We at Crack4sure are committed to giving students who are preparing for the Microsoft AZ-500 Exam the most current and reliable questions . To help people study, we've made some of our Microsoft Azure Security Technologies exam materials available for free to everyone. You can take the Free AZ-500 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
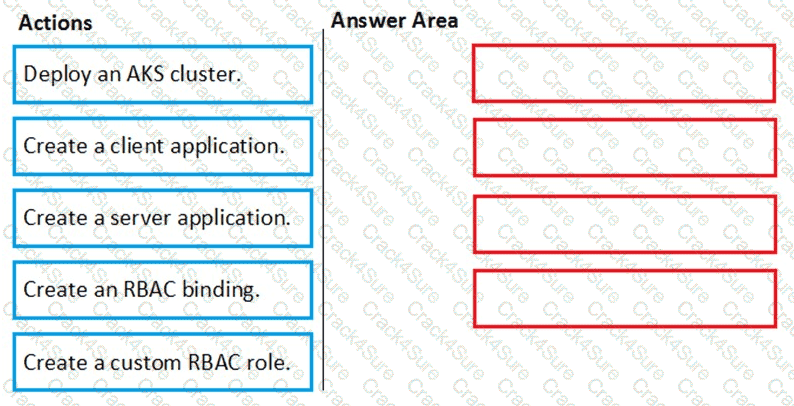
You need to deploy AKS1 to meet the platform protection requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
NOTE: More than one order of answer choices is correct. You will receive credit for any of the correct orders you select.
You are evaluating the security of the network communication between the virtual machines in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

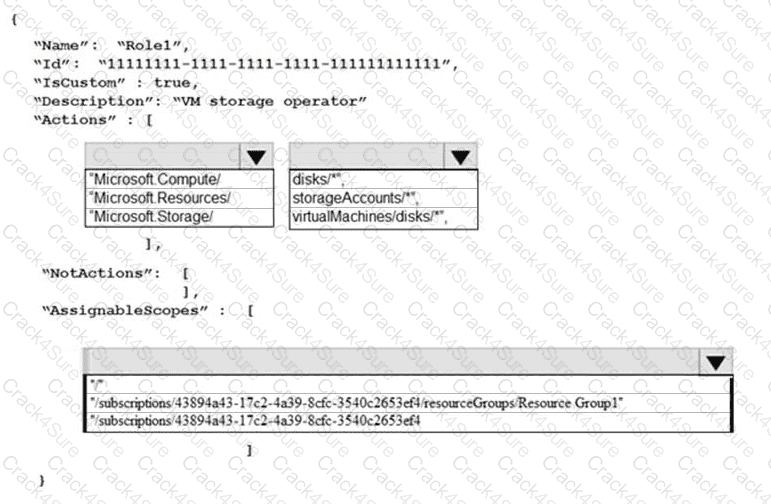
You need to create Role1 to meet the platform protection requirements.
How should you complete the role definition of Role1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to ensure that User2 can implement PIM.
What should you do first?
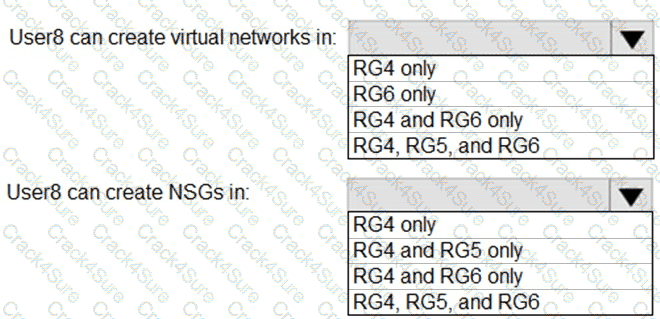
You assign User8 the Owner role for RG4, RG5, and RG6.
