We at Crack4sure are committed to giving students who are preparing for the Huawei H12-731_V2.0 Exam the most current and reliable questions . To help people study, we've made some of our HCIE-Security (Written) V2.0 exam materials available for free to everyone. You can take the Free H12-731_V2.0 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
The following is a description of traceability audits Which one is correct? (single selection).
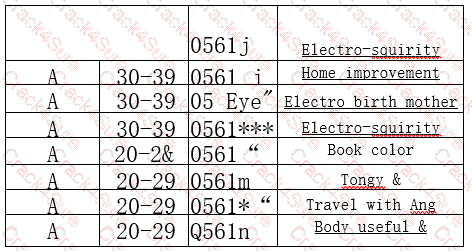
Figure 1 shows the raw data table Figure 2 shows the data processed by K•anonymization technology, what is the K value of the processing? (Selection).
NIP provides security mechanisms from multiple levels such as administrators and logs to build the security of operation and maintenance Which of the following security options are included?
Which of the following is not a virus exemption method? (single selection).
Let's take the L2TP over IPSec in the dual-machine scenario What is wrong with the description is the egg? (single selection).
Which of the following options is a major cause of business disruption in the cloud? (multiple selection).
The following describes FW's application behavior control features Which one is correct? (single selection).
Huawei's Sec Insight system comes with the function of stream pin.
In the capacity building of the security team, it is generally divided into management positions and technical posts, which of the following are not the key responsibilities of technical positions? (single selection).
Whitelisting may not properly handle complex obfuscation, which could allow attackers to subvert filters and potentially inject SQL language.
Which of the following does HiSec Insight's big data processing not include?
With the continuous development of network technology The firewall is also completing its own upgrade The technology evolution that firewalls have undergone includes which of the following options
When the Abnormal Traffic Inspection & Control System^ defense strategy of the Abnormal Traffic Monitoring System ATIC selects the anti-uninstall action, it utilizes the status code (targeted) for which of the following options GET request method redirection) to prove the true identity of the client?
Which of the following options is primarily detected by Threat Detection Services (MTD)?
Which options below are the main changes in Equal Protection 2.0 compared to Equal Protection 1.0' (multiple choices).
The trap configuration of the switching machine is as follows:
deception
deception enable
deception detect-network id 1 192.168.1.0 255.255.255.0
deception detect-network id 1 192.168.2.0 255.255.255.0
deception decoy destination 192.0.2.100
Which of the following descriptions of this configuration is correct? (single selection).
The IP address used by the Ax deception decoy destination to configure the trapping probe
B. The Deception Detect-Network ID is used to configure the detection network for trapping
C. Deception Enable should be configured under the interface.
D. Deception is used to turn on the device's trapping function
Common database security audit techniques according to technical characteristics What are the categories that can be divided into? (multiple selection).
Which of the following parameters is included in the DNS request routing method in the firewall DNS transparent proxy?
A global traffic steering strategy
B. Normal static or dynamic routing routing is selected
C. Policy routing routing is routed
D. The intelligent traffic steering mode configured by the DNS transparent proxy itself
About Huawei's firewall defense technology against SYN Flood Which of the following options is correctly described?
When deploying an Anti-DDos system using bypass, which of the following options is a common drainage method? (single selection).
End devices and users must authenticate and authorize before they can access the post-authentication domain.
Which of the following services are security management services in HUAWEI CLOUD solutions?
With the following description of the load balancing feature of USG Firewall Server, what are the correct items?
Which of the following options are the main dangers of computer Trojans?
Employees visit illegal or malicious websites at will Viruses, Trojans, and worms will be attacked, so we need to enable URL filtering. Which of the following options is a feature of URL Shopping?
By default, two subnets of the same VPC network deployed in different physical resource pools cannot access each other.
DNS Request Flood for DNS authoritative servers If TC source authentication is used The client device does not support using TCP to send DNS requests, how to verify the identity of the client? (single selection).
The sandbox and the firewall link anti-virus After the sandbox detects the virus file, the next information is fed back to the firewall (radio selection).
Data destruction refers to the use of various technical means to completely delete the data in computer storage devices, so as to prevent unauthorized users from using residual data to restore the original data information, so as to achieve the purpose of protecting key data. Which of the following options is wrong about how data is destroyed?
Which of the following options are part of the Internet Behavior? (multiple selection).
Formatting your computer means that the files have been completely erased Unable to fix.
The following is a description of DNS transparent proxy Which ones are correct? (multiple selection).
The firewall policy feature supports IPv4, but does not support IPv6 (radio selection).
The purpose of access control is to provide access to authorized subjects and prevent any unauthorized and intentional access.