We at Crack4sure are committed to giving students who are preparing for the Microsoft SC-900 Exam the most current and reliable questions . To help people study, we've made some of our Microsoft Security Compliance and Identity Fundamentals exam materials available for free to everyone. You can take the Free SC-900 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
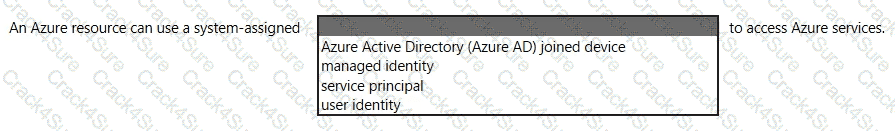
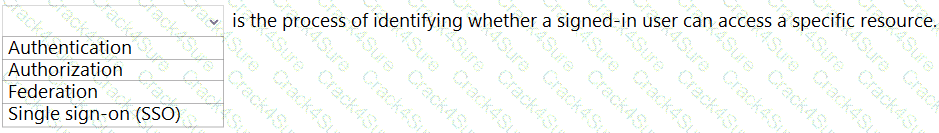
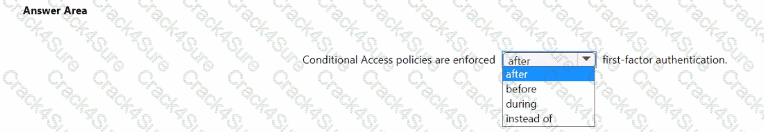
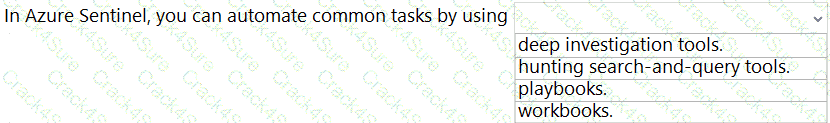
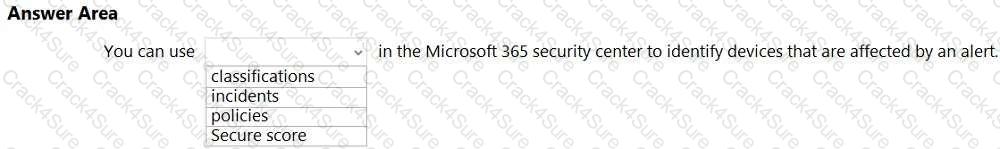
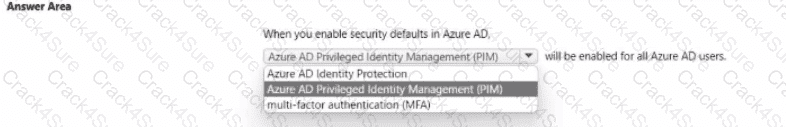
Select the answer that correctly completes the sentence.
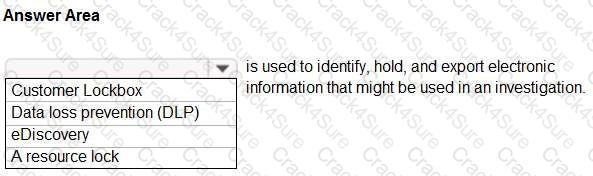
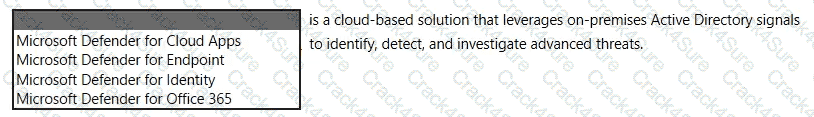
Select the answer that correctly completes the sentence.

