We at Crack4sure are committed to giving students who are preparing for the HP HPE7-A02 Exam the most current and reliable questions . To help people study, we've made some of our Aruba Certified Network Security Professional Exam exam materials available for free to everyone. You can take the Free HPE7-A02 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
A company uses HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application option). In the details for a generic device cluster, you see a
recommendation for "Windows 8/10" with 70% accuracy.
What does this mean?
A company wants HPE Aruba Networking ClearPass Policy Manager (CPPM) to respond to Syslog messages from its Palo Alto Next Generation Firewall (NGFW)
by quarantining clients involved in security incidents.
Which step must you complete to enable CPPM to process the Syslogs properly?
A company uses both HPE Aruba Networking ClearPass Policy Manager (CPPM) and HPE Aruba Networking ClearPass Device Insight (CPDI). What is one way integrating the two solutions can help the company implement Zero Trust Security?
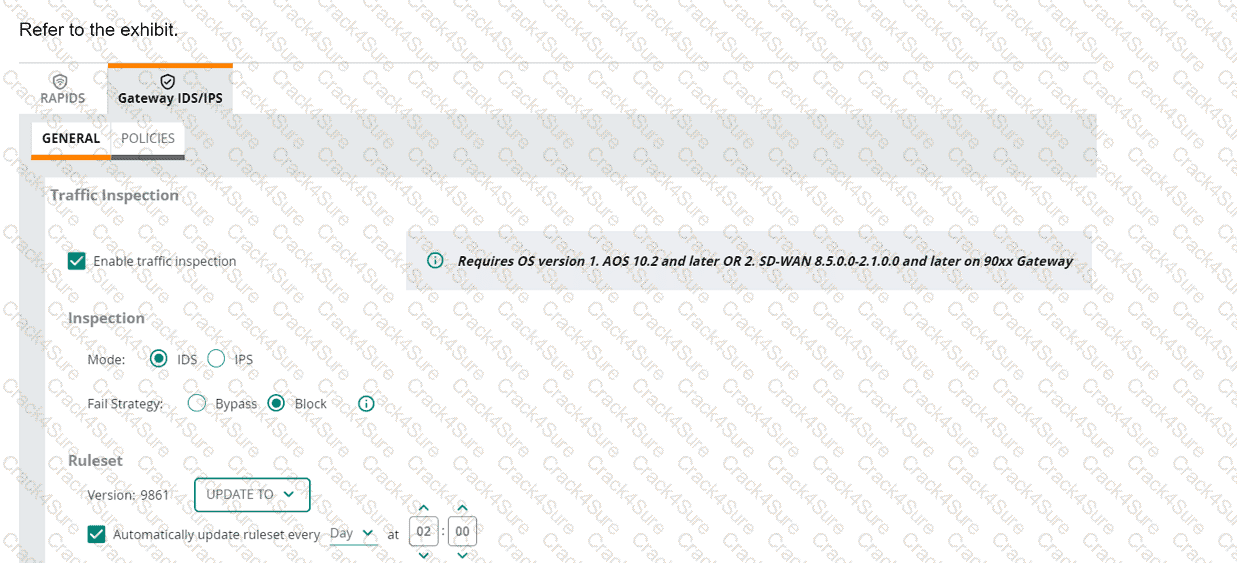
(Note that the HPE Aruba Networking Central interface shown here might look slightly different from what you see in your HPE Aruba Networking Central
interface as versions change; however, similar concepts continue to apply.)
An HPE Aruba Networking 9x00 gateway is part of an HPE Aruba Networking Central group that has the settings shown in the exhibit. What would cause the
gateway to drop traffic as part of its IDPS settings?
Refer to Exhibit:
An HPE Aruba Networking 9x00 gateway is part of an HPE Aruba Networking Central group that has the settings shown in the exhibit. What would cause the gateway to drop traffic as part of its IDPS settings?
A company uses HPE Aruba Networking ClearPass Policy Manager (CPPM) and HPE Aruba Networking ClearPass Device Insight (CPDI) and has integrated the
two. CPDI admins have created a tag. CPPM admins have created rules that use that tag in the wired 802.1X and wireless 802.1X services' enforcement policies.
The company requires CPPM to apply the tag-based rules to a client directly after it learns that the client has that tag.
What is one of the settings that you should verify on CPPM?
A company needs you to integrate HPE Aruba Networking ClearPass Policy Manager (CPPM) with HPE Aruba Networking ClearPass Device Insight (CPDI). What is one task you should do to prepare?
Which statement describes Zero Trust Security?
An admin has configured an AOS-CX switch with these settings:
port-access role employees
vlan access name employees
This switch is also configured with CPPM as its RADIUS server.
