We at Crack4sure are committed to giving students who are preparing for the Huawei H12-724 Exam the most current and reliable questions . To help people study, we've made some of our HCIP-Security (Fast track) V1.0 exam materials available for free to everyone. You can take the Free H12-724 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Regarding the trigger mechanism of 802.1X authentication, which of the following descriptions is correct? (multiple choice)
The following commands are configured on the Huawei firewall:
[USG] firewall defend ip-fragment enable
Which of the following situations will be recorded as an offensive behavior? (multiple choice)
In a WLAN network, intra-group isolation and inter-group isolation can be used at the same time.
When the -aa command is used on the access control device to test the connectivity with the Radius server, the running result shows success, but the user cannot Normal access, the possible reason does not include which of the following options?
Which of the following is the default port number of Portal authentication service?
Traditional access control policy passed ACL or VLAN Can not be achieved with IP Address decoupling, in IP The maintenance workload is heavy when the address changes. And because the agile network introduces the concept of security group, it can achieve the same IP Address decoupling.
Regarding computer viruses, which of the following options is correct?
Which is correct about the following Policy Center troubleshooting process?
Regarding the 3 abnormal situations of the file type recognition result, which of the following option descriptions is wrong?
Using Agile Controller-Campus for visitor management, users can obtain the account they applied for in a variety of ways, but which of the following are not included A way?
Which of the following options is not a cyber security threat caused by weak personal security awareness?
Which of the following iterations is correct for the description of the management center?
In a WLAN network, when the AP is in monitoring mode, what kind of packets does the AP use to determine the device type?
When you suspect that the company's network has been attacked by hackers, you have carried out a technical investigation. Which of the following options does not belong to the behavior that occurred in the early stage of the attack?
Mobile smartphone, tablet PC users through Any Office Client and AE Establish IPSec Encrypted tunnel, After passing the certification and compliance check, visit the enterprise business.
Regarding scanning and snooping attacks, which of the following descriptions is wrong?
Agile Controller-Campus The system architecture belongs to C/S Architecture.
Regarding the processing flow of file filtering, which of the following statements is wrong?
Anti-DDoS defense system includes: management center, detection center and cleaning center.
Viruses can damage computer systems. v Change and damage business data: spyware collects, uses, and disperses sensitive information of corporate employees.
These malicious pastoral software seriously disturb the normal business of the enterprise. Desktop anti-disease software can solve the problem of central virus and indirect software from the overall situation.
Regarding the file filtering technology in the USG6000 product, which of the following options is wrong?
Which of the following are typical intrusions? "Multiple choice)
In Portal authentication, which of the following parameters must be configured on the switch? (Multiple choice)
Regarding the sequence of the mail transmission process, which of the following is correct?
1. The sender PC sends the mail to the designated SMTP Server.
2. The sender SMTP Server encapsulates the mail information in an SMTP message and sends it to the receiver SMTP Server according to the destination address of the mail
3. The sender SMTP Server encapsulates the mail information in an SMTP message according to the destination address of the mail and sends it to the receiver POP3/MAP Senver
4. The recipient sends an email.
There are several steps in a stored XSS attack
?The attacker hijacks the user session
?The attacker submits an issue containing known JavaScript
?User login
?The user requests the attacker's question 5
?The server responds to the attacker’s JavaScript
? The user's browser sends a session token to the attacker
?The attacker's JavaScript is executed in the user's browser
For the ordering of these steps, which of the following options is correct?
Agile Controller-Campus All components are supported Windows System and Linux system.
In the Policy Center strategy configuration, how many violations rating of definition are there?
The configuration command to enable the attack prevention function is as follows; n
[FW] anti-ddos syn-flood source-detect
[FW] anti-ddos udp-flood dynamic-fingerprint-learn
[FW] anti-ddos udp-frag-flood dynamic fingerprint-learn
[FW] anti-ddos http-flood defend alert-rate 2000
[Fwj anti-ddos htp-flood source-detect mode basic
Which of the following options is correct for the description of the attack prevention configuration? (multiple choice)
Free mobility is a special access control method, according to the user’s access location, access time, access method and terminal authorization instructions. Set permissions, as long as the user’s access conditions remain unchanged, the permissions and network experience after accessing the network--To q
Regarding WLAN, which of the following descriptions is correct?
Abnormal detection is to establish the normal behavior characteristic profile of the system subject through the analysis of the audit data of the system: check if the audit data in the system
If there is a big discrepancy with the normal behavior characteristics of the established subject, it is considered an intrusion. Nasu must be used as the system subject? (multiple choice)
Which of the following options is correct for the description of the Anti DDoS system configuration?