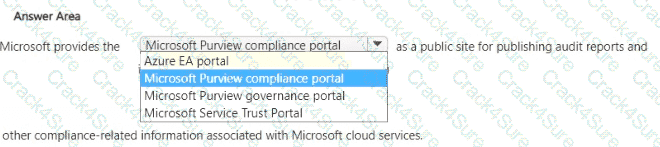
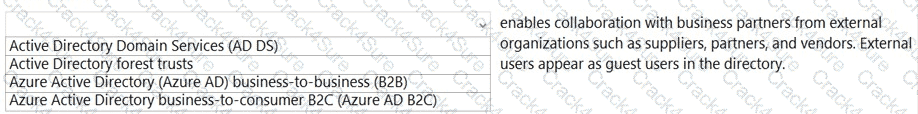
Select the answer that correctly completes the sentence.
What should you use in the Microsoft 365 security center to view security trends and track the protection status of identities?
completes the sentence.
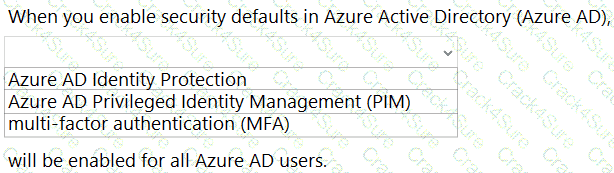
Select the answer that correctly completes the sentence.
Select the answer that correctly completes the sentence.
What do you use to provide real-time integration between Azure Sentinel and another security source?
What is an example of encryption at rest?
Which two types of devices can be managed by using Endpoint data loss prevention (Endpoint DLP)? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
You plan to implement a security strategy and place multiple layers of defense throughout a network infrastructure.
Which security methodology does this represent?
You need to create a data loss prevention (DLP) policy. What should you use?
What is a function of Conditional Access session controls?
