We at Crack4sure are committed to giving students who are preparing for the Huawei H12-721 Exam the most current and reliable questions . To help people study, we've made some of our Huawei Certified ICT Professional - Constructing Infrastructure of Security Network exam materials available for free to everyone. You can take the Free H12-721 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
The principle of HTTPS Flood source authentication defense is that the Anti-DDoS device replaces the SSL server with the client to complete the TCP three-way handshake. If the TCP three-way handshake is complete, the HTTPS flood source authentication check is successful.
The management control information and service information of the out-of-band management interface are sent on the same channel.
The Tracert packet attack is an ICMP timeout packet returned by the attacker when the TTL is ____, and the ICMP port unreachable packet returned when the destination address is reached to find the path through which the packet arrives at the destination. Spying on the structure of the network
Virtual firewall virtualizes multiple logical firewalls on a physical firewall device and implements multiple instances?
IPSec VPN uses digital certificates for authentication. It has the following steps: 1. verify the certificate signature; 2. find the certificate serial number in the CRL; 3. share the entity certificate between the two devices; 4. verify the validity period of the certificate; . Establish a VPN tunnel. Which of the following is correct?
By default, GigabitEthernet0/0/0 can be used as an out-of-band management interface in the USG2200 series.
Regarding the virtual gateway type exclusive and shared type, what are the following statements correct?
When using the SSL VPN client to start the network extension, the prompt "Connection gateway failed", what are the possible reasons for the failure?
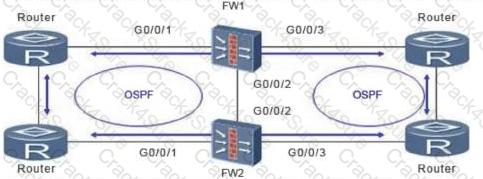
When the firewall works in the dual-system hot backup load balancing environment, if the upstream and downstream routers are working in the routing mode, you need to adjust the OSPF cost based on HRP.
Which of the following methods is used to switch between active and standby links in the IPSec backup and backup system?
Avoid DHCP server spoofing attacks. DHCP snooping is usually enabled. What is the correct statement?
Virtual firewall technology can achieve overlapping IP addresses.
According to the dual-system hot backup network diagram, what are the correct descriptions in the following dual-system hot backup preemption function?

In IPSec VPN, which one is incorrect about the difference between the barbaric mode and the main mode?
Which of the following is correct about the configuration of the firewall interface bound to the VPN instance?
The following are traffic-type attacks.
Which of the following technologies can enhance the security of mobile users accessing the company's intranet VPN solution?
Two USG firewalls establish an IPSec VPN through the Site to Site mode. When viewing the status of a USG A, the following is displayed: display ipsec statistics the security packet statistics: input/output security paskets: 40 input/output security bytes: 400/0 input /output dropped security packets: 0/0 By status information, what information can be obtained correctly?
The firewall device defends against the SYN Flood attack by using the technology of source legality verification. The device receives the SYN packet and sends the SYN-ACK probe packet to the source IP address host in the SYN packet. If the host exists, it will Which message is sent?
The IPSec establishment of a device is unsuccessful. The debug print information is as follows. What are the possible causes of the fault?
? %%01IKE/4/WARING(1):phase2:proposal mismatch,please check ipsec proposal configuration 0 34476900 %%01IKE/7/DEBUG(d) dropped message from 3.3.3.1 due to notification type NO_PROPOSAL_CHOSEN
The default interval for sending VGMP hello packets is 1 second. That is, when the hello packet sent by the peer is not received within the range of three hello packets, the peer is considered to be faulty. Master status.
After the NAT server is configured (no-reverse parameter is added), the firewall automatically generates static Server-Map entries. The first packet matches the Server-Map entry and does not match the session table.
Which of the following protocols does the USG firewall hot standby not include?
USG A and USG B are configured with a static BFD session. The following is true about the process of establishing and tearing down a BFD session.