Which of the following behaviors is a false positive of the intrusion detection system?
Terminal security access technology does not include which of the following options?
In WPA2, because of the more secure encryption technology-TKIP/MIC, WPA2 is more secure than WPA.
Visitor management can authorize visitors based on their account number, time, location, terminal type, access method, etc., and can also push personalized pages to visitors based on time, location, and terminal type.
For special message attacks, which of the following option descriptions is correct?
A Special control packet attack is a potential attack and does not have direct destructive behavior
B. The attacker probes the network structure by sending special control messages to launch a real attack.
C. Special control message attacks do not have the ability to detect the network structure. Only scanning attacks can detect the network.
D. Special control message items can only use ICMP to construct attack messages.
In the construction of information security, the intrusion detection system plays the role of a monitor. It monitors the flow of key nodes in the information system.
In-depth analysis to discover security incidents that are occurring. Which of the following are its characteristics?. c0O
Visitors can access the network through their registered account. Which of the following is not an account approval method?
The AD/LDAP account can be synchronized to the Agile Controller-Campus or not to the Agile Controller-Campus. Synchronize.
The Agile Controller-Campus can only be authorized by user group. If it is not synchronized to the Agile Controller-Campus, it can be fine-tuned based on the account.
Authorization
The results of the RBL black and white list query on the firewall are as follows:
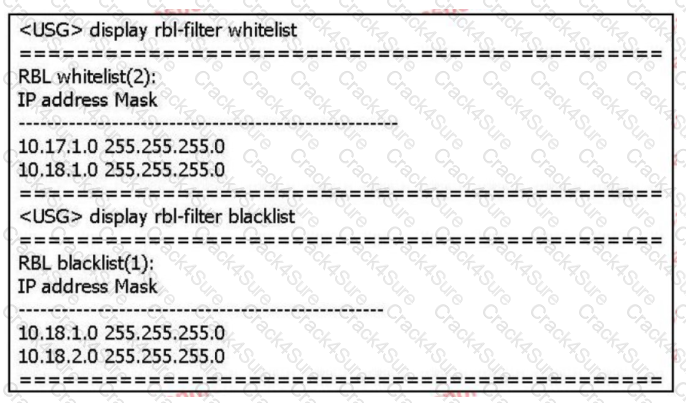
Based on the above information only, which of the following statements is correct? (multiple choice)
An enterprise has a large number of mobile office employees, and a mobile office system needs to be deployed to manage the employees. The number of employees in this enterprise exceeds 2000 People, and the employees’ working areas are distributed all over the country. In order to facilitate management, which deployment method is adopted?
Which of the following options is right PKI The sequence description of the work process is correct?
1. PKI Entity direction CA ask CA Certificate. .
2. PKI Entity received CA After the certificate, install CA Certificate.
3. CA receive PKI Entity CA When requesting a certificate, add your own CA Certificate reply to PKI entity.
4. PKI Entity direction CA Send a certificate registration request message.
5. PKI When the entities communicate with each other, they need to obtain and install the local certificate of the opposite entity.
6. PKI Entity received CA The certificate information sent.
7. PKI After the entity installs the local certificate of the opposite entity,Verify the validity of the local certificate of the peer entity. When the certificate is valid,PC The public key of the certificate is used for encrypted communication between entities.
8. CA receive PKI The entity's certificate registration request message.
Web Standards that come with the client and operating system 8021 The instrument client only has the function of identity authentication: It does not support the execution of inspection strategies and monitoring strategies. Any Office The client supports all inspection strategies and monitoring strategies.
Windows in environment,Agile Controller-Campus After the installation is successful, how to manually start the management center(MC)? (Multiple choice)
Use on the terminal Portal The authentication is connected to the network, but you cannot jump to the authentication page. The possible reason does not include which of the following options?
Server Fault information collection tool Server Collector, which of the following does collected information items not include?
Which of the following technology, administrators can according to business requirements, to scale to achieve load sharing of business flow?
About the software SACG And hardware SACG Description, which of the following is correct?
Deploying on Windows platform, using SQL Server database About the HA function of Agile Cotoller-Campus, which of the following descriptions Is it correct? (multiple choice)
Regarding the role of each role in the Portal authentication framework, which of the following descriptions are correct? (multiple choice)
Which of the following options does not belong to the basic DDoS attack prevention configuration process?