In which resource groups can User8 create virtual networks and NSGs? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
: 2 HOTSPOT
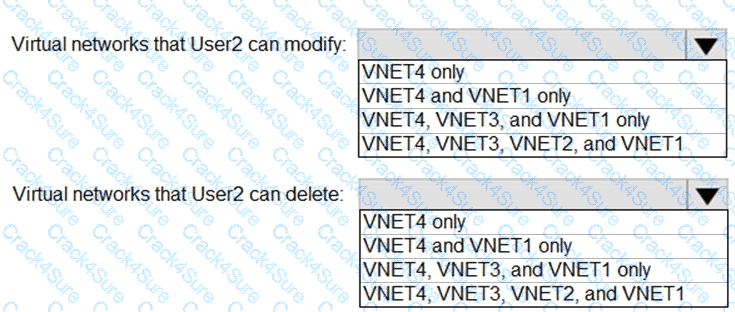
Which virtual networks in Sub1 can User2 modify and delete in their current state? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You are evaluating the effect of the application security groups on the network communication between the virtual machines in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

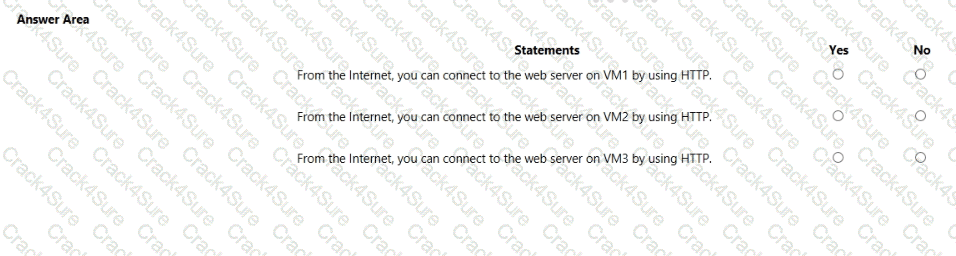
You are evaluating the security of VM1, VM2, and VM3 in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
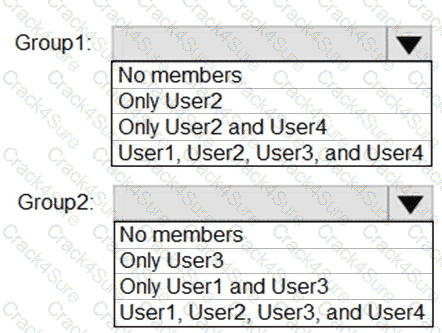
What is the membership of Group1 and Group2? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to meet the technical requirements for VNetwork1.
What should you do first?
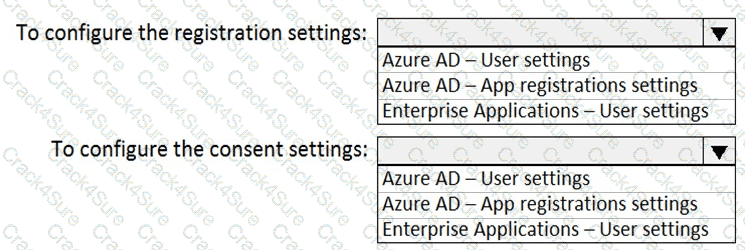
You need to ensure that the Azure AD application registration and consent configurations meet the identity and access requirements.
What should you use in the Azure portal? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to ensure that you can meet the security operations requirements.
What should you do first?
Your network contains an on-premises Active Directory domain named contoso.com. The domain contains a user named User1.
You have an Azure subscription that is linked to an Azure Active Directory (Azure AD) tenant named contoso.com. The tenant contains an Azure Storage account named storage1. Storage1 contains an Azure file share named share1.
Currently, the domain and the tenant are not integrated.
You need to ensure that User1 can access share1 by using his domain credentials.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.

You have an Azure subscription named Subscription1 that contains the resources shown in the following table.
