We at Crack4sure are committed to giving students who are preparing for the Juniper JN0-636 Exam the most current and reliable questions . To help people study, we've made some of our Security, Professional (JNCIP-SEC) exam materials available for free to everyone. You can take the Free JN0-636 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
What is the purpose of the Switch Microservice of Policy Enforcer?
Exhibit
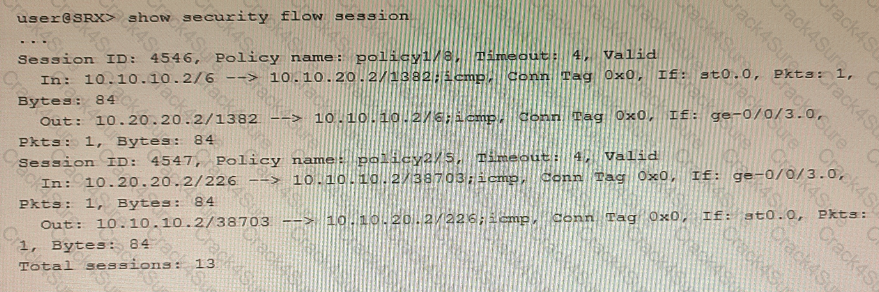
You are validating bidirectional traffic flows through your IPsec tunnel. The 4546 session represents traffic being sourced from the remote end of the IPsec tunnel. The 4547 session represents traffic that is sourced from the local network destined to the remote network.
Which statement is correct regarding the output shown in the exhibit?
Your Source NAT implementation uses an address pool that contains multiple IPv4 addresses Your users report that when they establish more than one session with an external application, they are prompted to authenticate multiple times External hosts must not be able to establish sessions with internal network hosts
What will solve this problem?
Click the Exhibit button.
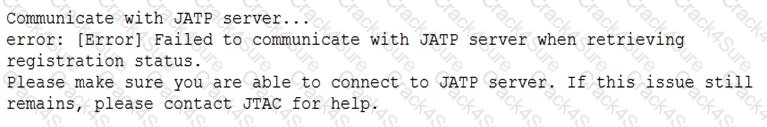
When attempting to enroll an SRX Series device to JATP, you receive the error shown in the exhibit. What is the cause of the error?
Exhibit.
