We at Crack4sure are committed to giving students who are preparing for the Huawei H12-891_V1.0 Exam the most current and reliable questions . To help people study, we've made some of our HCIE-Datacom V1.0 exam materials available for free to everyone. You can take the Free H12-891_V1.0 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
MPLS implements data forwarding based on two different planes. Which of the following statements regarding the forwarding mechanism are correct?
A 32-bit MPLS header consists of a 20-bit label used for packet forwarding, a 3-bit EXP field that identifies the IP packet priority, a 1-bit bottom-of-stack flag that identifies the last label, and an 8-bit TTL field. Which statement regarding the TTL field is correct?
What can be determined from the following figure?
< R1 > display bgp ipv6 routing-table
Total Number of Routes: 2
* > i Network : 3002::3
NextHop : 3000:FDEA::3
MED : 0
Path/Orgn : i
* > i Network : 3002::4
NextHop : 3000:FDEA::3
MED : 0
PrefixLen : 128
LocPrf : 100
PrefVal : 0
Path/Orgn : 65001 i
BGP EVPN can be used as the VXLAN control plane protocol to completely prevent traffic flooding, such as broadcast ARP packets, on the VXLAN network.
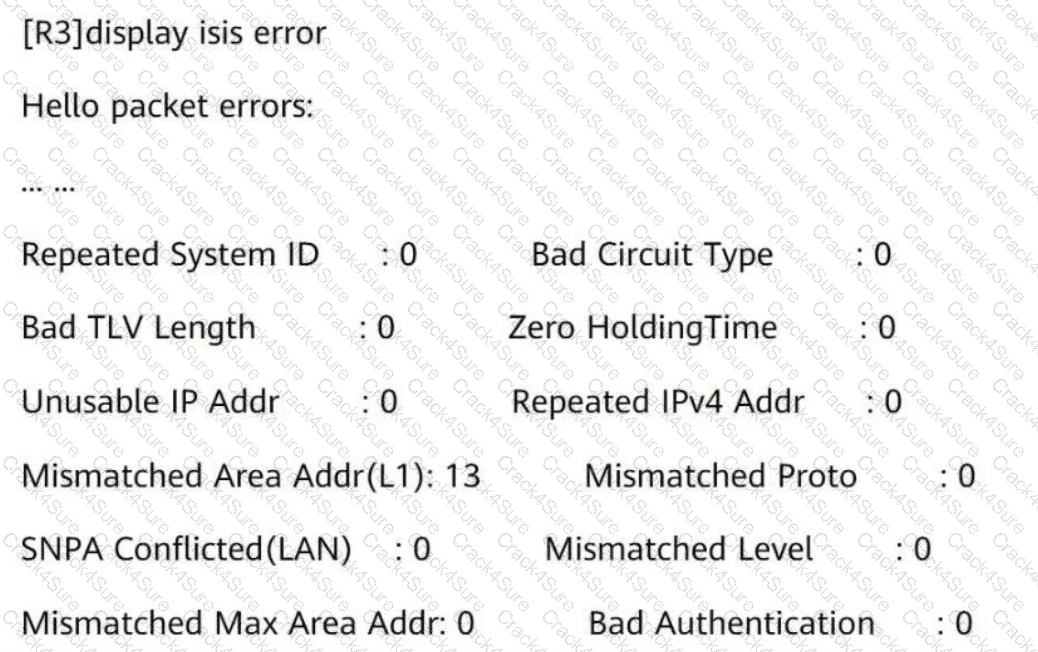
The IS-IS Level-1 neighbor relationship is not established between R3 and R4. Referring to the following information, what is the possible cause?
On a VXLAN-based virtualized campus network, BGP EVPN can be used as the control plane protocol. Which of the following EVPN route types are not used in the virtualized campus network scenario?
Network Quality Analysis (NQA) is a real-time network performance detection and measurement technology. It monitors the performance of multiple protocols running on a network. Which of the following protocols can be monitored by NQA?
Which of the following issues do DiffServ model-based QoS have?
Which of the following inter-AS MPLS L3VPN solutions needs ASBRs to transmit VPNv4 routes?
The on-premise mode is recommended for controller deployment on small and midsize campus networks.
