We at Crack4sure are committed to giving students who are preparing for the Huawei H12-711_V4.0 Exam the most current and reliable questions . To help people study, we've made some of our HCIA-Security V4.0 Exam exam materials available for free to everyone. You can take the Free H12-711_V4.0 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Please match the following information security risks to information security incidents one by one.[fill in the blank]*
physical security risk Enterprise server permissions are loosely set
Information Security Management Risk Infected Panda Burning Incense
Information Access Risk Fire destroyed equipment in computer room
application risk Talk to people about leaking company secrets
Which of the following statements are incorrect about the differences between routers and Layer 2 switches?
The traffic direction of a firewall is based on the zone priority. The _____ direction refers to the direction from a low-priority zone to a high-priority zone. Capitalize the first letter.
What are the correct entries in the following description of firewall security zones?
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
In the automatic backup mode of hot standby on the second machine, which of the following sessions is backed up?
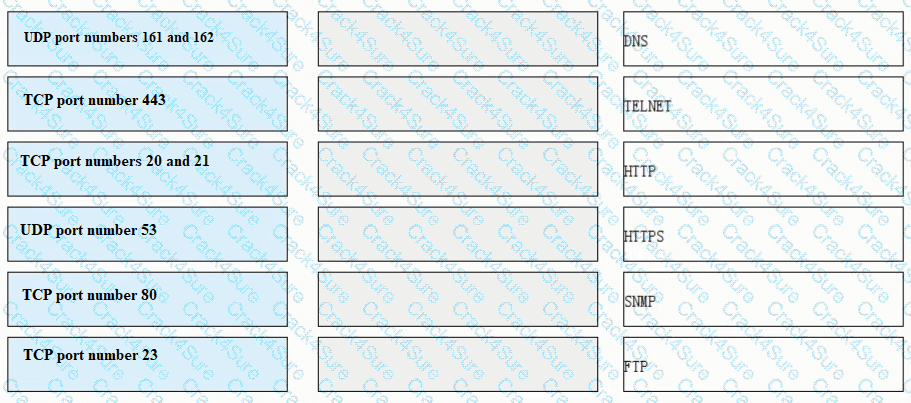
Match each of the following application layer service protocols with the correct transport layer protocols and port numbers.
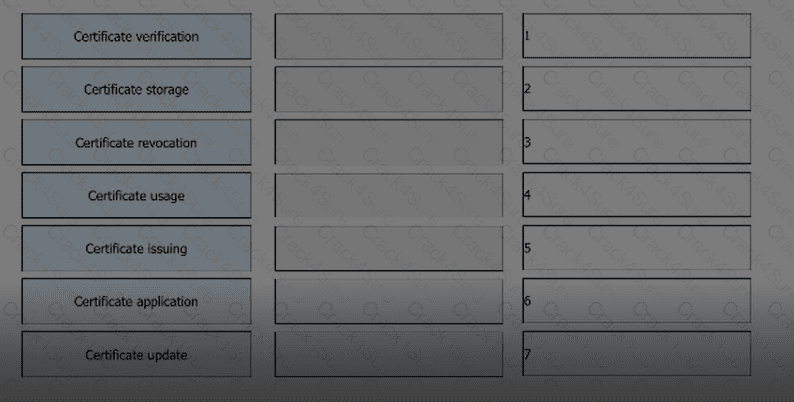
Arrange the following processes in the correct order based on the PKI lifecycle.
Which of the following protocols is a multichannel protocol?
The following description of the construction of a digital certificate, which item is wrong
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
In hot standby networking, the heartbeat interfaces of the two firewalls must be directly connected.
When using passive mode to establish an FTP connection, the control channel uses port 20 and the data channel uses port 21.
Which of the following protocols are transport layer protocols?
Which of the following functions help implement IPsec secure transmission of user service data on the Internet by means of encryption and authentication?
Which of the following descriptions of server authentication is correct?
Which of the following is not the default security zone of the firewall
The trigger authentication method for firewall access user authentication does not include which of the following?
Information security aims to protect data in hardware, software, and their systems on information networks to prevent data damage, tampering, or breach due to occasional or malicious reasons and ensure proper system running and non-stop information services.