A hub member of an ADVPN is not functioning correctly.
Referring the exhibit, which action should you take to solve the problem?
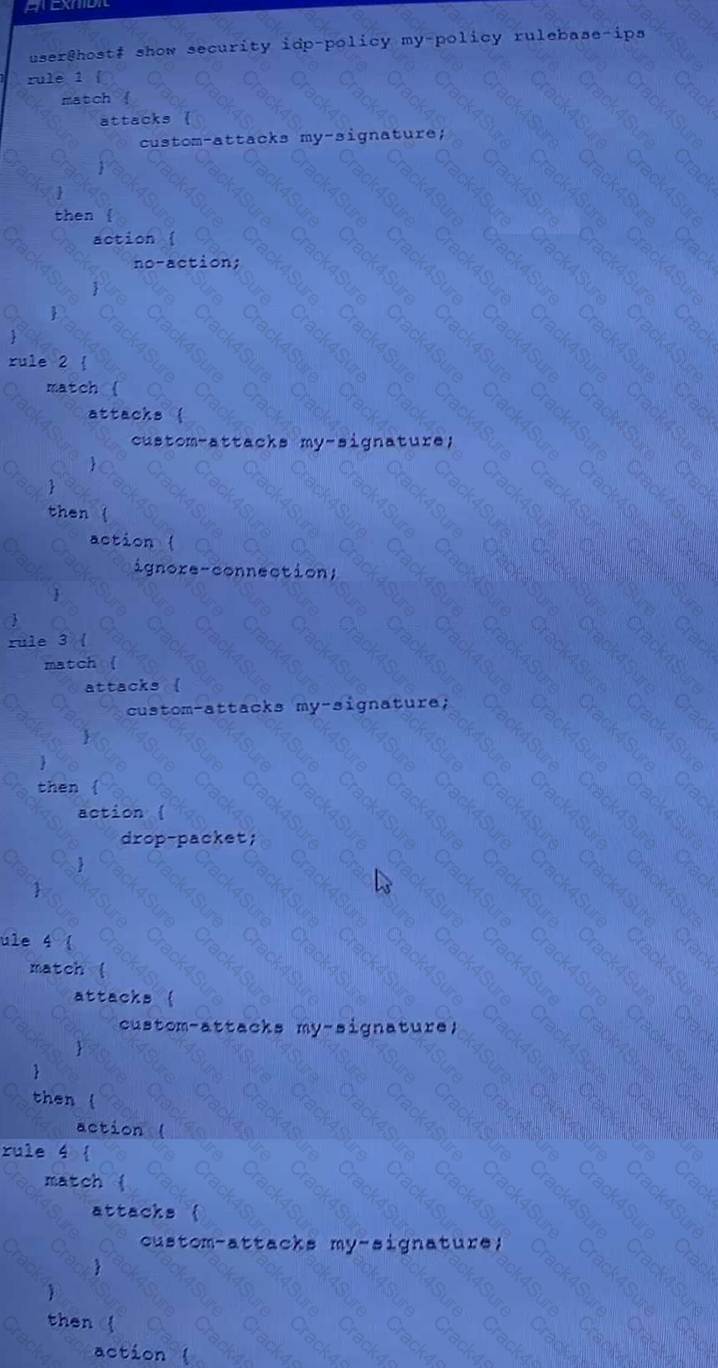
Exhibit
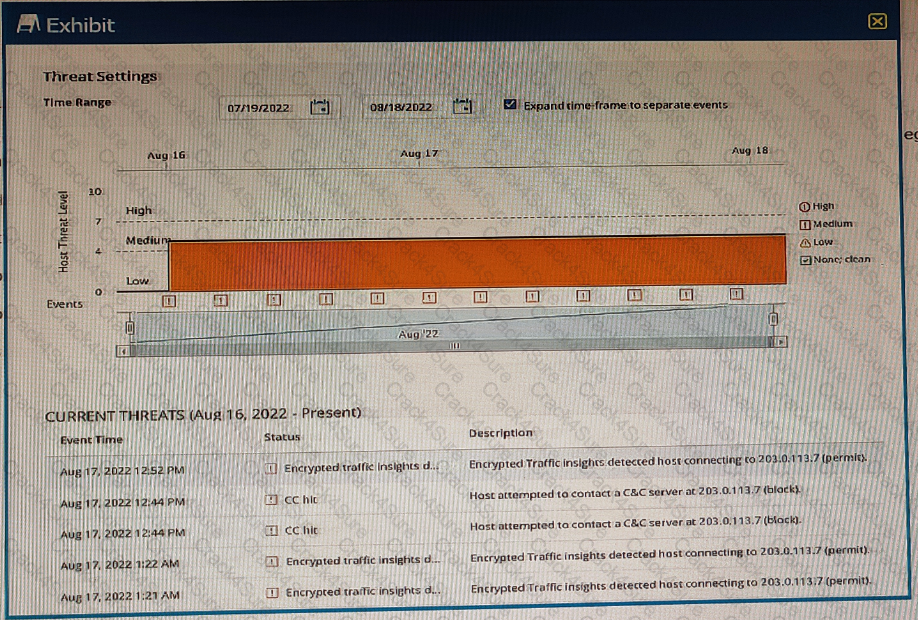
You are using ATP Cloud and notice that there is a host with a high number of ETI and C&C hits sourced from the same investigation and notice that some of the events have not been automatically mitigated.
Referring to the exhibit, what is a reason for this behavior?
The monitor traffic interface command is being used to capture the packets destined to and the from the SRX Series device.
In this scenario, which two statements related to the feature are true? (Choose two.)
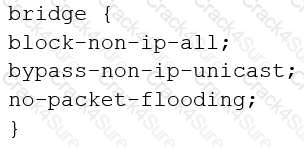
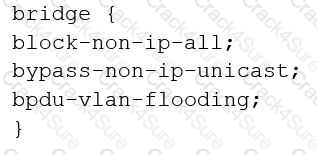
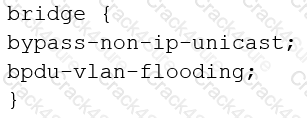
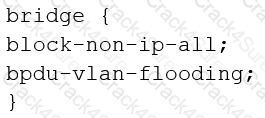
You are configuring transparent mode on an SRX Series device. You must permit IP-based traffic only, and BPDUs must be restricted to the VLANs from which they originate.
Which configuration accomplishes these objectives?
A)
B)
C)
D)
You have the NAT rule, shown in the exhibit, applied to allow communication across an IPsec tunnel between your two sites with identical networks. Which statement is correct in this scenario?
Which two types of source NAT translations are supported in this scenario? (Choose two.)