Which enforcement profile should you configure on CPPM to work with this configuration?
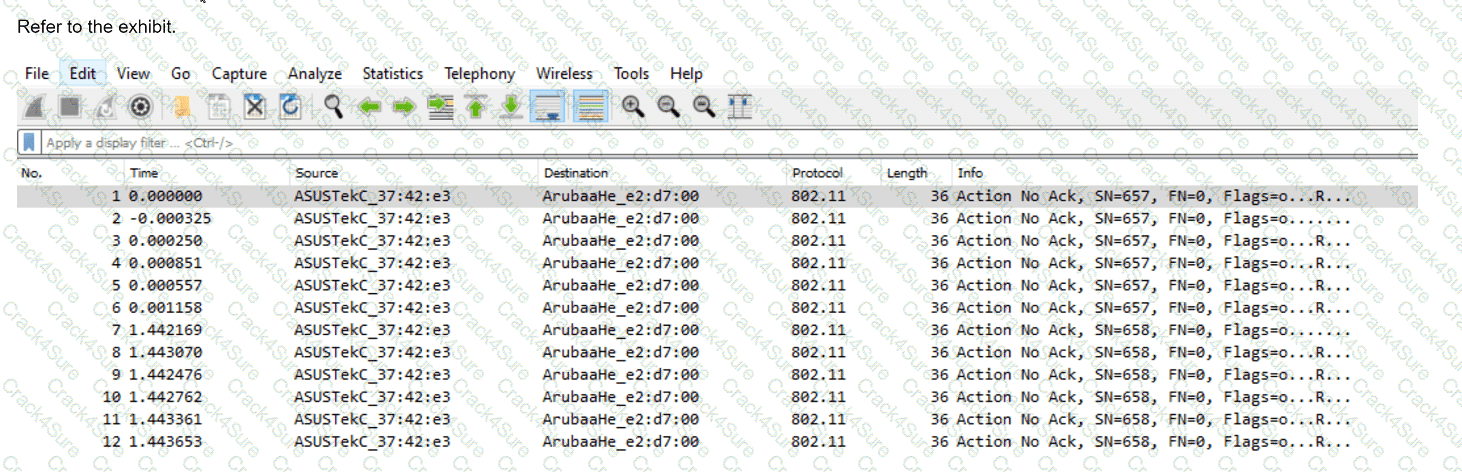
You have downloaded a packet capture that you generated on HPE Aruba Networking Central. When you open the capture in Wireshark, you see the output shown in the
exhibit.
What should you do in Wireshark so that you can better interpret the packets?
You are using OpenSSL to obtain a certificate signed by a Certification Authority (CA). You have entered this command:
openssl req -new -out file1.pem -newkey rsa:3072 -keyout file2.pem
Enter PEM pass phrase: **********
Verifying - Enter PEM pass phrase: **********
Country Name (2 letter code) [AU]:US
State or Province Name (full name) [Some-State]:California
Locality Name (eg, city) []:Sunnyvale
Organization Name (eg, company) [Internet Widgits Pty Ltd]:example.com
Organizational Unit Name (eg, section) []:Infrastructure
Common Name (e.g. server FQDN or YOUR name) []:radius.example.com
What is one guideline for continuing to obtain a certificate?
As part of setting up an HPE Aruba Networking ClearPass Onboard solution for wireless clients, you created Network Settings, a Configuration Profile, and a Provisioning Settings object in ClearPass Onboard. You also ran the ClearPass Onboard Service Only Template on ClearPass Policy Manager (CPPM).
You now need to ensure that only domain users are authenticated and allowed to log into the ClearPass Onboard portal.
Which component should you edit?
A company has AOS-CX switches and HPE Aruba Networking APs, which run AOS-10 and bridge their SSIDs. Company security policies require 802.1X on all edge ports, some of which connect to APs. How should you configure the auth-mode on AOS-CX switches?
A company has HPE Aruba Networking APs and AOS-CX switches, as well as HPE Aruba Networking ClearPass. The company wants CPPM to have HTTP User-
Agent strings to use in profiling devices.
What can you do to support these requirements?
You are deploying a virtual Data Collector for use with HPE Aruba Networking ClearPass Device Insight (CPDI). You have identified VLAN 101 in the data center
as the VLAN to which the Data Collector should connect to receive its IP address and connect to HPE Aruba Networking Central.
Which Data Collector virtual ports should you tell the virtual admins to connect to VLAN 101?
A company is using HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application). In the CPDI security settings, Security Analysis is On, the Data Source is ClearPass Device Insight, and Enable Posture Assessment is On. You see that a device has a Risk Score of 90.
What can you know from this information?
You want to examine the applications that a device is using and look for any changes in application usage over several different ranges. In which HPE Aruba Networking solution can you view this information in an easy-to-view format?