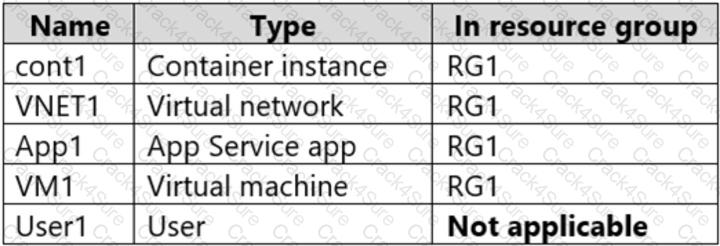
You create a custom RBAC role in Subscription1 by using the following JSON file.
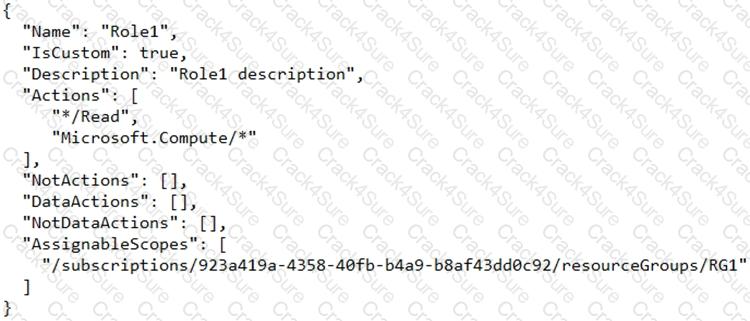
You assign Role1 to User1 on RG1.
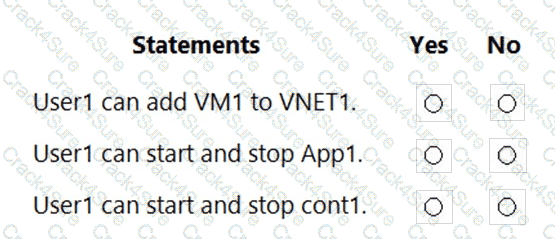
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have an Azure subscription.
You configure the subscription to use a different Azure Active Directory (Azure AD) tenant.
What are two possible effects of the change? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
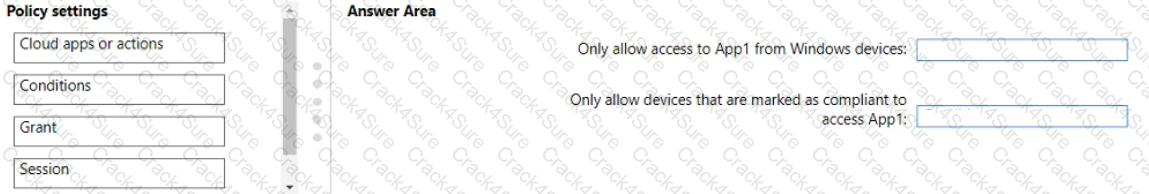
You have an Azure subscription that contains an Azure web app named Appl.
You plan to configure a Conditional Access policy for Appl. The solution must meet the following requirements:
• Only allow access to App1 from Windows devices.
• Only allow devices that are marked as compliant to access Appl.
Which Conditional Access policy settings should you configure? To answer, drag the appropriate settings to the correct requirements. Each setting may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains the resources shown in the following table.
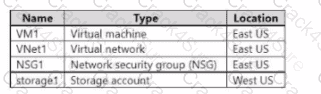
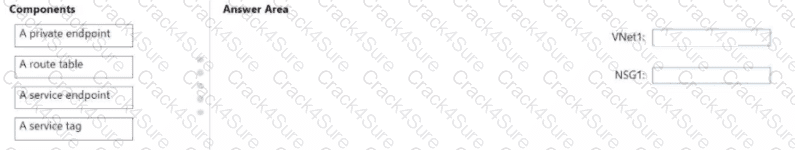
You need to configure network connectivity to meet the following requirements:
• Communication from VM1 to storage' must traverse an optimized Microsoft backbone network.
• All the outbound traffic from VM1 to the internet must be denied.
• The solution must minimize costs and administrative effort
What should you configure for VNetl and NSG1? To answer, drag the appropriate components to the correct resources. Each component may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content
NOTE: Each correct selection is worth one point.