What are the typical technologies of anti-virus engines (multiple choice)
The visitor management process includes page customization, account application, user authentication, audit, and logout. After the user successfully applies for an account, he needs to change.
When the account is distributed to users, what stage does the distribution of the account belong to?
In enterprises where terminal host access control management is relatively strict, administrators hope to bind terminal hosts and accounts to prevent terminal users from accessing the controlled network from unauthorized terminal hosts at will. Regarding the description of binding the terminal host and account, which of the following is correct?
If the processing strategy for SMTP virus files is set to alert, which of the following options is correct?
Which of the following options are relevant to MAC Certification and MAC The description of bypass authentication is correct? (Multiple choice)
Which of the following features does Huawei NIP intrusion prevention equipment support? (multiple choice)
For hardware SACC Access control, if the terminal does not pass the authentication, it can access the resources of the post-authentication domain. This phenomenon may be caused by the following reasons? (Multiple choice)
Regarding the description of file reputation technology in anti-virus engines, which of the following options is correct?
Sort all services according to user group and account: By the end IP The address range is time-sharing, if it is a user group, a small terminal with an account IP Address range allocation for the same business(Chen Gongji outside business) I The business assigned to the one with the highest priority will take effect.
Which of the following is correct regarding the order of priority?
For full encryption registered mobile storage devices must be formatted to normal use in not installed NAC client terminal host.
Guest management is Agile Controller-Campus Important function of, regarding visitor management, which of the following statements are correct? (Multiple choice)
In the penetration stage of an APT attack, which of the following attack behaviors will the attacker generally have?
A network adopts 802. 1X To authenticate access users, the access control equipment is deployed at the convergence layer, and after the deployment is completed, it is used on the access control equipment t-aa The command test is successful, but the user cannot access the network. The failure may be caused by the following reasons? (Multiple choice)
Deployed by an enterprise network managerAgile Controller-Campus withSACG Later;Identity authentication is successful but cannot access the post-authentication domain, This phenomenon may be caused by any reason? (Multiple choice)
The processing flow of IPS has the following steps;
1. Reorganize application data
2. Match the signature
3. Message processing
4. Protocol identification
Which of the following is the correct order of the processing flow?
The anti-tampering technology of Huawei WAF products is based on the cache module. Suppose that when user A visits website B, website B has page tampering.
Signs: The workflow for the WAF tamper-proof module has the following steps:.
? WAF uses the pages in the cache to return to the client;
?WAF compares the watermark of the server page content with the page content in the cache
?Store the content of the page in the cache after learning
? When the user accesses the Web page, the WAF obtains the page content of the server
?WAF starts the learning mode to learn the page content of the user's visit to the website;
For the ordering of these steps, which of the following options is correct?
Regarding the file source set in the software management, which of the following descriptions is correct?
Location refers to the end user's use AC-Campus The terminal environment when accessing the controlled network office. Which of the following options is correct for the description of the place?
Which of the following technologies can achieve content security? (multiple choice)
The multi-level defense system is mainly reflected in the network level and the system level. Which of the following options are used for security defense at the network level? (Multiple choice)
How to check whether the SM and SC silverware start normally after installing the Agile Controller-Campus) (multiple delivery)
Huawei NIP6000 products have zero-setting network parameters and plug-and-play functions, because the interfaces and interface pairs only work on layer 2 without
Set the IP address.
A True
B. False
UDP is a connectionless protocol. UDP Flood attacks that change sources and ports will cause performance degradation of network devices that rely on session forwarding.
Even the session table is exhausted, causing the network to be paralyzed. Which of the following options is not a preventive measure for UDP Flood attacks?
After the user deploys the firewall anti-virus strategy, there is no need to deploy anti-virus software
When you suspect that the company's network has been attacked by hackers, you have carried out a technical investigation. Which of the following options does not belong to the behavior that occurred in the early stage of the attack?
When a data file hits the whitelist of the firewall's anti-virus module, the firewall will no longer perform virus detection on the file.
A network adopts Portal Authentication, the user finds the pushed Web No username entered on the page/The place of the password. This failure may Which of the following causes?