A company already uses HPE Aruba Networking ClearPass Policy Manager (CPPM) as the RADIUS server for authenticating wireless clients with 802.1X. Now you are setting up 802.1X on AOS-CX switches to authenticate many of those same clients on wired connections. You decide to copy CPPM's wireless 802.1X service and then edit it with a new name and enforcement policy. What else must you change for authentication to work properly?
You are setting up HPE Aruba Networking SSE to detect threats as remote users browse the internet.
What is part of this process?
A security team needs to track a device's communication patterns and identify patterns such as how many destinations the device is accessing.
Which Aruba solution can show this information at a glance?
A company has a third-party security appliance deployed in its data center. The company wants to pass all traffic for certain clients through that device before forwarding that traffic toward its ultimate destination.
Which AOS-CX switch technology fulfills this use case?
A ClearPass Policy Manager (CPPM) service includes these settings:
Role Mapping Policy:
Evaluate: Select first
Rule 1 conditions:
Authorization:AD:Groups EQUALS Managers
Authentication:TEAP-Method-1-Status EQUALS Success
Rule 1 role: manager
Rule 2 conditions:
Authentication:TEAP-Method-1-Status EQUALS Success
Rule 2 role: domain-comp
Default role: [Other]
Enforcement Policy:
Evaluate: Select first
Rule 1 conditions:
Tips Role EQUALS manager AND Tips Role EQUALS domain-comp
Rule 1 profile list: domain-manager
Rule 2 conditions:
Tips Role EQUALS manager
Rule 2 profile list: manager-only
Rule 3 conditions:
Tips Role EQUALS domain-comp
Rule 3 profile list: domain-only
Default profile: [Deny access]
A client is authenticated by the service. CPPM collects attributes indicating that the user is in the Contractors group, and the client passed both TEAP methods.
Which enforcement policy will be applied?
What role can Internet Key Exchange (IKE)/IKEv2 play in an HPE Aruba Networking client-to-site VPN?
A company wants to apply a standard configuration to all AOS-CX switch ports and have the ports dynamically adjust their configuration based on the identity of
the user or device that connects. They want to centralize configuration of the identity-based settings as much as possible.
What should you recommend?
A company has several use cases for using its AOS-CX switches' HPE Aruba Networking Network Analytics Engine (NAE).
What is one guideline to keep in mind as you plan?
HPE Aruba Networking Central displays an alert about an Infrastructure Attack that was detected. You go to the Security > RAPIDS events and see that the attack
was "Detect adhoc using Valid SSID."
What is one possible next step?
A company is using HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application). You have identified a device, which is currently
classified as one type, but you want to classify it as a custom type. You also want to classify all devices with similar attributes as this type, both already-discovered
devices and new devices discovered later.
What should you do?
You are setting up HPE Aruba Networking SSE. Which use case requires you to apply a non-default device posture in a rule?
A company uses both HPE Aruba Networking ClearPass Policy Manager (CPPM) and HPE Aruba Networking ClearPass Device Insight (CPDI).
What is one way integrating the two solutions can help the company implement Zero Trust Security?
A company has HPE Aruba Networking APs running AOS-10 that connect to AOS-CX switches. The APs will:
. Authenticate as 802.1X supplicants to HPE Aruba Networking ClearPass Policy Manager (CPPM)
. Be assigned to the "APs" role on the switches
. Have their traffic forwarded locally
What information do you need to help you determine the VLAN settings for the "APs" role?
You are proposing HPE Aruba Networking ZTNA to an organization that currently uses a third-party, IPsec-based client-to-site VPN.
What is one advantage of ZTNA that you should emphasize?
What correctly describes an HPE Aruba Networking AP's Device (TPM) certificate?
You are using Wireshark to view packets captured from HPE Aruba Networking infrastructure, but you are not sure that the packets are displaying correctly.
In which circumstance does it make sense to ensure that Wireshark has GRE enabled as one of its analyzed protocols?
A company has HPE Aruba Networking APs running AOS-10 that connect to AOS-CX switches. The APs will:
Authenticate as 802.1X supplicants to HPE Aruba Networking ClearPass Policy Manager (CPPM)
Be assigned to the "APs" role on the switches
Have their traffic forwarded locally
What information do you need to help you determine the VLAN settings for the "APs" role?
A company has HPE Aruba Networking APs running AOS-10 and managed by HPE Aruba Networking Central. The company also has AOS-CX switches. The security team wants you to capture traffic from a particular wireless client. You should capture this client’s traffic over a 15-minute time period and then send the traffic to them in a PCAP file. What should you do?
3 Months Free Update
3 Months Free Update
3 Months Free Update