We at Crack4sure are committed to giving students who are preparing for the Microsoft SC-200 Exam the most current and reliable questions . To help people study, we've made some of our Microsoft Security Operations Analyst exam materials available for free to everyone. You can take the Free SC-200 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
You have a Microsoft 365 E5 subscription and a Microsoft Sentinel workspace. You need to create a KQL query that will combine data from the following sources:
• Microsoft Graph
• Risky users detected by using Microsoft Entra ID Protection
The solution must minimize the volume of data returned. How should the query start?
You purchase a Microsoft 365 subscription.
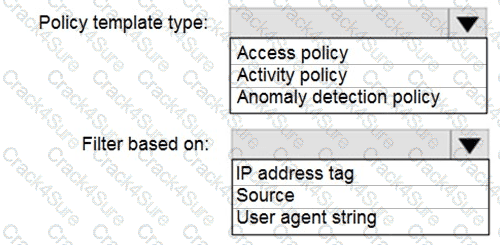
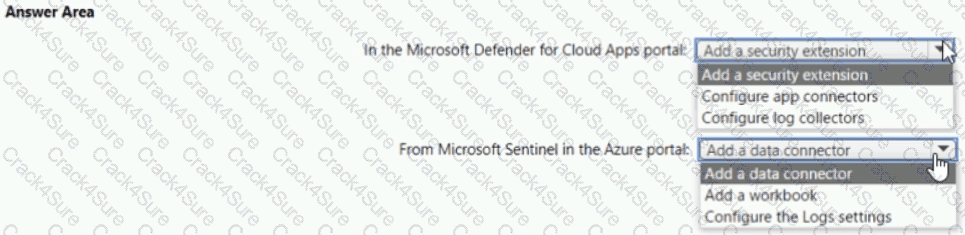
You plan to configure Microsoft Cloud App Security.
You need to create a custom template-based policy that detects connections to Microsoft 365 apps that originate from a botnet network.
What should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have five on-premises Linux servers.
You have an Azure subscription that uses Microsoft Defender for Cloud.
You need to use Defender for Cloud to protect the Linux servers.
What should you install on the servers first?
You have an Azure subscription that uses Microsoft Defender for Cloud and contains a storage account named storage1. You receive an alert that there was an unusually high volume of delete operations on the blobs in storage1.
You need to identify which blobs were deleted.
What should you review?
You have an Azure subscription that uses Microsoft Defender for Cloud and contains a resource group named RG1. RG1. You need to configure just in time (JIT) VM access for the virtual machines in RG1. The solution must meet the following
• Limit the maximum request time to two hours.
• Limit protocol access to Remote Desktop Protocol (RDP) only.
• Minimize administrative effort.
What should you use?
You have a Microsoft Sentinel workspace that has user and Entity Behavior Analytics (UEBA) enabled for Signin Logs.
You need to ensure that failed interactive sign-ins are detected.
The solution must minimize administrative effort.
What should you use?
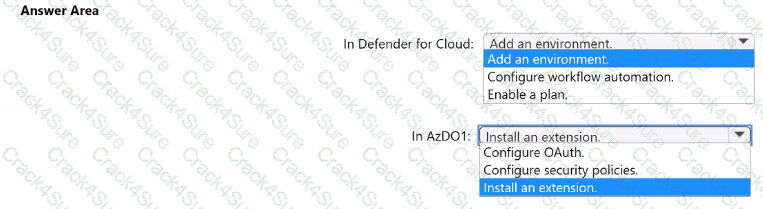
You have an Azure subscription named Sub1 that uses Microsoft Defender for Cloud.
You have an Azure DevOps organization named AzDO1.
You need to integrate Sub! and AzDO1. The solution must meet the following requirements:
• Detect secrets exposed in pipelines by using Defender for Cloud.
• Minimize administrative effort.
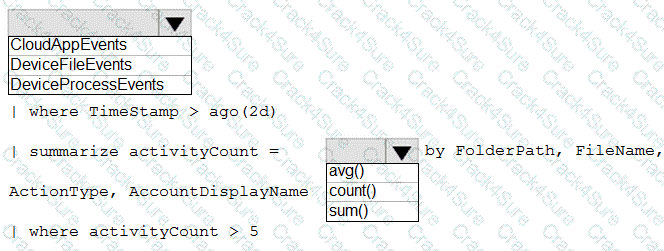
You have a Microsoft 365 subscription that uses Microsoft Defender XDR.