On a CloudCampus virtualized campus network, virtual networks are defined based on services. Each virtual network corresponds to a service, and isolation needs to be manually configured between virtual networks.
There are multiple SR-MPLS TE tunnel protection mechanisms. FRR (Fast Reroute) constructs a virtual node to convert multiple identical route advertisement nodes into a single route advertisement node, and then computes the backup next hop of the virtual node based on the TI-LFA algorithm. In this way, traffic can be quickly switched when a fault occurs.
What is the name of this protection mechanism?
A carrier ' s home broadband service requires a maximum downstream bandwidth of 100 Mbit/s during off-peak hours and a guaranteed downstream bandwidth of 50 Mbit/s during peak hours. The home broadband service includes the home IP phone service and the home Internet access service. Which of the following configurations best meets the service requirement?
OSPF is deployed on a campus network to implement network interconnection. The LSDB of R2 is shown in the figure.
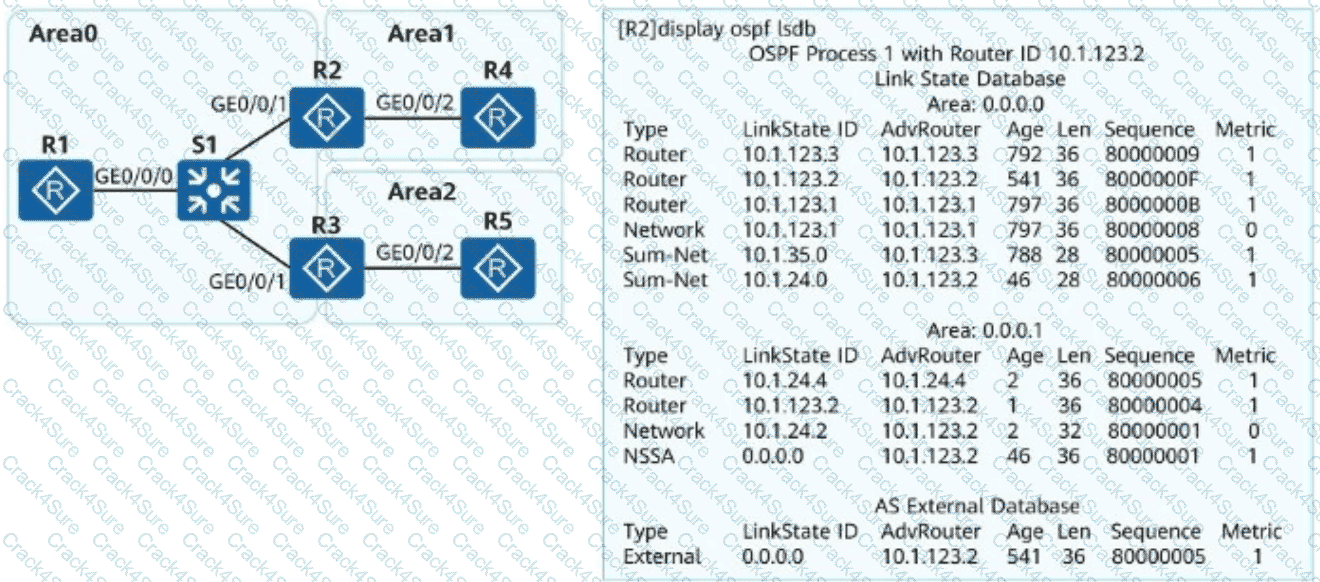
What can be determined from the LSDB?
Which of the following statements about BGP EVPN principles are correct in a scenario where a VXLAN tunnel is dynamically established through BGP EVPN?
Man-in-the-middle attacks (MITM) or IP/MAC Spoofing attacks are common on intranets and can cause information leakage.
Which configuration method can prevent these attacks?
NETCONF provides a set of mechanisms for managing network devices. What layers can NETCONF be conceptually partitioned into?
