We at Crack4sure are committed to giving students who are preparing for the Huawei H12-711_V3.0 Exam the most current and reliable questions . To help people study, we've made some of our HCIA-Security V3.0 exam materials available for free to everyone. You can take the Free H12-711_V3.0 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
SIPprotocol usageSDPmessage to establish a session,SDPThe message contains a remote address or a multicast address
Common scanning attacks include: port scanning tools, vulnerability scanning tools, application scanning tools and database scanning tools, etc.
Which of the following areHRP(Huawei Redundancy Protocol) protocol can back up state information? (multiple choice)
aboutVGMPIn a description of group management, which of the following is false?
Data analysis technology is to find and match keywords or key phrases in the acquired data stream or information stream, and analyze the correlation of time. Which of the following is not an evidence analysis technique?
Which of the following does not belong toP2DRin the modelDetectionThe method used in the link?
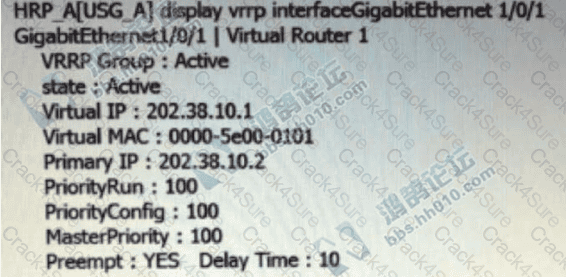
existVRRP(Virtual Router Redundancy Protocol) group, the primary firewall regularly sends notification messages to the backup firewall, and the backup firewall is only responsible for monitoring notification messages and will not respond
Multiple different ( ) cannot be added to the same interface on the firewall at the same time (fill in the blank)
Digital envelope technology means that the sender uses the receiver's public key to encrypt the data, and then sends the ciphertext to the receiver ( )[Multiple choice]*
Which of the following angles should be considered in the information security stage to consider the security of information?
Questionnaire design principles do not include which of the following?
aboutSSL VPNdescription, which of the following is correct?
the following aboutVGMPWhich protocol description is wrong?
aboutVPN, which of the following statements is false?
The matching principle of the security policy is: first search for the manually configured interzone security policy, and if no match is found, the data packet will be discarded directly.
aboutAHandESPSecurity protocol, which of the following options is true? (multiple choice)
The repair of anti-virus software only needs to repair some system files that were accidentally deleted when scanning and killing viruses to prevent the system from crashing
About firewall gateways forHTTPWhich of the following statements is false about the protocol's antivirus response?
Which of the following is not a key technology of antivirus software?
On the surface, threats such as viruses, loopholes, and Trojan horses are the causes of information security incidents, but at the root, information security incidents are also closely related to people and the information system itself.
againstIPspoofing attack (IP Spoofing), which of the following is an error?
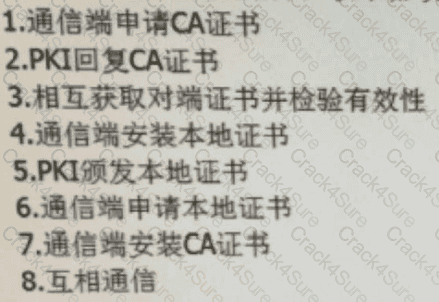
aboutPKIOrdering of work processes, which of the following is correct?
DDosWhich of the following attack types is an attack?
Which of the following options are key elements of information security precautions? (multiple choice)
deployIPSec VPNIn tunnel mode, useAHprotocol for packet encapsulation. NewIPIn the header field of the packet, which of the following parameters does not need to be checked for data integrity?
TCSECWhich of the following protection levels are included in the standard? (multiple choice)
The method of collecting information by port scanning using scanning tools belongs to the means of ( ) analysis. (fill in the blank)
Execute the command on the firewall and display the above information. Which of the following descriptions is correct? (multiple choice)
The direction of the traffic can be seen in the ___ of the firewall.[fill in the blank]*
According to the management specification, regularly check the network security system and equipment, upgrade the patch, and organize the network security emergency response drill. The above actions belong toMPDRRWhat are the elements of the network security model?
Which of the following options areIPSec VPNSupported encapsulation modes? (multiple choice)
Applying for special funds for emergency response and purchasing emergency response software and hardware equipment belong to the work content of which stage of the network's complete emergency response?