Exhibit:
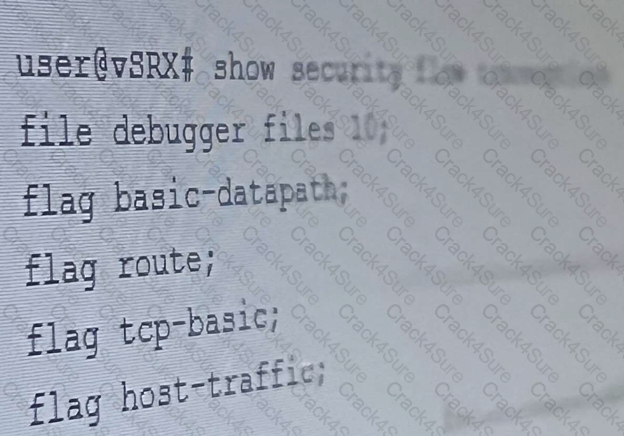
The security trace options configuration shown in the exhibit is committed to your SRX series firewall. Which two statements are correct in this Scenario? (Choose Two)
What are two valid modes for the Juniper ATP Appliance? (Choose two.)
Your company wants to use the Juniper Seclntel feeds to block access to known command and control servers, but they do not want to use Security Director to manage the feeds.
Which two Juniper devices work in this situation? (Choose two)
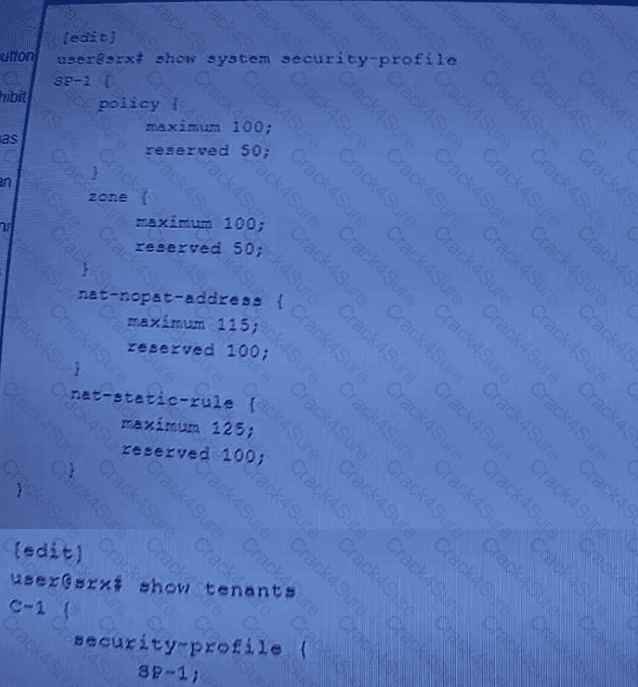
You are asked to allocate security profile resources to the interconnect logical system for it to work properly.
In this scenario, which statement is correct?
Your company uses non-Juniper firewalls and you are asked to provide a Juniper solution for zero-day malware protection. Which solution would work in this scenario?
All interfaces involved in transparent mode are configured with which protocol family?
Exhibit
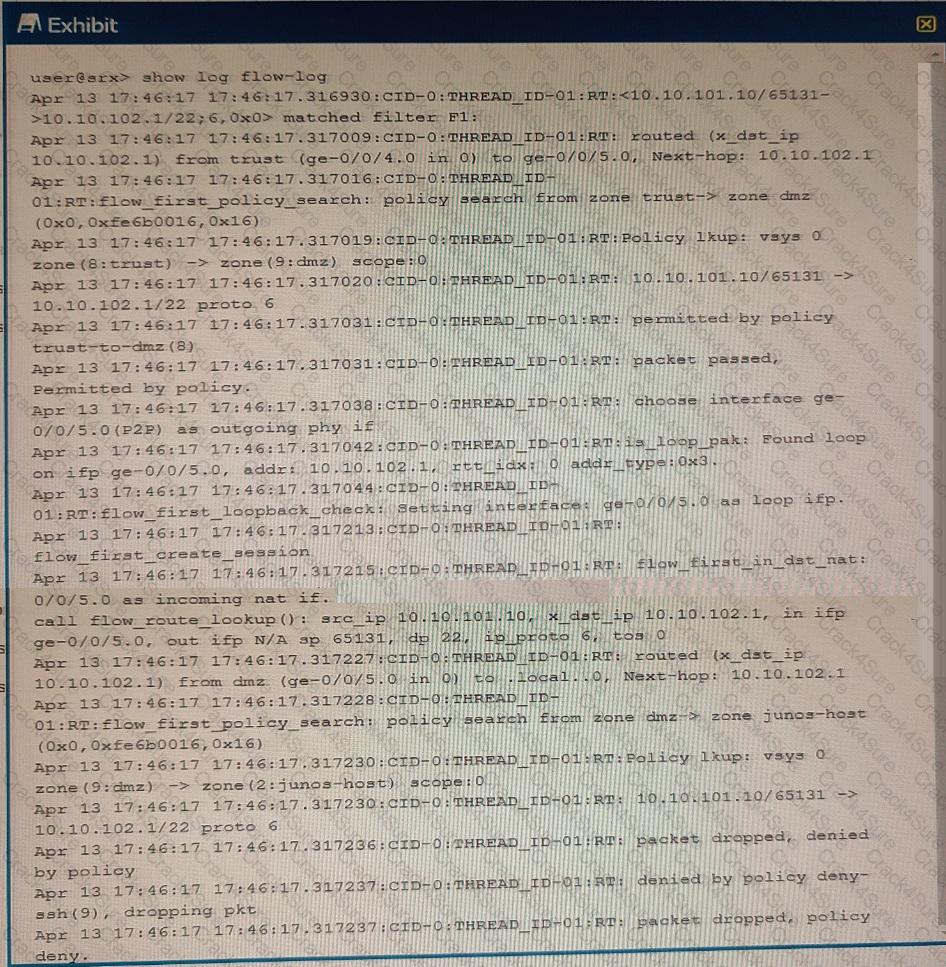
Referring to the exhibit, which three statements are true? (Choose three.)
