We at Crack4sure are committed to giving students who are preparing for the ISC CC Exam the most current and reliable questions . To help people study, we've made some of our CC - Certified in Cybersecurity exam materials available for free to everyone. You can take the Free CC Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
A structured approach used to oversee and manage risk for an enterprise is called:
Which of the following attacks can TLS help mitigate?
VLAN hopping belongs to which OSI layer?
How many bits represent the Organizationally Unique Identifier (OUI) in MAC addresses?
Security commensurate with risk and magnitude of harm is known as:
A set of security controls or system settings used to ensure uniformity of configuration through the IT environment?
In Mandatory Access Control (MAC), which statement is true?
Example of Type 1 authentication:
A DLP solution should be deployed so it can inspect all forms of data leaving the organization, including:
Port scanning attacks target which OSI layer?
The primary functionality of Privileged Access Management (PAM) is:
Which is NOT a component of a Business Continuity (BC) plan?
A transaction over $50,000 requires approval from both a manager and an accountant. Which concept applies?
The prevention of authorized access to resources or delaying time-critical operations is known as:
Which is an example of a deterrent control?
_______ are virtual separations within a switch used mainly to limit broadcast traffic.
A hacker launches a specific attack to exploit a known vulnerability. This is called:
What is the potential impact of an IPSec replay attack?
Which works by encapsulating one packet inside another?
In DAC, a subject granted access can:
Uses multiple types of access controls in layered fashion to avoid monolithic security:
A method for risk analysis that is based on the assignment of a descriptor such as low, medium, or high.
A device that forwards traffic to the port of a known destination device is a:
What is the main challenge in achieving non-repudiation in electronic transactions?
What is the purpose of the post-incident phase?
What federal law requires the use of vulnerability scanning on information systems operated by federal government agencies?
What is the main purpose of digital signatures?
David's team recently implemented a new system that gathers information from a variety of different log sources, analyzes that information, and then triggers automated playbooks in response to security events. What term BEST describes this technology?
Mark is configuring an automated data transfer between two hosts and needs an authentication method. What approach is best suited?
A company network experiences a sudden flood of network packets that causes major slowdown in Internet traffic. What type of event is this?
Which zero-trust component breaks LANs into very small, localized security zones?
A popular way of implementing the principle of least privilege is:
Which is strongly used for securing Wi-Fi?
Which device is used to control traffic flow between networks?
A measure combining impact and likelihood is known as:
Example of a deterrent control:
What is an IP address?
An event that jeopardizes confidentiality, integrity, or availability is called:
What is the purpose of a Business Impact Analysis (BIA)?
Which phase of the access control process (AAA) does a user prove his/her identity?
Which of the following best describes a zero-day vulnerability?
Which of the following does NOT normally influence an organization’s log retention policy?
Information should be consistently and readily accessible for authorized parties.
Which technology should be implemented to increase the work effort required for buffer overflow attacks?
Removing the design belief that the network has any trusted space. Security is managed at each possible level, representing the most granular asset. Microsegmentation of workloads is a tool of the model.
Natalia is concerned that users on her network may be storing sensitive information, such as Social Security numbers, on their hard drives without proper authorization or security controls. What third-party security service can she implement to best detect this activity?
Mark has purchased a Mac laptop. He is scared of losing his screen and is planning to buy an insurance policy. Which risk management strategy is this?
What does internal consistency of information refer to?
What does the termbusinessin business continuity planning refer to?
Which principle states that users should have access only to the specific data and resources needed to perform required tasks?
Which prevents threats?
An unusual occurrence in a system or network is best described as:
David is worried about distributed denial-of-service (DDoS) attacks against his company’s primary web application. Which option will provide the MOST resilience against large-scale DDoS attacks?
Duke would like to restrict users from accessing a list of prohibited websites while connected to his network. Which control would BEST achieve this objective?
Exhibit.
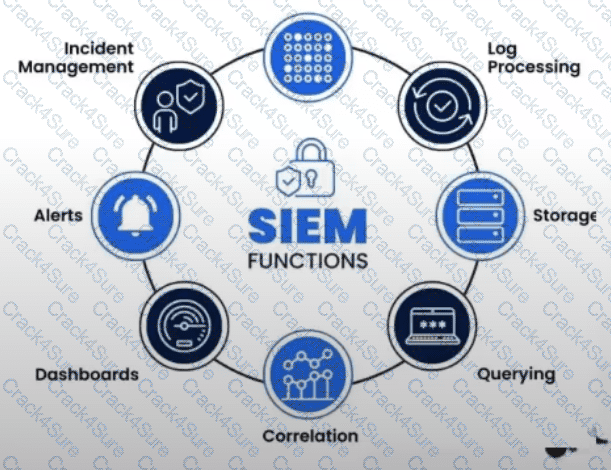
What is the purpose of a Security Information and Event Management (SIEM) system?
