data is found in which of the following files?
Which of the following selections would be used to keep track of a fragmented file in the FAT file system?
During the power-up sequence, which of the following happens first?
When a file is deleted in the FAT file system, what happens to the FAT?
A restored floppy diskette will have the same hash value as the original diskette.
Which of the following is found in the FileSignatures.ini configuration file?
All investigators using EnCase should run tests on the evidence file acquisition and verification process to:
This question addresses the EnCase for Windows search process. If a target word is within a logical file, and it begins in cluster 10 and ends in cluster 15 (the word is fragmented), the search:
The EnCase evidence file logical filename can be changed without affecting the verification of the acquired evidence.
If cluster #3552 entry in the FAT table contains a value of this would mean:
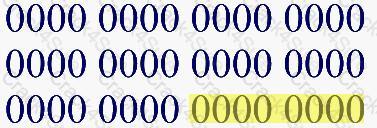
Select the appropriate name for the highlighted area of the binary numbers.
3 Months Free Update
3 Months Free Update
3 Months Free Update