Exhibit:
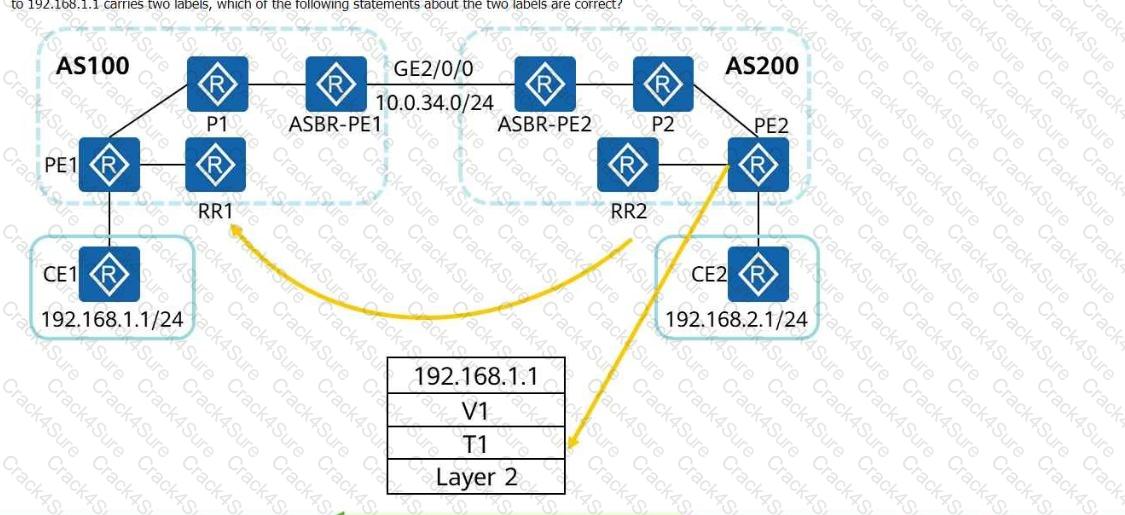
The following figure shows the inter-AS MPLS VPN Option C (solution 2). RRs are deployed, and no traffic passes through the RRs during forwarding. If a data packet sent from PE2 to 192.168.1.1 carries two labels, which of the following statements about the two labels are correct?
MPLS supports forwarding equivalence class (FEC). Which of the following cannot be used as an FEC allocation standard?
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, run the command on the VTEP to view BGP EVPN routes. The route entries shown in the following figure are displayed. Which of the following statements about these routing entries are correct?
Network (EthTagId/IP Prefix/IP PrefixLen)
NextHop
* > i 0:172.16.2.0:24 1.1.1.2
* > i 0:172.16.13.0:24 1.1.1.2
* > i 0:192.168.122.0:30 1.1.1.2
OSPF is a mature protocol and is unlikely to have route computation errors in a regular networking environment under correct configurations. Which of the following statements are correct about the possible causes preventing an OSPF neighbor relationship from entering Full state?
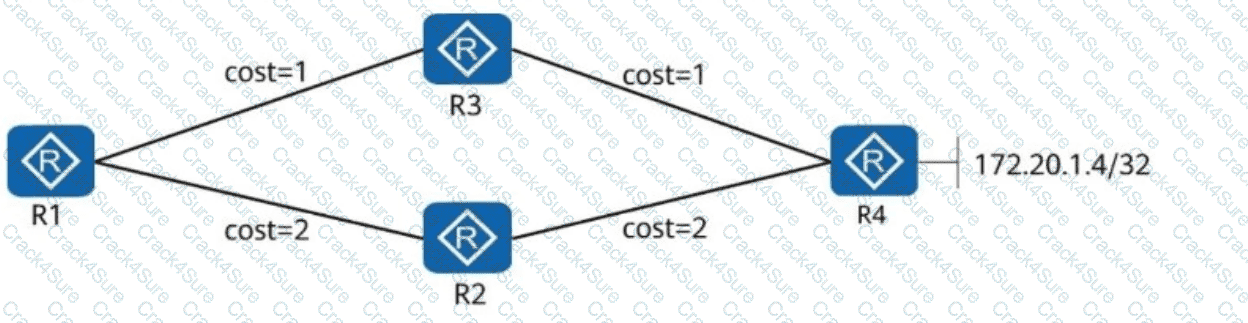
In the following figure, R1, R2, R3, and R4 all belong to OSPF area 0. The link costs are marked in the figure. The Loopback0 addresses of R1, R2, R3, and R4 are advertised to OSPF. R1, R2, and R3, which are R4 clients, use Loopback0 to establish an iBGP peer relationship with R4. The directly connected network segment 172.20.1.4/32 of R4 is advertised to BGP. Which of the following statements are correct about the direction of traffic from R1 to 172.20.1.4/32?