You have a query that contains the following statements.
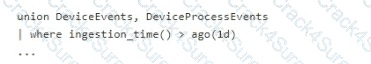
You need to configure a custom detection rule that will use the query. The solution must minimize how long it takes to be notified about events that match the query.
Which frequency should you select for the rule?
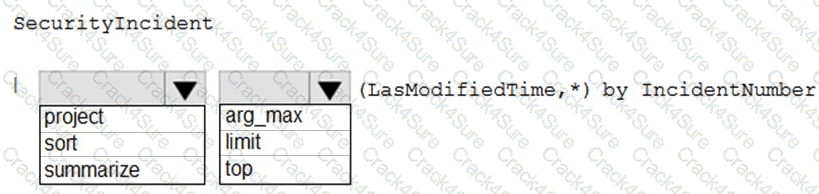
You need to create a query for a workbook. The query must meet the following requirements:
List all incidents by in cident number.
Only include the most recent log for each incident.
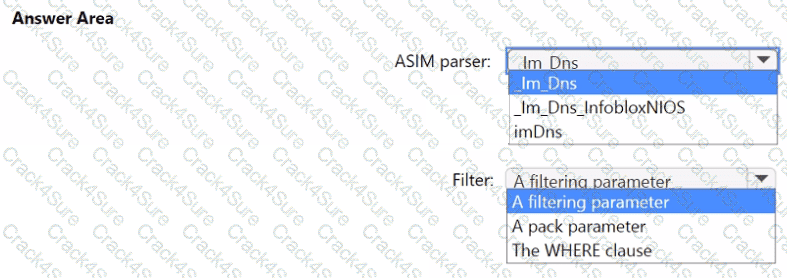
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have 500 on-premises Windows 11 devices that use Microsoft Defender for Endpoint
You enable Network device discovery.
You need to create a hunting query that will identify discovered network devices and return the identity of the onboarded device that discovered each network device.
Which built-in function should you use?
You have a Microsoft 365 E5 subscription.
Automated investigation and response (AIR) is enabled in Microsoft Defender for Office 365 and devices use full automation in Microsoft Defender for Endpoint.
You have an incident involving a user that received maIware-infected email messages on a managed device.
Which action requires manual remediation of the incident?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might hav e more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You are configuring Mi crosoft Defender for Identity integration with Active Directory.
From the Microsoft Defender for identity portal, you need to configure several accounts for attackers to exploit.
Solution: You add each account as a Sensitive account.
Does this meet the goal?
You have the following advanced hunting query in Microsoft 365 Defender.
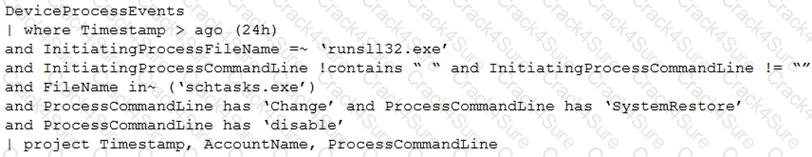
You need to receive an alert when any process disables System Restore on a device managed by Microsoft Defender during the last 24 hours.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
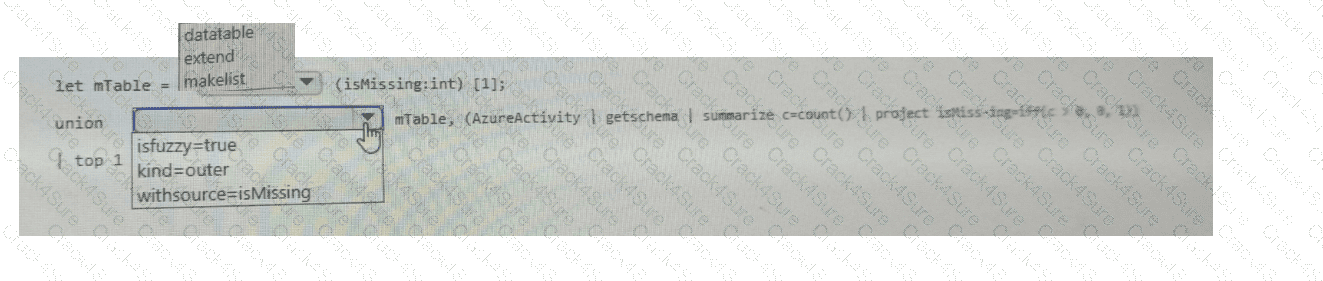
You have multiple Azure subscriptions that contain multiple Microsoft Sentinel workspaces.