HTTPS introduces the TLS layer based on HTTP to provide identity authentication, encryption, and integrity check for data transmission.
Which of the following attack methods is to construct special SQL statements and submit sensitive information to exploit program vulnerabilities
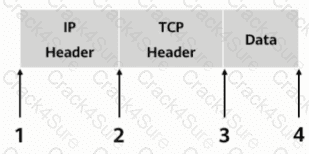
As shown, in transmission mode, which of the following locations should the AH header be inserted in?
Which of the following attacks can be detected through intrusion prevention?
DES is a stream encryption algorithm, because the cipher capacity is only 56 bits, so it is not enough to deal with the weakness of insufficient security, and later 3DES was proposed.
We should choose the encryption algorithm according to our own use characteristics. When we need to encrypt a large amount of data, it is recommended to use the ____ encryption algorithm to improve the encryption and decryption speed.[fill in the blank]*
When forwarding a TCP, UDP, or ICMP packet, the firewall needs to query the session table in order to determine the connection to which the packet belongs and take corresponding measures.
The following description of IDS, which items are correct
The IDS cannot be linked to the firewall.
Which of the following are antivirus response actions of the firewall?
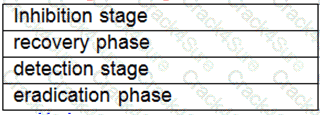
Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution.[fill in the blank]*
Which of the following is not an advantage of symmetric encryption algorithms?
_____ Authentication is to configure user information (including local user's user name, password and various attributes) on the network access server. The advantage is that it is fast.[fill in the blank]*
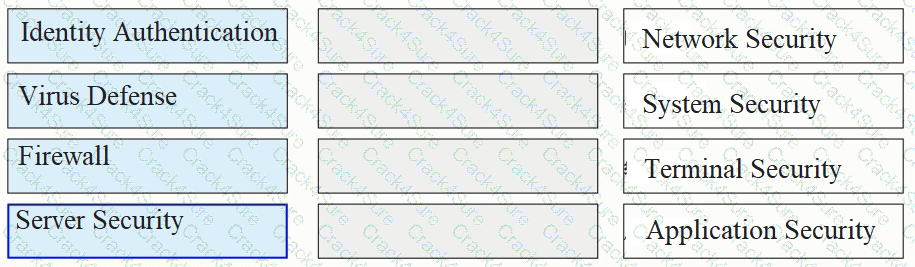
Please classify the following security defenses into the correct classification.
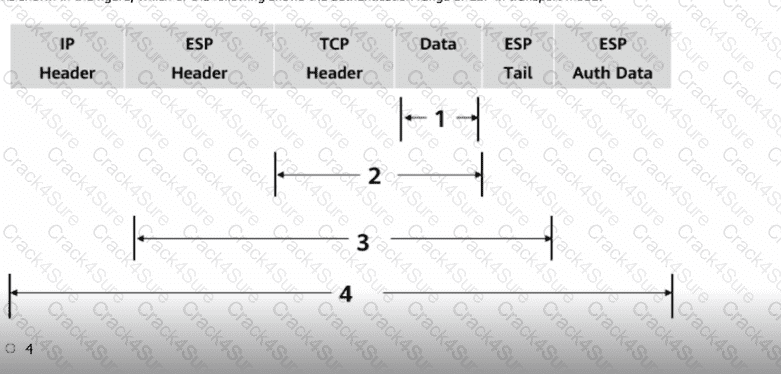
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?
What is correct in the following description of Security Alliance in IPSec?
There are two ways to set up an IPSec SA
Which of the following packets is controlled by a firewall's security policy by default?
The following description of investigation and evidence collection, which one is correct
In the authentication policy of the firewall, _____ allows the user to not need to enter the user name and password, but can obtain the corresponding relationship between the user and the IP, so as to carry out policy management based on the user[fill in the blank]*
Which of the following statements are correct about the PKI system structure?
WAF can accurately control and manage users' online behavior and user traffic.
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?
3 Months Free Update
3 Months Free Update
3 Months Free Update