IPsec SAs can be established in either manual mode or IKE auto-negotiation mode. Which of the following statements about the two modes is incorrect?
After the reset isis all command is run, the specified IS-IS process is reset, and all involved IS-IS neighbor relationships are re-established; however, IS-IS statistics are not cleared.
Which of the following are advantages of GRE tunnels? (Select All that Apply)
When static IPsec VPN is used for WAN interconnection in the Huawei CloudCampus Solution, the AP, Router, and _____ can be used as egress devices. (Use full spelling with the first letter capitalized.)
Which of the following factors does not need to be considered during the selection of core devices for the enterprise bearer WAN?
Refer to the following command output on the router R1. Which of the following statements is incorrect?
< R1 > display interface Tunnel
Tunnel0/0/0 current state : UP
Line protocol current state : UP
Last line protocol up time : 15:21:23 UTC-08:00
Description: ! 0.0.3.3
Route Port, The Maximum Transmit Unit is 1500
Internet Address is 20.1.1.1/24
Encapsulation is TUNNEL, loopback not set
Tunnel source 10.0.1.1 (LoopBack0), destination 10.0.3.3
Tunnel protocol/transport GRE/IP, key disabled
keepalive disabled
Checksumming of packets disabled
Current system time: 15:21:37-08:00
300 seconds input rate 0 bits/sec, 0 packets/sec
300 seconds output rate 0 bits/sec, 0 packets/sec
13 seconds input rate 0 bits/sec, 0 packets/sec
13 seconds output rate 448 bits/sec, 0 packets/sec
9 packets output, 824 bytes
0 output error
Input bandwidth utilization : -
Output bandwidth utilization : -
The ________ command can be run to completely isolate Layer 2 and Layer 3 of different interfaces in a VLAN. (Use lowercase letters to supplement the command, which cannot be abbreviated.)
Which of the following statements regarding RT are correct?
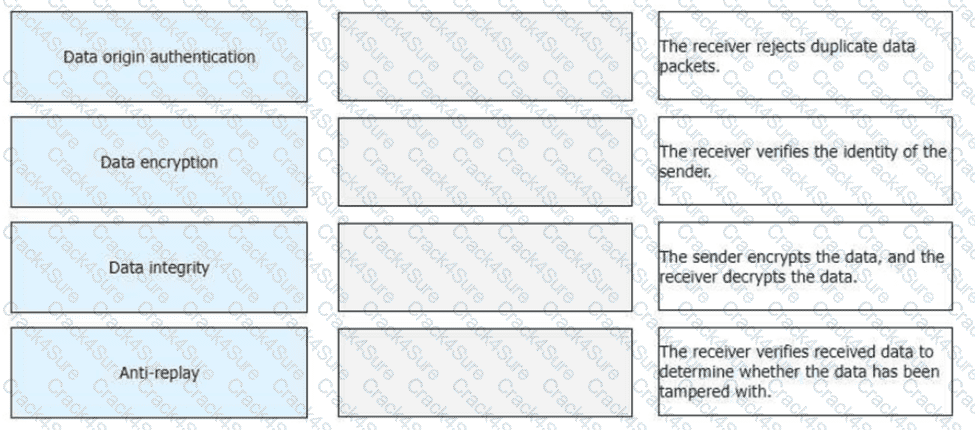
Drag the IPsec functions on the left to the corresponding function description on the right.
Portal authentication is recommended for scenarios with high mobility and numerous terminal types, such as shopping malls and supermarkets. MAC address authentication is recommended for dumb terminals that do not support Portal authentication, such as printers, fax machines, and IP phones.
OSPFv2 is an IGP running on IPv4 networks, whereas OSPFv3 is an IGP running on IPv6 networks. OSPFv2 and OSPFv3 have similar LSA types, but their LSA functions are slightly different. Which of the following is not an OSPFv3 LSA type?