You are creating a Microsoft Sentinel workbook that will include references to the AzureActivity table.
You need to create a KQL query that will perform the following actions:
. Check whether the AzureActivity table exists in each workspace.
. If the table exists, return a single row that has the isMissing column set to 0.
. If the table does NOT exist, return a single row that has the isMissing column set to 1.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an on-premises network.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Identity.
From the Microsoft Defender portal, you investigate an incident on a device named Device1 of a user named User1. The incident contains the following Defender for Identity alert.
Suspected identity theft (pass-the-ticket) (external ID 2018)
You need to contain the incident without affecting users and devices. The solution must minimize administrative effort.
What should you do?
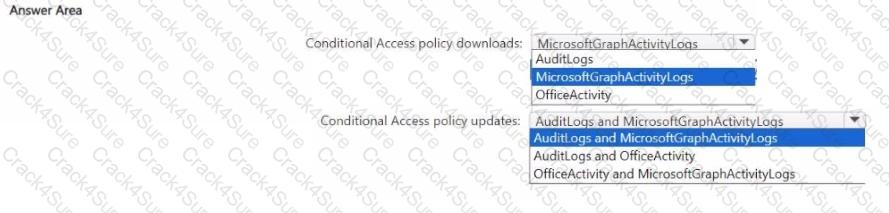
You have a Microsoft 365 E5 subscription that uses Microsoft Defender XDR.
You have a Microsoft Sentinel workspace.
Microsoft Sentinel connectors are configured as shown in the following table.
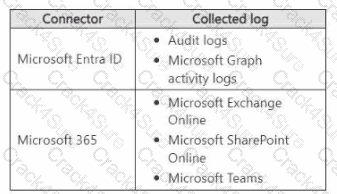
You use Microsoft Sentinel to investigate suspicious Microsoft Graph API activity related to Conditional Access policies. You need to search for the following activities:
• Downloads of the Conditional Access policies by using PowerShell
• Updates to the Conditional Access policies by using the Microsoft Entra admin center
Which tables should you query for each activity? lo answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
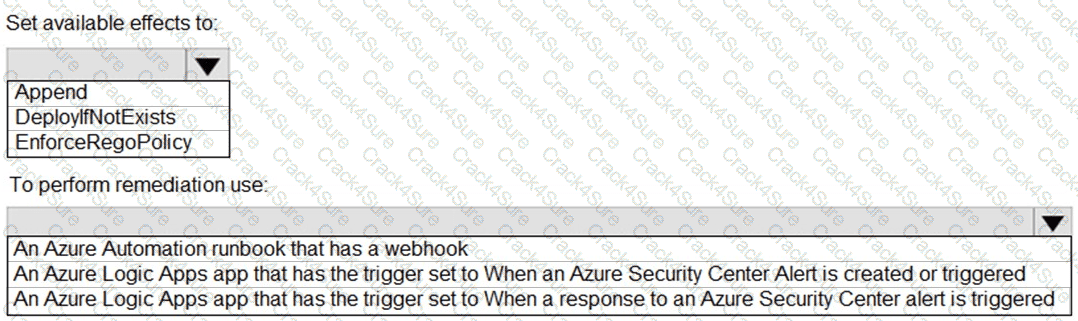
You have an Azure subscription that uses Azure Defender.
You plan to use Azure Security Center workflow automation to respond to Azure Defender threat alerts.
You need to create an Azure policy that will perform threat remediation automatically.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 B5 subscription. You have a PowerShell script that queries the unified audit log.
You discover that the query returns only the first page of results due to server-side paging. You need to ensure that you get all the results. Which property should you query in the results?
You have an Azure subscription that uses Microsoft Sentinel.
You need to minimize the administrative effort required to respond to the incident s and remediate the security threats detected by Microsoft Sentinel.