On Monday, you configure an email notification in Microsoft Defender for Cloud to notify user1 @contoso.com about alerts that have a severity level of Low, Medium, or High. On Tuesday, Microsoft Defender for Cloud generates the security alerts shown in the following table.
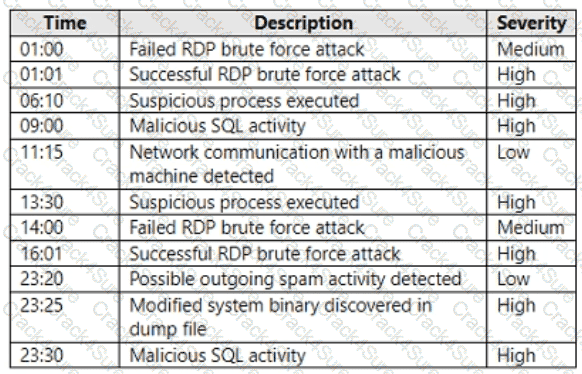
How many email notifications will user1 @contoso.com receive on Tuesday? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

You have an Azure subscription named Sub1 that contains an Azure Log Analytics workspace named LAW1.
You have 100 on-premises servers that run Windows Server 2012 R2 and Windows Server 2016. The servers connect to LAW1. LAW1 is configured to collect security-related performance counters from the connected servers.
You need to configure alerts based on the data collected by LAW1. The solution must meet the following requirements:
Alert rules must support dimensions.
The time it takes to generate an alert must be minimized.
Alert notifications must be generated only once when the alert is generated and once when the alert is
resolved.
Which signal type should you use when you create the alert rules?
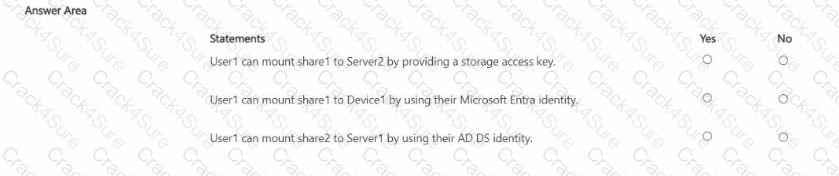
Your on-premises network contains an Active Directory Domain Services (AD DS) domain and the devices shown in the following table.
You have a hybrid Microsoft Entra tenant that contains a synced user named User1.
You have an Azure subscription that contains the Azure Files shares shown in the following table.
Used is assigned the Storage File Data SMB Share Contributor role tor storage1 and storage2.
The Security settings for Share! are configured as shown in the following exhibit.

For each of the following statements, select Yes if the statement is true. Otherwise. Select No.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains an Azure Data Lake Storage account named sa1.
You plan to deploy an app named App1 that will access sa1 and perform operations, including Read. List, Create Directory, and Delete Directory.
You need to ensure that App1 can connect securely to sa1 by using a private endpoint
What is the minimum number of private endpoints required for sa1?