Which of the following is network address port translation (NAPT) and only translate network addresses (No-PAT) difference?
Regarding the NAT policy processing flow, which of the following options are correct? ( )*
Which of the following statements about the patch is incorrect?
Personal information leakage is the destruction of the ______ characteristics of information.[fill in the blank]*
When configuring security policies, you can control traffic based on the user's______.[fill in the blank]*
Equipment sabotage attacks are generally not easy to cause information leakage, but usually cause interruption of network communication services.
Which of the following options belong to international organizations related to the standardization of information security? (multiple choice)
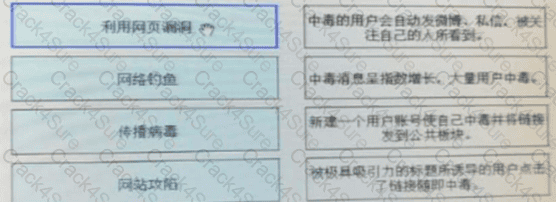
Please match the whole worm attack process and attack description.[fill in the blank]*
at HuaweiUSGOn the series firewalls, the default security policy does not support modification.
The reason why NAPT can realize one-to-many address translation is that the ______ is also translated when the address is translated, so multiple private addresses can share the same public address.[fill in the blank]*
Which of the following is true about firewall security policies?
The interface on the firewall cannot forward traffic until it is added ( ). (fill in the blank)
Which of the following options is not a passive means of obtaining information? ( )[Multiple choice]*
The initial priority of the USG9500VGMP group is related to which of the following factors ( )? *
During the process of establishing IPSec VPN between peers FW_A and FW_B, two types of security associations need to be established in two stages. In the first stage, _____ is established to verify the identity of the peers.[fill in the blank]*
An engineer needs to back up the firewall configuration. Now he wants to use a command to view all the current configurations of the firewall. May I ask the command he uses is ____[fill in the blank]*
Which of the following security measures does the monitor correspond to?
Which of the following does not belong to the block encryption algorithm in the symmetric encryption algorithm?
The CA certificate is the certificate of the CA itself. If there is no multi-level CA in the PKI system, the original certificate of the CA is a self-signed certificate; if there are multiple levels of CA, it will form a CA hierarchy. The top CA is the root CA, which has A CA' self-signed certificate.
Which of the following SSLVPN functions can and can only access all TCP resources?
In USG6000E, the initial priority of VGMP is ( ) (fill in the blank)
Information security prevention technologies include: data encryption, identity authentication, intrusion prevention and anti-virus, etc.
When IPSec VPN uses tunnel mode to encapsulate packets, which of the following is not within the encryption scope of the ESP security protocol? ( )[Multiple choice]*
If we do not want to generate a reverse Server Mapi entry when configuring NAT Server, we need to add a parameter when configuring NATServerE. This parameter is ( ) (fill in the blank)
The company administrator uses the ping command to test the connectivity of the network. If he needs to specify the source address of the ehco-request message, what are the additional parameters he needs?
In the authentication policy of the firewall, _____ allows the user to not need to enter the user name and password, but can obtain the corresponding relationship between the user and the IP, so as to carry out policy management based on the user[fill in the blank]*
To configure a NAT policy in command line mode, you need to use the .command ( ) in the system view to enter the NAT policy configuration view. (all lowercase) (fill in the blank)
Please order the following steps in the PKI life cycle correctly, 1. Issued, 2. storage, 3. Update, 4. verify[fill in the blank]*
The firewall imports users locally, and supports importing user information from _____ format files and database dbm files to the local device.[fill in the blank]*
Which of the following descriptions about dual-system hot backup is wrong? ( )[Multiple choice]*
Which of the following options isL2TPThe port number used by the packet?
Firewall usagehrp standby config enableAfter the standby device configuration function is enabled by the command, all information that can be backed up can be configured directly on the standby device, and the configuration on the standby device can be synchronized to the active device.
Which of the following information is encrypted during the use of digital envelopes? (multiple choice)
The administrator wishes to clear the current session table. Which of the following commands is correct? ( )[Multiple choice]*
Gratuitous ARP can be used to detect whether the ______ address conflicts, and it can also refresh the switch MAC address table.[fill in the blank]*