VLAN-based MAC address flapping detection is configured. If MAC address flapping occurs, actions to be taken on an interface can be configured as required. Which of the following actions cannot be configured?
SR-MPLS uses IGP extensions to advertise labels and reserve bandwidth to support high-bandwidth services.
Which of the following statements about SR-MPLS Policy path planning are correct?
Telemetry data must be encoded in GPB binary format. This format reduces the number of bytes in telemetry messages and improves the transmission efficiency compared with messages encoded in JSON format.
The ingress VTEP performs both Layer 2 and Layer 3 table lookup for packet forwarding. The forwarding mode is _____ IRB forwarding. (Capitalize the first letter.)
The following figure shows the inter-AS MPLS L3VPN Option C (Solution 2). ASBR-PE2 is connected to CE3 and runs eBGP.
To enable all CEs to communicate with each other, which of the following address families must peer relationships be enabled in the BGP process of ASBR-PE2?
When static IPsec VPN is used for WAN interconnection in the Huawei CloudCampus Solution, the AP, Router, and ____ can be used as egress devices.
After a wireless user passes Portal authentication, which of the following parameters cannot be used for authorizing the user?
An SR-MPLS Policy needs to divert service traffic to a tunnel for forwarding. If traffic from various services is destined for the same address, which of the following traffic diversion modes is recommended to ensure the quality of each service?
In the small and midsize campus network design based on the Huawei CloudCampus Solution, when over 100 branches need to communicate with each other, which of the following interconnection networking models is recommended?
In the Huawei CloudCampus Solution, which of the following devices can go online through the registration query center?
As shown in the figure, when PE1 receives an ARP request packet, it forwards the packet to PE4. The packet then carries two labels. The label value 201 is carried by the EVPN Type ____ route. (Enter only digits.)
iMaster NCE-Campus provides the terminal identification function to display the terminal type, operating system, and manufacturer information.
Which of the following commands needs to be run in the BGP view to enable a VPN instance to advertise IP routes to the BGP-EVPN address family?
Which of the following roles is NOT a core role in Huawei ' s Free Mobility solution?
When configuring a static VXLAN tunnel, you need to manually configure the _____, VTEP IP address, and ingress replication list. (Enter only uppercase letters.)
The TTL field encapsulated in the MPLS label header can prevent infinite loops of MPLS packets. Which of the following statements regarding the TTL field are correct?
Which of the following number sequences can be matched by the regular expression 100.s?
During the evolution from OSPFv2 to OSPFv3, LSA formats and functions remain unchanged, except that the network layer addresses in LSAs are changed from IPv4 to IPv6.
Which of the following statements about SR-MPLS characteristics are correct? (Select all that apply)
During the implementation of iMaster NCE-Campus Wi-Fi location-based services (LBS), terminal location data is sent to an LBS platform through HTTP requests. Which of the following data formats is used in such HTTP requests?
Flavors can be used to enhance SRv6 instructions to meet more diversified service requirements. Which of the following are flavors? (Select all that apply)
The channelized sub-interface and FlexE technologies both can be used to implement network slicing, but the application scenarios of the two technologies are slightly different. Which of the following statements about the two technologies are correct?
Which of the following is the purpose of configuring IS-IS fragmentation on an IS-IS device?
Which of the following are carried in an HTTP/1.1 response?
/ifm/interfaces/interface in Huawei Open Programmability System (OPS) is the URL used to identify a device ' s managed object.
Among NETCONF operations, the < config > operation may contain an operation attribute, which is used to specify an operation type for configuration data. Which of the following operation attributes is incorrect?
IPsec uses an asymmetric encryption algorithm to encrypt the symmetric algorithm key, which it uses to encrypt/decrypt data, ensuring security and performance.
Which of the following are carried in the HTTP/1.1 response header?
The NETCONF content layer contains device configuration data.
Which of the following statements are correct about the following NETCONF configuration?