112. The ESP only verifies the IP payload and can perform NAT traversal, but the ESP encrypts the Layer 4 port information and causes the PAT function to be unusable. This problem can be solved by using the IPSec transparent NAT function, which encapsulates the ESP packet in the UDP header and comes with the necessary port information to make the PAT work normally.
The DHCP snooping function needs to maintain the binding table. What are the contents of the binding table?
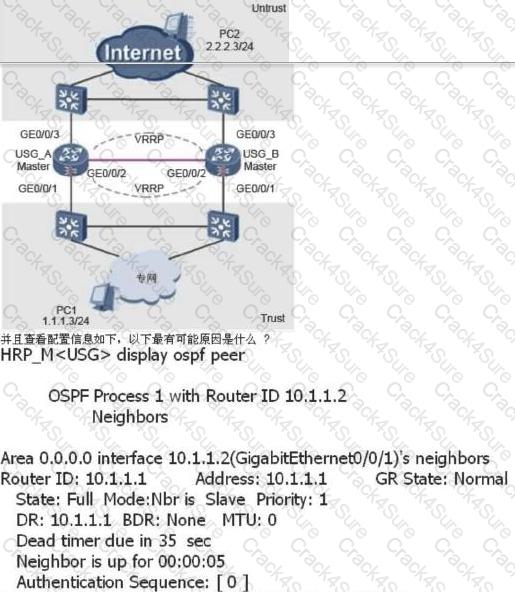
In the active/standby mode of the USG dual-system hot standby, the service interface works at Layer 3, and the upstream and downstream routers are connected to the router. The administrator can view: USG_A status is HRP_M[USG_A], USG_B status is HRP_S[USG_B], current 15000+ session Table, every time a switchover occurs, all traffic is interrupted for a period of time, and seamless switching is impossible.
The topology of the BFD-bound static route is as follows: The administrator has configured the following on firewall A: [USG9000_A] bfd [USG9000_A-bfd] quit [USG9000_A] bfd aa bind peer-ip 1.1.1.2 [USG9000_A- Bfd session-aa] discriminator local 10 [USG9000_A-bfd session-aa] discriminator remote 20 Which of the following configurations can be added to the firewall to implement BFD-bound static routes?

When there are a large number of BFD sessions in a system, what mode can be used to prevent BFD detection when the cost of sending BFD control packets periodically affects the normal operation of the system?
Which of the following security services can a secure multi-instance provide for a virtual firewall?
As shown in the figure, the firewall is dual-system hot standby. In this networking environment, all service interfaces of the firewall work in routing mode, and OSPF is configured on the upper and lower routers. Assume that the convergence time of OSPF is 30s after the fault is rectified. What is the best configuration for HRP preemption management?
A certain network is as follows: LAN----G0/0/0 USG G0/0/1 ----Server. After the administrator analyzes the Attarcker on the LAN network connected to G0/0/0, if you want to prevent ARP flood attacks, limit the ARP traffic to 100 packets/minute. Which is the correct configuration?
In Huawei's abnormal traffic cleaning solution, the characteristics of the straight-line deployment mode and the bypass deployment mode are correct.
Comparing URPF strict mode and loose mode, which of the following statements is incorrect?
What are the following attacks that are malformed?
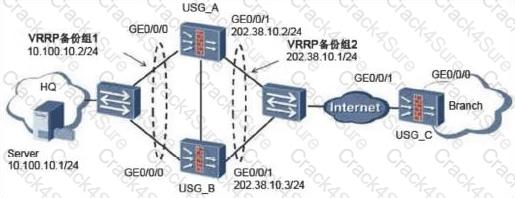
87. The SSL VPN scenario under dual-system hot standby is shown in the following figure. The administrator has enabled the SSL network extension function. The following is about the configuration of the SSL VPN function.
The ip-link sends a probe packet to the specified IP address. By default, after 3 probe failures, the link to this IP address is considered faulty.