Which two features should you use? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
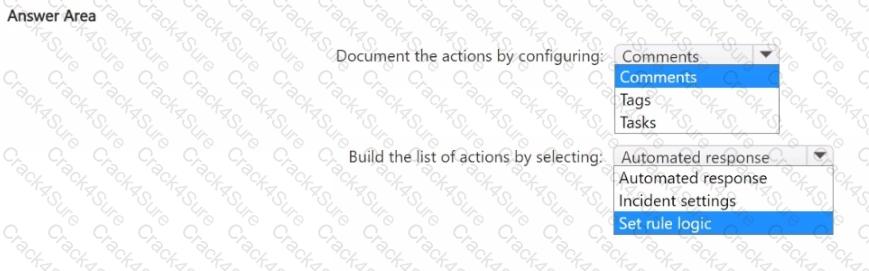
You have an Azure subscription that contains a Microsoft Sentinel workspace named WS1.
You need to ensure that the incidents in WS1 include a list of actions that must be performed. The solution must meet the following requirements:
• Ensure that you can build a tailored list of actions for each type of incident.
• Minimize administrative effort.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
A security administrator receives email alerts from Azure Defender for activities such as potential malware uploaded to a storage account and po tential successful brute force attacks.
The security administrator does NOT receive email alerts for activities such as antimalware action failed and suspicious network activity. The alerts appear in Azure Security Center.
You need to ensure that the sec urity administrator receives email alerts for all the activities.
What should you configure in the Security Center settings?
You have a Microsoft 365 subscription that uses Microsoft Defender for Office 365.
You have Microsoft SharePoint Online sites that contain sensitive documents. The documents contain customer account numbers that each consists of 32 alphanumeric characters.
You need to create a data loss prevention (DLP) policy to protect the sensitive documents. What should you use to detect which documents are sensitive?
You have an Azure subscription that contains an Microsoft Sentinel workspace.
You need to create a playbook that will run automatically in response to an Microsoft Sentinel alert.
What should you create first?
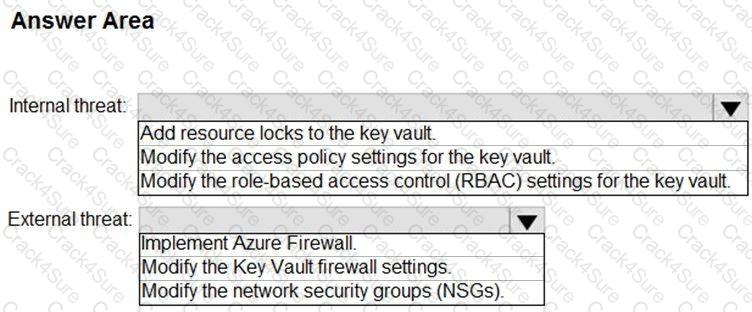
You need to remediate ac tive attacks to meet the technical requirements.
What should you include in the solution?
You need to recommend remediation actions for the Azure Defender alerts for Fabrikam.
What should you recommend for each threat? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to complete the query for failed sign-ins to meet the technical requirements.
Where can you find the column name to complete the where clause?
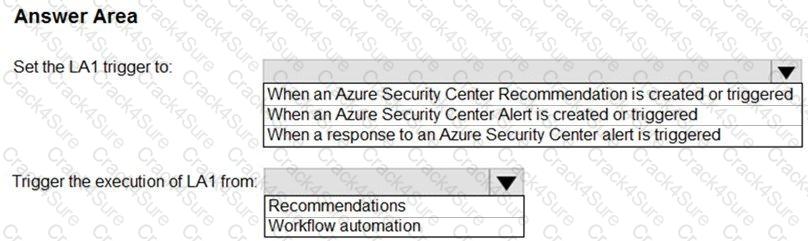
You have an Azure subscrip tion that has Azure Defender enabled for all supported resource types.
You create an Azure logic app named LA1.
You plan to use LA1 to automatically remediate security risks detected in Azure Security Center.
View the window
You need to test LA1 in Security Center.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to ensure that the processing of incidents generated by rulequery1 meets the Microsoft Sentinel requirements.
What should you create first?
You need to create an advanced hunting query to i nvestigate the executive team issue.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to ensure that the configuration of HuntingQuery1 meets the Microsoft Sentinel requirements.