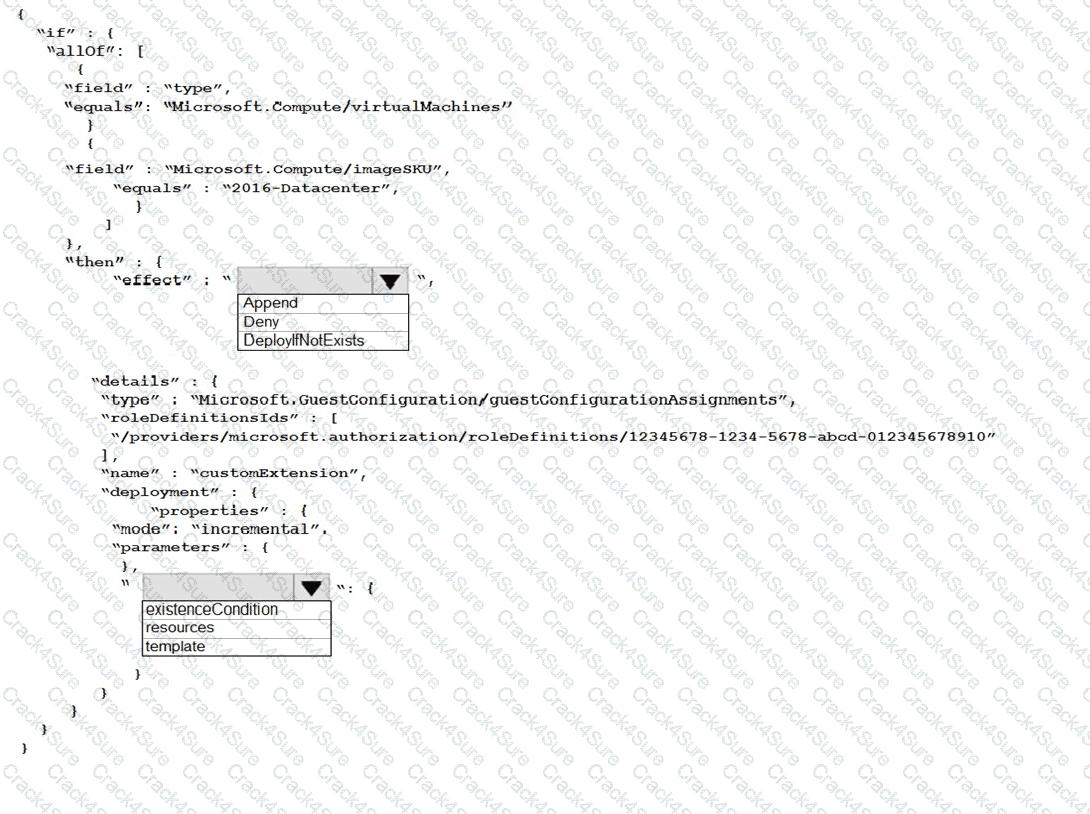
You have an Azure subscription. The subscription contains Azure virtual machines that run Windows Server 2016.
You need to implement a policy to ensure that each virtual machine has a custom antimalware virtual machine extension installed.
How should you complete the policy? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains a key vault and an Azure SQL server.
You need to deploy an Azure SQL database that uses Transparent Data Encryption (TDE) and a customer-managed key.
What should you create before you deploy the database?
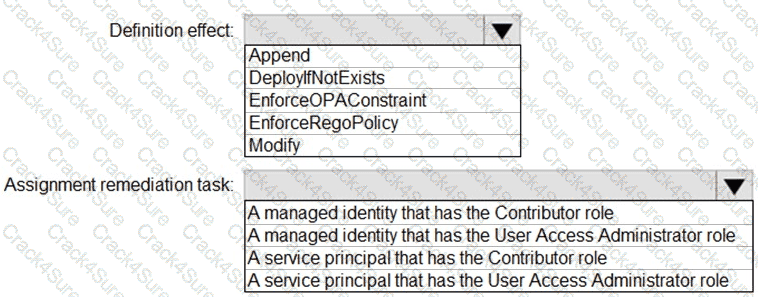
You have an Azure subscription.
You need to create and deploy an Azure policy that meets the following requirements:
When a new virtual machine is deployed, automatically install a custom security extension.
Trigger an autogenerated remediation task for non-compliant virtual machines to install the extension.
What should you include in the policy? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Your company plans to create separate subscriptions for each department. Each subscription will be
associated to the same Azure Active Directory (Azure AD) tenant.
You need to configure each subscription to have the same role assignments.
What should you use?
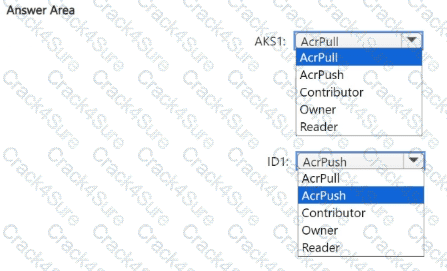
You need to configure the AKS1 and ID1 managed identities to meet the technical requirements. The solution must follow the principle of least privilege.
Which role should you assign to each identity? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to delegate a user to implement the planned change for Defender for Cloud.