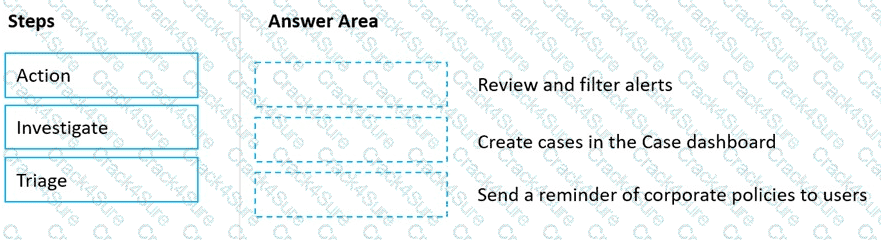
Match the Microsoft 365 insider risk management workflow step to the appropriate task.
To answer, drag the appropriate step from the column on the left to its task on the right. Each step may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
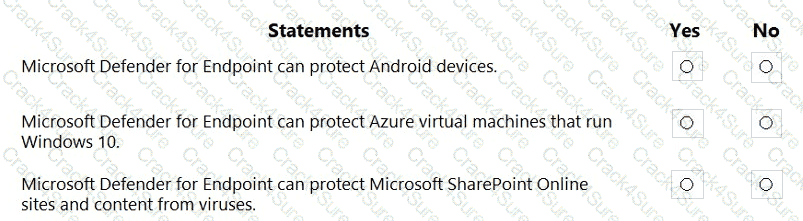
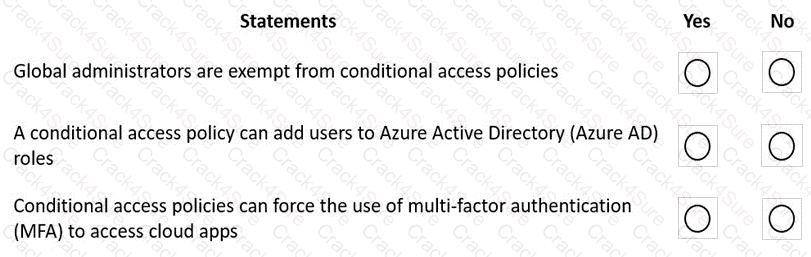
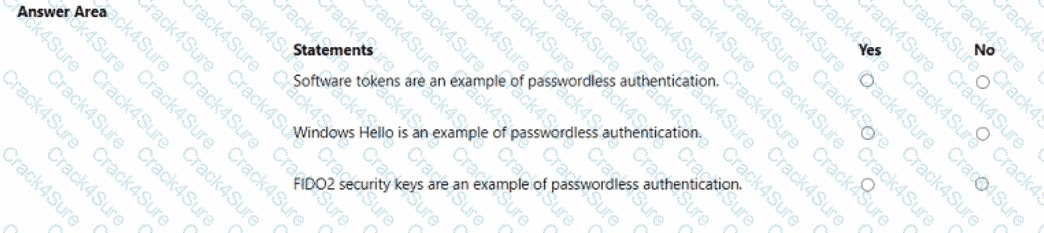
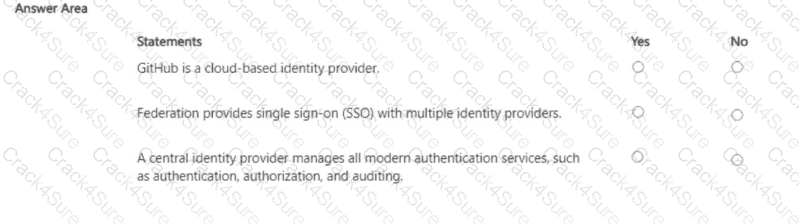
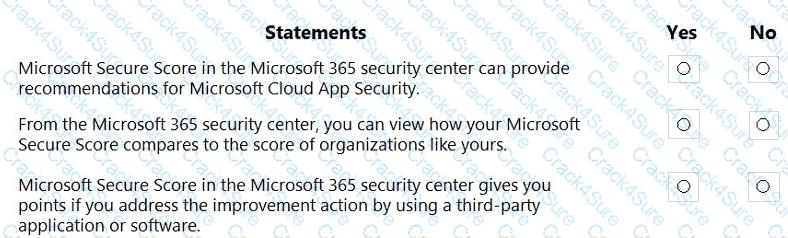
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have an Azure subscription.
You need to implement approval-based, tiProme-bound role activation.
What should you use?
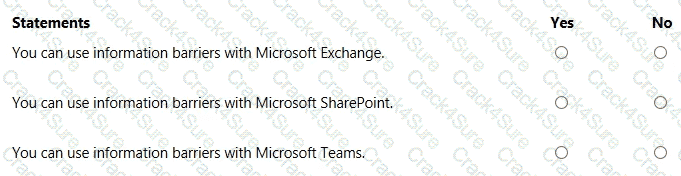
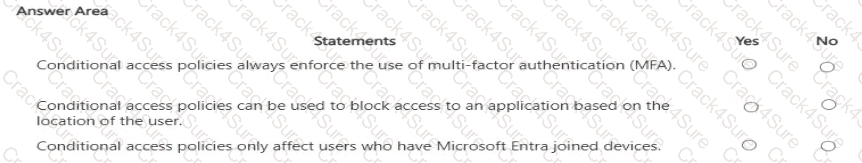
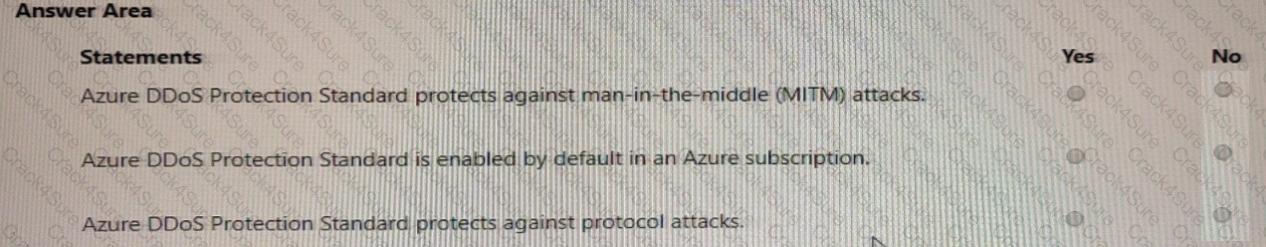
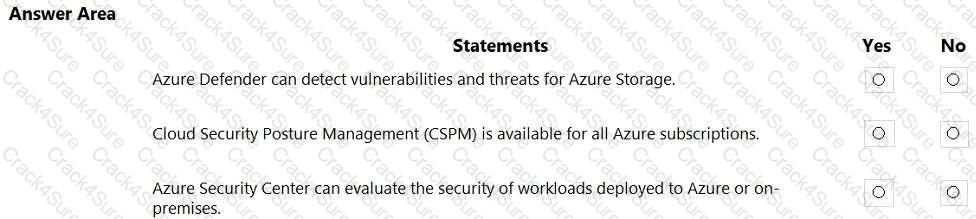
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Which Microsoft 365 compliance center feature can you use to identify all the documents on a Microsoft SharePoint Online site that contain a specific key word?