You must implement an IPsec VPN on an SRX Series device using PKI certificates for authentication. As part of the implementation, you are required to ensure that the certificate submission, renewal, and retrieval processes are handled
automatically from the certificate authority.
In this scenario, which statement is correct.
According to the log shown in the exhibit, you notice the IPsec session is not establishing.
What is the reason for this behavior?
Exhibit

You have configured the SRX Series device to switch packets for multiple directly connected hosts that are within the same broadcast domain However, the traffic between two hosts in the same broadcast domain are not matching any security policies
Referring to the exhibit, what should you do to solve this problem?
Exhibit.
Referring to the exhibit, which two statements are true? (Choose two.)
Which two additional configuration actions are necessary for the third-party feed shown in the exhibit to work properly? (Choose two.)
Which two modes are supported on Juniper ATP Cloud? (Choose two.)
Exhibit

Referring to the exhibit, which three protocols will be allowed on the ge-0/0/5.0 interface? (Choose three.)
Exhibit:
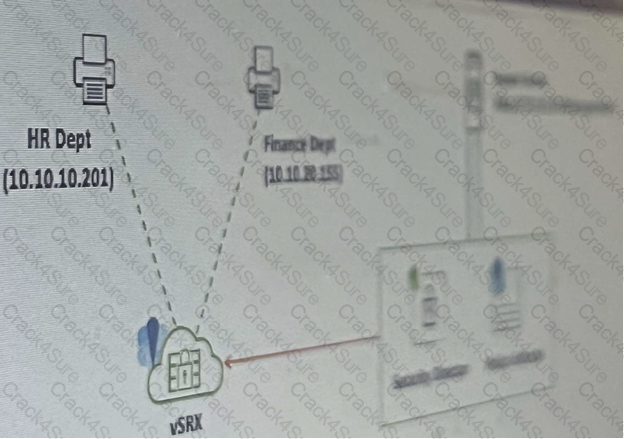
Referring to the exhibit, your company’s infrastructure team implemented new printers
To make sure that the policy enforcer pushes the updated Ip address list to the SRX.
Which three actions are required to complete the requirement? (Choose three )
You want to configure a threat prevention policy.
Which three profiles are configurable in this scenario? (Choose three.)
You opened a support ticket with JTAC for your Juniper ATP appliance. JTAC asks you to set up access to the device
using the reverse SSH connection.Which three setting must be configured to satisfy this request? (Choose three.)
Exhibit
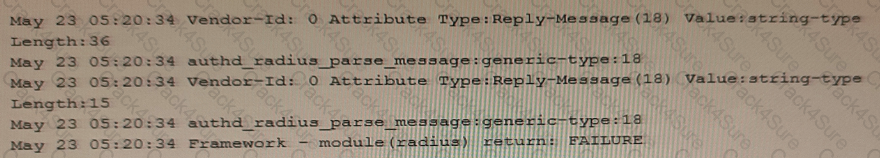
You configure a traceoptions file called radius on your returns the output shown in the exhibit
What is the source of the problem?
You are asked to deploy filter-based forwarding on your SRX Series device for incoming traffic sourced from the 10.10 100 0/24 network in this scenario, which three statements are correct? (Choose three.)
3 Months Free Update
3 Months Free Update
3 Months Free Update