< ?xml version= " 1.0 " encoding= " UTF-8 " ? >
< rpc xmlns= " urn:ietf:params:xrnl:ns:netconf:base:1.0 " message-id= " 801 " >
< edit-config >
< target >
< running/ >
< /target >
< default-operation > merge < /default-operation >
< error-option > rollback-on-error < /error-option >
< config xmlns:xc= " urn:ietf:params:xml:ns:netconf:base:1.0 " >
< vlan xmlns= " http://www.huawei.com/netconf/vrp/huawei-vlan " >
< vlans >
< vlan >
< vlanId > 10 < /vlanId >
< protocolVlans >
< protocolVlan xc:operation= " merge " >
< protocolIndex > 0 < /protocolIndex >
< /protocolVlan >
< /protocolVlans >
< /vlan >
< /vlans >
< /vlan >
< /config >
< /edit-config >
< /rpc >
Refer to the following command output on the router R3. Which of the following statements are correct?
< R3 > display interface Tunnel
Tunnel0/0/0 current state : UP
Line protocol current state : UP
Last line protocol up time : 15:21:26 UTC-08:00
Description: HUAWEI, AR Series, Tunnel0/0/0 Interface
Route Port, The Maximum Transmit Unit is 1500
Internet Address is 20.1.1.2/24
Encapsulation is TUNNEL, loopback not set
Tunnel source 10.0.3.3 (LoopBack0), destination 10.0.1.1
Tunnel protocol/transport GRE/IP, key disabled
keepalive disabled
Checksumming of packets disabled
In the Huawei SD-WAN Solution, which of the following routing protocols is used to advertise VPN routes between CPEs?
An enterprise has three types of services. Voice and video services are key services and need to be guaranteed, and FTP services are non-key services. Which of the following scheduling modes is optimal for satisfying the service requirements?
What can be determined from the following figure?
< R1 > display ipv6 routing-table protocol isis
Public Routing Table : ISIS
Summary Count: 6
ISIS Routing Table ' s Status : < Active >
Summary Count: 6
Destination : 3000:FDEA::4
NextHop : FE80::2E0:FCFF:FE98:2577
Cost : 20
Interface : GigabitEthernet0/0/1
PrefixLength : 128
Preference : 15
Protocol : ISIS-L2
Flags : D
What is the router ID length supported by OSPFv3?
Which MPLS label will be used by PE2 for forwarding traffic to 10.0.1.1 based on the following SR-MPLS database?
Given Data (LSDB Information):
Prefix-SID: 100
SRGB Base: 40000
An O & M platform mainly provides unified monitoring and performance management for network devices. Which of the following is NOT device monitoring data?
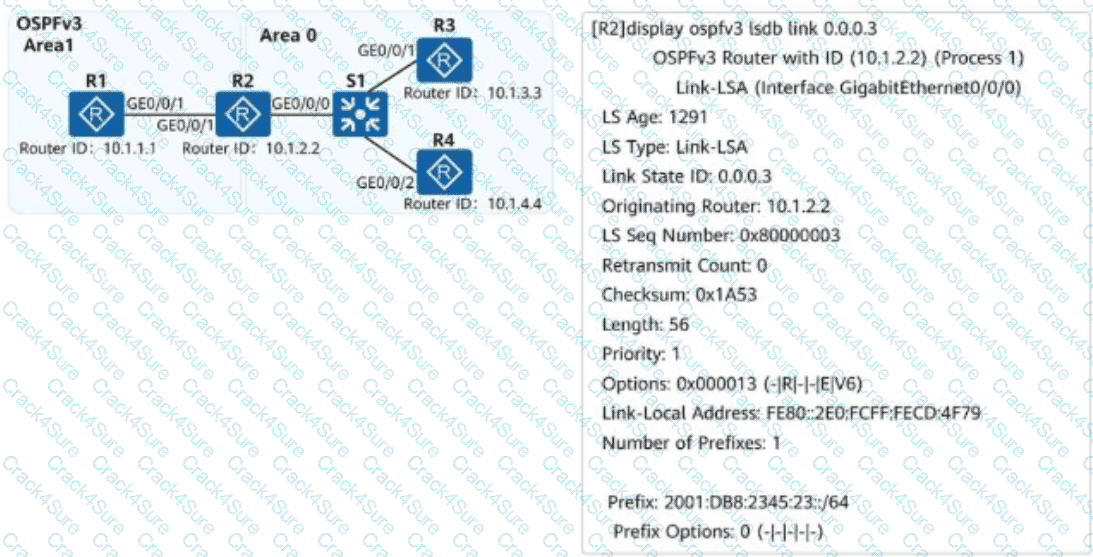
On the campus network shown, IPv6 is deployed for service tests. Four routers are deployed on the network, and OSPFv3 is used for IPv6 network connectivity. An engineer checks the LSDB of R2 and obtains a Link-LSA. Which of the following statements about the LSA are correct?
