We at Crack4sure are committed to giving students who are preparing for the Netskope NSK101 Exam the most current and reliable questions . To help people study, we've made some of our Netskope Certified Cloud Security Administrator (NCCSA) exam materials available for free to everyone. You can take the Free NSK101 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
You want to set up a Netskope API connection to Box.
What two actions must be completed to enable this connection? (Choose two.)
Which Netskope component would an administrator use to see an overview of private application usage and performance?
You are setting up a real-time threat protection policy for patient zero to block previously unseen files until a benign verdict is produced by the Netskope Threat Protection Service. In this scenario, which two policy parameters must you configure? (Choose two)
You want to use an out-of-band API connection into your sanctioned Microsoft 365 OneDrive for Business application to find sensitive content, enforce near real-time policy controls, and quarantine malware.
In this scenario, which primary function in the Netskope platform would you use to connect your application to Netskope?
You want to block access to sites that use self-signed certificates. Which statement is true in this scenario?
A company user cannot open a sports news site. You want to review the category of the website and see how the rules are applied even though this category is allowed. In this scenario, which action will accomplish this task?
When would an administrator need to use a tombstone file?
A customer asks you to create several real-time policies. Policy A generates alerts when any user downloads, uploads, or shares files on a cloud storage application. Policy B blocks users from downloading files from any operating system (OS) other than Mac or Windows for cloud storage. In this case, policy A is least restrictive and policy B is more restrictive.
Which statement is correct in this scenario?
Which Netskope platform component uses NewEdge Traffic Management for traffic steering?
You are required to mitigate malicious scripts from being downloaded into your corporate devices every time a user goes to a website. Users need to access websites from a variety of categories, including new websites.
Which two actions would help you accomplish this task while allowing the user to work? (Choose two.)
You want to deploy Netskope's zero trust network access (ZTNA) solution, NPA. In this scenario, which action would you perform to accomplish this task?
Which three status indicators does the NPA Troubleshooter Tool provide when run? (Choose three)
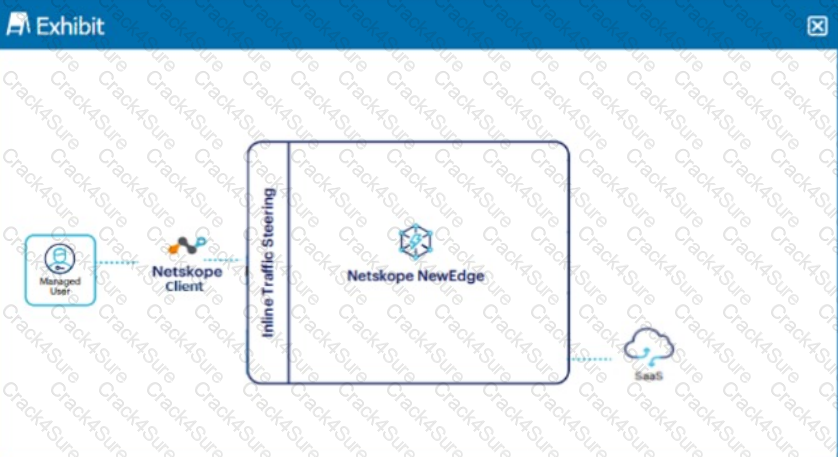
Click the Exhibit button.
A user is connected to a SaaS application through Netskope's Next Gen SWG with SSL inspection enabled. In this scenario, what information is available in SkopeIT? (Choose three.)
Your department is asked to report on GDPR data publicly exposed in Microsoft 365, Salesforce. and Slack-sanctioned cloud applications. Which deployment model would you use to discover this data?
The Netskope deployment for your organization is deployed in CASB-only mode. You want to view dropbox.com traffic but do not see it when using SkopeIT.
In this scenario, what are two reasons for this problem? (Choose two.)
You need to create a service request ticket for a client-related issue using the Netskope client Ul. In this scenario, you generate the client logs by right-clicking on the system tray icon and choosing
A customer changes CCI scoring from the default objective score to another score. In this scenario, what would be a valid reason for making this change?
You just deployed the Netskope client in Web mode and several users mention that their messenger application is no longer working. Although you have a specific real-time policy that allows this application, upon further investigation you discover that it is using proprietary encryption. You need to permit access to all the users and maintain some visibility.
In this scenario, which configuration change would accomplish this task?
What are two reasons why legacy solutions, such as on-premises firewalls and proxies, fail to secure the data and data access compared to Netskope Secure Web Gateway? (Choose two.)
How do you protect your data at rest intellectual property (IP), such as source code or product designs, stored in Microsoft 365 SharePoint?
An administrator has created a DLP rule to search for text within documents that match a specific pattern. After creating a Real-time Protection Policy to make use of this DLP rule, the administrator suspects the rule is generating false positives.
Within the Netskope tenant, which feature allows administrators to review the data that was matched by the DLP rule?
A Netskope administrator wants to create a policy to quarantine files based on sensitive content.
In this scenario, which variable must be included in the policy to achieve this goal?
Your company started deploying the latest version of the Netskope Client and you want to track the progress and device count using Netskope.
Which two statements are correct in this scenario? (Choose two.)
There is a DLP violation on a file in your sanctioned Google Drive instance. The file is in a deleted state. You need to locate information pertaining to this DLP violation using Netskope. In this scenario, which statement is correct?
As an administrator, you are asked to monitor the status of your IPsec and GRE tunnels.
In the Netskope Admin UI, which two sections would you use in this scenario? (Choose two.)
What is a benefit that Netskope instance awareness provides?
Which compliance standard should a company consider if both controllers and processors have legal entities in the EU?
Which three statements about Netskope Private Access Publishers are correct? (Choose three.)
All users are going through Netskope's Next Gen SWG. Your CISO requests a monthly report of all users who are accessing cloud applications with a "Low" or a "Poor" CCL, where the activity is either "Edit" or "Upload".
Using the Advanced Analytics interface, which two statements describe which actions must be performed in this scenario? (Choose two.)
You need to locate events for specific activities such as "edit" or "login successful" in a cloud application.
In which SkopeIT Events & Alerts page would this information be found?
Exhibit

A user is connected to a cloud application through Netskope's proxy.
In this scenario, what information is available at Skope IT? (Choose three.)
You want to see the actual data that caused the policy violation within a DLP Incident view.
In this scenario, which profile must be set up?
You are deploying TLS support for real-time Web and SaaS transactions. What are two secure implementation methods in this scenario? (Choose two.)
3 Months Free Update
3 Months Free Update
3 Months Free Update