What should you do?
You need to implement the Defender for Cloud requirements.
What should you configure for Server2?
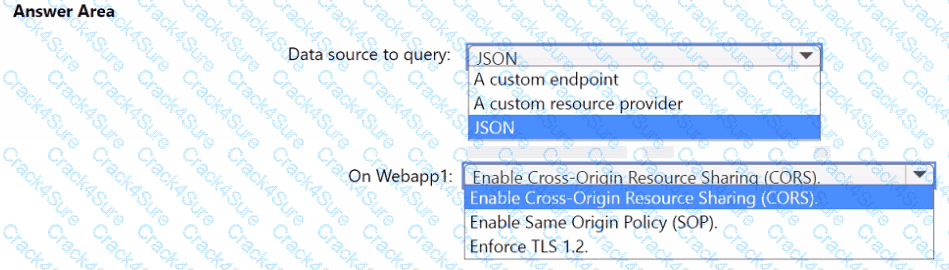
You need to implement the query for Workbook1 and Webapp1. The solution must meet the Microsoft Sentinel requirements. How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You need to configure event monitoring for Server1. The solution must meet the Microsoft Sentinel requirements. What should you create first?
You need to ensure that the Group1 members can meet the Microsoft Sentinel requirements.
Which role should you assign to Group1?
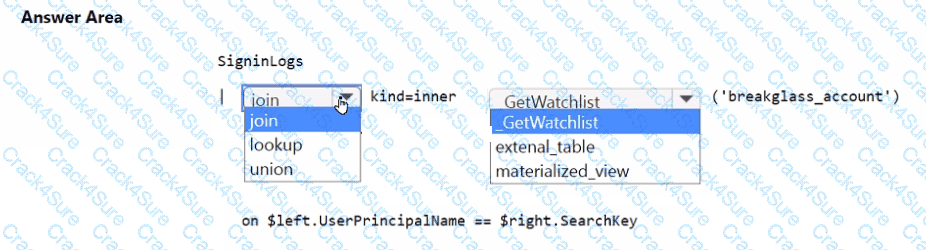
You need to implement the Microsoft Sentinel NRT rule for monitoring the designated break glass account. The solution must meet the Microsoft Sentinel requirements.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to implement the Defender for Cloud requirements.
Which subscription-level role should you assign to Group1?
You need to implement the scheduled rule for incident generation based on rulequery1.
What should you configure first?
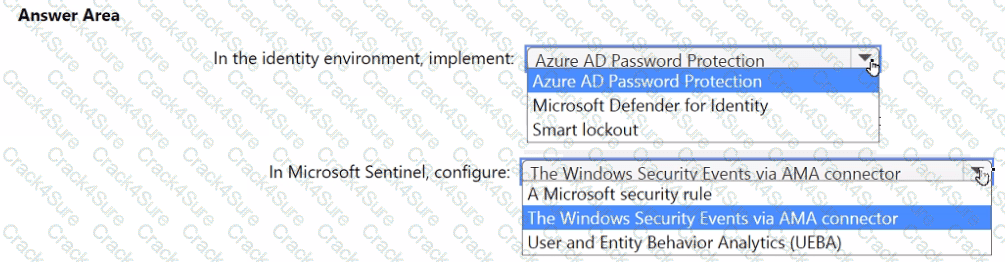
You need to monitor the password resets. The solution must meet the Microsoft Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to implement the ASIM query for DNS requests. The solution must meet the Microsoft Sentinel requirements. How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You need to create the test rule to meet the Azure Sentinel requirements. What should you do when you create the rule?
You need to implement the Azure Information Protection requirements. What should you configure first?
You need to assign a role-based access control (RBAC) role to admin1 to meet the Azure Sentinel requirements and the business requirements.
Which role should you assign?
You need to restrict cloud apps running on CUENT1 to meet the Microsoft Defender for Endpoint requirements. Which two configurations should you modify? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
You need to modify the anomaly detection policy settings to meet the Microsoft Defender for Cloud Apps requirements and resolve the reported problem.
Which policy should you modify?