In the IDC room, a USG firewall can be used to divide into several virtual firewalls, and then the root firewall administrator generates a virtual firewall administrator to manage each virtual firewall.
A data flow has established a session in the firewall. If the packet filtering policy corresponding to the data is modified, how should the firewall execute?
Huawei's abnormal traffic cleaning solution must deploy an independent testing center.
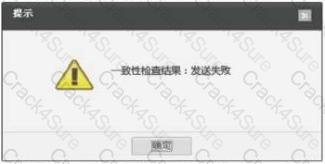
On the web configuration page, choose System --> High Reliability --> Hot Standby and click Check for HRP Configuration Consistency. Button. The following window pops up. Which of the following configurations can solve the problem (assuming the heartbeat is added to the DMZ area)?
Which is incorrect about IPSec NAT Traversal?
Which attack method is CC attack?
Using the virtual firewall technology, users on the two VPNs can log in to their private VPNs through the Root VFW on the public network to directly access private network resources. What are the following statements about the characteristics of the VPN multi-instance service provided by the firewall?
What are the correct statements about link-group below?
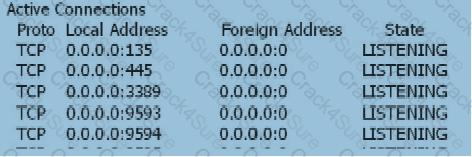
When the user's SSL VPN has been successfully authenticated, the user cannot access the Web-link resource. On the Web server, view the information as follows: netstat -anp tcp With the following information, which of the following statements is correct?
When the ip-link link health check is performed, if it is unable to receive the message several times in the absence of the link, it will be considered as a link failure.
Which of the following is the correct description of the SMURF attack?
The main function of URPF is to prevent network attack behavior based on destination address spoofing.
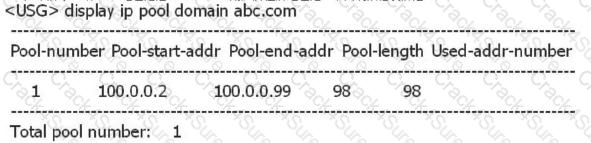
As shown below, the domain abc address pool is the address pool where the L2TP VPN user is located. What is wrong with the following statement?
Connecting the internal network interface address from the firewall By pinging the internal network address of the peer, the IPSec tunnel can be successfully triggered. The internal PC cannot trigger the tunnel establishment. What are the possible reasons?
The USG_B status is HRP_M[USG_A], and the USG_B status is HRP_S[USG_B]. The status of the USG_A is HRP_M[USG_A]. However, all traffic did not pass USG_A completely, and half of the traffic also passed USG_B.
What are the possible reasons why the firewall 2 IPSec VPN cannot be established successfully?
Which of the following is incorrect about IKE V1 and IKE V2?
In the IPSec VPN, the digital certificate is used for identity authentication. If the IKE main mode is used for negotiation, the certificate verification is completed in message 5 and message 6.
The classification of cyber-attacks includes traffic-based attacks, scanning and snooping attacks, malformed packet attacks, and special packet attacks.
What are the three elements of an abnormal flow cleaning solution?
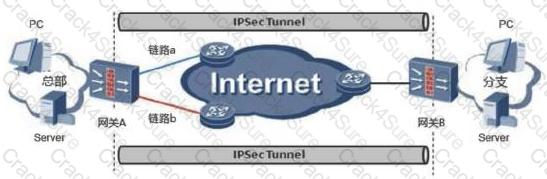
In the IPSec active/standby link backup application scenario, gateway B uses IPSec tunneling technology and gateway A to establish an IPSec VPN.
After a new security instance is created on the firewall, there is no security zone on the firewall, and the administrator needs to plan the configuration.
The static fingerprint filtering function is to defend the attack traffic by configuring a static fingerprint to process the packets that hit the fingerprint. Generally, the anti-DDoS device capture function can be used to input fingerprint information to static fingerprint filtering.
3 Months Free Update
3 Months Free Update
3 Months Free Update