An attack in which an attacker listens passively to the authentication protocol to capture information that can be used in a subsequent active attack to masquerade as the claimant is known as:
Embedded systems and network-enabled devices that communicate with the Internet are considered:
Which version of TLS is considered the most secure and recommended for use?
What security feature is used in HTTPS?
The purpose of risk identification is:
The process of applying secure configurations to reduce the attack surface is known as:
Which type of application can intercept sensitive information such as passwords on a network segment?
John joined the ISC2 organization. His manager asked him to check the authentication controls in a security module. What would John use to ensure a certain control is working as he expects it to?
What is remanence?
What is the focus of disaster recovery planning after a data center outage?
Which organization defines Internet protocol standards?
Created by switches to logically segment a network without changing physical topology:
Walmart has a large e-commerce presence worldwide. Which solution would ensure the LOWEST possible latency for customers using their services?
What is the range of well-known ports?
If a device is found to be non-compliant with the security baseline, what action should the security team take?
Which of the following properties is NOT guaranteed by digital signatures?
Permitting authorized access while preventing improper disclosure.
Exhibit.
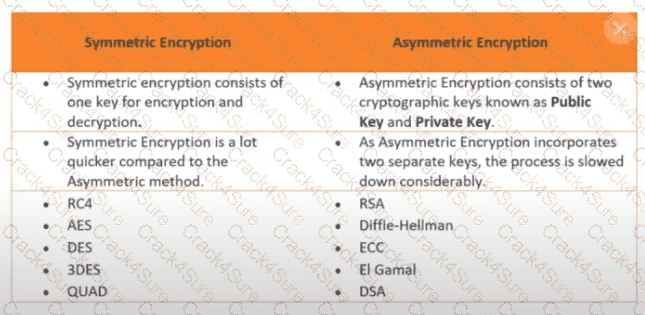
How many keys would be required to support 50 users in an asymmetric cryptography system?
Which one of the following groups is NOT normally part of an organization's cybersecurity incident response team?
The documented set of procedures to detect, respond to, and limit the consequences of cyberattacks is called:
Raj wants aphysical deterrent controlto discourage unauthorized entry. Which option best serves this purpose?
Which of the following is NOT a protocol of OSI Layer 3?
In cybersecurity, typical threat actors include:
What are registered ports primarily used for?
What kind of control is it when we add a backup firewall that takes over if the main one stops working?
What is the benefit of subnetting?
How often should an organization test its BCP?
Configuration settings or parameters stored as data and managed through a software graphical user interface (GUI) are examples of:
What drove the introduction of IPv6?
Which can be considered a fingerprint of a file or message?
A ________ creates an encrypted tunnel to protect your personal data and communications.
What is a threat in cybersecurity?
What is sensitivity in the context of confidentiality?
Are events that may indicate that an organization's systems or data have been compromised or that protective measures have failed.
Which authentication enables automatic identification across multiple service providers?
Which security control is most commonly used to prevent data breaches?
An attack in which a user authenticated to a server unknowingly invokes unwanted actions after visiting a malicious website is known as:
Load balancing primarily safeguards which CIA triad element?
The evaluation of security controls to determine whether they are implemented correctly and operating as intended is known as:
Is defined as the process of identifying, estimating, and prioritizing risks.
Which type of control is used to restore systems or processes to their normal state after an attack?
Representation of data at OSI Layer 3 is called a:
Who must follow HIPAA compliance?
What is the primary goal of input validation?
What is privacy in the context of Information Security?
In which access control model can the creator of an object delegate permissions?
Mark’s proposed configuration change must be approved and tested by a Change Control Board. This is an example of:
Which of the following protocols is a secure alternative to using Telnet?
A one-way spinning door or barrier that allows only one person at a time to enter a building or area.
The harmonization of automated computing tasks into reusable workflows is called:
Which attack most effectively maintains remote access and control over a victim’s computer?
Security controls protecting against fire, floods, and earthquakes are:
Often offered by third-party organizations and covering advisory or compliance objectives:
The method of distributing network traffic equally across a pool of resources is called:
Configuration settings or parameters stored as data and managed through a GUI are examples of:
A DDoS attack flooding ICMP packets is called:
A security event does not affect confidentiality, integrity, or availability. What is it?
Port used by DNS.
Access control used in high-security military and government environments:
An employee unintentionally shares confidential information with an unauthorized party. What term best describes this?
3 Months Free Update
3 Months Free Update
3 Months Free Update