You need to implement Microsoft Defender for Cloud to meet the Microsoft Defender for Cloud requirements and the business requirements. What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
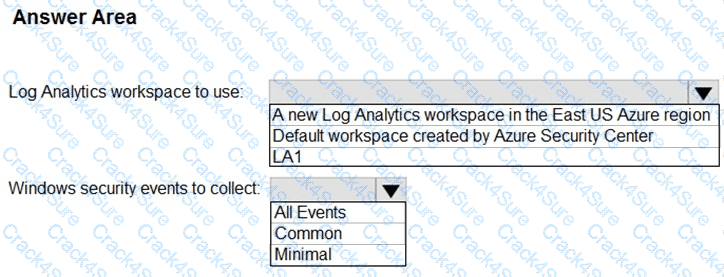
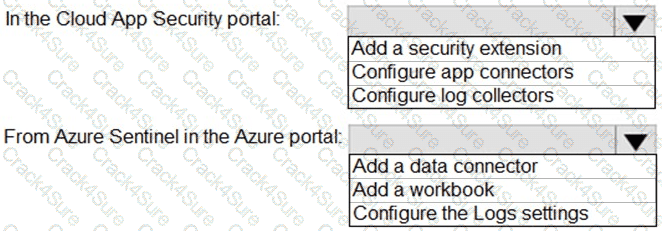
You need to configure the Azure Sentinel integration to meet the Azure Senti nel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to restrict cloud apps running on CLIENT1 to meet the Microsoft Defender for Endpoint requirements.
Which two configurations should you modify? Each correct answ er present part of the solution.
NOTE: Each correct selection is worth one point.
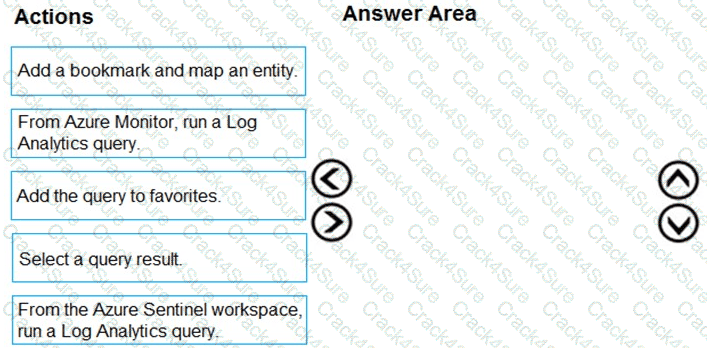
You need to add notes to the events to meet the Azure Sentinel requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of action to the answer area and arrange them in the correct order.
You need to configure the Microsoft Sentinel integration to meet the Microsoft Sentinel requirements. What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Which rule setting should you configure to meet the Microsoft Sentinel requirements?
You need to modify the anomaly detection policy settings to meet the Cloud App Security requirements. Which policy should you modify?
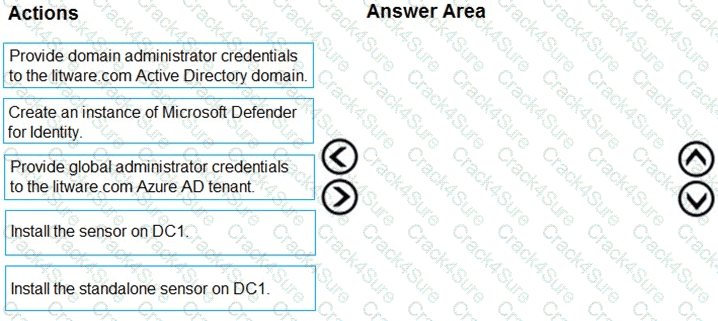
You need to configure DC1 to meet the business requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
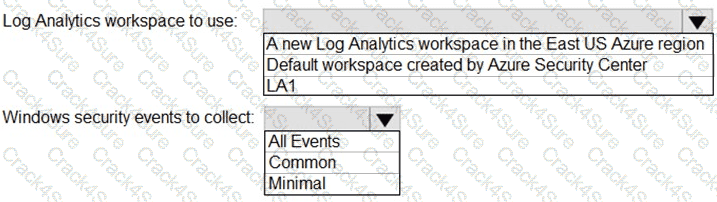
You need to implement Azure Defender to meet the Azure Defender requirements and the business requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
3 Months Free Update
3 Months Free Update
3 Months Free Update