We at Crack4sure are committed to giving students who are preparing for the Huawei H12-222 Exam the most current and reliable questions . To help people study, we've made some of our Huawei Certified Network Professional-R&S-IENP exam materials available for free to everyone. You can take the Free H12-222 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Which command is used to enable association between BFD and OSPF on all interfaces?
Which of the following statements regarding RT are true? (Multiple Choice)
Which are the new requirements on the enterprise network stimulated by the mobility trend? (Multiple Choice)
DHCP snooping is a security feature that can be used to defend against various attacks, including: (Multiple Choice)
Which of the following are included in the full lifecycle guest management of the Agile Controller? (Multiple Choice)
Which configuration modes are supported by VXLAN? (Multiple Choice)
Packet loss occurs only at the transmit end.
Which of the following statements regarding MPLS label space is false?
ASPF enables the firewall to support multi-channel protocols such as FTP and to define security policies for complex applications.
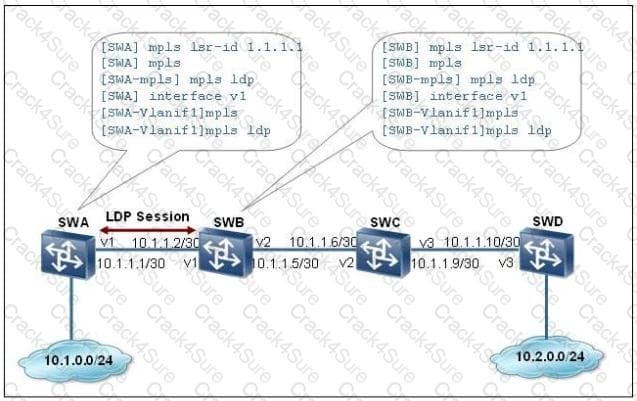
On the network shown in the following figure, a MPLS LSP is configured and a local LDP session is established between SWA and SWB. Which of the following statements is true?
Flow mirroring is divided into bcal flow mirroring and remote flow mirroring.
Which of the following is not the application scenario of the guest access management function of the Agile Controller?
MPLS performs different actions on labels. What is the meaning of the pop action?
Which queue technology is used to implement the Best-Effort Service model?
How is traffic classification classified based on reference different information of rules? (Multiple Choice)
IP packets are marked with the ToS field for QoS, and the first 6 bits of the ToS field mark the DSCP priority.
Which remote alarm notification modes are supported by eSight? (Multiple Choice)
MPLS supports multi-layer labels and connection-oriented on the forwarding plane, therefore it is widely used. So Which of the following is not the cause for MPLS deployment?
The WRED drop profile defines the following parameters for AF21 traffic: the lower drop threshold is 35, the upper drop threshold is 40, and the maximum drop probability is 50%. Which of the following statements regarding the processing result of AF21 traffic are false? (Multiple Choice)
Among the BE service model, IntServ model, and DiffServ model, only the IntServ model and DiffServ model can provide multi-service QoS guarantee. During network construction, the network edge should use the IntServ model and the network core should use the DiffServ model.
Which of the following items is not the disadvantage of the traditional congestion avoidance mechanism (tail drop)?
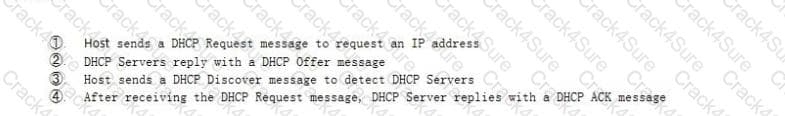
Which of the following is correct procedure for a DHCP client to apply for an IP address from a DHCP server?
MPLS is a label forwarding technology, Which of the following MPLS statements is false?
MPLS VPN is used to solve some limitations of traditional VPN technology. Which are the major limitation that MPLS VPN solves?
MPLS supports forwarding equivalence class (FEC). Which of the following cannot be used as a FEC allocation standard?
The TTL field encapsulated to the MPLS label header can prevent infinite loops of MPLS packets. Which of the following statements regarding the TTL field are true? (Multiple Choice)
Which IP precedence value represents the critical service traffic?
How is NFV defined?
The QoS service model includes? (Multiple Choice)
Which of the following statements regarding the firewall interzone security policy is true?
What are the advantages of NFV? (Multiple Choice)
Which mechanism can be used with VRRP to monitor the uplink connectivity? (Multiple Choice)
BFD uses TCP connections and the destination port number is 3784.
Which of the following statements regarding forwarding equivalence class (FEC) in MPLS are false?
(Multiple Choice)
Which are the layers of SDN network architecture? (Multiple Choice)
In peer-to-peer VPN model, which of the following devices is directly connected to a client and is responsible for connecting VPN services to the carrier network?
Which of the following statements regarding the VRRP backup are true? (Multiple Choice)
Which of the following statements regarding the differences between GTS, LR, and CAR is false?