Which of the following files can the sandbox detect? (multiple choice)
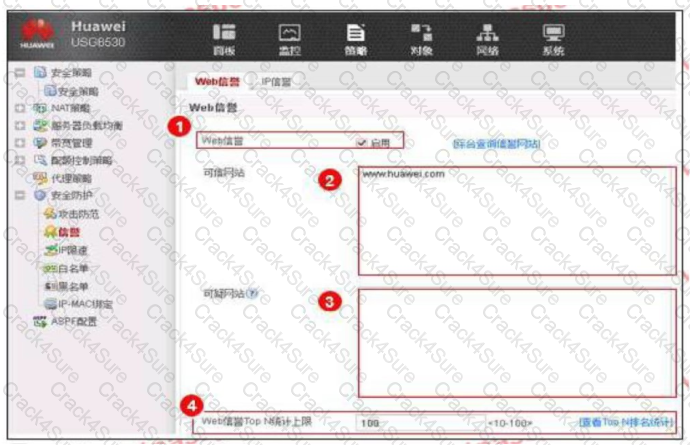
An enterprise administrator configures the Web reputation system as shown in the figure. Regarding the configuration, which of the following statements is correct?
In the campus network, employees can use 802.1X, Portal,MAC Address or SACG Way to access. Use different access methods according to different needs to achieve the purpose of user access control.
When configuring the terminal visits, we put some equipment configured exception equipment ,which of the following statements are true about the exception equipment?
Tianyu Nei answered the role of safety filtering technology, which of the following is still correct? (multiple choice)
In the Agile Controller-Campus solution, which device is usually used as the hardware SACG?
Which of the following options is about SACG The description of the online process is wrong?
BY00 The products and textiles provided by the history solution program cover the entire terminal network\Application and management and other fields/include: Serialization BC Equipment, paperless network system network access support, VPN Gateway, terminal security customer ladder software, authentication system, mobile device management(MDN),move eSpace UC.
The administrator of a certain enterprise wants employees of Yangzhi to visit the shopping website during working hours. So a URL filtering configuration file is configured to divide the predefined
The shopping website in the category is selected as blocked. But employee A can still use the company's network to shop online during lunch break. Then what are the following possible reasons
some?
In the following options, which of the two attacks use similar attack methods, they will generate a large number of useless response packets, occupying network bandwidth,
Consume equipment resources?
In the scenario of SACG linkage in bypass mode, only the traffic initiated by the terminal user will pass through the firewall, and the server will return to the terminal in use.
The traffic does not need to go through the firewall y. For the firewall, it belongs to the scenario of inconsistent traffic back and forth paths, this needs to turn off the session state check function.
Regarding traditional firewalls, which of the following statements are correct? (multiple choice)
Which of the following options belong to a third-party server account? (Multiple choice)
Regarding the use of MAC authentication to access the network in the WLAN networking environment, which of the following statements is wrong en.
Since the sandbox can provide a virtual execution environment to detect files in the network, the sandbox can be substituted when deploying security equipment
Anti-Virus, IPS, spam detection and other equipment.
URL filtering technology can perform URL access control on users according to different time objects and address objects to achieve precise management of users.
The purpose of the Internet behavior.
The relationship between user groups and accounts in user management is stored in a tree on the Agile Controller-Campus. An account belongs to only one user group.
Consistent with the corporate organizational structure: If the OU (OnizbonUnit) structure stored in the AD/LDAP server is consistent with the corporate organizational structure, users are stored Under 0OU, when the Agile Controller-Campus synchronizes AD/LDAP server accounts, which synchronization method can be used?
Business accompanying is-A special access control method, according to the user's access location, access time, access method and terminal use to grant designated investment limits, among which the physical connection can be divided into 3 Class, excluding which of the following access methods?
In centralized networking, database,SM server,SC server\ AE Servers are centrally installed in the corporate headquarters. This networking method is suitable for companies with a wide geographical distribution of users and a large number of users.
There are two ways for Business Manager to download patches. When using hierarchical deployment, you can download patches directly from the management center or through Microsoft patches Server download patch.
When the license of Huawei USG6000 product expires, the RBL function will be unavailable, and users can only use the local black and white list to filter junk mail.
155955cc-666171a2-20fac832-0c042c0435
Malicious code usually uses RootKit technology in order to hide itself. RootKit modifies the kernel of the system by loading a special driver.
To hide itself and the role of designated files.
The network-based intrusion detection system is mainly used to monitor the information of the critical path of the network in real time, listen to all packets on the network, collect data, and divide
Analyze the suspicious object, which of the following options are its main features? (multiple choices)
In Huawei USG6000 products, IAE provides an integrated solution, all content security detection functions are integrated in a well-designed
In the high-performance engine. Which of the following is not the content security detection function supported by this product?
Which of the following statement is correct about Policy Center system client function?
Portal page push rules have priority, and the rules with higher priority are matched with the user's authentication information first. If none of the configured rules match, The default rules are used.
3 Months Free Update
3 Months Free Update
3 Months Free Update