We at Crack4sure are committed to giving students who are preparing for the ISA ISA-IEC-62443 Exam the most current and reliable questions . To help people study, we've made some of our ISA/IEC 62443 Cybersecurity Fundamentals Specialist exam materials available for free to everyone. You can take the Free ISA-IEC-62443 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Which statement BEST describes the enforceability of standards?
What is the primary goal of the Assess phase in the IACS Cybersecurity Lifecycle?
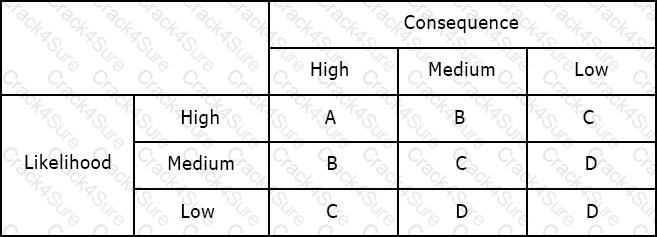
Using the risk matrix below, what is the risk of a medium likelihood event with high consequence?
Which characteristic is MOST closely associated with the deployment of a demilitarized zone (DMZ)?
Available Choices (select all choices that are correct)
Which analysis method is MOST frequently used as an input to a security risk assessment?
Available Choices (select all choices that are correct)
What port number is used by MODBUS TCP/IP for communication?
Which of the following BEST describes 'Vulnerability'?
What does the System under Consideration (SuC) include in the context of ISA/IEC 62443 risk assessment?
How does ISA-62443-2-1 suggest integrating the IACS Security Program (SP) within an organization?
Which steps are included in the ISA/IEC 62443 assess phase?
Available Choices (select all choices that are correct)
Which organization manages the ISASecure conformance certification program?
Available Choices (select all choices that are correct)
Which factor drives the selection of countermeasures?
Available Choices (select all choices that are correct)
A company needs to create a standardized interface for exchanging real-time plant data between heterogeneous control devices while maintaining a structured organization of data elements such as folders, classes, and methods. Which feature of OPC supports this requirement?
Which ISA/IEC 62443 part covers technical security requirements used by product suppliers, integration service providers, and asset owners?
What type of cyberattack was discussed in the Ukrainian power grid case study?
Security Levels (SLs) are broken down into which three types?
When selecting a risk assessment methodology for a complex industrial automation system, which approach aligns BEST with ISA/IEC 62443 guidance?
What makes patching in IACS environments particularly complex?
What is a feature of an asymmetric key?
Available Choices (select all choices that are correct)
Which of the following is the underlying protocol for Ethernet/IP?
Available Choices (select all choices that are correct)
What do packet filter firewalls examine?
Available Choices (select all choices that are correct)
Which of the following PRIMARILY determines access privileges for user accounts?
Available Choices (select all choices that are correct)
A multinational corporation needs to implement a cybersecurity framework that can be adapted across different countries and industries while allowing continuous improvement. Which feature of the NIST CSF makes it suitable for this purpose?
What are the two sublayers of Layer 2?
Available Choices (select all choices that are correct)
Why were PLCs originally designed?
What is the primary focus of Part 3-2 in the ISA/IEC 62443 series?
In a defense-in-depth strategy, what is the purpose of role-based access control?
Available Choices (select all choices that are correct)
Why is OPC Classic considered firewall unfriendly?
Who is responsible for defining the tolerable residual cybersecurity risk as an input requirement for all activities?
Which of the following is a trend that has caused a significant percentage of security vulnerabilities?
Available Choices (select all choices that are correct)
How many security levels are in the ISASecure certification program?
Available Choices (select all choices that are correct)
What are the connections between security zones called?
Available Choices (select all choices that are correct)
If an asset owner wants to improve their organization's ability to respond during a cyberattack, which of the following activities would be MOST appropriate to implement?
A manufacturing plant has inconsistent cybersecurity processes that vary widely between shifts and teams. According to the maturity levels described in ISA/IEC 62443-2-1, how would this situation be classified?
How can Modbus be secured?
Why is it important for the asset owner to incorporate the IACS into its organization and security program during the Operation and Maintenance phase?
Which of the following protocols is mentioned as being commonly used in control systems?
What must be established as part of the risk assessment process?
Which of the following attacks relies on a human weakness to succeed?
Available Choices (select all choices that are correct)
What do the tiers in the NIST CSF represent?
What does IACS stand for?
What is the primary purpose of the NIST Cybersecurity Framework (CSF)?
What is Modbus?
What does Layer 1 of the ISO/OSI protocol stack provide?
Available Choices (select all choices that are correct)
Which is the BEST practice when establishing security zones?
Available Choices (select all choices that are correct)
An industrial facility wants to ensure that only authorized communication reaches its PLCs while minimizing disruption to time-sensitive control processes. Which type of firewall would BEST suit this need?
Why is patch management more difficult for IACS than for business systems?
Available Choices (select all choices that are correct)
How many maturity levels (ML) are established for evaluation criteria according to ISA/IEC 62443-2-4?
What is TRUE regarding safety systems?
Which is the BEST deployment system for malicious code protection?
Available Choices (select all choices that are correct)
Why is OPC Classic considered firewall unfriendly?
Available Choices (select all choices that are correct)
Which of the following is an element of monitoring and improving a CSMS?
Available Choices (select all choices that are correct)
Which is NOT a potential consequence for organizations that fail to prioritize control system security?
What type of security level defines what a component or system is capable of meeting?
Available Choices (select all choices that are correct)
In what step of the development process of the CSMS is “Establish purpose, organizational support, resources, and scope” taken care of?
As related to technical security requirements for IACS components, what does CCSC stand for?
Why is segmentation from non-IACS zones important in Network & Communication Security (SP Element 3)?
A national standards body wants to represent its country’s interests at an international level and adopt global standards locally. What role does this organization fulfill?
Under User Access Control (SP Element 6), which of the following is included in USER 1 — Identification and Authentication?
How many element groups are in the "Addressing Risk" CSMS category?
Which of the following BEST describes a control system?
What caution is advised when using the vector approach to security levels?
Which part of the standard provides a list of possible Foundational Requirements to address assessed risks?
3 Months Free Update
3 Months Free Update
3 Months Free Update