NAFTIR policing can only be applied to the inbound direction. Its purpose is to monitor the traffic entering the device and ensure that the upstream device does not unnecessarily consume network resources.
In an MPLS VPN network, two-layer MPLS labels are added into data packets before they are transmitted over the public network. Which of the following statements regarding data packet processing are correct?
Huawei Open Programmability System (OPS) uses standard HTTP methods to access managed objects to manage network devices. Which of the following HTTP methods is used to configure the value of a network device ' s managed object?
Which of the following statements about IPSG is incorrect?
To obtain the token ID of iMaster NCE, you need to send an HTTP request message that includes the following Python code to invoke an iMaster NCE RESTful API.
Which of the following statements is incorrect?
import requests
nbi_name = " demo13@north.com "
nbi_pwd = " CgocVcVe1@ "
host = " 139.9.213.72 "
port = " 18002 "
URI = " /controller/v2/tokens "
post_token_url = " https:// " + host + " : " + port + URI
headers_post = { " Content-Type " : " application/json " , " Accept " : " application/json " }
r = requests.post(post_token_url, headers=headers_post, json={ " userName " : nbi_name, " password " : nbi_pwd}, verify=False)
O & M personnel for a large-scale event center receive feedback about Wi-Fi access failures. iMaster NCE-CampusInsight provides the function for personnel to view packet exchange processes and locate the root cause. It is found that IP addresses in the DHCP address pool are exhausted, preventing IP addresses from being assigned to mobile terminals. Which of the following functions is used by O & M personnel in this scenario?
The path of an SR-MPLS TE tunnel can be calculated by the controller or tunnel ingress.
Which of the following are application optimization functions in the Huawei SD-WAN Solution?
Network administrator A wants to use an IP prefix list to match specific routes. Which of the following routes can be matched by the IP prefix list shown in this figure?
ip ip-prefix TEST permit 10.0.0.0 24 less-equal 30
When you configure a virtualized campus network on iMaster NCE-Campus and enable external networks to connect to the Internet, iMaster NCE-Campus will automatically deliver a specific route to direct traffic to the corresponding external network.
How long is an IPv6 prefix assigned to a host when an IPv6 address is configured for the host in SLAAC mode?
Which of the following is the type of northbound API used by iMaster NCE-WAN?
On a CloudCampus virtualized campus network, which of the following modes can be used by a fabric to connect to external networks?
The following figure shows some configurations of R1. Based on these configurations, which of the following statements about IS-IS on R1 are correct?
isis 1
is-level level-2
cost-style wide
network-entity 49.0022.ee8c.a0c2.baf1.00
isis 2 vpn-instance tt
is-level level-2
cost-style wide
network-entity 47.00ce.390d.efdc.b3e1.00
isis 3 vpn-instance rr
is-level level-2
cost-style wide
network-entity 47.cc0a.3efb.bbdd.aae1.00
In the admission design for large- and medium-sized campus networks, which of the following authentication modes can be used for PCs connected to IP phones?
A client sends an HTTP request to a server, and the server sends back an HTTP response. Which of the following parameters is not carried in the HTTP response?
In a BGP/MPLS IP VPN scenario, if a PE and CE use OSPF to exchange routing information, domain IDs are used to identify whether the routes imported to VPN instances are from the same OSPF domain.
Which of the following statements about DHCP snooping is incorrect?
BGP Link State (BGP-LS) introduces a new NLRI into BGP. The NLRI carries link, node, topology prefix, and other information, and is also referred to as the link state NLRI.
As shown in the figure, SW1 and SW2 use asymmetric IRB (Integrated Routing and Bridging) forwarding, and PC1 and PC2 communicate with each other. Which of the following is the destination MAC address of the original data frame in the packet sent from VTEP1 to VTEP2?
3 Months Free Update
3 Months Free Update
3 Months Free Update