We at Crack4sure are committed to giving students who are preparing for the Juniper JN0-335 Exam the most current and reliable questions . To help people study, we've made some of our Security, Specialist (JNCIS-SEC) exam materials available for free to everyone. You can take the Free JN0-335 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
You want to control when cluster failovers occur.
In this scenario, which two specific parameters would you configure on an SRX Series device? (Choose two.)
You want to deploy a virtualized SRX in your environment.
In this scenario, why would you use a vSRX instead of a cSRX? (Choose two.)
What information does encrypted traffic insights (ETI) use to notify SRX Series devices about known malware sites?
Which statement about security policy schedulers is correct?
You are asked to implement IPS on your SRX Series device.
In this scenario, which two tasks must be completed before a configuration will work? (Choose two.)
Which two statements about unified security policies are correct? (Choose two.)
Which two statements are correct about the cSRX? (Choose two.)
You are asked to determine how much traffic a popular gaming application is generating on your network.
Which action will you perform to accomplish this task?
You are asked to ensure that if the session table on your SRX Series device gets close to exhausting its resources, that you enforce a more aggress.ve age-out of existing flows.
In this scenario, which two statements are correct? (Choose two.)
When a security policy is deleted, which statement is correct about the default behavior of active sessions allowed by that policy?
What are two types of system logs that Junos generates? (Choose two.)
Which two functions does Juniper ATP Cloud perform to reduce delays in the inspection of files? (Choose two.)
On which three Hypervisors is vSRX supported? (Choose three.)
Your network uses a single JSA host and you want to implement a cluster.
In this scenario, which two statements are correct? (Choose two.)
Which two statements about SRX Series device chassis clusters are true? (Choose two.)
You are asked to reduce the load that the JIMS server places on your Which action should you take in this situation?
Which two sources are used by Juniper Identity Management Service (JIMS) for collecting username and device IP addresses? (Choose two.)
You have implemented a vSRX in your VMware environment. You want to implement a second vSRX Series device and enable chassis clustering.
Which two statements are correct in this scenario about the control-link settings? (Choose two.)
Exhibit

Referring to the exhibit, which two statements describe the type of proxy used? (Choose two.)
You are implementing an SRX Series device at a branch office that has low bandwidth and also uses a cloud-based VoIP solution with an outbound policy that permits all traffic.
Which service would you implement at your edge device to prioritize VoIP traffic in this scenario?
Click the Exhibit button.
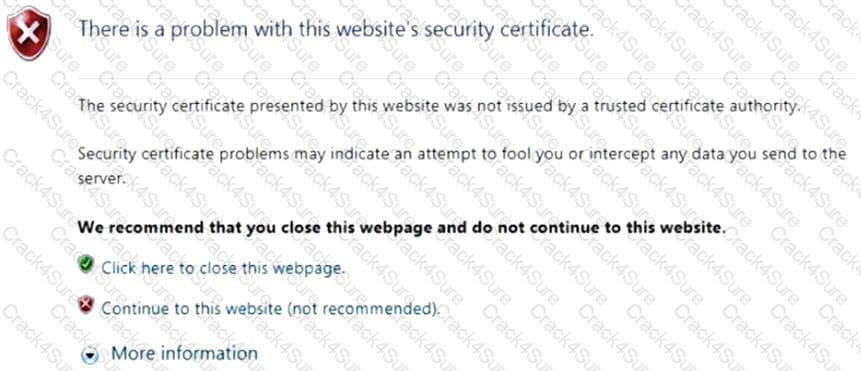
You have implemented SSL client protection proxy. Employees are receiving the error shown in the exhibit.
How do you solve this problem?
Which two statements are correct when considering IPS rule base evaluation? (Choose two.)
Which two statements are true about the vSRX? (Choose two.)
Which three statements about SRX Series device chassis clusters are true? (Choose three.)
3 Months Free Update
3 Months Free Update
3 Months Free Update