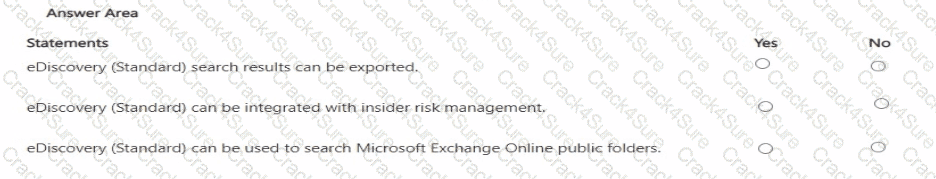
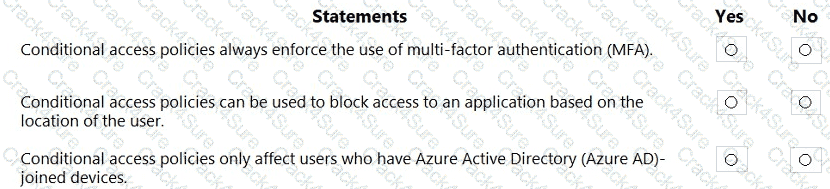
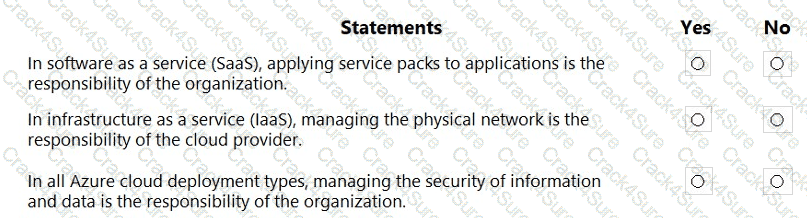
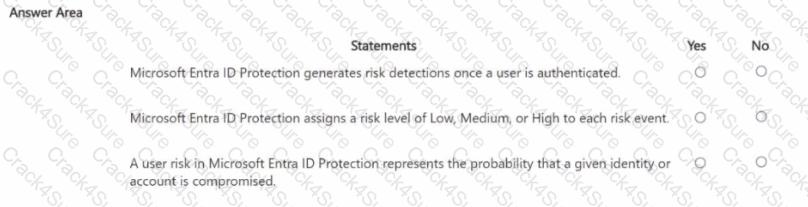
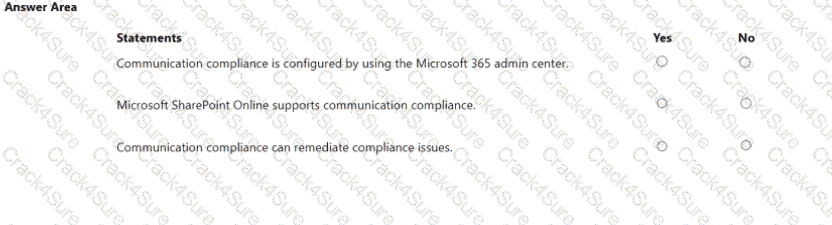
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Which Microsoft 365 feature can you use to restrict users from sending email messages that contain lists of customers and their associated credit card numbers?