The solution must follow the principle of least privilege.
Which user should you choose?
You need to implement the planned change for WAF1.
The solution must minimize administrative effort
What should you do?
You need to implement the planned change for SQLdb1.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You implement the planned changes for the key vaults.
To which key vaults can you restore AKV1 backups?
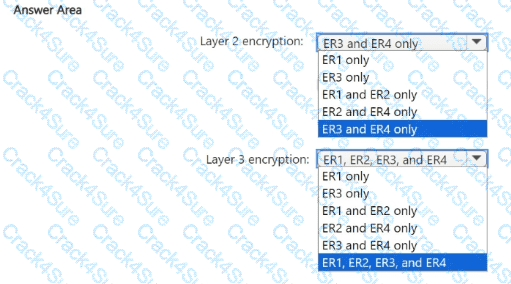
You need to recommend an encryption solution for the planned ExpressRoute implementation. The solution must meet the technical requirements.
Which ExpressRoute circuit should you recommend for each type of encryption? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to implement the planned change for VM1 to access storage1.
The solution must meet the technical requirements.
What should you do first?
You need to meet the technical requirements for the finance department users.
Which CAPolicy1 settings should you modify?
You plan to configure Azure Disk Encryption for VM4. Which key vault can you use to store the encryption key?
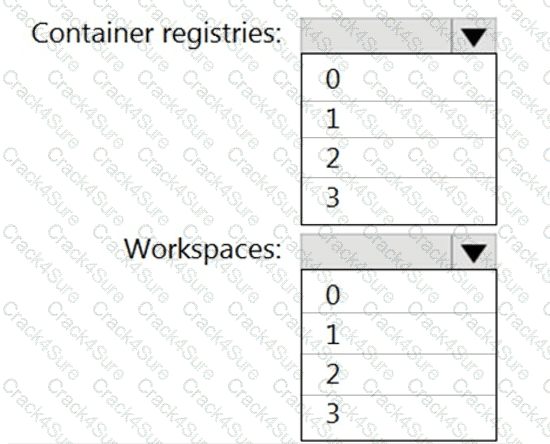
You need to configure support for Azure Sentinel notebooks to meet the technical requirements.
What is the minimum number of Azure container registries and Azure Machine Learning workspaces required?
You need to perform the planned changes for OU2 and User1.
Which tools should you use? To answer, drag the appropriate tools to the correct resources. Each tool may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.

From Azure Security Center, you need to deploy SecPol1.
What should you do first?
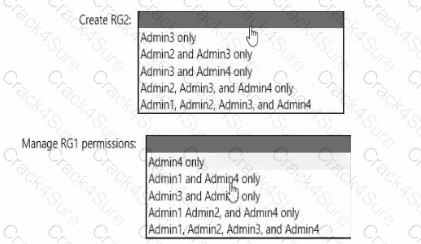
You need to delegate the creation of RG2 and the management of permissions for RG1. Which users can perform each task? To answer select the appropriate options in the answer area. NOTE: Each correct selection is worth one point
You need to encrypt storage1 to meet the technical requirements. Which key vaults can you use?
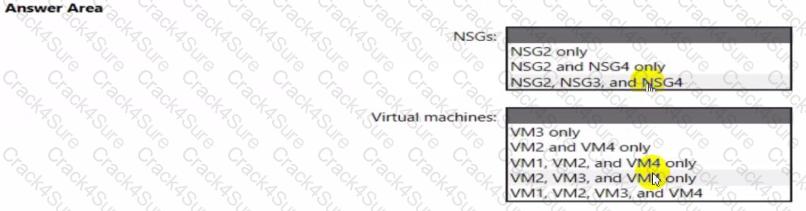
You implement the planned changes for ASG1 and ASG2.
In which NSGs can you use ASG1. and the network interfaces of which virtual machines can you assign to ASG2?
You plan to implement JIT VM access. Which virtual machines will be supported?
3 Months Free Update
3 Months Free Update
3 Months Free Update