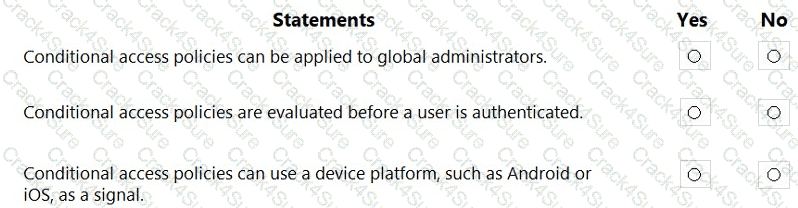
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Which three authentication methods can be used by Azure Multi-Factor Authentication (MFA)? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
Which two types of resources can be protected by using Azure Firewall? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
Select the answer that correctly completes the sentence.
What can you protect by using the information protection solution in the Microsoft 365 compliance center?
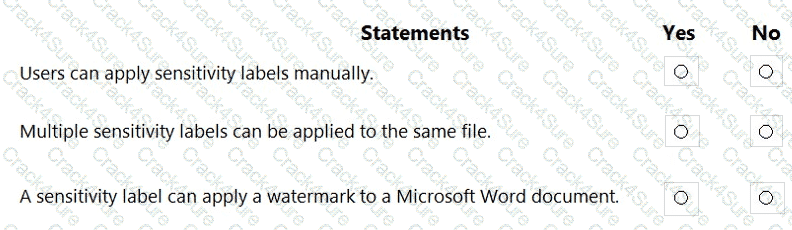
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Which score measures an organization ' s progress in completing actions that help reduce risks associated to data protection and regulatory standards?
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
When security defaults are enabled for an Azure Active Directory (Azure AD) tenant, which two requirements are enforced? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
Which Microsoft Defender for Cloud metric displays the overall security health of an Azure subscription?
When you enable Azure AD Multi-Factor Authentication (MFA), how many factors are required for authentication?
In a hybrid identity model, what can you use to sync identities between Active Directory Domain Services (AD DS) and Azure Active Directory (Azure AD)?
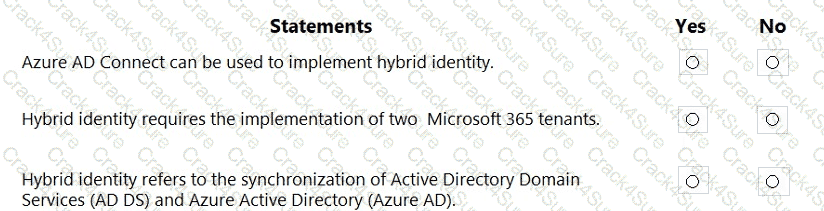
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Select the answer that correctly completes the sentence.
Select the answer that correctly completes the sentence.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Which Azure Active Directory (Azure AD) feature can you use to provide just-in-time (JIT) access to manage Azure resources?
Which compliance feature should you use to identify documents that are employee resumes?
You have a Microsoft 365 E3 subscription.
You plan to audit user activity by using the unified audit log and Basic Audit.
For how long will the audit records be retained?
You have an Azure subscription.
You need to implement approval-based time-bound role activation.
What should you use?
Select the answer that correctly completes the sentence.
You have an Azure subscription that contains multiple resources.
You need to assess compliance and enforce standards for the existing resources.
What should you use?
Select the answer that correctly completes the sentence.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
What can you use to provision Azure resources across multiple subscriptions in a consistent manner?
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
What is an assessment in Compliance Manager?
Select the answer that correctly completes the sentence.
What can you use to scan email attachments and forward the attachments to recipients only if the attachments are free from malware?
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Which feature is included in Microsoft Entra ID Governance?
You need to keep a copy of all files in a Microsoft SharePoint site for one year, even if users delete the files from the site. What should you apply to the site?
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
3 Months Free Update
3 Months Free Update
3 Months Free Update